Onions adventures
How to use onion services and the
network in your web endeavors
hiro@torproject.org

👾

¡Hola!

Hi, I am silvia..
- Some known me as Hiro.
- I work at the Tor Project.
- I am also part of the Information Security Group in the Department of Telematics Engineering at UPC-Barcelona where I got my Ph.D.

Know your onions
-
What is Tor and what it can do for you.
-
How Tor provides privacy and anonymity.
-
Using Tor at the application layer: The Tor Browser.
-
Onion services and bidirectional anonymity.
-
Using onion services in your personal and web projects.

What is and
what it can do for you

Tor is a privacy tool
- Tor is free software.
- Tor is a community made up of a diverse group of developers, researchers, relay operators, volunteers.
- Tor is an open network.
- Tor is a non-profit.

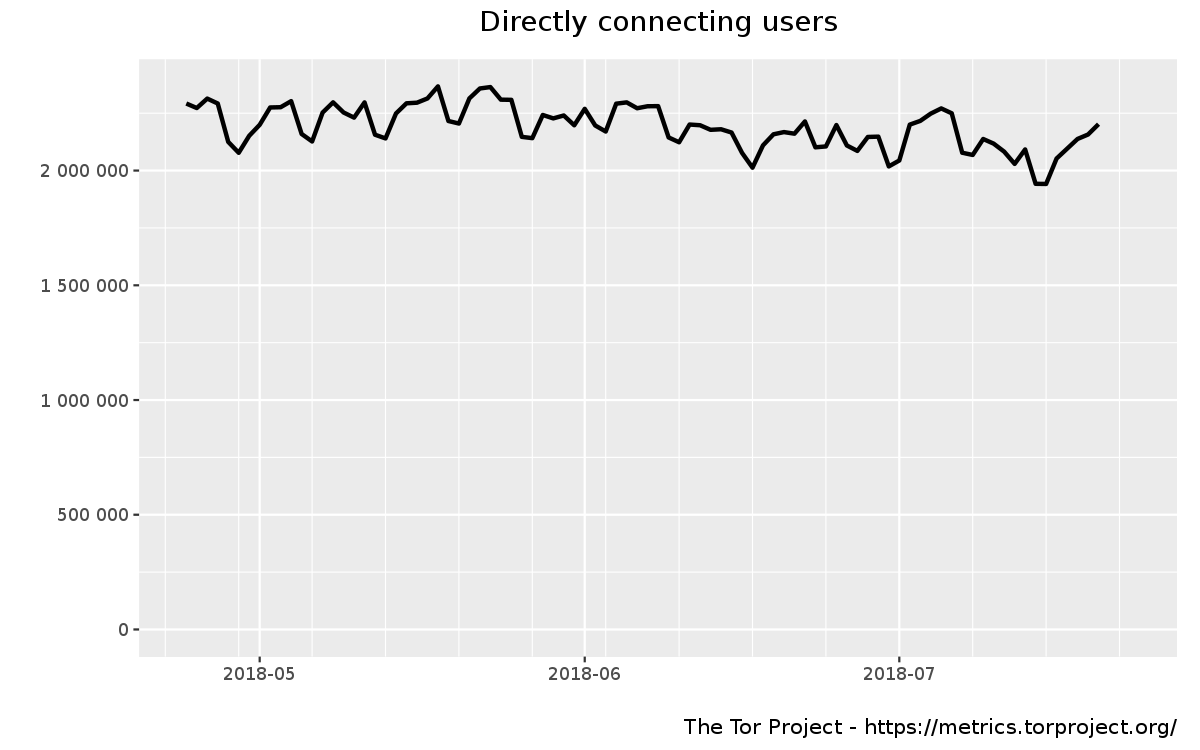
Tor is about 2M daily users using the network!

Tor is about 2K bridges and 6K relays


Tor provides about 200Gbit/s bandwidth


What does Tor do?
- Tor provides privacy.
- Tor provides anonymity.
- Tor provides communication security.
- Tor provides a traffic analysis resistant communication network.
- Tor provides reachability against censorship.

How does provide Privacy and Anonymity?

Privacy by design
Tor provides privacy by distributing TRUST


How Tor works

Alice wants to talk to some Bob. Alice also wants to stay safe.
How Tor works

The connection between Alice and the tor network is encrypted. The connection between the last exit node and Bob is not.
That's why it is important to use HTTPS!
How Tor works

Anonymity > Encryption
Anonymity > Encryption
- Encryption doesn't hide conversations metadata
- Encryption doesn't hide your social graph
- Encryption doesn't hide network metadata
- Encryption doesn't hide your location
Using at the app layer:
Tor Browser

What is Tor Browser
Tor Browser is a modified Firefox ESR.
Tor Browser Packages:
-
Tor, Torbutton,
-
TorLauncher,
-
NoScript,
-
and HTTPS-Everywhere.
Why Tor makes a browser
Tor browser is designed to:
- Ensure the safe use of Tor.
- Reduce linkability of user activities on different websites.

Onion Services
Providing bidirectional anonymity
Next gen Onion Services
- Better crypto [ed|curve25519 - Keccak(SHA3)]
-
54 chars for onion service address.
- Address the onion service through their public key
- The key system allows to create subkeys (so the main key stays hidden)
- Rendezvous Single Onion Services
- Vanguards design against the guard discovery attack
- Shared randomness in the desc id

How Onion Services work

Bob is an onion service and Alice a Tor Browser user.
Bob picks 3 introduction points and builds a circuit.
How Onion Services work

Bob builds a descriptor and uploads it to the directory
How Onion Services work

Alice fetches the descriptor from the directory and learns how to reach Bob.
How Onion Services work

Alice tells Bob to meet her at the rendezvous point.
How Onion Services work

How Onion Services work
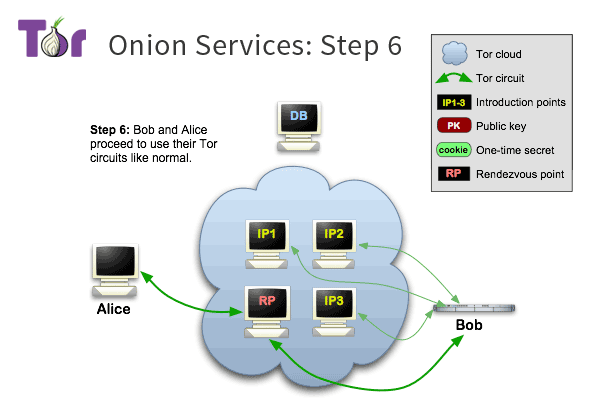
Both Alice and Bob connect with a 3 hops circuit to the RP.
Using Tor within other applications through onion services.
Tor ecosystem


Onion-micro-services ??
- Onion services can be integrated into existing web services, making them more secure.
- This is especially interesting for microservices architectures.

SSH onion-services
ssh:
container_name: onion_ssh
hostname: onion_ssh
build: ${PWD}/config/ssh
command: /home/root/init.sh
volumes:
- ./config/ssh/tor/torrc:/etc/tor/torrc
- ./config/ssh/keys/:/home/root/.ssh/keys
- ./config/ssh/init.sh:/home/root/init.sh
- ./config/ssh/sshd_config:/home/root/.ssh/ssh/sshd_config
ports:
- "2222:22"FROM debian
MAINTAINER hiro <hiro@torproject.org>
RUN apt-get update
RUN apt-get install -y sudo vim openssh-server tor
USER root
RUN mkdir -p 700 /home/root/.ssh \
&& mkdir /var/run/sshd \
&& mv /etc/ssh /home/root/.ssh/ssh \
&& ln -s /home/root/.ssh/ssh /etc/ssh
WORKDIR /home/root
VOLUME /home/root
EXPOSE 22SSH onion-services
## /etc/torcc
##
############### This section is just for location-hidden services ###
## Once you have configured a hidden service, you can look at the
## contents of the file ".../hidden_service/hostname" for the address
## to tell people.
##
## HiddenServicePort x y:z says to redirect requests on port x to the
## address y:z.
HiddenServiceDir /home/tor/onion_ssh_service/
HiddenServicePort 22 127.0.0.1:22SSH onion-services
$ docker-compose up --build ssh$ docker exec -it onion_ssh /bin/bash
$ torsocks ssh -o IdentitiesOnly=yes -i /home/hiro/.ssh/key -v root@wklfdwgq5txfvq5v.onion
TorSOCKS
$ torsocks curl http://yjuwkcxlgo7f7o6s.onion/
- Torsocks is a wrapper use applications through the Tor network
- In this example, we run curl through the tor network and reach the onion address for archive.torproject.org
- We have a how-to torify apps [WIP]
Using the Socks5 Proxy
#!/usr/bin/env python3
# -*- coding: utf-8 -*-
import requests
proxies = {
'http': 'socks5://127.0.0.1:9050',
'https': 'socks5://127.0.0.1:9050'
}
r = requests.get('http://yjuwkcxlgo7f7o6s.onion/', proxies=proxies)
- We can use the SOCKS5 proxy provided by tor
- In this example, we fetch archive.torproject.org via its onion address

Onions for the
decentralised weB
Onion services can also be used for p2p applications:
-
OnionShare is a file sharing app that works by starting a web server, making it accessible as a Tor Onion Service, and generating an unguessable URL to access and download the files.
- https://onionshare.org
NEXT STEP
Start a container from any device and share any kind of service and make this as easy as opening an app!
Onions for the
decentralised weB
$ ./dev_scripts/onionpeer.py
api_client = docker.APIClient(base_url='unix://var/run/docker.sock')
client = docker.from_env()
build = [line for line in api_client.build(path='./containers/website',
tag='website',
dockerfile='./Dockerfile')]
container = client.containers.run('website:latest', detach=True)
nginx = container.exec_run('nginx', user='root').outputCyberspace.
A consensual hallucination experienced daily by billions of legitimate operators, in every nation, by children being taught mathematical concepts...
A graphic representation of data abstracted from banks of every computer in the human system. Unthinkable complexity. Lines of light ranged in the nonspace of the mind, clusters and constellations of data. Like city lights, receding...
William Gibson, Neuromancer
Learn more...
- www.torproject.org
- Tor Browser design doc
- Mozilla Firefox Extended Support Release
- Tor Projects
- Tor Rendezvous Specification - Version 3
- Secure Messaging with Onion Services, a How-To