Anonymous Voting by 2-Round Public Discussion
Feng Hao, Peter Ryan, Piotr Zielin ́ski
Article in IET Information Security · July 2010
Introduction
-
Depending on whether trusted third parties are involved, it can be divided into two classes
-
1. decentralized elections where the protocol is essentially run by the voters themselves
-
2. centralized elections where trusted authorities are employed to administer the process
-
- => focus on class 1
Introduction
Introduction
-
There are two challenges
-
No trusted third parties exist
-
No voter-to-voter private channels
-
Introduction
No trusted third parties exist
-
Many security problems could be easily solved if we assume a trusted third party
-
But, the “trusted” third party may become the one who breaks the security policy totally
-
-
Standard approach
-
distribute trust among several third parties by using a threshold scheme
-
But, goal is to eliminate the use of trusted third parties altogether
-
-
Introduction > No trusted third parties exist
No voter-to-voter private channels
-
This is
-
to ensure dispute freeness – everybody can check whether all voters have faithfully followed the protocol
-
to minimise the assumptions required for the protocol to be secure
-
- Some solutions were proposed...
- Computation cost, Round efficiency problems still existed
Introduction > No voter-to-voter private channels
Protocol
-
Let us consider the single-candidate case first
-
vote is either "yes" or "no"
-
-
Each participant \(P_i\) selects a random value as the secret \(x_i \in_R \mathbf{Z}_q\)
- participants execute the 2-round protocol
Protocol
2-round protocol
- Round1
-
Every participant \(P_i\) publishes \(g^{x_i}\) and a ZKP(Zero Knowledge Proof) for \(x_i\)
-
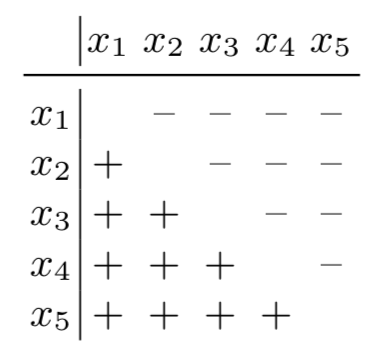
When this round finishes, each participant \(P_i\) checks the validity of the ZKP and computes
\(g^{y_i} = \prod_{j=1}^{i-1}g^{x_j}/\prod_{j=i+1}^{n}g^{x_j}\)
-
- Round2
- Every participant publishes \(g^{x_iy_i}g^{v_i}\) and a ZKP showing that \(v_i\) is one of {0,1} (-> {"no", "yes"})
Protocol > 2-round protocol
2-round protocol
- To tally the “yes” votes, each participant, or anyone observer can compute \(\prod_{i}g^{x_iy_i}g^{v_i} = g^{\sum_{i}v_i}\) (∵ \(\sum_ix_iy_i = 0\))
- \(\gamma := \sum_iv_i\) is normally a small number, it is not difficult to compute the discrete logarithm of \(g^{\gamma}\)
Protocol > 2-round protocol
First Round
- \(P_i\) needs to demonstrate his knowledge of the exponent without revealing it
- use Schnorr’s signature
- prove: exponent for \(g^{x_i}\)
- send \((g^v, r := v - x_iz)\) where \(v \in_R \mathbf{Z}_q\), \(z := Hash(g, g^v, g^{x_i}, i)\)
- verified by anyone through checking \(g^v \overset{?}= g^rg^{x_iz}\)
- use Schnorr’s signature
Protocol > 2-round protocol > First Round
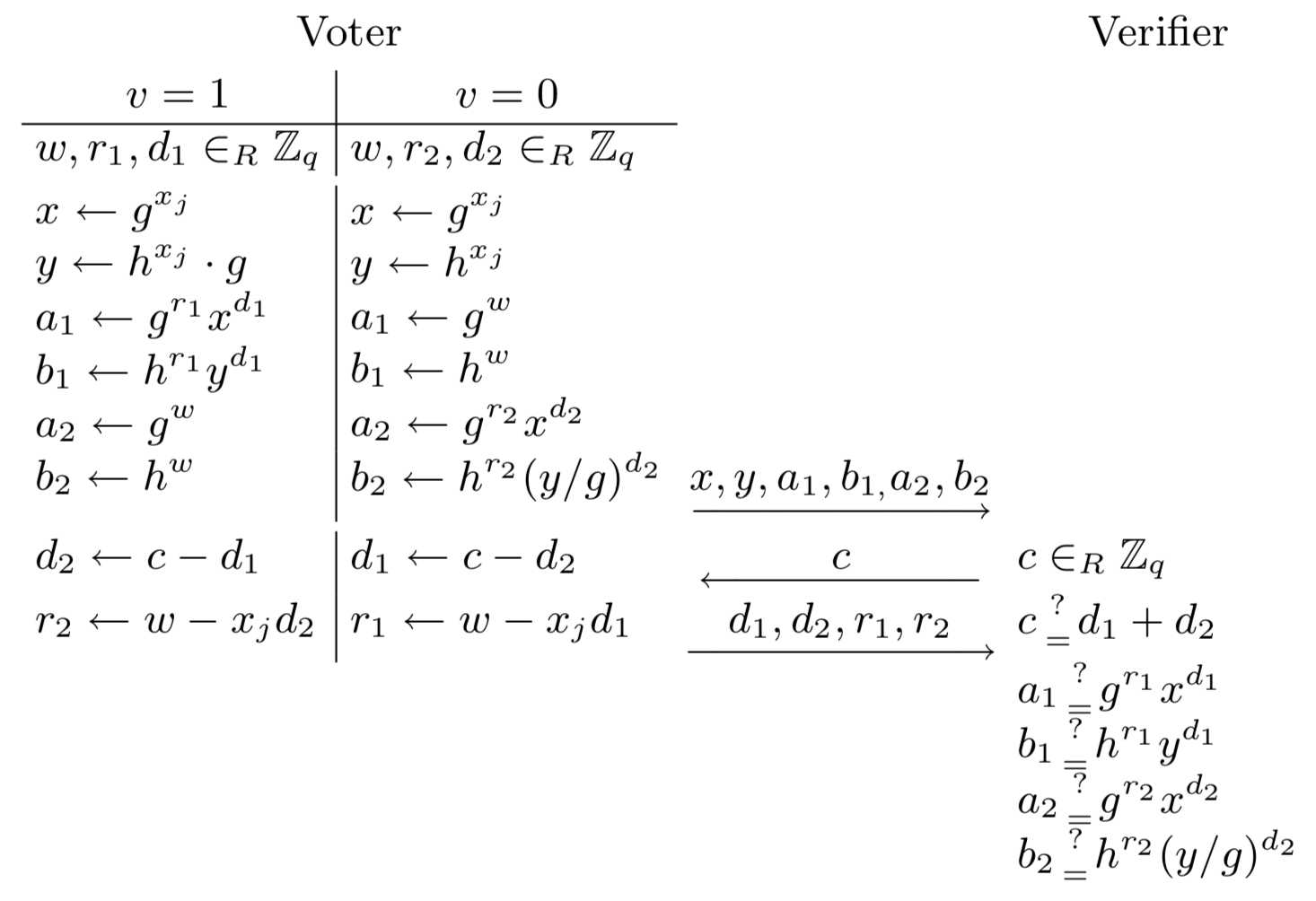
Second Round
- \(P_i\) needs to demonstrate that the encrypted vote is one of \(\{0,1\}\) without revealing which one
- use CDS(Cramer, Damgard and Schoenmakers) technique
- convert into Elgamal encryption
- use CDS(Cramer, Damgard and Schoenmakers) technique
Protocol > 2-round protocol > Second Round
Security analysis
-
Maximum ballot secrecy
- Casted ballot is a ciphertext that is indistinguishable from random, and hence doesn't reveal about the voter’s choice
-
Self Tallying
- After all ballots have been cast, anyone can compute the result without external help
-
Dispute Freeness
- Everybody can check whether all voters act according to the protocol
Security analysis
Maximum ballot secrecy
- Colluders cannot learn \(y_i\) even if the worst case that only \(P (k \neq i)\) is not involved in the collusion
- \(y_i\) is computed from \(x_j (j \neq i, k)\)
Security analysis > Maximum ballot secrecy
\(y_i = \sum_{j < i}x_j - \sum_{j > i}x_j\)
Self Tallying
- Any interested party can compute the final tally without external help
- ZKPs ensure that voters faithfully follow the protocol
Security analysis > Self Tallying
Dispute Freeness
- the use of CDS technique serves to ensure that each ballot will encode exactly one candidate
- one-man-one-vote requirement is enforced
Security analysis > Self Tallying
Limitation
- potential subjection to the denial of service (DOS) attack
- For example, if some voters refuse to send data in round 2, the tallying process will fail
- can detect this attack but process will be delayed
Security analysis > Limitation
-
lack of coercion resistance
- reveal secret values and can prove how he voted
- ZKP show that he knows exponent for \(g^{x_i}\)
- reveal secret values and can prove how he voted