BUILDING OF A MULTILEVEL SECURITY PLATFORM [PMN]


GENERAL
DIRECTORATE
FOR
ARMAMENT

Definition: Multilevel Security
A set of practices, technologies, and policies to protect systems at different classification levels (e.g., Confidential, Secret, Top Secret), relying on compartmentalization and strict access control.


Definition: REAL TIME
Real-time constraints: time-bounded requirements where a system’s correctness depends on when results are produced, not only on what they are.
-
Hard: any missed deadline = system failure (e.g., braking control).
-
Firm: late results have zero value; rare misses tolerated.
-
Soft: occasional misses degrade quality only (e.g., video).
Key metrics: deadlines, worst-case execution time (WCET), latency, jitter, determinism/schedulability.
Objective
Develop a functional prototype of the multilevel platform to confirm scalability without loss of functionality.
(Context: a full build would take several years—for example, the Thales Smart Digital Platform took 3+ years.)
REQUIREMENTS
| 🆔 | 📋 Requirement |
|---|---|
| E1 | Filter non-compliant packets |
| E2 | Inspect packet content |
| EA1 | Passively and centrally log application activity |
| EA2 | Verify the authenticity of packets |
| EA3 | Verify the integrity of packets |
| EM1 | Ensure real-time performance (< 10 ms response time) |
| EI1 | Adhere to secure development standards (state of the art) |
Document ANALysis: GUIDE ON THE DEVELOPMENT OF A MULTILEVEL ARCHITECTURE


??
OK
Document ANALysis: GUIDE ON THE DEVELOPMENT OF A MULTILEVEL ARCHITECTURE

Document ANALysis: NATO's metadata system standard

[]
Document ANALysis: NATO's metadata system standard
[]


Private
1
2
Public
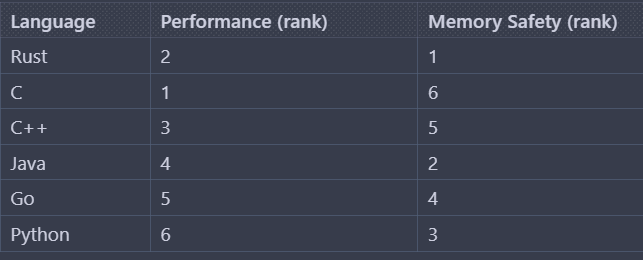
Choice of PROGRAMMING LANGUAGE
the encapsulator & THE PMN
DATA


Metadata
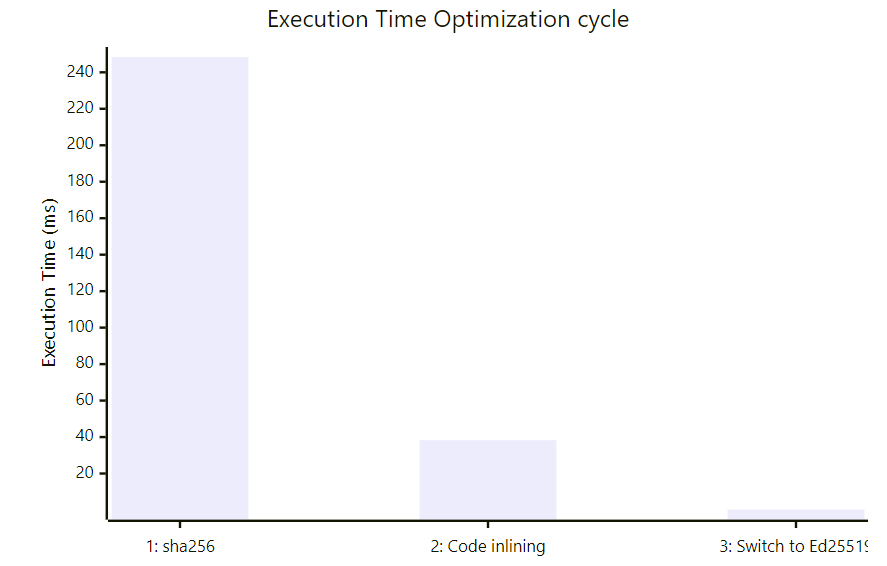
BENCHMARKING