PPAP
Perfectly Poison ARP Poisoning
Team19
b05902127 劉俊緯
b05902117 陳柏文
b05902031 謝議霆
What is ARP?
Task: 87 -> 88
140.112.31.87
140.112.31.88
Switch cannot look ip.
So we needs 88's MAC to let switch forward.
src: 140.112.31.87
dst: 140.112.31.88
dst MAC: ???
87:87:87:87:87:87
88:88:88:88:88:88
ARP Request & Reply

140.112.31.87
140.112.31.88
ARP Request
who has 140.112.31.88 ?
87:87:87:87:87:87
88:88:88:88:88:88
ARP Reply
88:88:88:88:88:88 has 140.112.31.88 ?
src ip: 140.112.31.87 src MAC: 87:87:87:87:87:87
dst ip: 140.112.31.88 dst MAC: 88:88:88:88:88:88
What is ARP Poisoning?
ARP Poisoning
140.112.31.87
140.112.31.88
I know 140.112.31.88 => 88:88:88:88:88:88
87:87:87:87:87:87
88:88:88:88:88:88
ARP Reply
89:89:89:89:89:89
has 140.112.31.88

140.112.31.89
89:89:89:89:89:89
89:89:89:89:89:89

How to mitigate ARP Poisoning?
Dynamic ARP Inspection(DAI)
Why not?
- DAI needs information in Layer 3
- Must be Layer3 Switch
- Not flexible
ARP poisoning + MitM
Attack Flow Chart
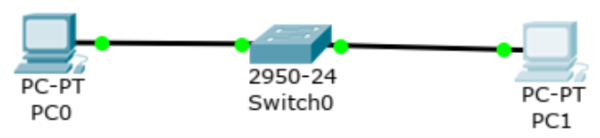
Environment
- Layer2 switch
- Port security
- Attacker can't fake mac address
1. Everything is fine

2. Attacker send arp reply

3. user update arp table

4. package redirect

5. package redirect

Demo arp poisoning
Monitoring + Patch on L2 switch!
Monitor with Cisco switch
- Monitor in Cisco
- Copy all packages from port to destination port
switch
monitor
PC
Monitor with other L2 switch
- Monitor -> Gateway
- Firewall
switch
monitor
PC
IP -> multiple MAC?
- user update arp table
- Possible reason:
- change device
- DHCP
- attack
1 MAC -> multiple IP?
- Possible reason:
- change IP
- attack
Detect
- if MAC2 -> IP2 and previous IP1 && IP2 has its MAC1
- ping IP2 with the MAC1
- if received
- ban MAC2