Cybersecurity
M. Rocha
ROP Exploring Computer Science
The rate of growth for jobs in information security is projected at 37% from 2012–2022
Cybersecurity is in High Demand!

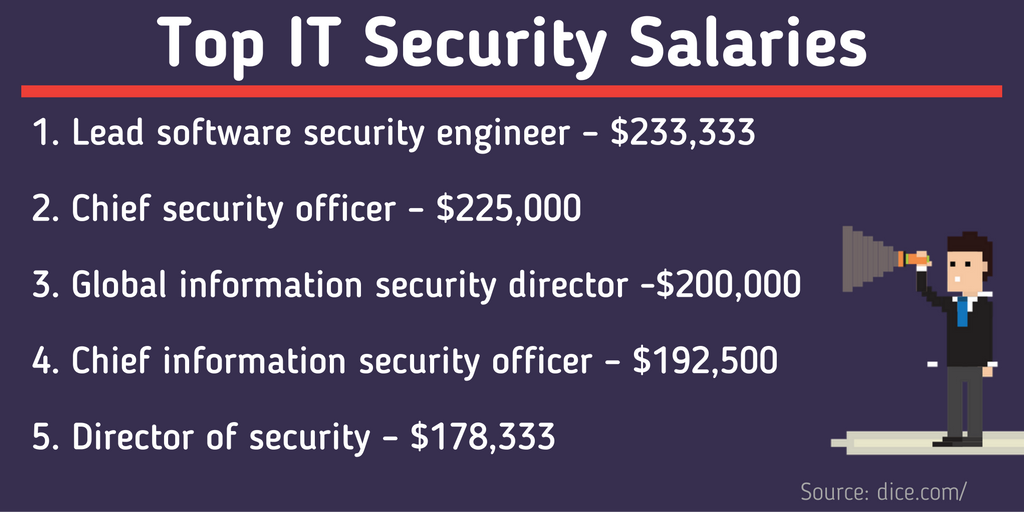
Cybersecurity pays really well!
Cybersecurity is the body of technologies, processes and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access.
Elements of Cybersecurity include:
- Application security
- Information security
- Network security
- Disaster recovery
- Operational security
- End-user education
Cybersecurity Definition
Defensive vs. Offensive Security
Defensive: When time and resources are spent on the protection from already known vulnerabilities and attacks
Offensive: When time and resources are spent discovering new vulnerabilities and exploiting new or known vulnerabilities for security purposes. When exposed to the public with good intentions this becomes Ethical Hacking
Types of Vulnerabilities and Attacks
Exploits
An exploit is a piece of software, a chunk of data, or a sequence of commands that takes advantage of a bug or vulnerability to cause unintended or unanticipated behavior to occur on computer software, hardware, or something electronic (usually computerized). Such behavior frequently includes things like gaining control of a computer system, allowing privilege escalation, or a denial-of-service (DoS or related DDoS) attack
When exploits are known and released to the public the associated vulnerabilities are usually fixed immediately
Exploits unknown to everyone but only the people that found and developed them are referred to as zero day exploits
Vulnerabilities and Exploits Data Bases
As soon as vulnerabilities or exploits are made known to the public they get published in public databases
These databases are the #1 resource for defensive cybersecurity experts, hackers targeting unpatched systems/applications
Learning Cybersecurity for FREE
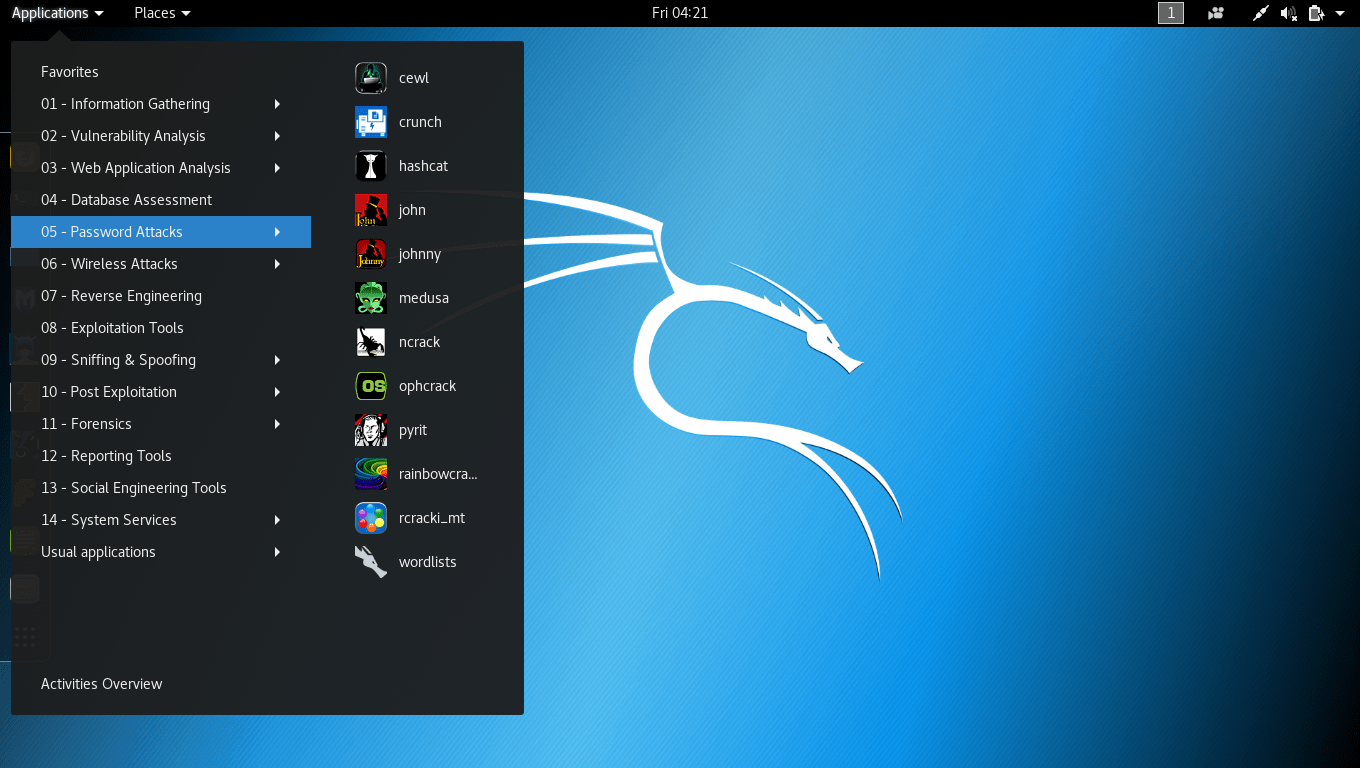
Kali Linux - The Hackers' Swiss Army Knife
Useful Things to Know
Assignment 16
You have two options, complete either one of these or do both for extra credit.