Zero Trust
13.01.2021
Enabler for data sovereignty and secure data communication
_

Hello from pi-lar
Short introduction to zero trust (~15 minutes)
Data Sovereignty example (~10 minutes)
Questions and discussion (~20 minutes)
_
Meet Marvin
_
security obsessed
and Eliza
_
little miss chatter-box

Security
of the Past:
Limitations
_ only protection of bilateral IP connections
_ not protecting different data objects, but apis
_ unsuited for rapid change of
data owners / new data channels

_
Security
of the Past:
Limitations

_
Security
of the Past:
Limitations
_ static design: build once, run forever
_ new requirements vs. security design
_ introduce security exceptions on change
_
too bad
Security
of the Future:
Zero Trust
_ trust perimeter has changed
_ fragmented information (flows) need protection
_ authn/authz must be possible everywhere
_ data objects governed by
external/internal access policies (AP)

_
Security
of the Future:
Zero Trust

Security
of the Future:
Zero Trust
_ defines trust levels for data objects
or smaller groups
_ fine grained access to objects possible
_ more insights means minimizing risk
_ Never trust, always verify

_
better
Security for Complex Ecosystems:
Zero Trust & Access Policy
_ data object interactions main driver
for future IT architecture
_ devices produce and consume data
at the same time
_ respect different data owners per device
if one fails, all suffer!

_
Security of Ecosystems:
Zero Trust, IDSA,
AccesPolicies

_
Security of Ecosystems:
Zero Trust, AccesPolicies
_ business agility: enables your company
to adapt and survive
_ switch to a different service provider is easy
_ change policies in days (rather than months)
_ enables data reduction and data economy
_

much better
Approaches

_
Ten principles
of Zero Trust
Architecture:
_ Know your architecture including users, devices, services
_ Create a single strong user identity
_ Create a strong device identity
_ Authenticate everywhere
_ Know the health of your devices and services
_ Focus your monitoring on devices and services
_ Set policies according to value of the service or data
_ Control access to your services and data
_ Don’t trust the network, including the local network
_ Choose services designed for zero trust
_

perfect.
Ressources:
_ NIST -
Implementing a zero trust architecture (March 2020)
(www.nccoe.nist.gov/sites/default/files/library/project-descriptions/zt-arch-project-description-draft.pdf)
Zero Trust Fundamentals
(www.oreilly.com/library/view/zero-trust-networks/9781491962183/ch01.html)
_ UK NCSC
Principles to help you design and deploy a zero trust
architecture (github.com/ukncsc/zero-trust-architecture)
_

<- RTFM!
Data Sovereignty
_The capability of an individual or an organization to have control
over their personal and business data. This entails that they should
be able to know which party holds which data, under what conditions (purpose, duration, reward), where data is kept, and are able to re-use
the data at other places.
Source: Data Sovereignty Now
_
team digital sovereignty
Secure Data Exchange with IDSA
_
_ important roles of data sovereignty:
_ data owner
_ data provider
_ data creator
_ data consumer
_ application provider
_ vocabulary provider
_ service provider
_ service data consumer
source: https://www.internationaldataspaces.org/ids-ram-3-0/
Let me
show you how!
*$!%/&!#X
Dr. SiTh* has not only taken the hippocratic oath,
she also believes in protecting her patients' data.
*Secure internet of Things
Doctor, what about my...?!
You and your data are safe with me.
_ Save records for 10 yrs
_ Full access control to view and issue access control rights
_Data is encrypted in cloud
_Back-up of records
Dr. Bone just received encrypted patient record and can add the x-rays.
Mr. Caseworker from Social Security Services is already processing the accident data to which Chris has provided access.
In summary
_
_ Save records for 10 yrs
_ Full access control to view and issue access control rights
_Data is encrypted in cloud
_Back-up of records
_Grant access rights to specific parts
_Authorities can contact, but not draw conclusions

Data Sovereignty: a Zero-Trust Security Environment
_
Not a real life scenario. Yet.

Transparent data communication
should be available to everyone!
_























_ secure, sovereign and sustainable data integration
_ small, secure connector library
_ a decentralized identity space enabling privacy
_ discovery of data channels funded by NGI Zero Discovery
_ pub/sub message encryption funded by NGI Zero Discovery

_
Our Approach: neuropil.org


_ would you like to help implementing the medical use case?
_ other ideas about joint development in the context of the NGI?
_ let's redefine IIoT security together !

_
Collaboration via neuropil.io
+49 221 16531700
info@pi-lar.net
www.pi-lar.net
marvin@ neuropil.io
eliza@ neuropil.io

pi-lar GmbH
Kreuzgasse 2-4
D-50667 Köln
Workshop
__

WebServer
MicroService A
MicroService B
MicroService C
This interface returns different data sets
based on the role of the user !
Secure a simple workflow with Zero Trust!
_
Firewall
Ten principles of zero trust architecture
(https://www.ncsc.gov.uk/blog-post/zero-trust-architecture-design-principles)
- Know your architecture including users, devices, and services
- Create a single strong user identity
- Create a strong device identity
- Authenticate everywhere
- Know the health of your devices and services
- Focus your monitoring on devices and services
- Set policies according to value of the service or data
- Control access to your services and data
- Don’t trust the network, including the local network
- Choose services designed for zero trust
Reliability
_ Legal
_ Economic
_ Environment
_ Social

_
NIST - Implementing a zero trust architecture (March 2020)
https://www.nccoe.nist.gov/sites/default/files/library/project-descriptions/zt-arch-project-description-draft.pdf
O’Reilly - Zero Trust Fundamentals
https://www.oreilly.com/library/view/zero-trust-networks/9781491962183/ch01.html
UK NCSC - Principles to help you design and deploy a zero trust architecture
https://github.com/ukncsc/zero-trust-architecture

Security First
_ digital identities
_ dual encryption layer
_ attribute based access control
_ decentralized access delegation
... and more
_
Privacy First
_ stacked identities (realm / audience)
_ addressing hash based
_ DHT to protect metadata discovery
... and more
_
Easy to use
_ installed as a OS library
_ connect once, communicate globally
_ python / lua binding available
_ identity / data based routing
... and more
_
no more gateways
decentralized
P2P networks
>
>
Trusted B2B mesh network
Benefits
_ stay secure behind closed firewalls
_ standardized security measures
_ limit packet size / throughput
_ "blind broker" nodes

_
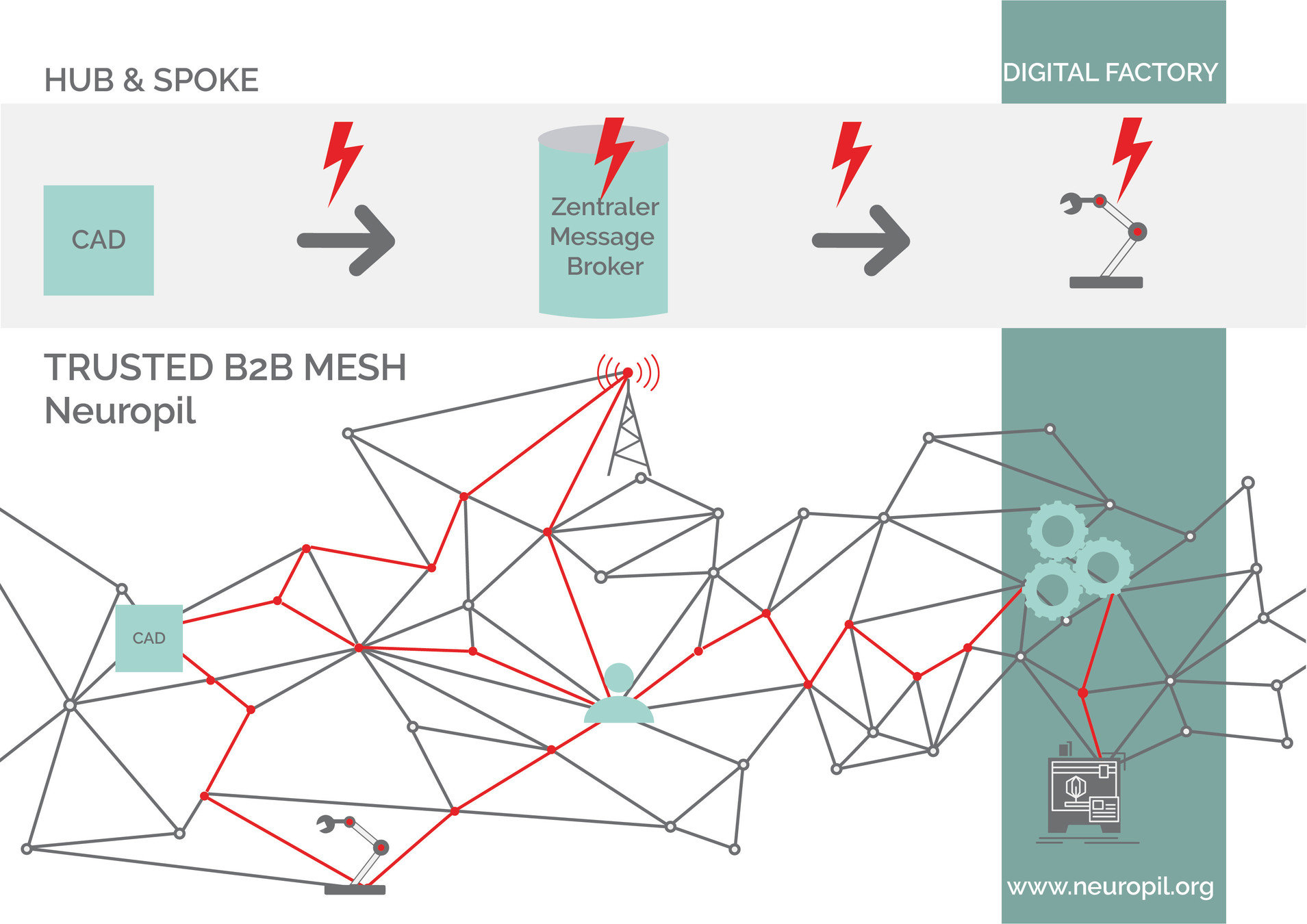
Trusted B2B mesh network
connects everything:
devices, edge, processes,
applications, users, enterprises
...
Neuropil
Cooperation, dialogue, contribution etc.