Reality
vs.
CyberSecurity
how to enable
secure, scalable, souvereign
data communication
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024

Dipl. Ing. (FH), MBA
Stephan Schwichtenberg
- founder of pi-lar GmbH 2014
- current focus on Enterprise Architecture // Enterprise Security
- since 2020 speaker of BITMI IT - Security Group
- Over 25 years of working experience in IT projects
- open source development of Neuropil cybersecurity mesh since 2016
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024
Approach:
- only protection of bilateral IP connections
- not protecting different data objects, but systems
- unsuited for rapid change / new data channels
- reduce identified risks one by one
Limitations of Cyber Security
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024
Consequences:
- static design: build once, run forever
- new requirements vs. security design
- introduce security exceptions on change
- vulnerabilities in IT landscape
Limitations of Cyber Security
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024
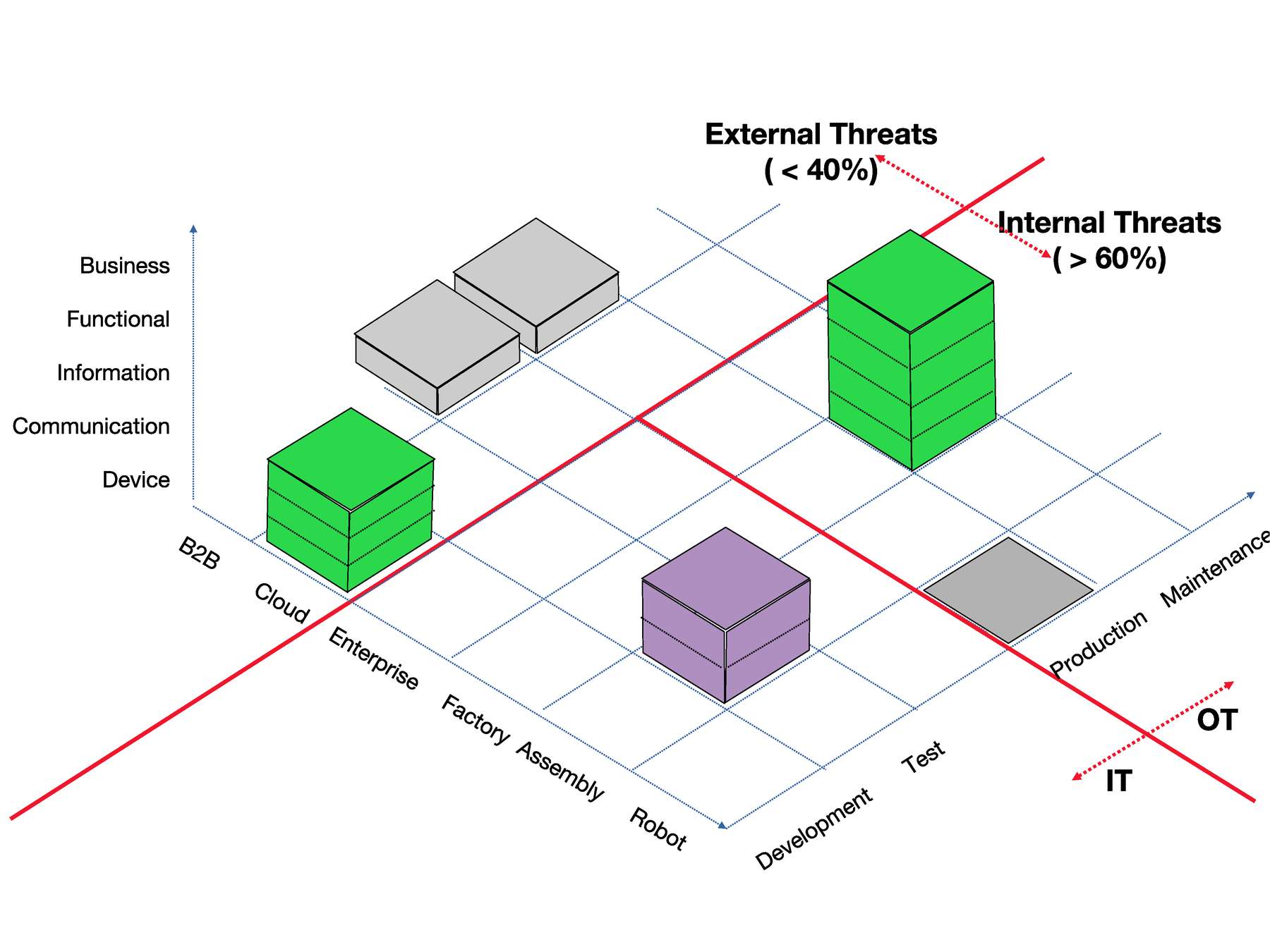
Limitations of Cyber Security
Complexity & Protocol fragmentation:
- B2B: SAML, WS-Security, Security-GW ...
- LAN / Cloud: Basic Auth, TLS 1.x, various cipher suites
- (I)IoT: MQTT, COAP, ZigBee, ZWave, OPC-UA, HomeKit, ...
- User: JWT, X3DH, DPT-3, OAuth, OIDC
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024

Limitations of Cyber Security
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024

Quelle: https://commons.wikimedia.org/wiki/File:Cognitive_bias_codex_en.svg // License CC 4.0
Limitations of Cyber Security
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024
Zero Trust Architectures
- no trust perimeter, everything is a gateway
- fragmented information (flows) need protection
- authn/authz must be possible everywhere
- data objects governed by attribute basex access control (ABAC)















Inspiration by

Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024
Named Data Networks
- replace IP / DNS networks with named data channels
- automatically adds data provenance / integrity
- evolution to distribution networks
- removes inefficent middleware technologies
IP
Hash
IP
Inspiration by
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024
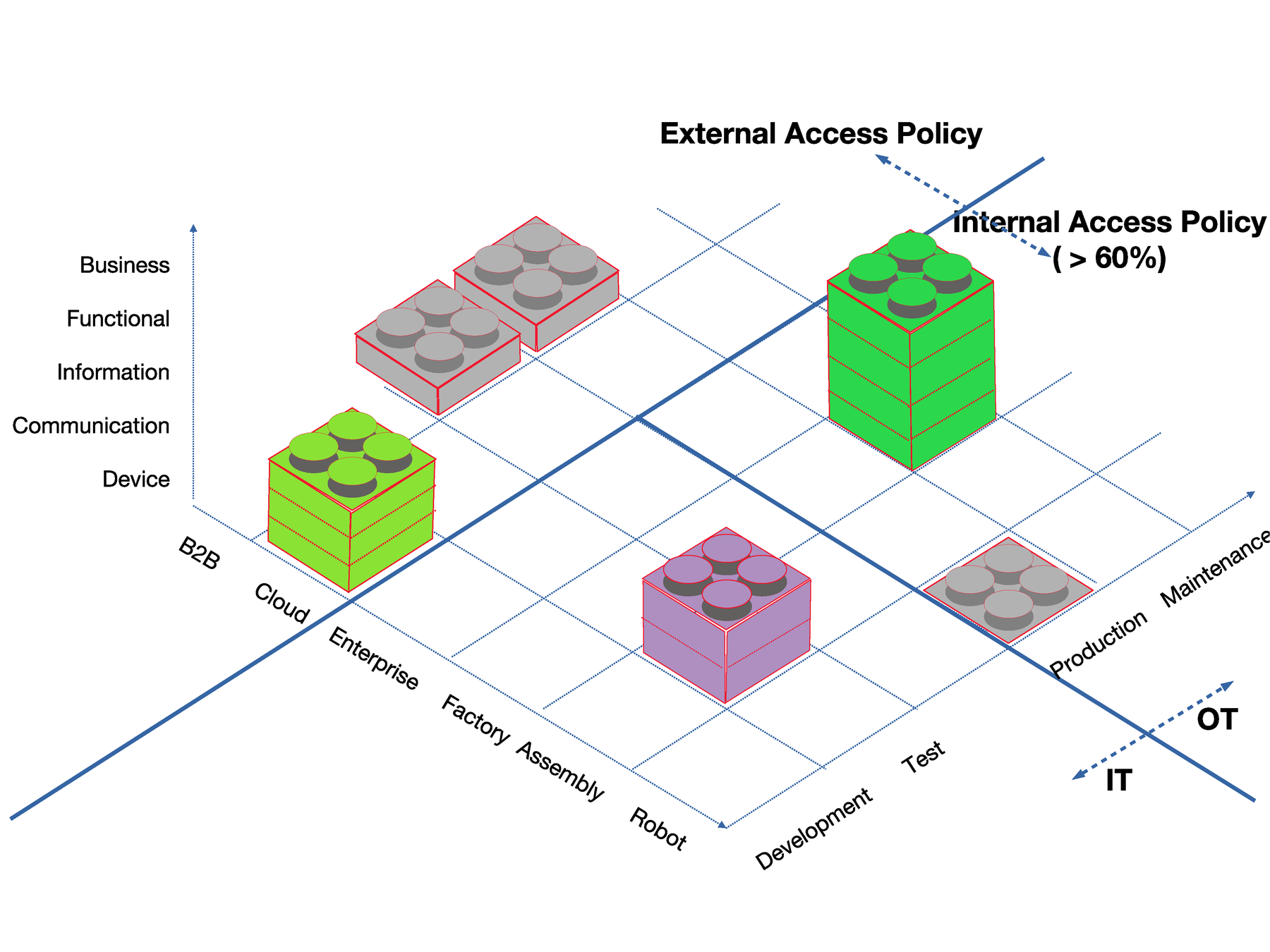
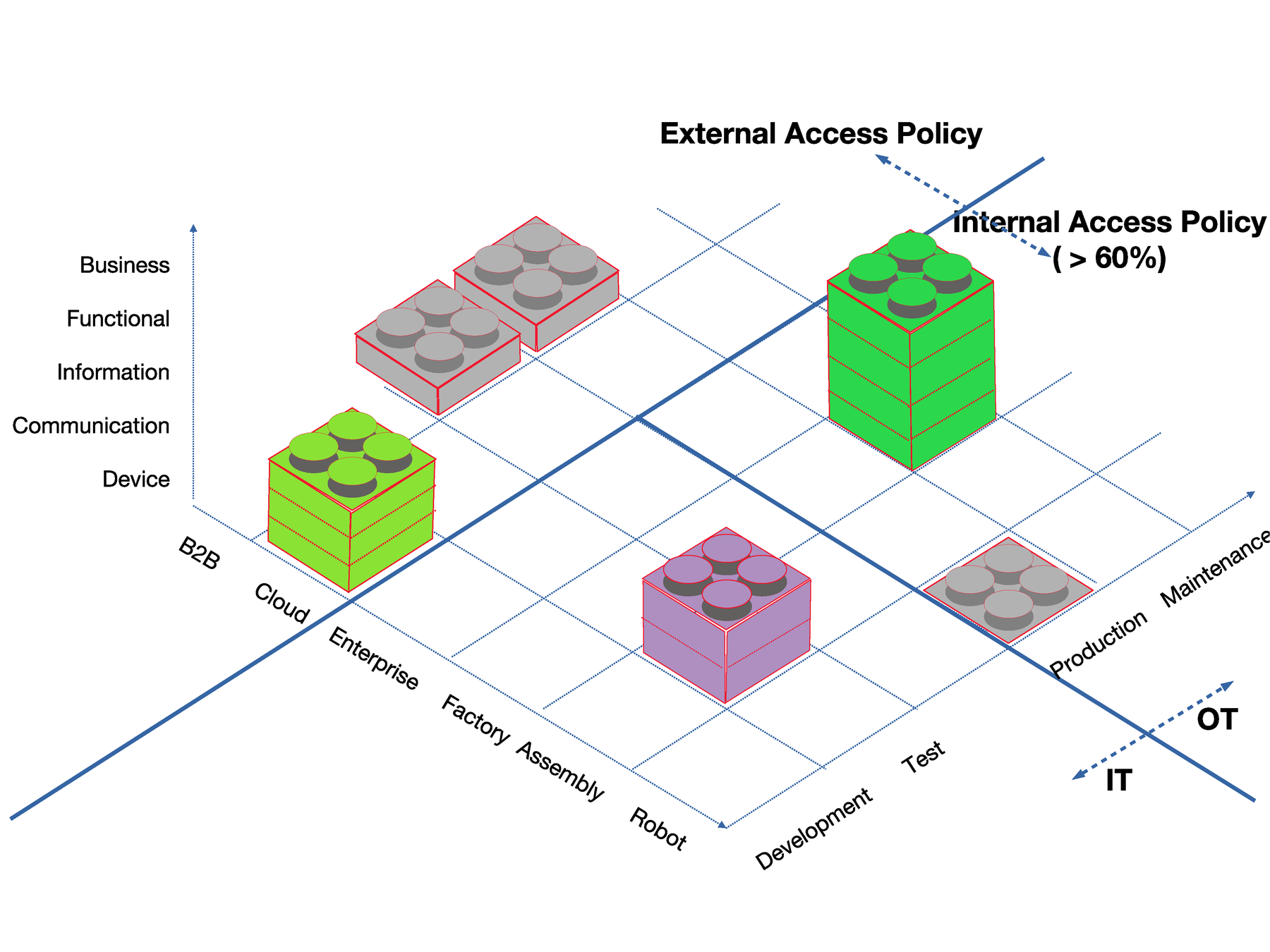
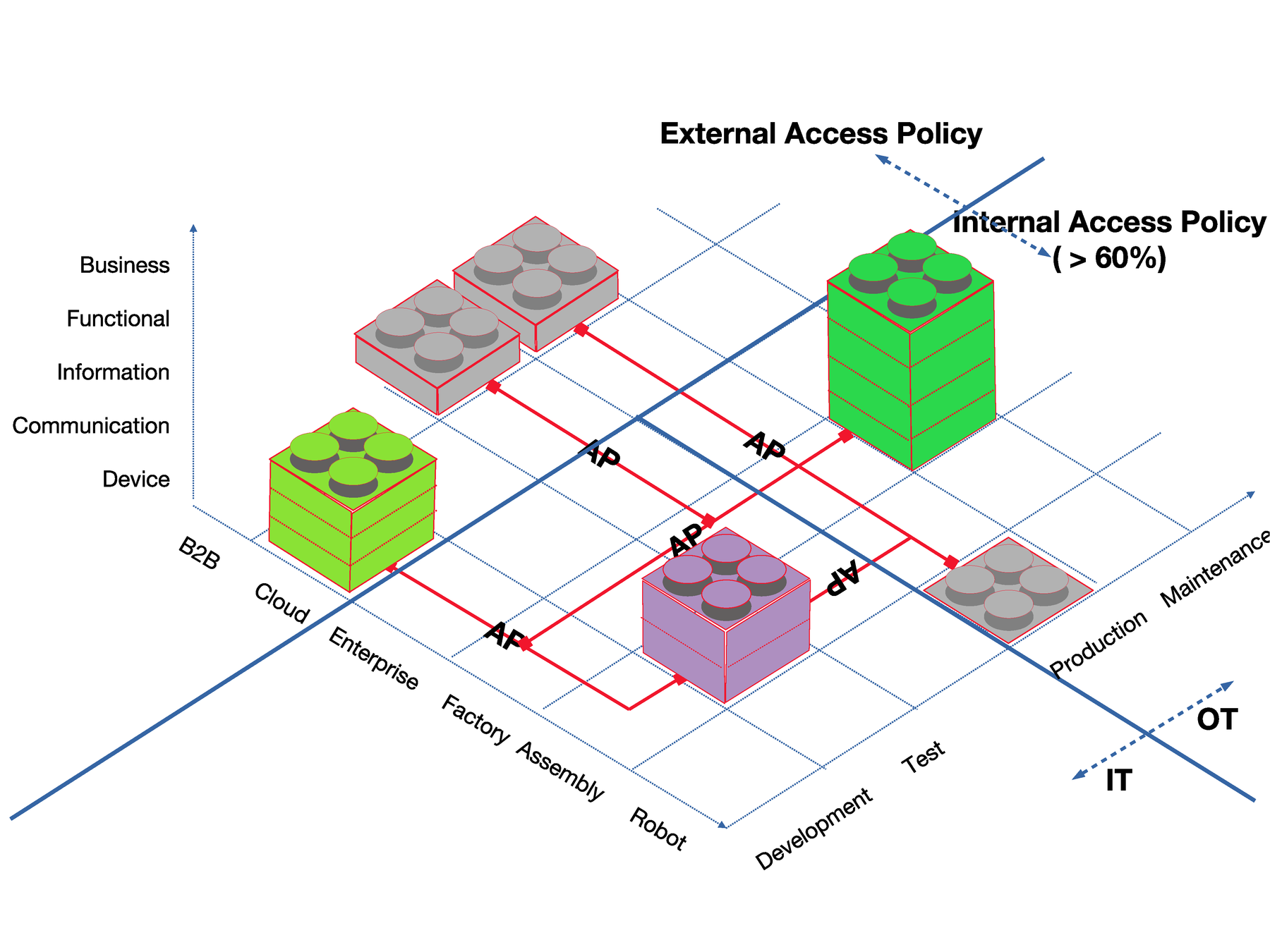
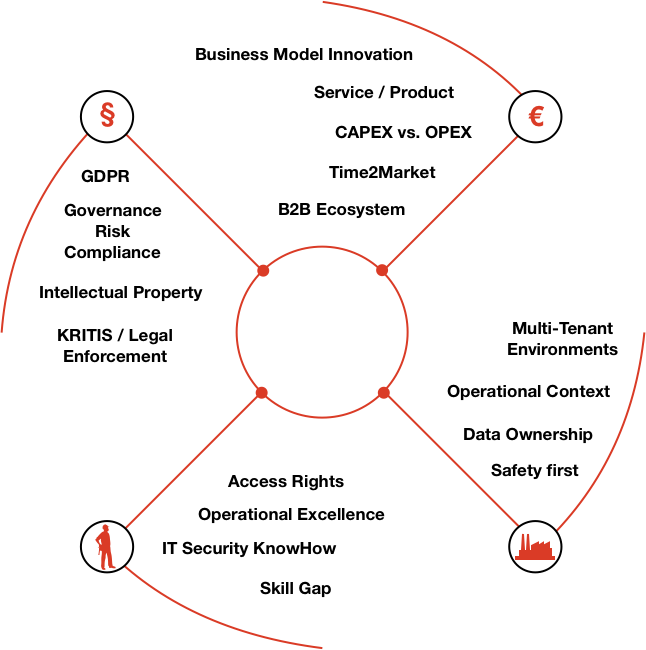
Secure IDSA dataspaces
- data interactions are the driver of future IT architectures
- devices produce and consume data with different IDSA roles
- respect several data owners per device
- end-to-end process B2B integration

Inspiration by
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024

Enterprise Security Architecture
Inspiration by
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024
- Digital Identity: information about an entity used to represent persons, organizations, applications, devices. ISO/IEC 24760-1 defines identity as "set of attributes related to an entity"
- SSI (Self Sovereign Identities): a user has a mean to generate, control and add unique information / identifiers
- Disposable Yet Official Identities: a user has a mean to generate, control and use pseudonyms for different purposes
- Organizations use and verify digital identities for authentication and authorization & accounting
Inspiration by
Self-Sovereign Identities
Issuer
Holder
Verifier
signs claim
countersign
verify claim
present
issue
decentralized data access
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024
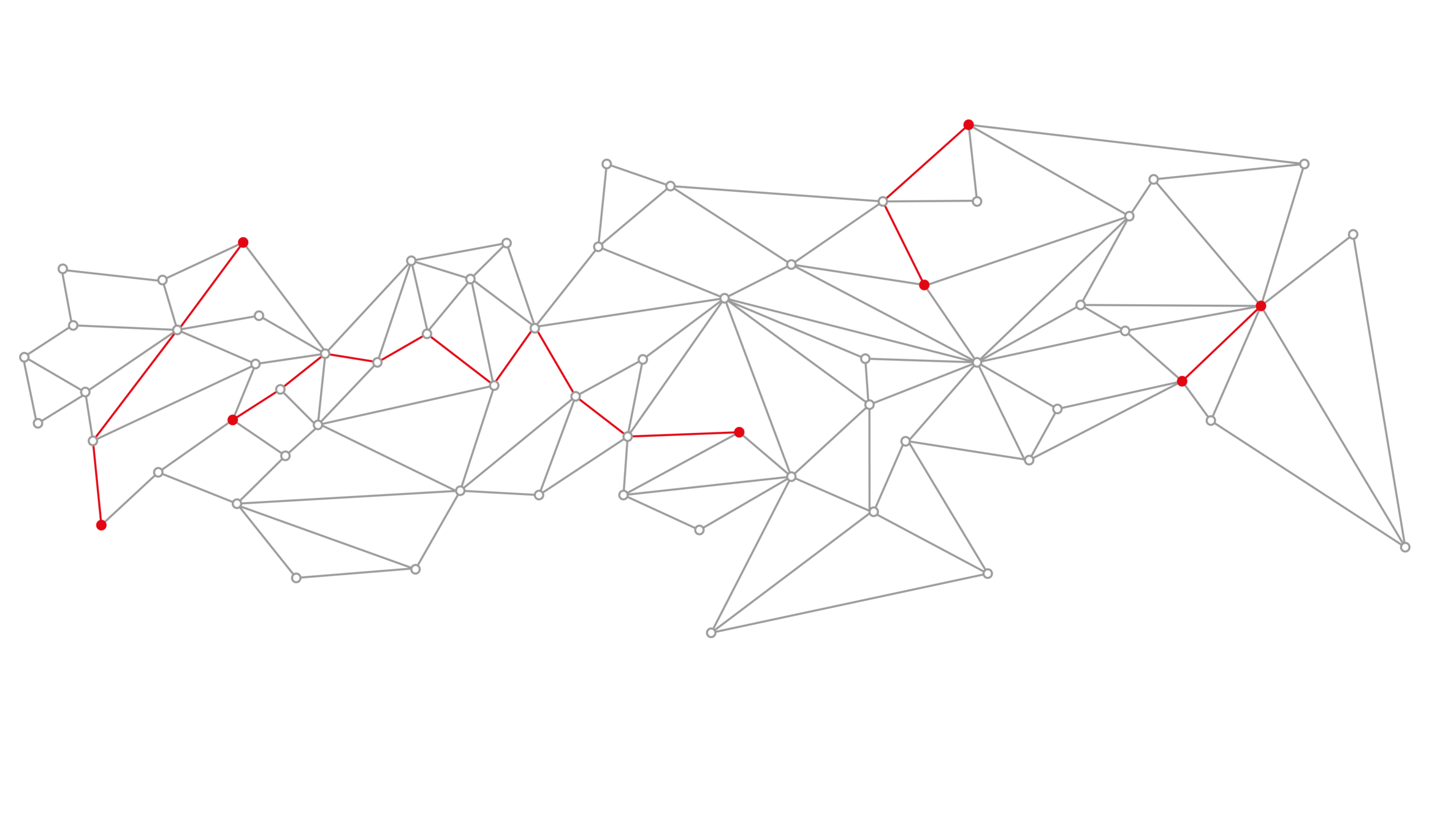
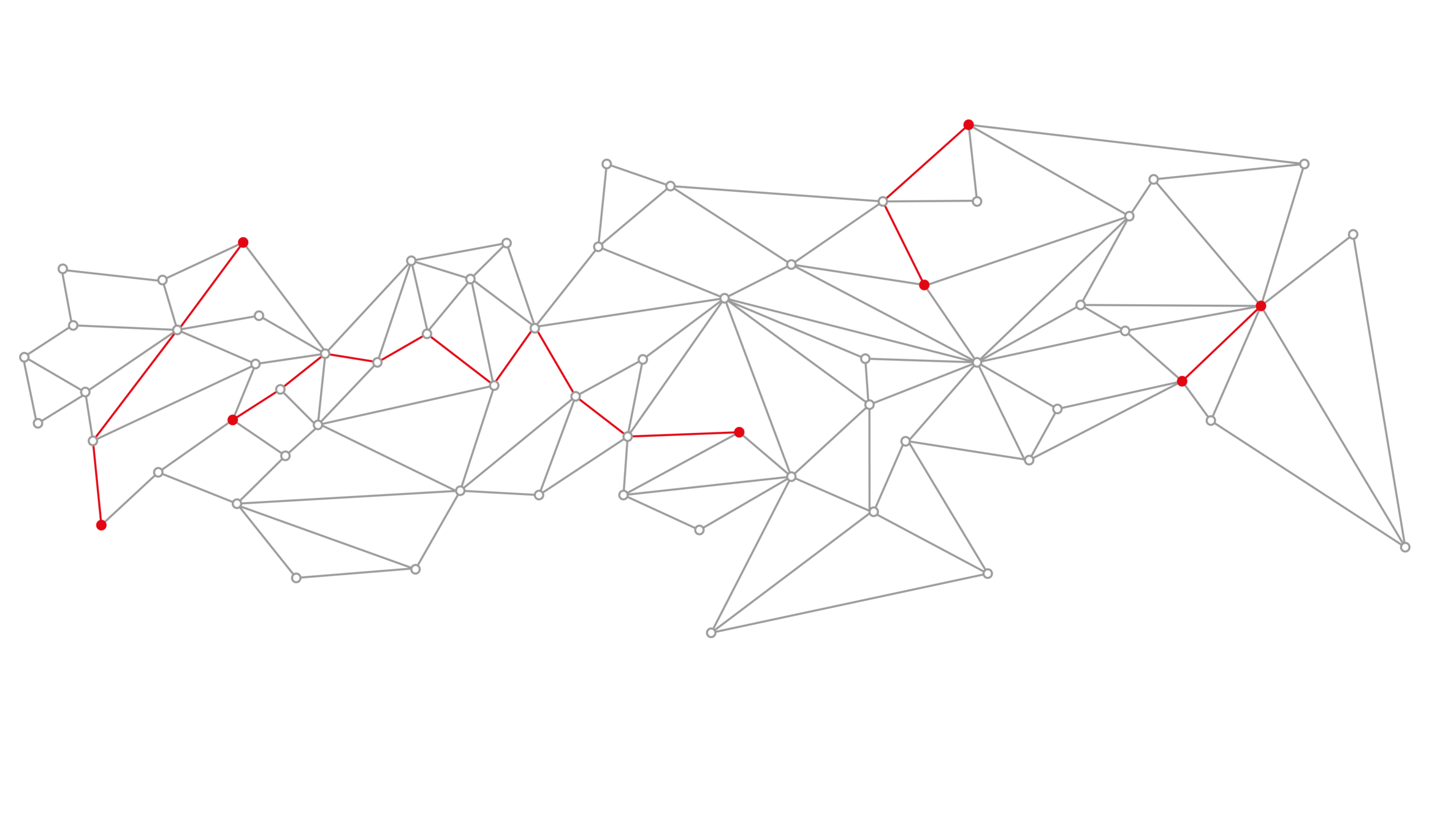
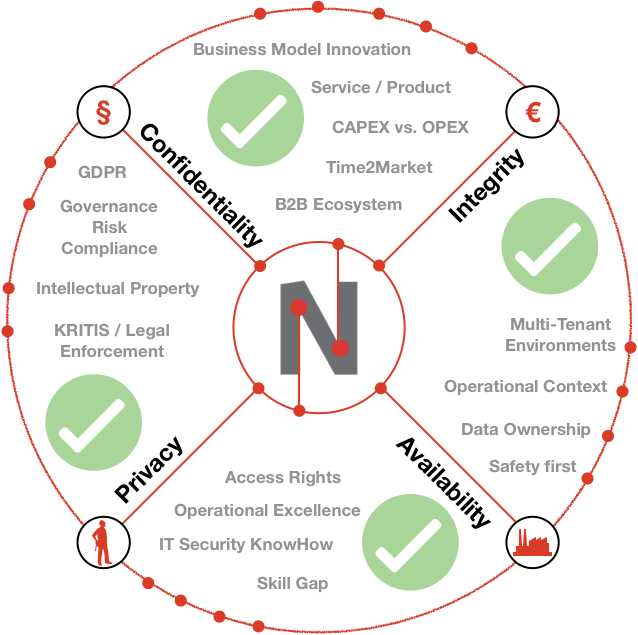
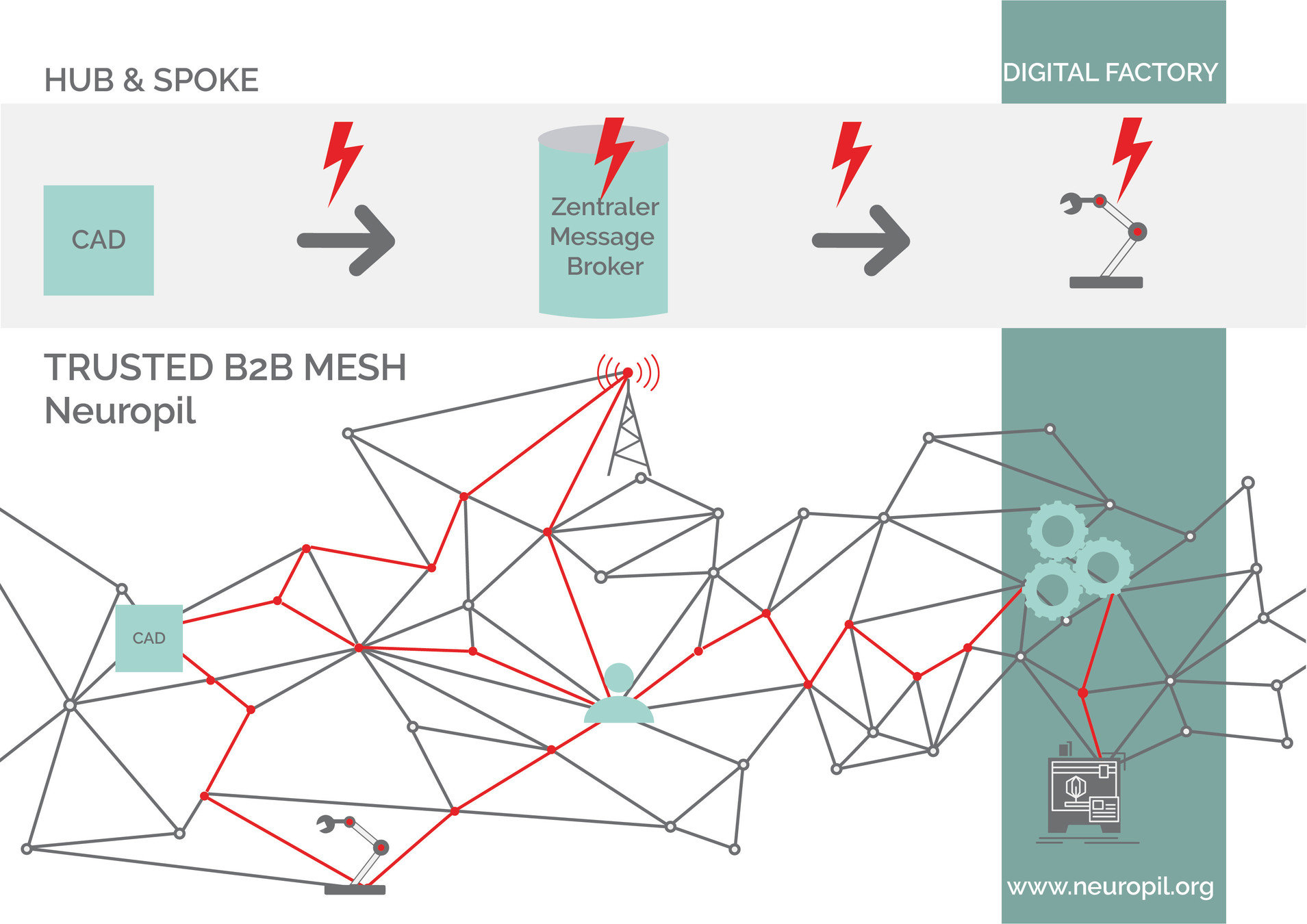
Security of the Future: ZeroTrust
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
Future Cyber Security
defines trust levels for data objects / smaller groups
fine grained access to objects possible
more insights means minimizing risk
Never trust, always verify
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
A composable and scalable approach to extending security controls, even to widely distributed assets. It's flexibility is especially suitable for increasingly modular approaches consistent with hybrid multi-cloud architectures.
Gartner
- As organizations grow beyond a physical location, each node becomes a potential access point that can be exploited to compromise the whole network.
- Hackers increasingly use these vulnerable access points to deploy cyberattacks such as ransomware and other forms of malware. Losses due to such attacks are continuedly rising each year.
neuropil® - CyberSecurity Mesh
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024
Identity
H(I1)
Node
H(N1)
Data
Node
H(N2)
Data
Identity
H(I2)
neuropil® - data owners decide
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024
Identity
H(I1)
Node
H(N1)
Subject
Node
H(N2)
Subject
Identity
H(I2)
+ attributes
+ attributes
tcp/udp/ip/pas
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
neuropil® - access control
Identity
Node
+ attributes
- Mesh is based on random digital identities
- Peer discovery is running automagically
- Only IHT message allowed, no real content
Node
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
neuropil® - building the mesh
Identity
Node
Subject
e2e session
+ attributes
+ attributes
- Connections can be established via countless paths
- Communicate with more than two identities
- Discovery and establishment is almost untraceable
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
neuropil® - Connectivity
Identity
Node
Subject
Identity
Node
Subject
e2e session
+ attributes
+ attributes
+ attributes
+ attributes
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
neuropil® - CyberSecurity Mesh
neuropil® - CyberSecurity Mesh
-
secure, scalable, souvereign data integration
-
c-library, runs anywhere, footprint 1MB
-
DHT allows enforcement of good security practice
-
modern cryptographic algorithms / data protection
-
needs integration into products
-
Python binding available
-
implementation as a side car proxy
-
- not a fully implemented IDSA connector
- open source since 2016
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024
neuropil® - Security First
Security First
-
SSI / digital identities (OIDC)
-
dual encryption layer (transport and end-to-end)
-
attribute based access control
-
decentralized access delegation
-
object level permissions via security token
-
limit packet size / throughput
-
standardized security measures (OSI Layers 1-7)
-
... and more
(see also: OWASP API Security)
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
- stacked/pseudonymized identities
- transport layer privacy / source anonymity
- addressing and discovery is hash based (Blake2b)
- DHT to protect from metadata discovery
- "blind" broker nodes
- stay secure behind closed firewalls
- packet fragmentation
- disposible identities
- ... and more
(see also: OWASP Privacy risks)
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
neuropil® - Privacy First
2016
2019
2020
2021
2022
open source
NGI Zero funding
Beta release
HM 2020 exhibition
NGI Assure: LDTS / DTP
production ready
Fed4Fire: scaleup testbed
Gartner: CyberSecurity Mesh
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
neuropil® - Roadmap
NGIZero: Distributed Search
Neuropil is a project that wants to turn the tables on online search and discovery: instead of search solutions calling the shots, data owners decide what content is publicly searchable in the first place.
They can do this through their cybersecurity mesh that is private and secure by design. Data owners can send cryptographic and unique so-called intent messages that state what specific information can be found where.
The access to the actual information or content is also controlled by data owners, for instance to provide either paid or public free content.


Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024

bm25 - 5kmer - space
org-science-AI space
H256(X)
0...
8...
4...
c...
your-private space
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
NGIZero: Distributed Search
NGIAssure: Distributed Governance
The neuropil cybersecurity mesh will be updated to a first production ready release. Two new concepts will be integrated:
Distributed Time: A decentralized approach to the concept of "time" as a fundamental building block for any IT landscape will be incorporated into the cybersecurity mesh.
Democratic Access Control: By introducing the four conceptual roles of judicial, legislative, executive and informational entities the project lays down the foundation for an faster and easier exchange of cybersecurity information throughout the enterprise

Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024

CyberResilience Superpowers
- virtual / public / protected / private data channels
- everything is a VPN connection
- verifiable environments on startup
- integrated data provenance and data ownership
- key management / truly passwordless setups
- hybrid WoT / PKI settings
- hybrid cloud integration
- distributed enterprise search
- easier release management
- By Design: Zero Trust Architecture
- ... and more
neuropil® - CyberSecurity Mesh
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024
partnership / use cases

- collaboration on / realization of several use cases
- added-value of the IDSA data model, distributed discovery
- run IDSA connector even on small devices
- ecosystems of partners / presentation at the plugfest
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
Our Bootcamp: Hackathon
- real world use case packed into a hackathon
- participants take on roles / code an common target
- target: fully functional architecture at the end
- target: all security goals achieved

Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
neuropil® - looking for partners
neuropil.org
Protocol Definition
Governance
neuropil.io
Protocol Implementation
Core Services
neuropil.com
Business Projects
Data Services
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
OpenCollective Funding
Governance base on Democratic Access Control
- joint development / training setup
- open source development / use cases
- open for master / bachelor thesis topics
- contact: eliza@neuropil.org / marvin@neuropil.org
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
neuropil® - open for feedback
contact: info@pi-lar.net
questions / feedback ?
Reality vs. CyberSecurity - Digitaltag Köln Unternehmen 11.06.2024
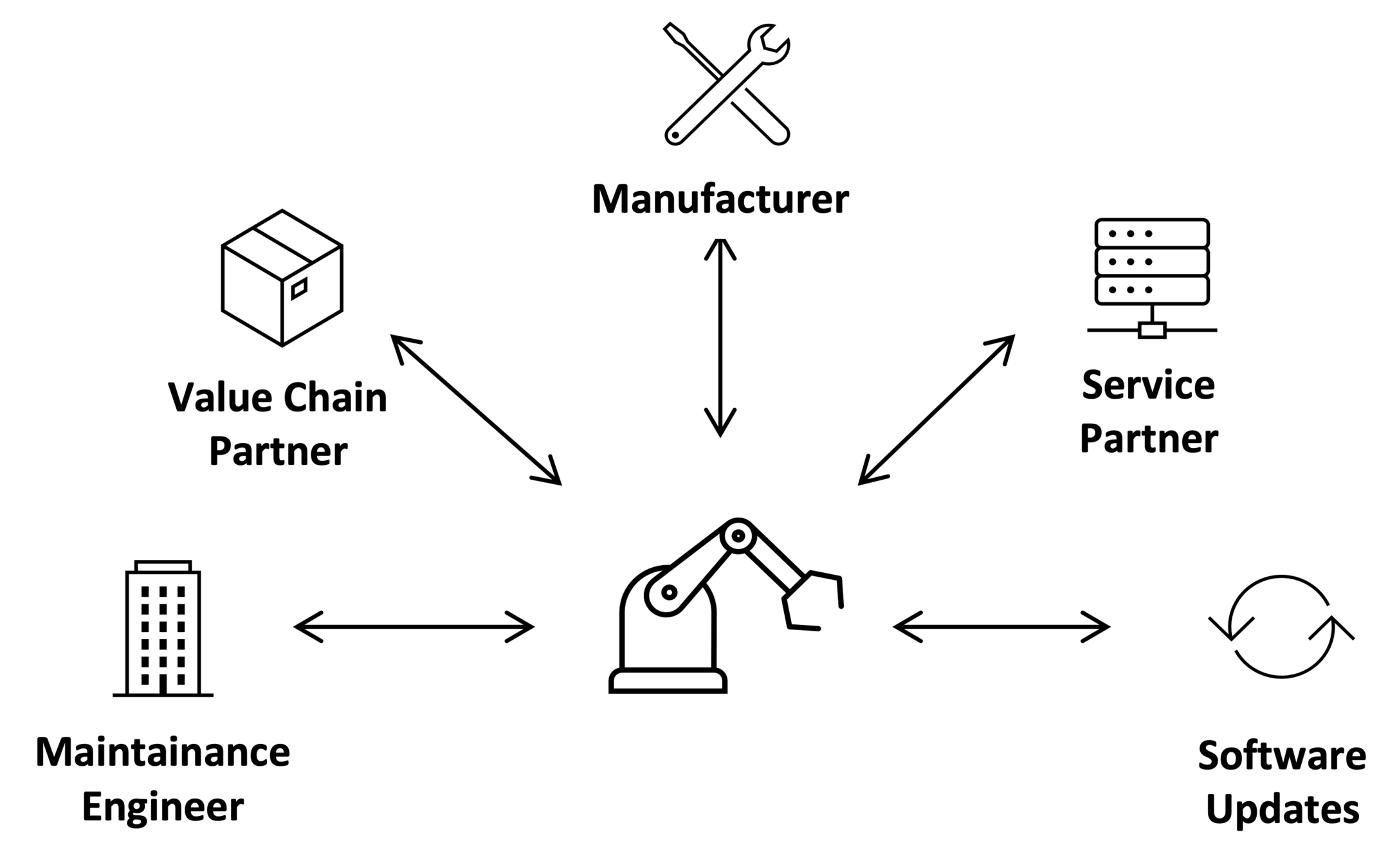
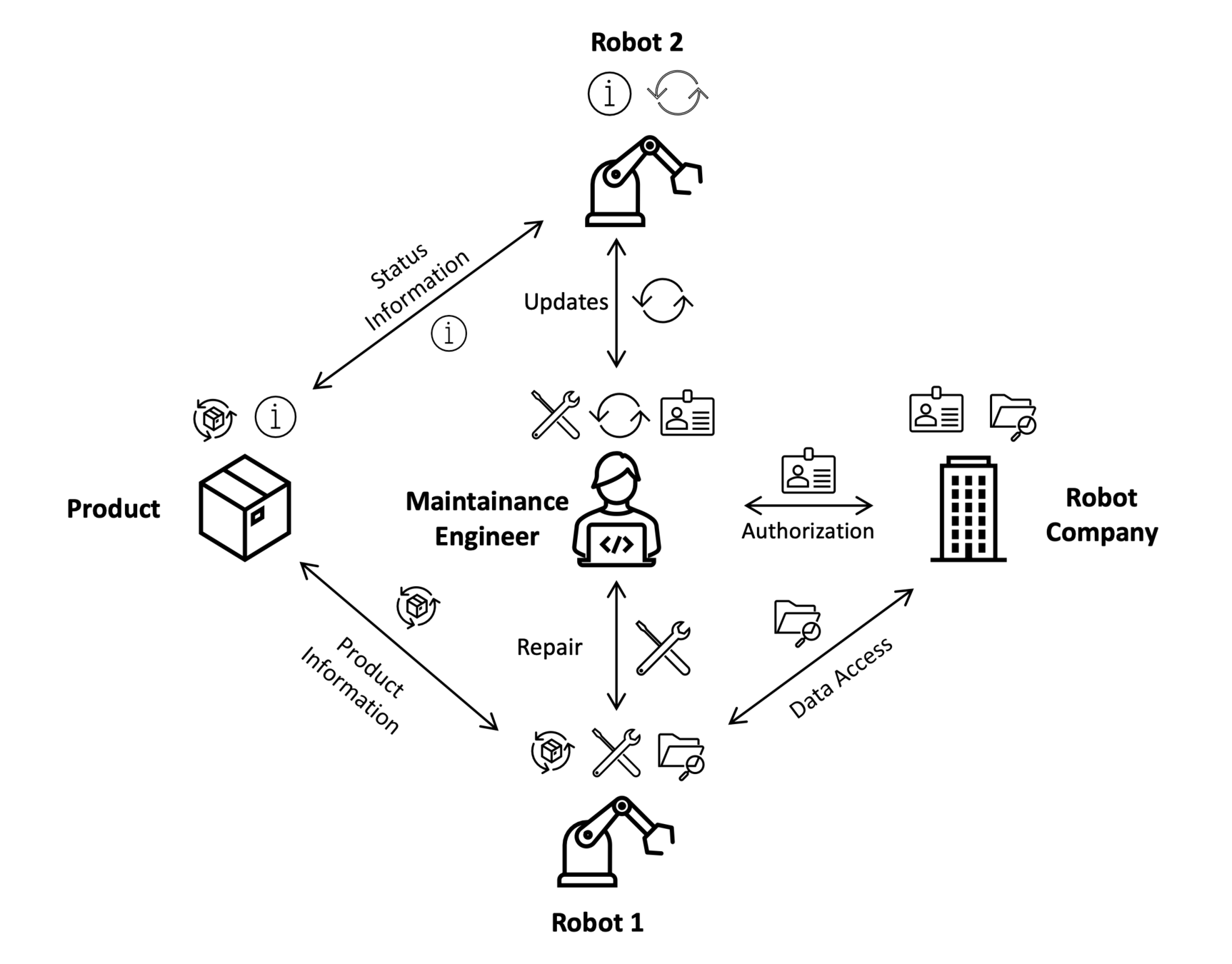
Security for complex Ecosystems:
Zero Trust / IDSA / AccessPolicies
data object interactions main driver for future IT architecture
devices produce and consume data at the same time
respect different data owners per device
if one fails, all suffer!
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
Security of Ecosystems:
Zero Trust / IDSA / AccessPolicies
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
Security of Ecosystems:
Zero Trust / IDSA / AccessPolicies
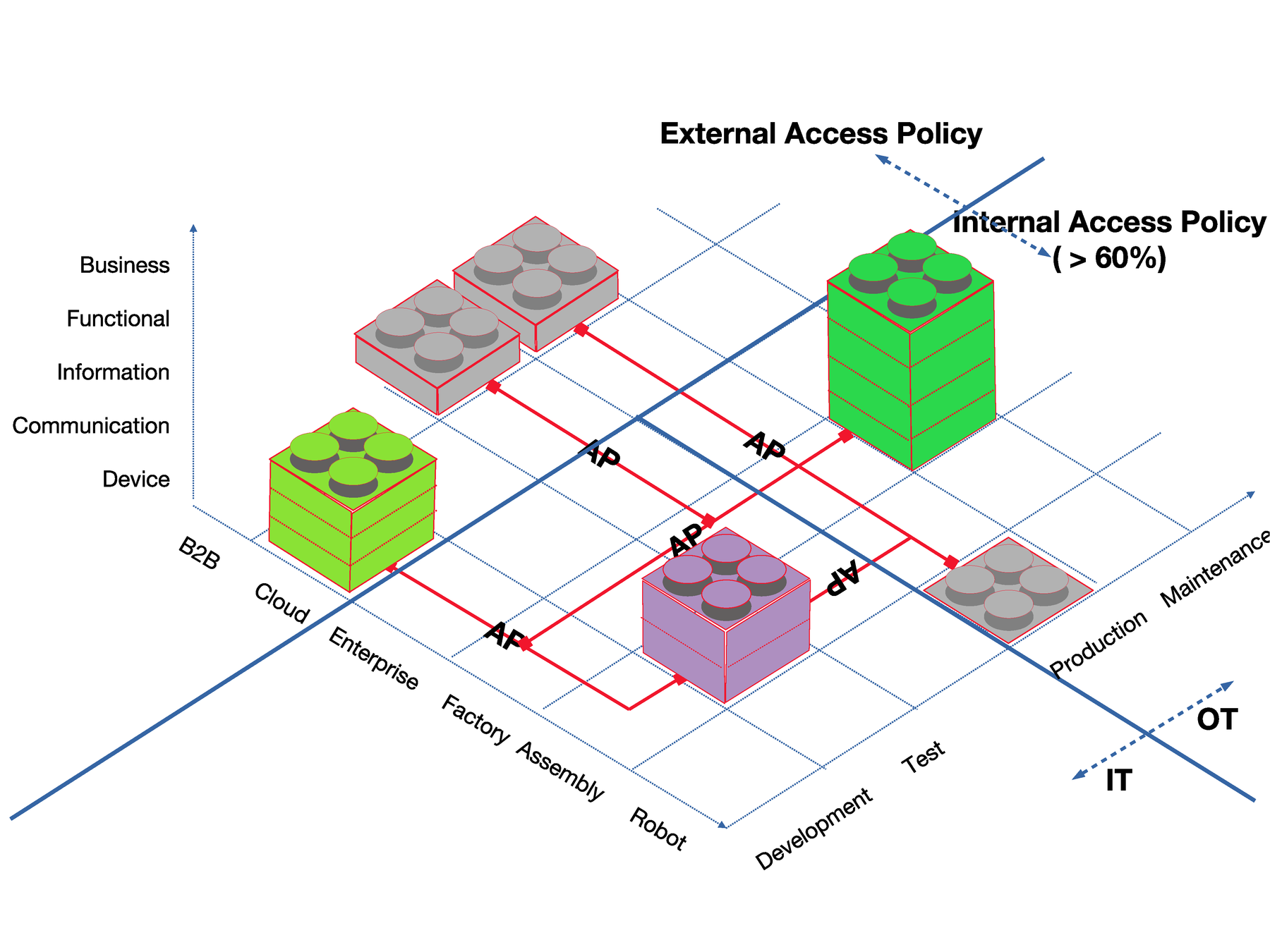
business agility: enables your company to adapt and survive
switch to a different service provider is easy
change policies in days (rather than months)
enables data reduction and data economy
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
Reliability
Legal
Economic
Environment
Social
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
Reality vs. CyberSecurity - IT-Forum FZ Jülich - 27.02.2024
Our Approach

www.neuropil.org
The first decentralized
open-source
messaging protocol
with security and privacy
by design
Benefits
messaging & security protocol for ecosystems
benefit for easy data sharing with full control over data flows
open source development to establish trust
apply end-to-end principle for data objects
Milestones
development started in 2014
2016: first exhibition @FROSCON
2019: NGI Zero / EU funded
2020: market-ready HMI 2020
IDSA certification & looking for partners
Security First:
digital identities
dual encryption layer
attribute based access control
decentralized access delegation
... and more
Privacy First:
stacked identities (realm / audience)
addressing hash based
DHT to protect metadata discovery
... and more
Easy to use
installed as a OS library
connect once, communicate globally
python / lua binding available
identity / data based routing
... and more
no more gateways
decentralized
P2P networks
decentralized
P2P networks
Trusted B2B mesh network
Benefits
stay secure behind closed firewalls
standardized security measures
limit packet size / throughput
"blind broker" nodes
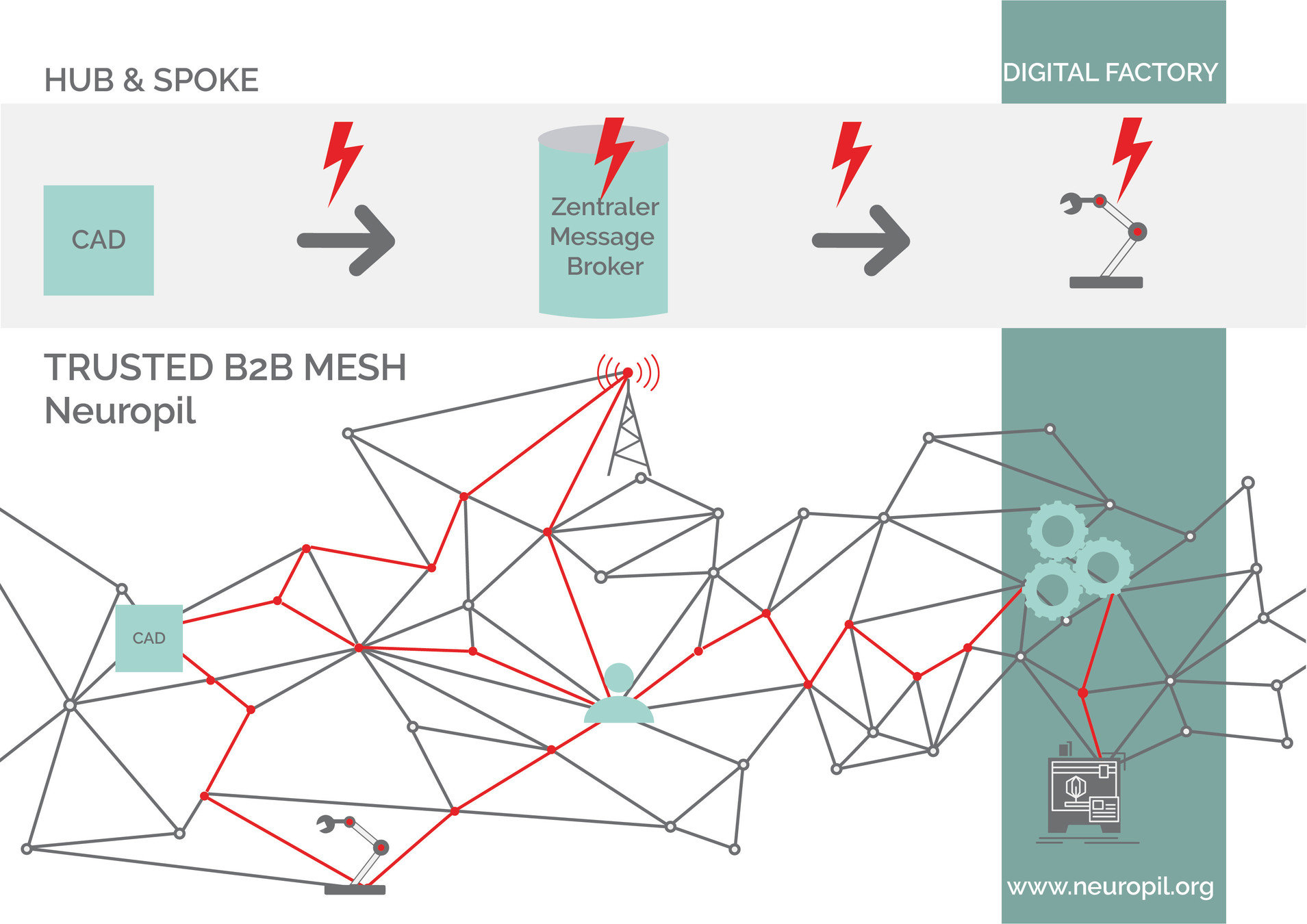
Trusted B2B mesh network
connects everything:
devices, edge, processes,
applications, users, enterprises
...
neuropil & IDSA
why we joined:
rules to enforce data ownership / sovereignty
increase data quality and transparency
building european-wide ecosystems
neuropil & IDSA
neuropil@IDSA
decentralized (meta-data) broker
each application/device is a connector
decentralized MQTT
neuropil & IDSA
how to contribute to IDSA:
identity federation
resilience
high availability
e2e encrypted pub/sub streams
neuropil & IDSA
what's going on:
data models / participation in plugfest
governance model (idsa.neuropil.io ?) / IDS ready certification
mutual ongoing development / collaboration
Use Cases
Use Case:
On the horizon
"Boring Bookkeeping"
"Traveling around the world"
"Healthy Healthcare"

Let's
chat!