Tales from the crypto
We take ideas and build, mould and shape them into commercial products and operating companies.
Classic Cryptography
Dates back to ancient Egypt.
Live up until the 20th century, methods of encryption using pen and paper, sometimes small mechanical aid.
Kings had their chief cipherers.
1800 - WWI
Cryptanalysis starts to be taken more seriously, with more academics getting involved.
Cryptography plays a huge part in WW I, mostly used in the navy.
Cryptanalysis
Cryptanalysis
-
Total break - key is compromised
-
Global deduction - algo to break the code w/out the key
-
Instance deduction
-
Information deduction - Shannon information about the ciphertext
-
Distinguish algo - Differentiate between random characters and ciphertext
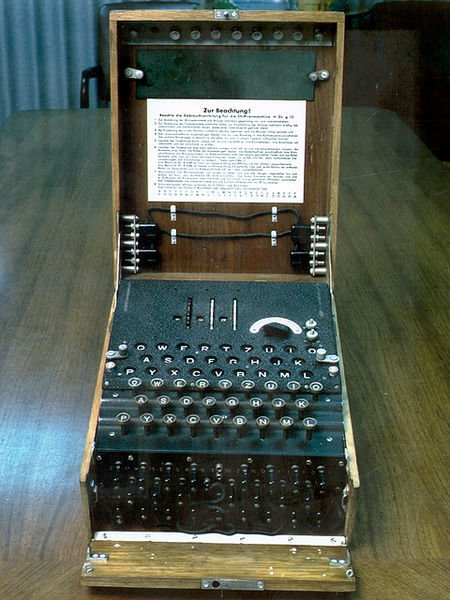
WW II
Electromechanical cipher machines became widely used.
Start to move away from one-time pads to mechanical ciphers.
Enigma
Modern Cryptography
These keys convert the messages and data into “digital gibberish” through encryption and then return them to the original form through decryption.
Symmetric-key algorythms
They use the same cryptographic keys for both encryption of plaintext and decryption of ciphertext.
Examples: AES, Twofish, Blowfish
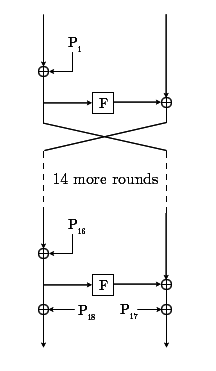
Blowfish (bcrypt)
Block cipher, except when changing keys.
The algorithm keeps two subkey arrays: the 18-entry P-array and four 256-entry S-boxes
Blowfish (bcrypt)
64-bit block size; 32-bit - 448-bit key length
Uses Substitution Boxes to make an 8-bit input into 32-bit output

Advanced Encryption Standard - AES
Based on combination of both substitution and permutation, and is fast in both software and hardware.
Specified with block and key sizes that may be any multiple of 32 bits.
Operates on a 4×4 matrix of bytes, termed the state.
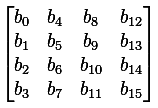
Advanced Encryption Standard - AES
- KeyExpansions—round keys are derived from the cipher key using Rijndael's key schedule. AES requires a separate 128-bit round key block for each round plus one more.
- InitialRound
- AddRoundKey—each byte of the state is combined with a block of the round key using bitwise xor.
- Rounds
- SubBytes—a non-linear substitution step where each byte is replaced with another according to a lookup table.
- ShiftRows—a transposition step where the last three rows of the state are shifted cyclically a certain number of steps.
- MixColumns—a mixing operation which operates on the columns of the state, combining the four bytes in each column.
- AddRoundKey
- Final Round (no MixColumns)
- SubBytes
- ShiftRows
- AddRoundKey.
Asymmetric-key algorithms
It has a public and private key, this key pair is mathematically linked.
Public key is used for ditigal signature, encrypt plain text.
Private key is used to create signature, decrypt cipher.
RSA
RSA creates and then publishes a public key based on two large Prime numbers.
Usually some padding is applied before encrypting a message.
RSA - keygen
p = 61, q = 53, n = 3233;
φ(n) = 3120; # Euler-function
e = 17; # 1 < e < 3120
d = e (mod φ(n)) = 2753;
public key is (n = 3233, e = 17)
private key is (d = 2753)
RSA
To encrypt m = 65, we calculate
c = 65^17 mod 3233 # 2790
To decrypt c = 2790, we calculate
m = 2790^2753 mod 3233 # 65
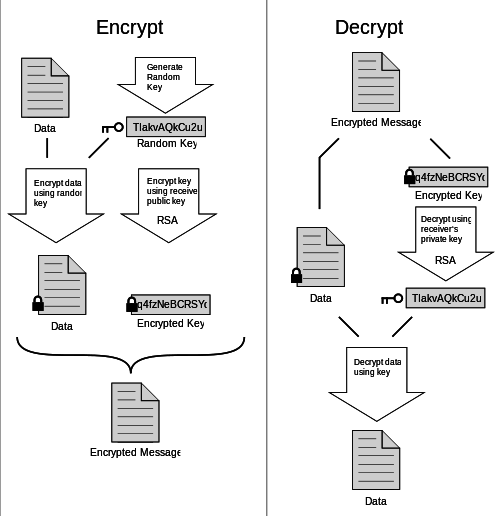
PGP - Pretty Good Privacy
Used for signing, encrypting and decrypting emails, texts, files, and documents. PGP combines symmetric-key encryption and public-key encryption.
Each public key is bound to a user's email address.
PGP - Pretty Good Privacy
Hash Functions
A function that is considered practically impossible to invert. The input data is often called the message, and the hash value is often called the message digest or simply the digest.
Examples: MD5, SHA-1
Hash Functions
- Easy to compute the hash value for any given message.
- Infeasible to generate a message that has a given hash.
- Infeasible to modify a message without changing the hash.
- Infeasible to find two different messages with the same hash.
Salt
- Random, non-secret value
- Stored in pair with the digest
- Concatenated to the message before hashing applied
Pepper
- Random, secret value
- Held separately from the message/digest
- Added to the message before hashing applied
Hashing example
require 'digest'
salt = "G0rd0n/R4mSey" # Generated for the user and stored with the digest
pepper = "B33F-We11ingt0n" # Not stored anywhere near the digests/salts
message = "Ruby Ireland"
# simple
digest = Digest::MD5.hexdigest(message) # "ba7b9a8db08db9e98c3b7549db008f0b"
# seasoned
digest = Digest::MD5.hexdigest(salt + pepper + message) # "90ae1628a113a7b213756360a311d319"Thank You!