An efficient and effective Decentralized
Anonymous Voting System
2018, Wu, Wei-Jr Lai Ja-Ling
Introduction
-
The election needs one or more authority for both authentication and protect the privacy of participant
-
However, it is difficult for voter to believe
-
government or authority that will always follow the rules
-
never get hacked
-
-
Introduction
Introduction
-
Open Vote Network is decentralized, anonymous and transparent
-
cannot tally the result even only one voter doesn't cast his ballot
-
only suitable for small-scale voting
-
-
Introduction
- propose a lightweight E-voting system minimize trust in the authority or government
System
Key ideas
-
One-time Ring signature
-
Stealth Address
System > Key ideas
One-time Ring Signature
-
General Ring Signature
-
signer in a particular group can signs the message as group member, and verifier cannot distinguish the identity of signer
-
a voter can cast their ballot twice
-
System > Key ideas > One-time Ring Signature

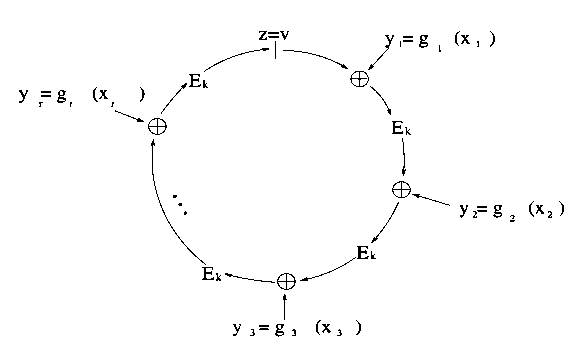
One-time Ring Signature
-
One-time Ring Signature
-
singer generate key pair \((x, P)\), additionally compute key image \(I = xH_p(P)\)
-
sign
-
create ring signature with group public keys \(P_i\) and own key pair \((x, P)\) and key image \(I\)
-
-
verify
-
check if \(I\) has been used in past signatures
-
Multiple uses imply that two signatures were produced under the same secret key
-
-
-
System > Key ideas > One-time Ring Signature
One-time Ring Signature
-
If the mapping \(x \rightarrow I\) is an injection
-
Nobody can recover the public key from the key image and identify the signer
-
\(H_p(P) = I\cdot x^{-1}\)
-
-
The signer cannot make two signatures with different \(I\) and the same \(x\)
-
System > Key ideas > One-time Ring Signature
\(I = xH_p(P)\)
Stealth address
-
unlinkable payments scheme proposed in CryptoNote
- The destination of each output is a public key, derived from recipient’s address and sender’s random data
System > Key ideas > Stealth address
Stealth address
System > Key ideas > Stealth address
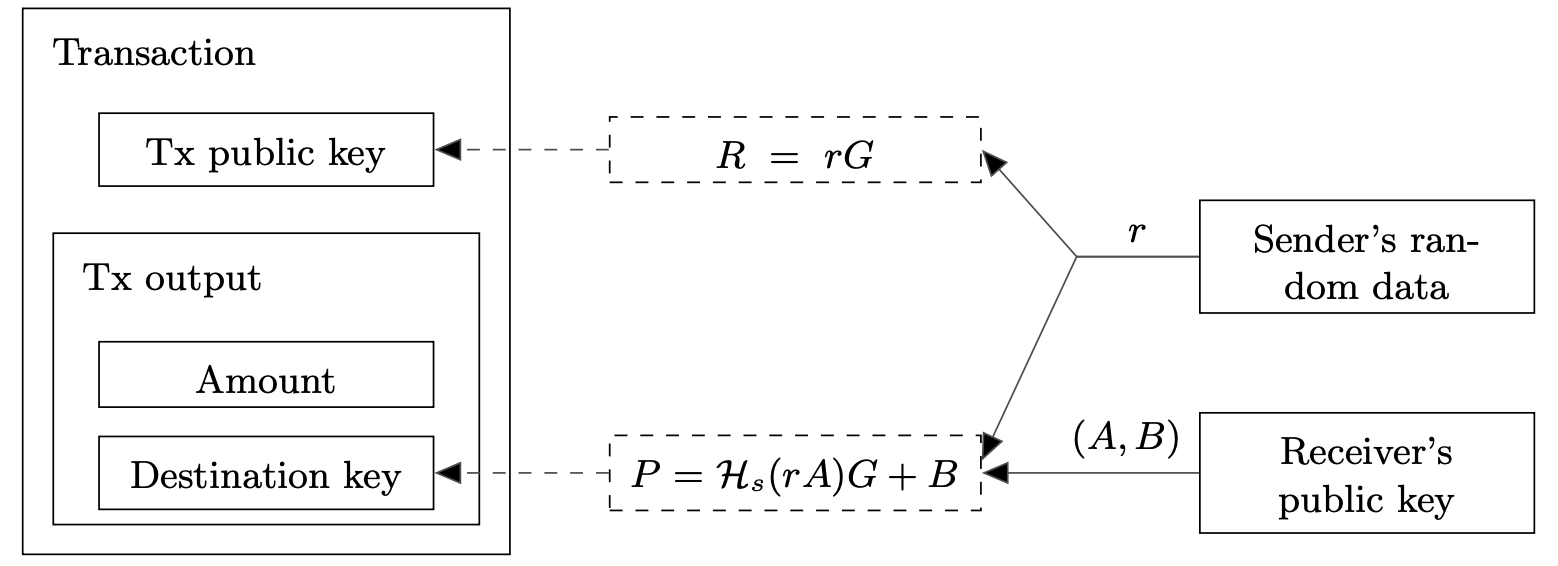
Alice(sender) wants to send a payment to Bob(receiver)
Stealth address
System > Key ideas > Stealth address
Bob checks if Alice’s transaction is sending for himself
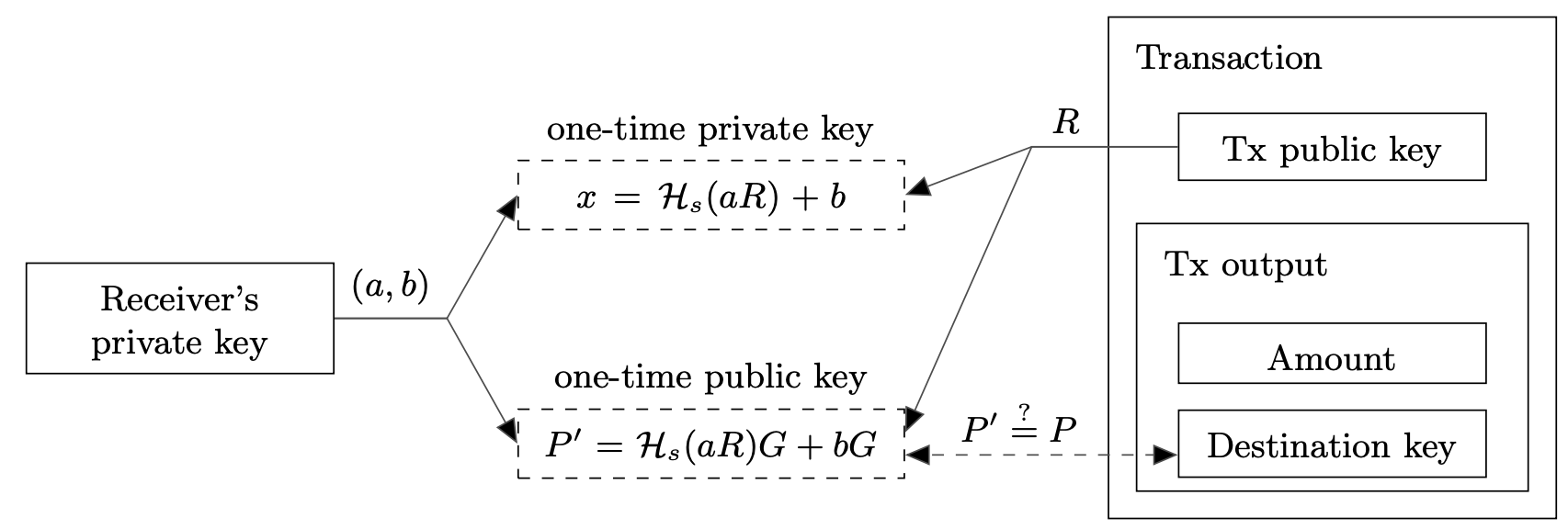
Stealth address
System > Key ideas > Stealth address
- In this propose, sender is voter, receiver is candidate
- It means that voters can obfuscate the observers who they actually vote for
Key management
System > Key ideas > Stealth address > Key management
- Information about election results should not be opened until tally phase
- We need more than one people to share the first private key of candidate
- Diffie-Hellman key exchange
- We need more than one people to share the first private key of candidate
Key management
System > Key ideas > Stealth address > Key management
- Alice and Bob pick a random number \(r_a, r_b\) and announce \(r_aG, r_bG\) separetly
- Both them can compute \(r_ar_bG\) and make it public
- After voting phase, they submit \(r_a, r_b\) separately
- => \((r_ar_b, r_ar_bG)\) will be candidates' first shared key pair
- candidate cannot tally before tally phase
Election
System > Election
- This election can split into 3 phase
- setup
- voting
- tally
Setup
System > Election > Setup
- Voter list
- A set of public key, each one is a point on elliptic point and corresponds to a valid voter
- Candidate
- To generate public key for stealth address, voter can encode them into coordinate on elliptic curve
- Secret sharing
- The chosen key managers build shared secret by DH on the smart contract
- To ensure that key managers will submit their individual secret, introduce a deposit
Voting
System > Election > Voting
- Voter knows public information including candidates' first public key A, candidate list from smart contract
- First, compute a ballot \((SA, R)\) for selected candidate by \(A, B_i\)
- Then, the ballot be signed with owned private key and one-time ring signature to get signed ballot \((m, \sigma), m = (SA,R)\)
- Third, send signed ballot on smart contract with different Ethereum account
Voting
System > Election > Voting
- Complex operations cost much on smart contract
- We separate the verification of ring signature from voting phase to reduce the computation cost
- As a result, everyone can try to send invalid or revoting ballots
- But those wrong ballots can always be detected
- A rational attacker will not cost gas to make a useless attack
- As a result, everyone can try to send invalid or revoting ballots
- We separate the verification of ring signature from voting phase to reduce the computation cost
Tally
System > Election > Tally
- Key managers should open their individual secret for retrieve their deposit
- No one can vote after voting phase
- People who interested in election can access all information and tally the result by themselves
Tally
System > Election > Tally
- The signed ballot \(m, \sigma\) will be counted to candidate \(C_i\) if
- key image \(I\) is never shown before
- verify the signature
- stealth address is for \(C_i\)
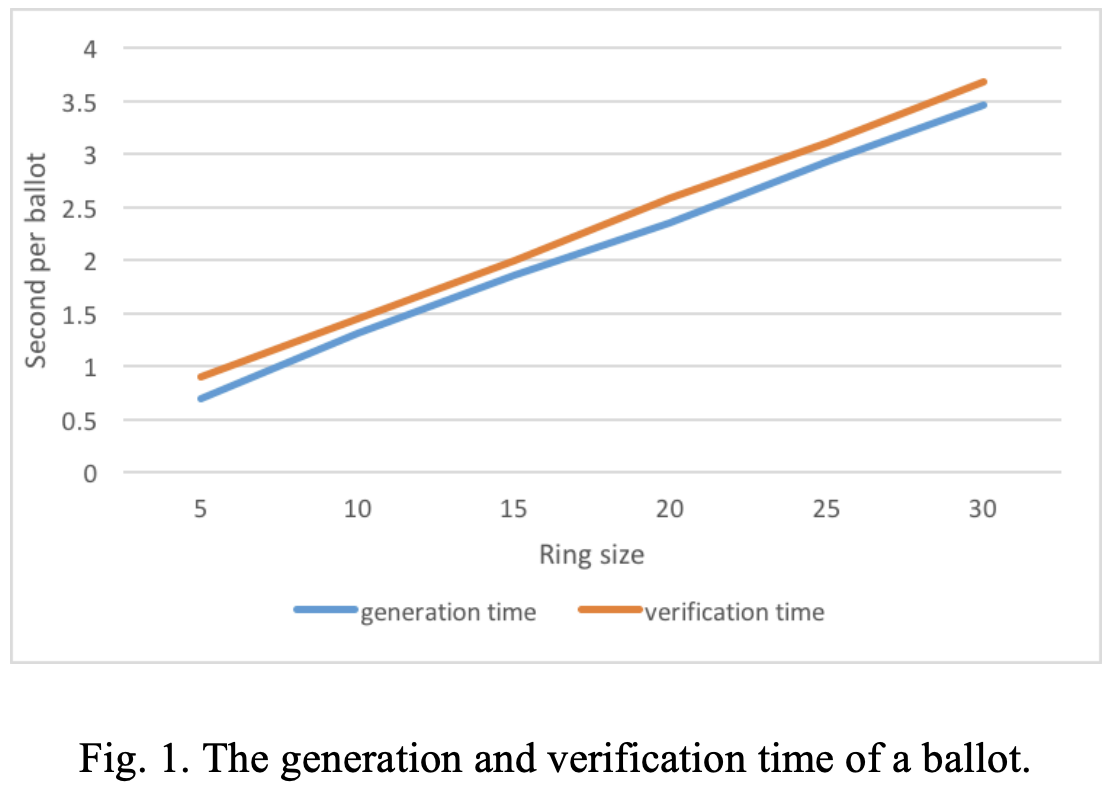
Analysis
Time analysis
-
Environment
-
2 core, 2.7 GHz Intel Core i5 and 8 GB DDR3 RAM
-
written in javascript
-
Analysis > Time analysis
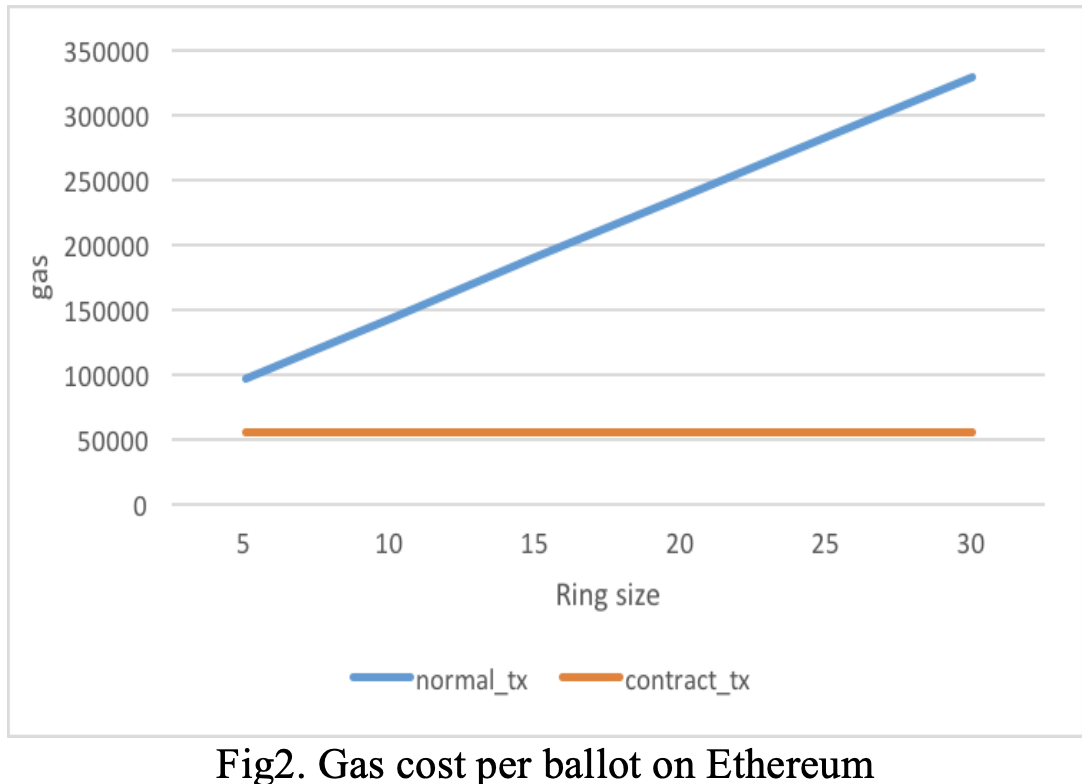
Gas cost
-
We don't record the ballot information on smart contract directly, but save it in normal transaction
-
The ballot information on smart contract is only transaction id of normal transaction
-
Analysis > Gas cost
Security
-
Anonymity is protected by ring signature
-
Colluding of key managers is risk
-
In the worst case, all of them collude to retrieve shared secret key, can only make them tally the result earlier
-
Analysis > Security
Conclusion
-
We proposed a decentralized anonymous voting system which only requires minimal trust in others and gas cost per voter
-
Since the tally phase could speed up via parallel computation, the system is also suitable for large-scale voting
Conclusion