Photo by Chris Barbalis on Unsplash
Sovereign Identity
on the Blockchain
Laurent Hardy
do not
trust
me
do research, learn the technology,
test the product, engage with the community, compare with other projects, read the documentation, look for red flags
Personal information is available in its totality, regardless of what is actually needed
Identity is fragmented in different forms and places
Identify yourself is tedious and repetitive
There is almost no compatibility between identification processes
We are not the owners of our identity
How many identities?



personal
legal
digital
Challenges around digital identity
| Privacy | Increase the level of privacy of our identity with enough flexibility in establishing our identity |
| Context | Keep the identity system compatible with its context |
| Practicality | Identity must be helpful for everyday activities |
| Provenance | Preserve the provenance of identifiers |
| Risks | Lower the risks attached to establishing an identity |
| Intermediaries | The dilemma of Distributed Ledger Technologies in the case of identity |
source: consensys podcast
Self Sovereign Identity
vs. Federated Identity
Photo by Mike Enerio on Unsplash
Photo by Noah Silliman on Unsplash
Maybe
it's what we are
not who we are
Blockchain-based identity
infrastructure
identity
I'm 32
I have 1.764€ on my bank account
I know who Satoshi Nakamoto is
identifiers
verifiable claims
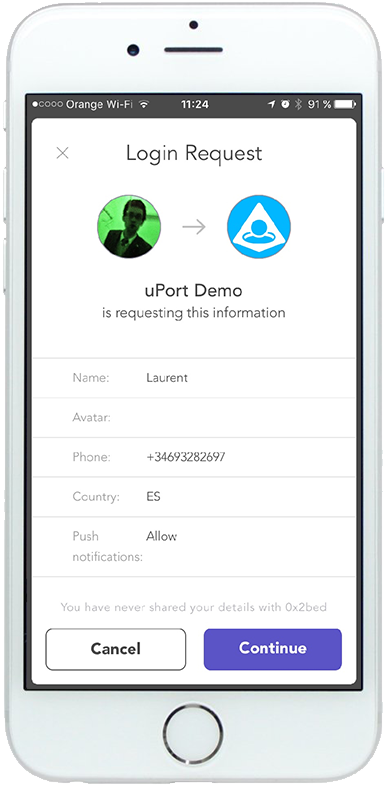
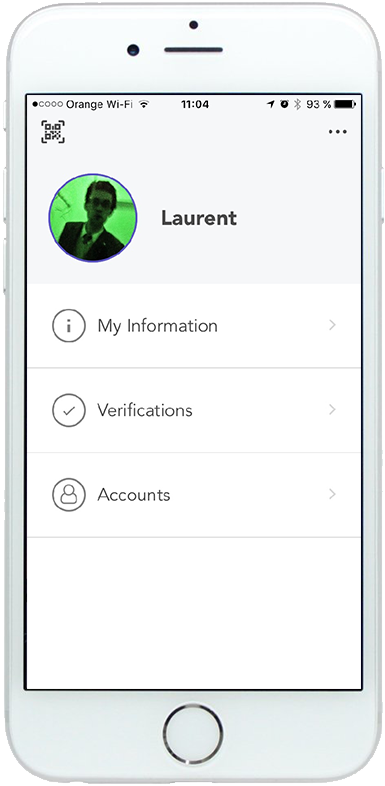
uPort features
| Identity rooted in Ethereum blockchain | User reputation system | |
| Passwordless, Single Sign-On | Browser to mobile app communication | |
| Simplified user centric keys management | Identity verification / KYC | |
| Binding digital signatures | Private chain support |
source: Self Sovereign Identity in Zug
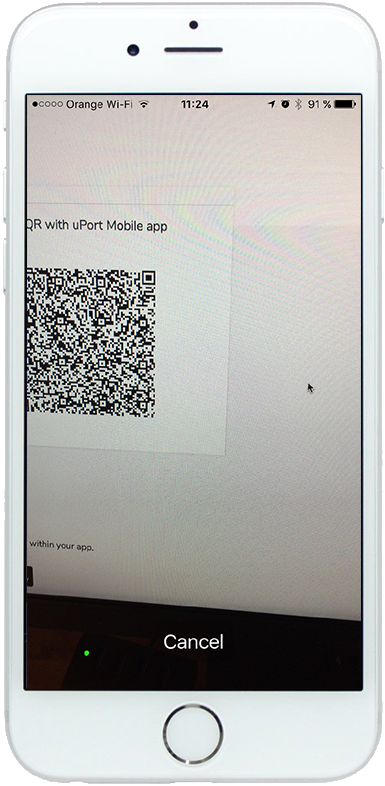
uPort integration

Server App
web2
Blockchain App
web3
uPort in action