Neuropil®
Open Source
CyberSecurity Mesh
enabler for
secure, scalable, souvereign
data communication
Designed // Created by


Security of the Past: Limitations
only protection of bilateral IP connections
not protecting different data objects, but apis
unsuited for rapid change of data owners / new data channels
Meet Eliza & Marvin
Security of the Past: Limitations
Security of the Past: Limitations
static design: build once, run forever
new requirements vs. security design
introduce security exceptions on change
neuropil® - CyberSecurity Mesh
-
secure, scalable, souvereign data integration
-
c-library, runs anywhere, footprint 1MB
-
DHT allows enforcement of good security practice
-
modern cryptographic algorithms / data protection
-
needs integration into products
-
Python binding available
-
implementation as a side car proxy
-
- not a fully implemented IDSA connector
Zero Trust Architectures
- no trust perimeter, everything is a gateway
- fragmented information (flows) need protection
- authn/authz must be possible everywhere
- data objects governed by attribute basex access control (ABAC)















inspired by

Named Data Networks
- replace IP / DNS networks with named data channels
- automatically adds data provenance / integrity
- evolution to distribution networks
- removes inefficent middleware technologies
IP
Hash
IP
inspired by

Enterprise Security Architecture
inspired by
Enterprise Security Architecture
Reliability

Availability
inspired by
Secure IDSA dataspaces
- data interactions are the driver of future IT architectures
- devices produce and consume data with different IDSA roles
- respect several data owners per device
- end-to-end process B2B integration

inspired by
neuropil® - CyberSecurity Mesh
Security First
-
SSI / digital identities (OIDC)
-
dual encryption layer (transport and end-to-end)
-
attribute based access control
-
decentralized access delegation
-
object level permissions via security token
-
limit packet size / throughput
-
standardized security measures (OSI Layers 1-7)
-
... and more
(see also: OWASP API Security)
neuropil® - CyberSecurity Mesh
Privacy First
- stacked/pseudonymized identities
- transport layer privacy / source anonymity
- addressing and discovery is hash based (Blake2b)
- DHT to protect from metadata discovery
- "blind" broker nodes
- stay secure behind closed firewalls
- packet fragmentation
- disposible identities
... and more
(see also: OWASP Privacy risks)
Security of the Future: ZeroTrust
Security of the Future: ZeroTrust
defines trust levels for data objects / smaller groups
fine grained access to objects possible
more insights means minimizing risk
Never trust, always verify
building secure connectivity
Identity
H(I1)
Node
H(N1)
Subject
Node
H(N2)
Subject
Identity
H(I2)
building secure connectivity
Identity
H(I1)
Node
H(N1)
Subject
Node
H(N2)
Subject
Identity
H(I2)
+ attributes
+ attributes
tcp/udp/ip/pas
neuropil® - CyberSecurity Mesh
Identity
Node
+ attributes
- Mesh is based on random digital identities
- Peer discovery is running automagically
- Only IHT message allowed, no real content
Node
neuropil® - CyberSecurity Mesh
Identity
Node
Subject
Identity
Node
Subject
e2e session
+ attributes
+ attributes
+ attributes
+ attributes
neuropil® - CyberSecurity Mesh
Identity
Node
Subject
e2e session
+ attributes
+ attributes
- Connections can be established via countless paths
- Communicate with more than two identities
- Discovery and establishment is almost untraceable
Roadmap
2016
2019
2020
2021
2022
open source
NGI Zero funding
Beta release
HM 2020 exhibition
truzzt participation
NGI Assure: LDTS / DTP
production ready
Fed4Fire: scaleup testbed
Gartner: Cybersecurity Mesh
NGIZero: Distributed Search
Neuropil is a project that wants to turn the tables on online search and discovery: instead of search solutions calling the shots, data owners decide what content is publicly searchable in the first place.
They can do this through a new messaging layer that is private and secure by design. Data owners can send cryptographic and unique so-called intent messages that state what specific information can be found where.
The access to the actual information or content is also controlled by data owners, for instance to provide either paid or public free content.


partnership / use cases

- collaboration on / realization of several use cases
- added-value of the IDSA data model, distributed discovery
- run IDSA connector even on small devices
- ecosystems of partners / presentation at the plugfest
Our Bootcamp: Hackathon
- real world use case packed into a hackathon
- participants take on roles / code an common target
- target: fully functional architecture at the end
- target: all security goals achieved

neuropil® - is looking for partners
neuropil.org
Protocol Definition
Governance
neuropil.io
Protocol Implementation
Core Services
neuropil.com
Business Projects
Data Services
neuropil® - is looking for partners
- joint development / training setup
- open source development / use cases
- open for master / bachelor thesis topics
- contact: eliza@neuropil.org / marvin@neuropil.org
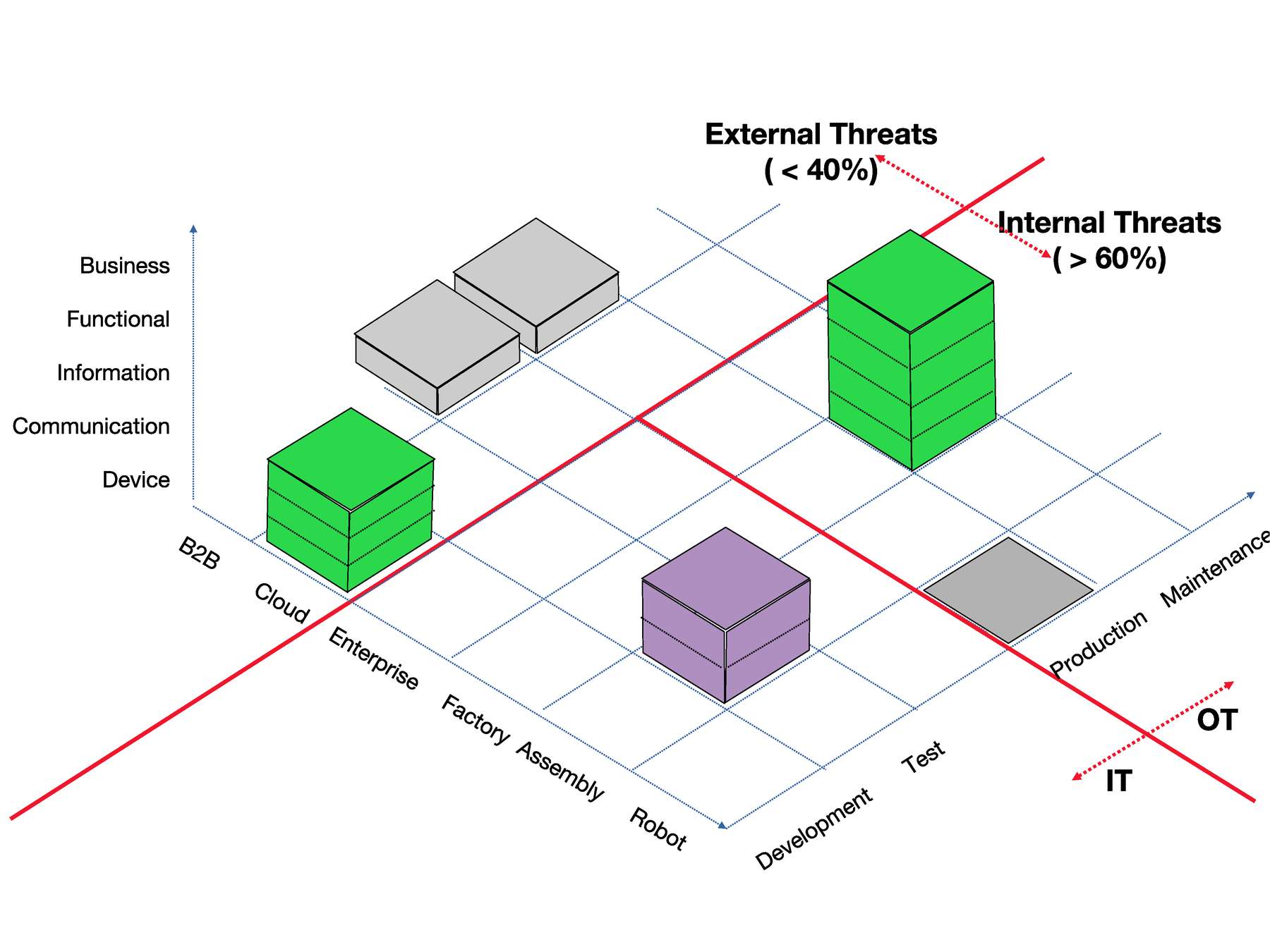
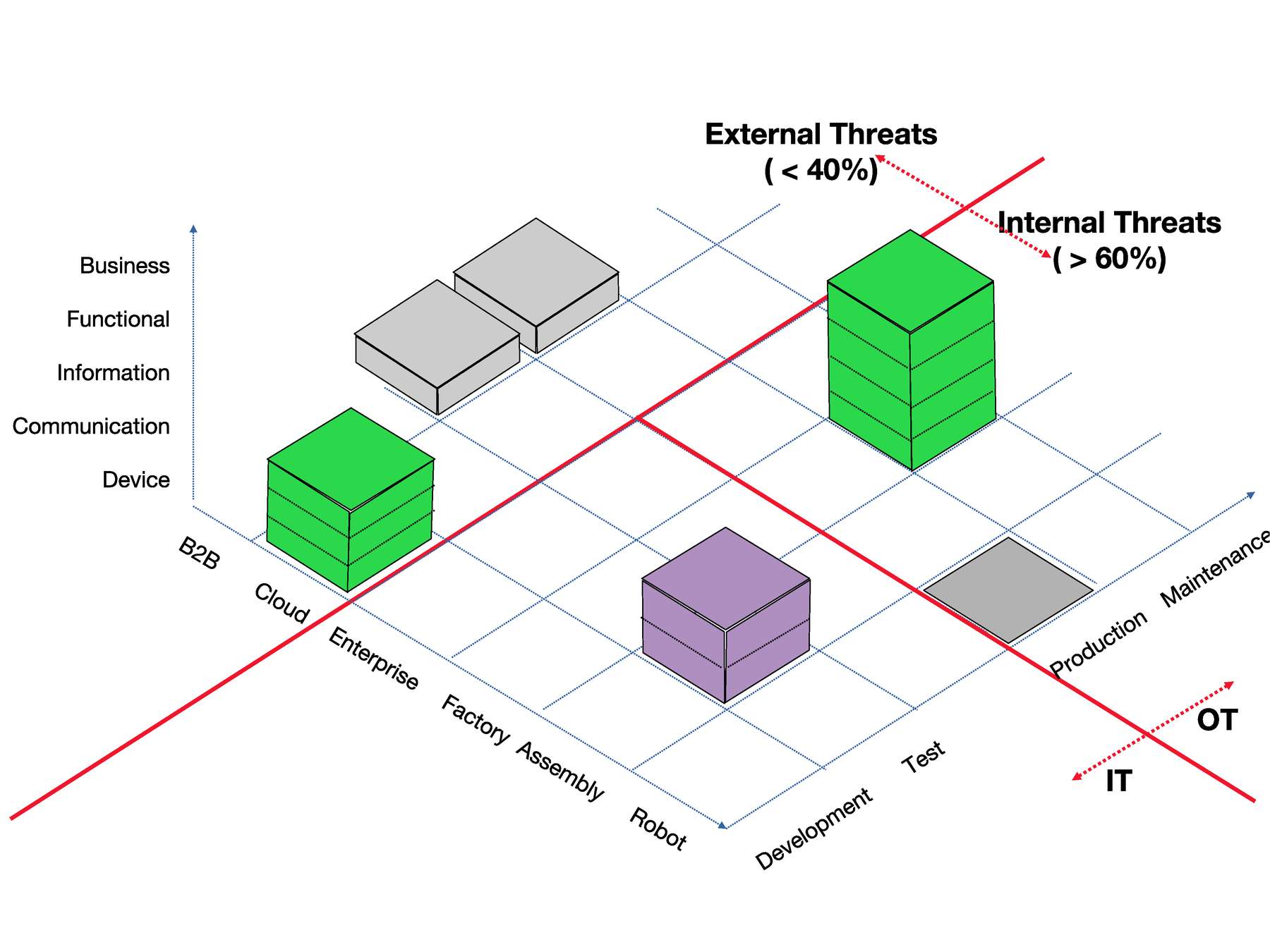
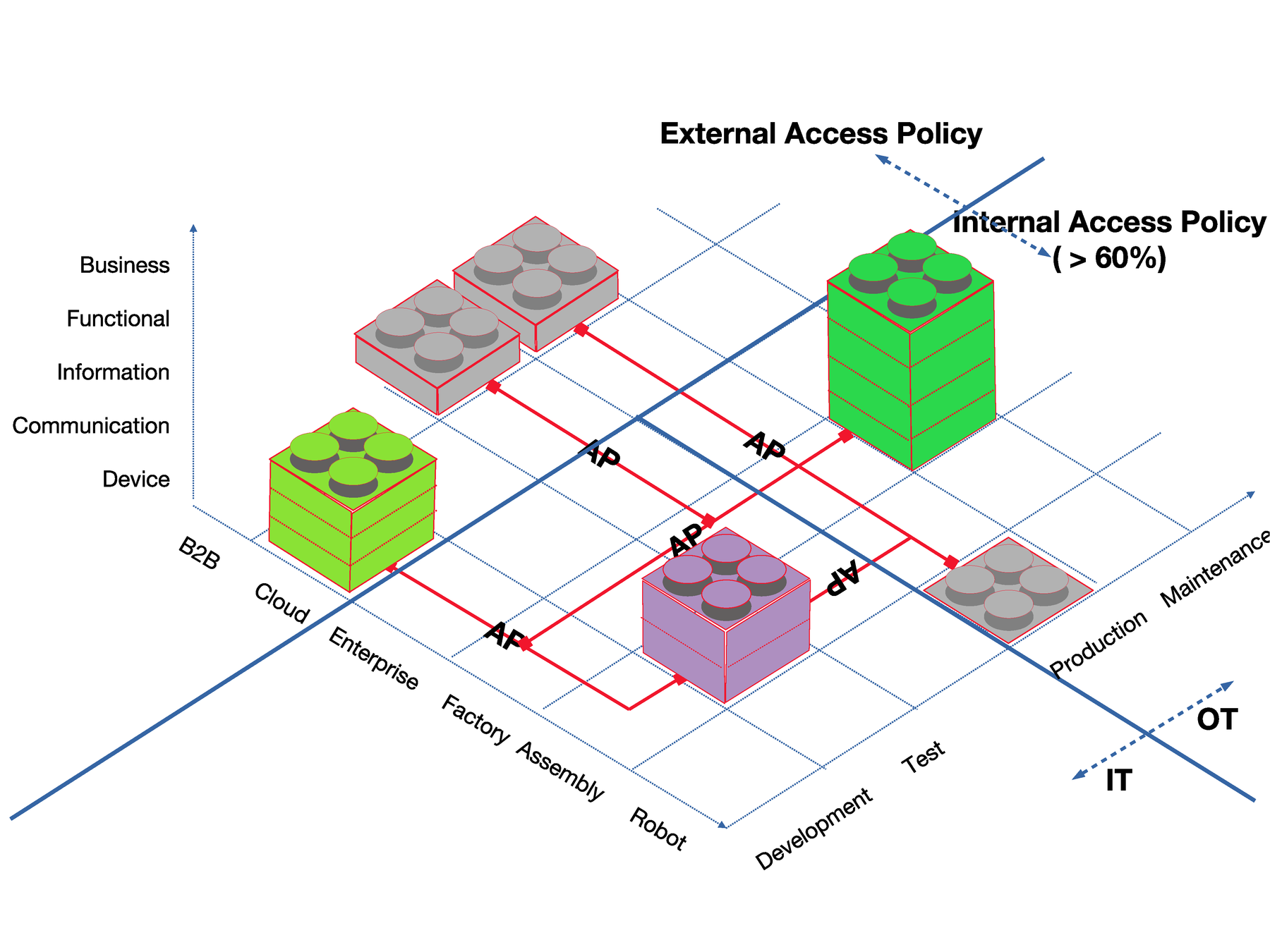
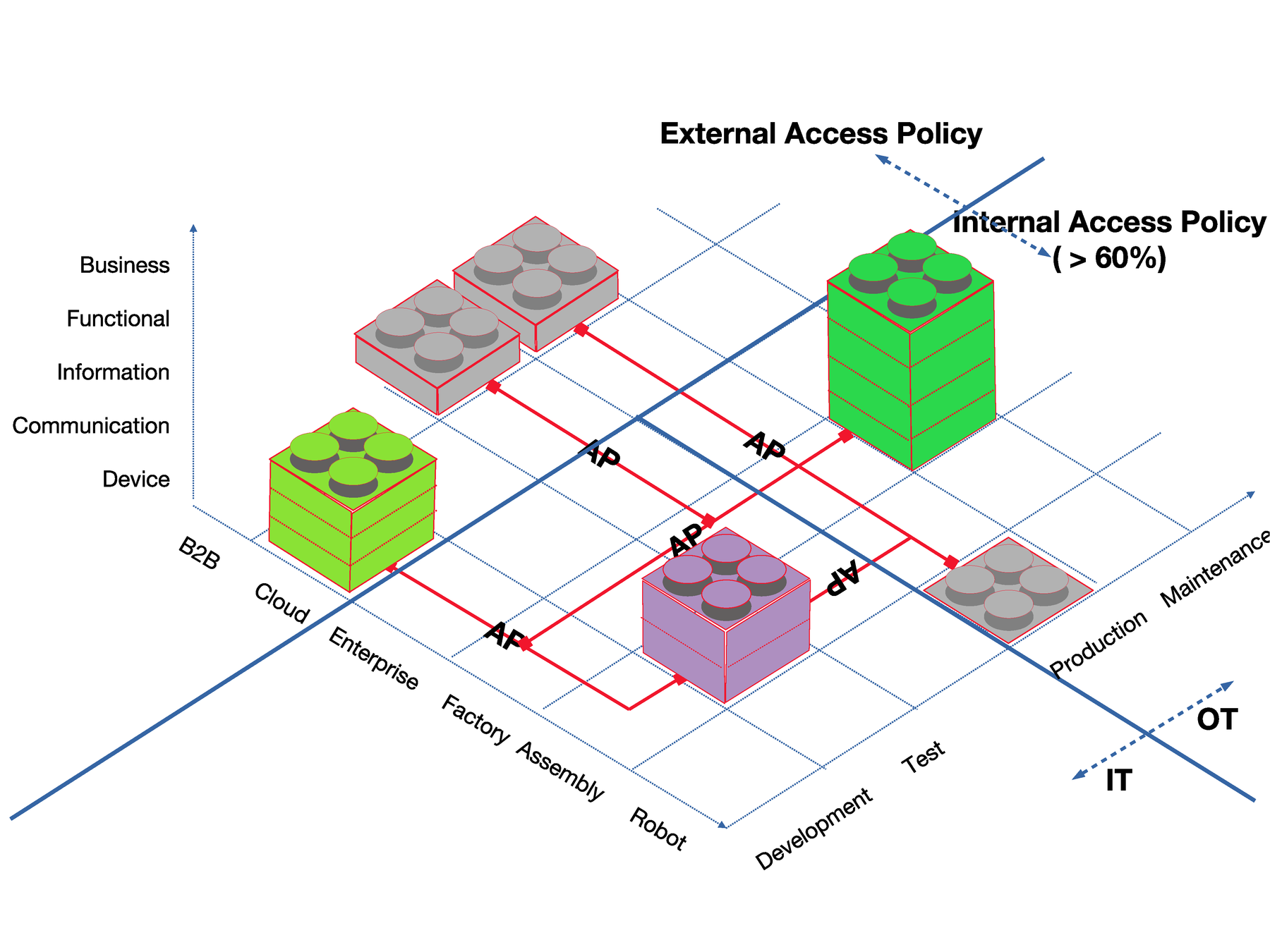
Security for complex Ecosystems:
Zero Trust / IDSA / AccessPolicies
data object interactions main driver for future IT architecture
devices produce and consume data at the same time
respect different data owners per device
if one fails, all suffer!
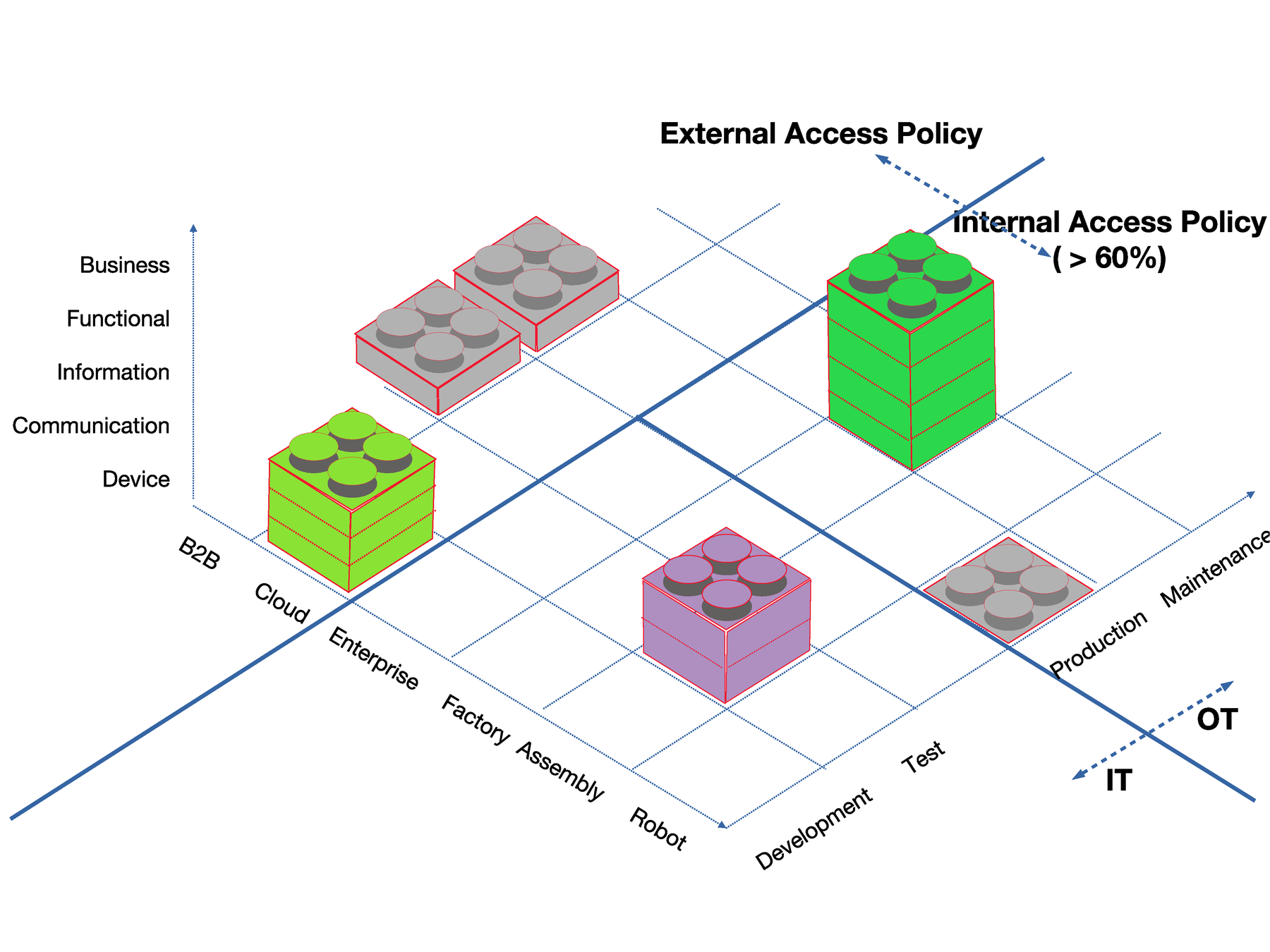
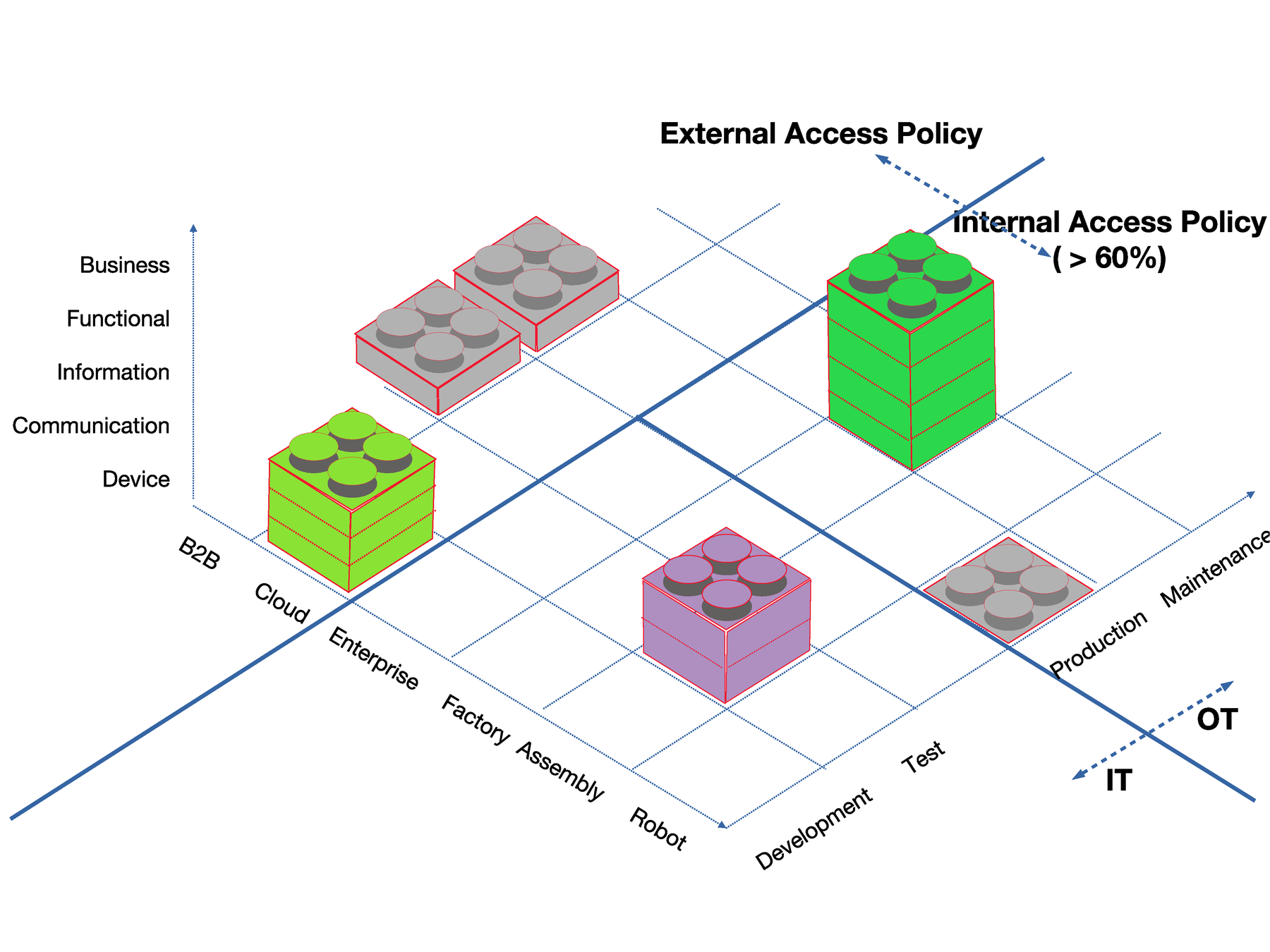
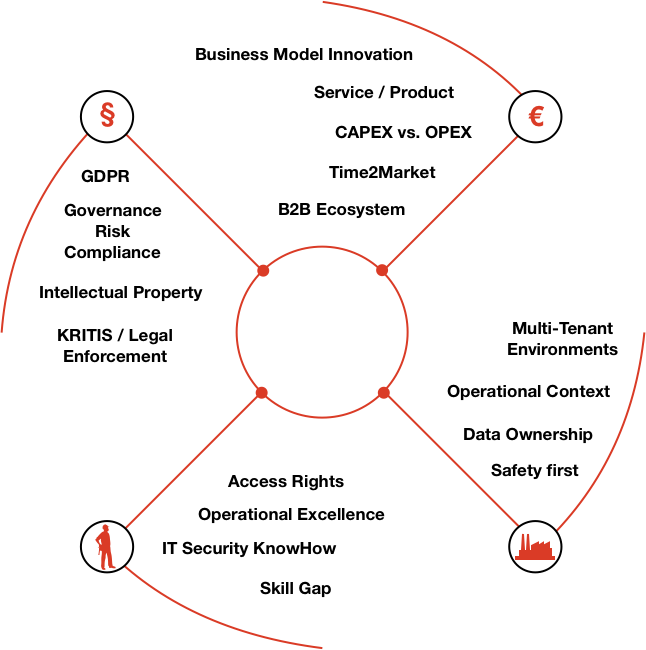
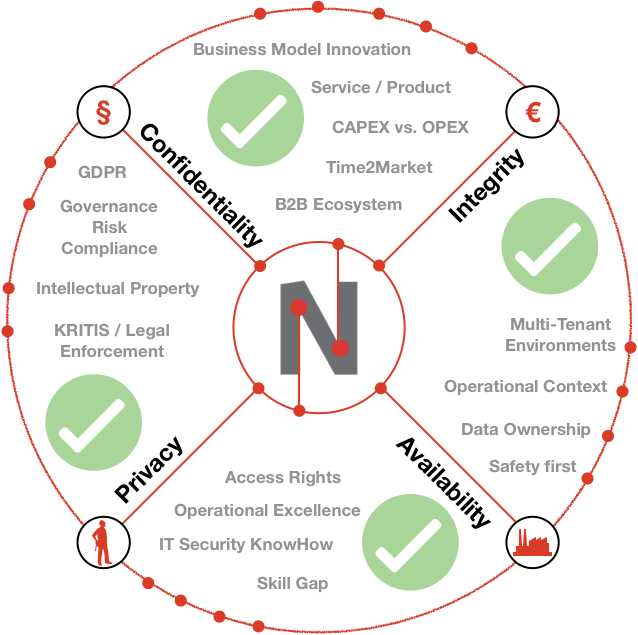
Security of Ecosystems:
Zero Trust / IDSA / AccessPolicies
Security of Ecosystems:
Zero Trust / IDSA / AccessPolicies
business agility: enables your company to adapt and survive
switch to a different service provider is easy
change policies in days (rather than months)
enables data reduction and data economy
Reliability
Legal
Economic
Environment
Social
Our Approach

www.neuropil.org
The first decentralized
open-source
messaging protocol
with security and privacy
by design
Benefits
messaging & security protocol for ecosystems
benefit for easy data sharing with full control over data flows
open source development to establish trust
apply end-to-end principle for data objects
Milestones
development started in 2014
2016: first exhibition @FROSCON
2019: NGI Zero / EU funded
2020: market-ready HMI 2020
IDSA certification & looking for partners
Security First:
digital identities
dual encryption layer
attribute based access control
decentralized access delegation
... and more
Privacy First:
stacked identities (realm / audience)
addressing hash based
DHT to protect metadata discovery
... and more
Easy to use
installed as a OS library
connect once, communicate globally
python / lua binding available
identity / data based routing
... and more
no more gateways
decentralized
P2P networks
decentralized
P2P networks
Trusted B2B mesh network
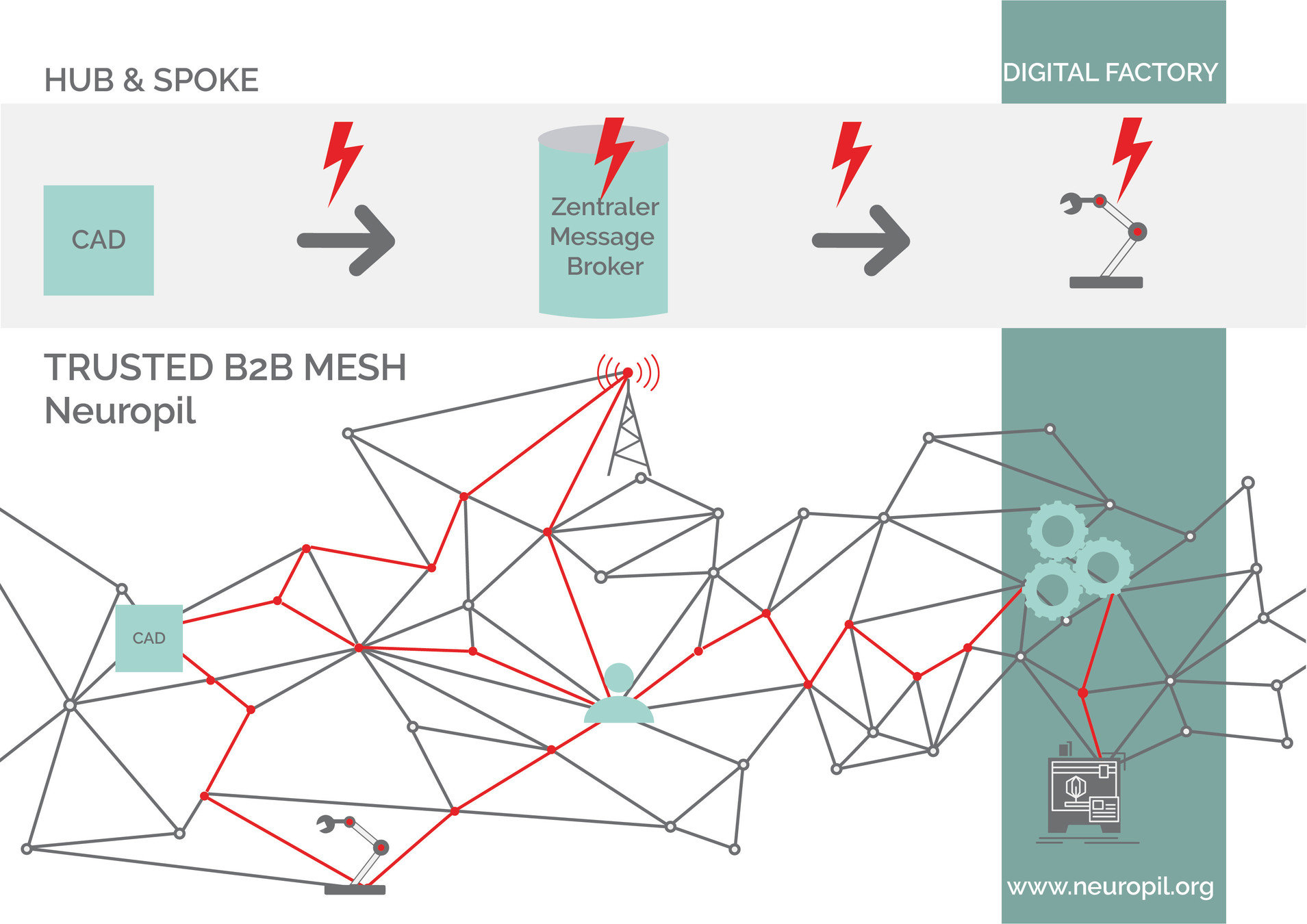
Benefits
stay secure behind closed firewalls
standardized security measures
limit packet size / throughput
"blind broker" nodes
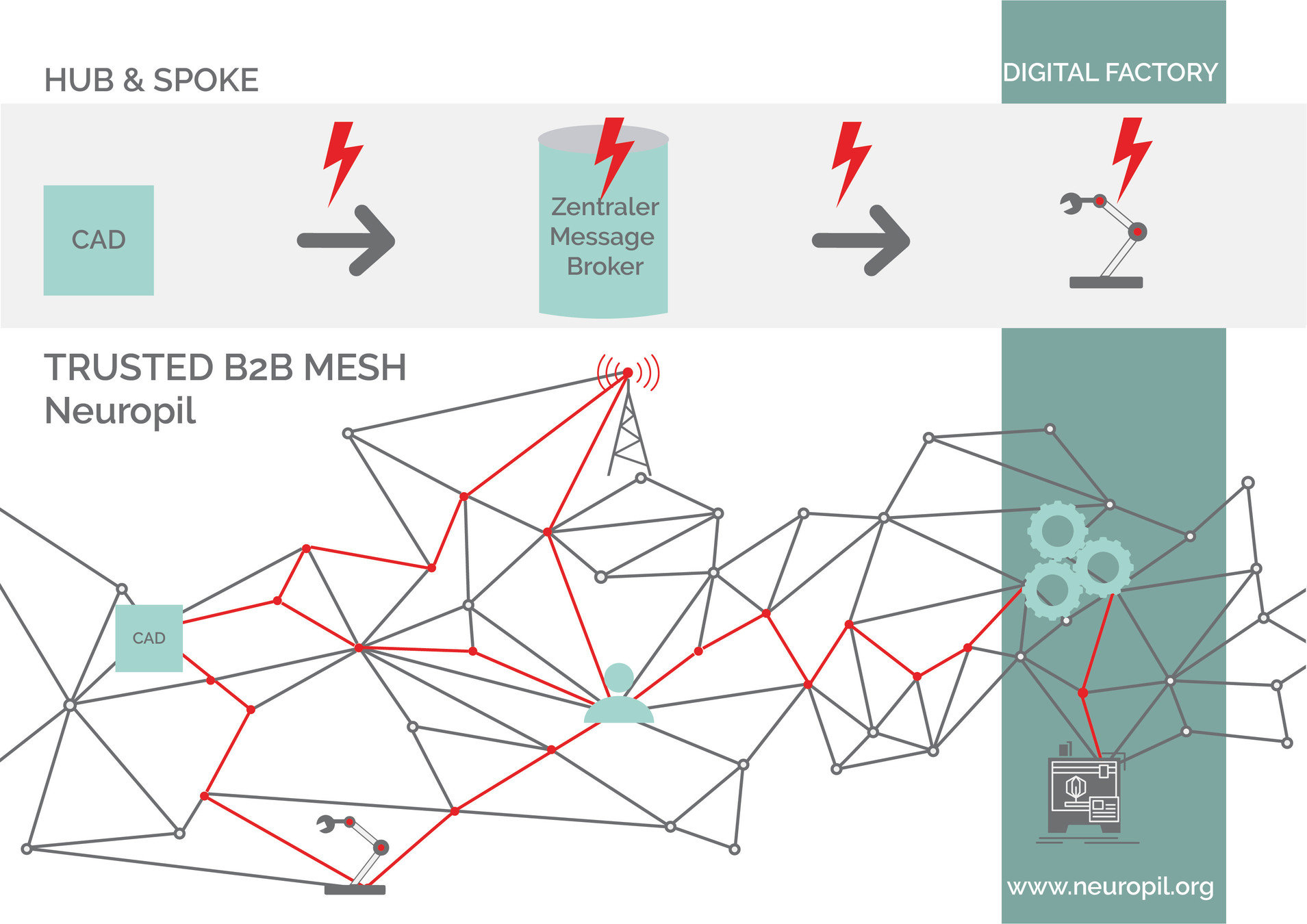
Trusted B2B mesh network
connects everything:
devices, edge, processes,
applications, users, enterprises
...
neuropil & IDSA
why we joined:
rules to enforce data ownership / sovereignty
increase data quality and transparency
building european-wide ecosystems
neuropil & IDSA
neuropil@IDSA
decentralized (meta-data) broker
each application/device is a connector
decentralized MQTT
neuropil & IDSA
how to contribute to IDSA:
identity federation
resilience
high availability
e2e encrypted pub/sub streams
neuropil & IDSA
what's going on:
data models / participation in plugfest
governance model (idsa.neuropil.io ?) / IDS ready certification
mutual ongoing development / collaboration
Use Cases
Use Case:
On the horizon
"Boring Bookkeeping"
"Traveling around the world"
"Healthy Healthcare"

Let's
chat!