DEEP WEB
Introduction to
presented by:
Hamid Salehian
-
Introduction
- Iceberg of Internet
- How big it is
- Deep vs Surface
-
Not Visible...
- Search Engines
- Reason of non Indexing
-
Darknet
- TOR
- Onion Routing
-
Pros and Cons
- Dark Side of the Deep Web
- The Bright Side
- Workshop (Dirty Hands)
- Summary
- Resources
Have Ever You Seen
THE ICEBERG
How Big ....
- The Deep Web contains 7,900 terabytes of information, compared to 19 terabytes of information in the Surface Web.
- 550 billion documents
- 500X surface web
- Google has identified 1.2 billion documents
- An Internet search typically searches .03% (1/3000) of available content.
*
* there are just estimation
Deep Web
- Not Discoverable
- Not Visible, Not Traceable
- Anonymously
- Darknet Content (TOR)
- Cannot Be Indexed
Surface Web
- Visible
- Indexed by conventional search engines
- Also called clearnet, visible web, indexed web




Not Visible...
Why!??
Search Engines
1st we need to knwo how
works
• Spider (crawler) will seek out webpage by going from one hyperlink to another and adding each page to it's catalog
• A program called an indexer then reads these webpages and creates an index, storing the URL and important content of webpage.
• Each search engine has its own ranking algorithm that returns results based on their relevance to the user’s specified keywords or phrases.
Search Engine
Why not Searchable
-
Some sites are not linked by other pages
-
Some sites require authentication before accessing the actual content (password-protected resources)
-
Difficult desing for indexer
-
The use of language JavaScript (like Ajax) misunderstood by spiders
-
Dynamic links (URL)
-
Darknet content
Darknet
- Computer network just like Internet
- Encrypted connection
- Accessed with specific software, configurations, or authorization
- Using non-standard communications protocols
| Normal Web Site | Darknet Hosted Web Site |
|---|---|
| The domain name (and associated registration details) | No owner details |
| The IP address (and thus the physical location and registered owner) | No physical location |
-
Researchers at the U.S. Naval Research Laboratory Originally designed Darknet to protect the identity of American operatives and dissidents in repressive countries like China
- Freenet (1999)
- GNUnet (2001)
- I2P (2003)
- TOR (2004) – most popular technology
Darknet (cont.)
TOR (The Onion Router)
-
Tor is a free software for for enabling anonymous communication.
-
Protects you by bouncing your communications around a distributed network of relays run by volunteers all around the world
-
Works on The Onion Routing technique
-
.onion Links
-
Access by Tor Browser
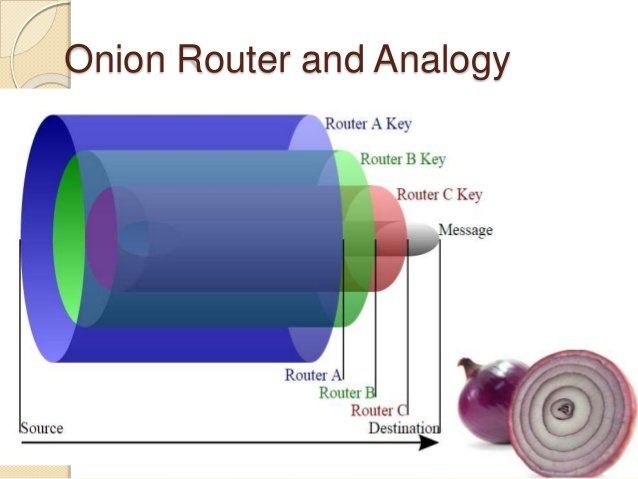
Onion Routing
-
Onion routing encrypts and decrypts data typically 3 or more separate times, once for each tor node it passes through on the way to the destination via the path given by the tor directory server.
-
It does this using the public key of the router(tor relay), which only the router’s private key can decrypt.
-
No single router knows the entire network path from source to destination.
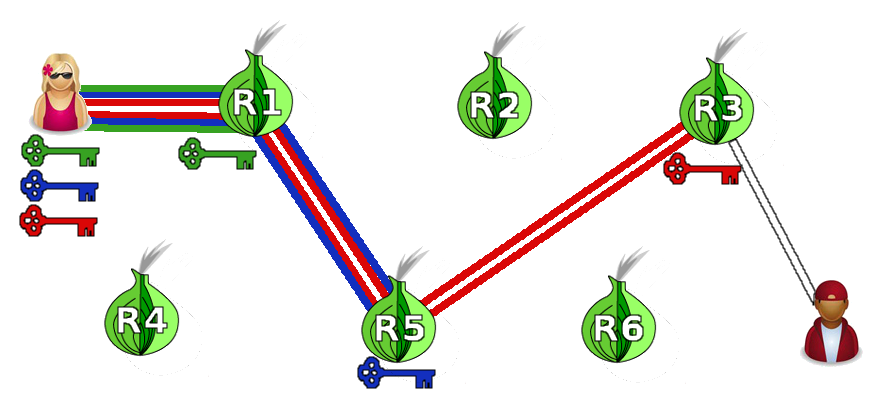
Alice
Bob
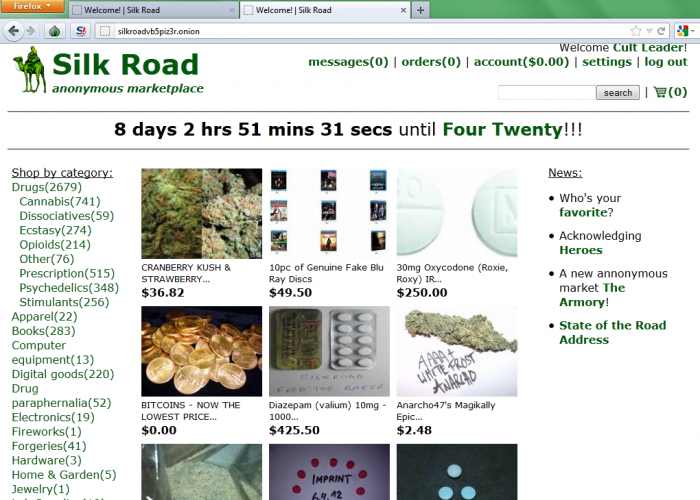
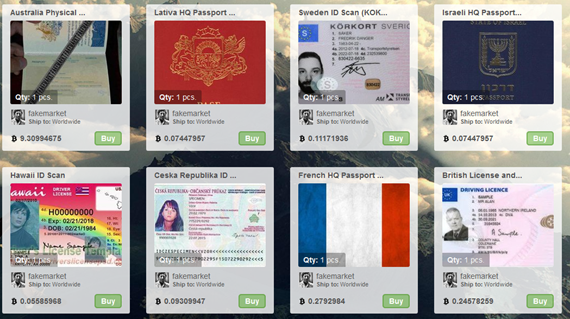
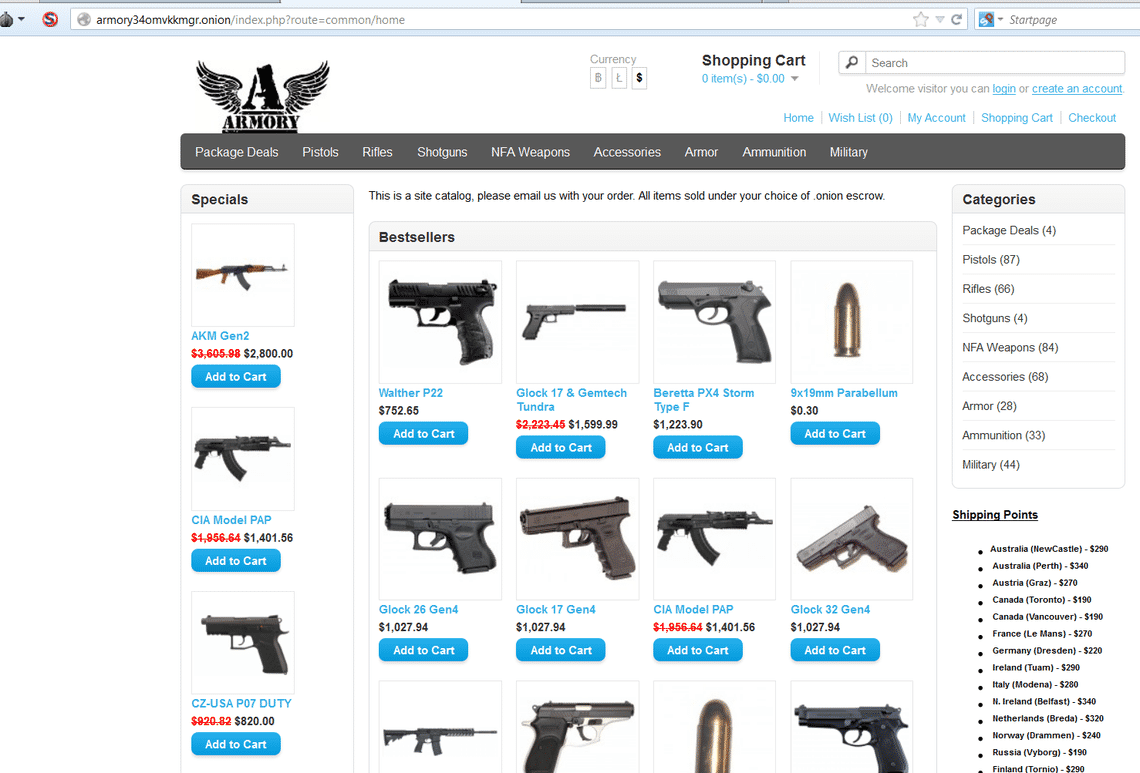
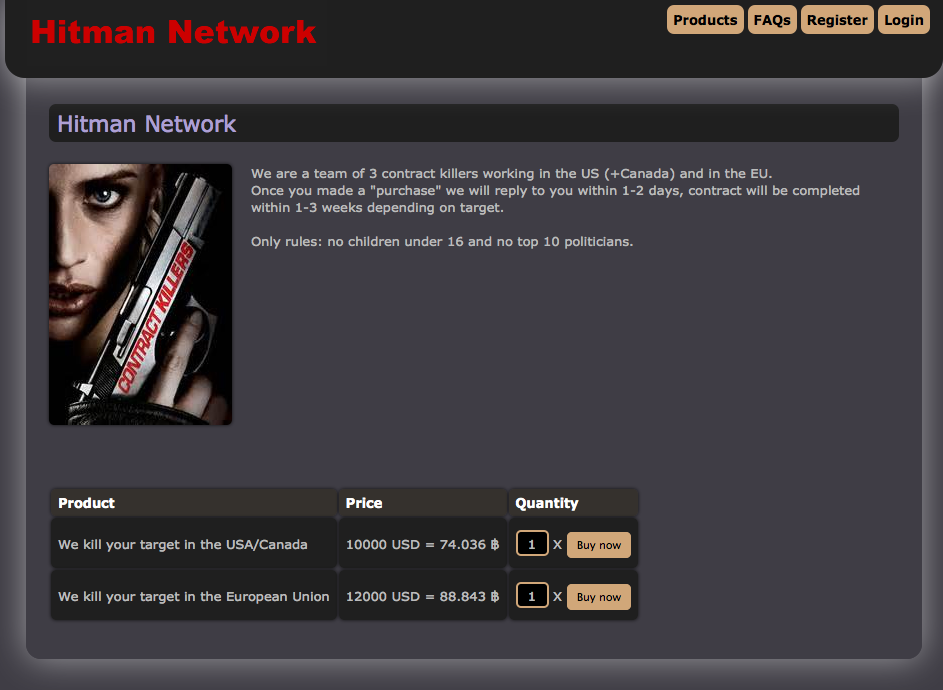
The Dark Side of The Moon
Deep Web
Ease of use: Surfing is more complex due the absence of indexing of the content
Speed: Slower to access than surface Web information.
Cybercrime: Inability to track down criminals. Activities range from the sales of illegal drugs and weapons, to hacking services, the hiring of contract killers etc...
Deep
Web
The Bright Side
"there is always something positive..."
Privacy and Security: Cannot know which connection is initiated as a user and which as node, making impossible the monitoring of the communications
Information: Access to private content and information (Government Security Info)
Freedom of speech and information: A way for people living under oppressive or restrictive regimes to reveal the truth like WikiLeaks



http://xmh57jrzrnw6insl.onion – TORCH – Tor Search Engine
http://xmh57jrzrnw6insl.onion - Freedom of Press Foundation
http://32rfckwuorlf4dlv.onion – Onion URL Repository
http://tuu66yxvrnn3of7l.onion – UK Guns and Ammo
http://dirnxxdraygbifgc.onion - OnionDir - Deep Web Link Directory
http://wlupld3ptjvsgwqw.onion/wlupload.en.html - WikiLeaks Submission Upload
http://rso4hutlefirefqp.onion/ - Medical Grade Cannabis Buds
http://newpdsuslmzqazvr.onion/ - THE PEOPLES DRUG STORE
http://smoker32pk4qt3mx.onion/ - Smokeables! Finest Organic Cannabis, shipping from the USA!
http://fzqnrlcvhkgbdwx5.onion/ - CannabisUK
Some .Onion Links
- Know the other side of internet (Deep Web)
- How Google works
- Why Google can't access Deep Web content
- Know why Deep Web is hidden
- Darknet
- TOR and Onion Routing Algorithm
- Know why Deep web has anonimity
- Pros and Cons of Deep Web
- Work with Tor Browser and see some .onion web pages
What you Know
Question!?
Resources
-
Bergman, Michael K , "The Deep Web: Surfacing Hidden Value". The Journal of Electronic Publishing , August 2001
-
http://www.nytimes.com/2009/02/23/technology/internet/23search.html?th&emc=th
-
Jesse Alpert & Nissan Hajaj, “We knew the web was big…”, 2008
-
http://googleblog.blogspot.com/2008/07/we-knew-web-was-big.html
-
https://en.wikipedia.org/wiki/Deep_web
-
https://www.deepdotweb.com/how-to-access-onion-sites/
-
http://www.deepwebsiteslinks.com/