Packages for Mass Consumpti n:
supply chain security concerns of
dependencies

Liran Tal

Developer Advocate at




// NodeGoat Core Team
// Node.js Security WG
Liran Tal

Developer Advocate at
@liran_tal
github.com/lirantal































































@liran_tal

"Installing an average npm package introduces an implicit trust on 79 third-party packages and 39 maintainers, creating a surprisingly large attack surface"
- Zimmerman et. al.
@liran_tal

2019















Your code
Challeneges in managing Open Source Deps at scale
1,538,483
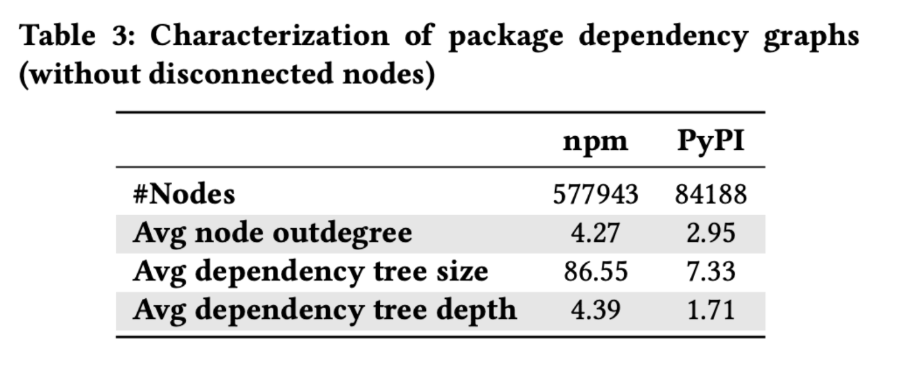
npm's Heavy reuse
Spring web framework
10 transitive dependencies

Express web framework
47 transitive dependencies










@liran_tal

src: https://snyk.io/stateofossecurity/
@liran_tal

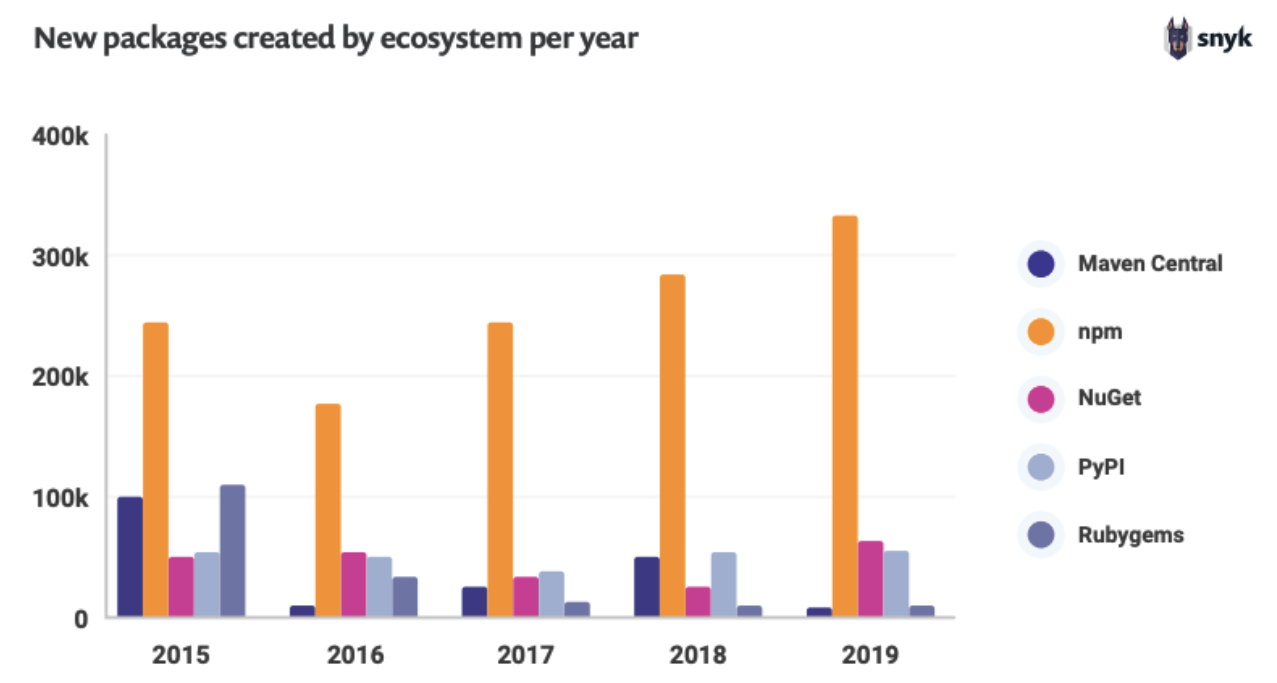
The Biggest Repository
Invites big risks

Lucrative attack playground

Open and free-to-publish ecosystem

Difficult to counter-measure
- Disconnect between SCM and Registry
- Commiter !== Publisher
@liran_tal

Small World with High Risks:
A Study of Security Threats in the npm Ecosystem
src: www.usenix.org/conference/usenixsecurity19/presentation/zimmerman
2019
@liran_tal

"a small, linear increase in direct dependencies leads to a significant, super-linear increase in transitive dependencies"
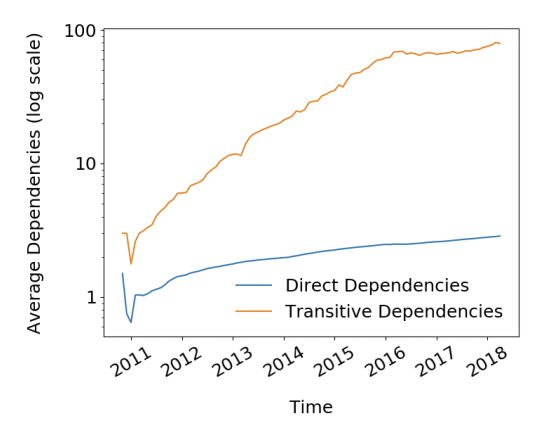
@liran_tal

"for the majority of the time the reach of vulnerable unpatched code is between 30% and 40% is alarming"
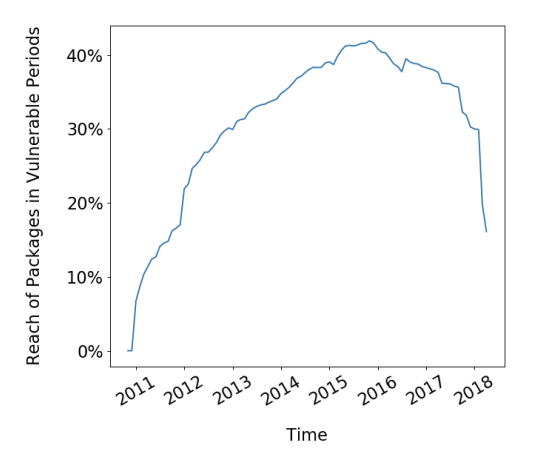
@liran_tal

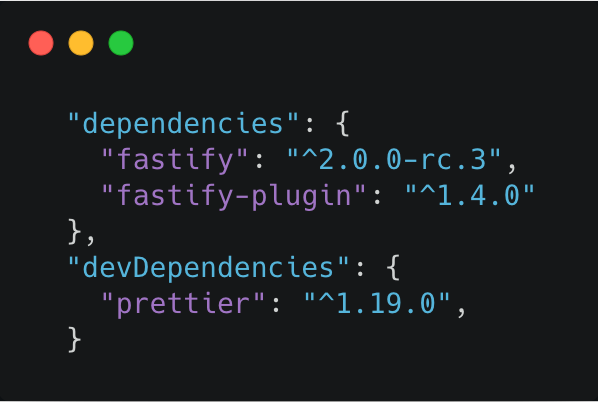
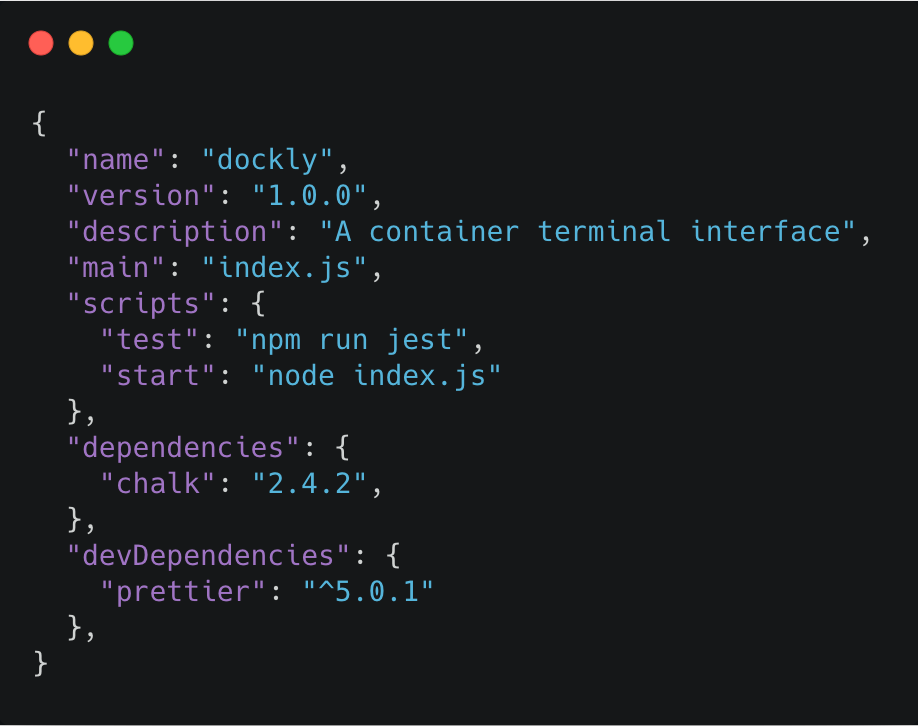
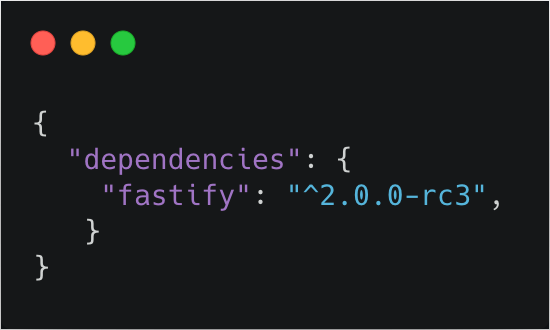
The Package Manifest
The package.json
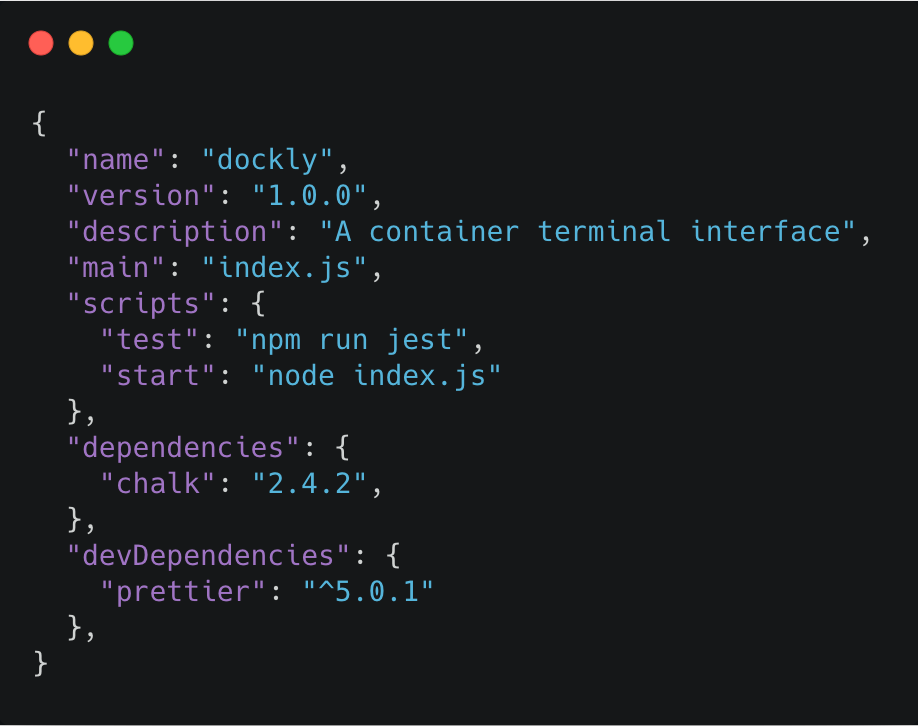
Dependencies
Package vs Version
Explicit package name + version

package.json

debug@4.1.0

debug@2.0.0

debug@4.1.0

debug@2.0.0

Package vs Version
The Package Manifest
The package.json
$ npm run test
"preinstall": "rm -rf /"How often do you npx ?
$ npx create-node-appTyposquatting Attacks
Compromised Accounts
Social Engineering
Malicious Modules



@liran_tal

Malicious Modules
time
Jan 2017
crossenv
@liran_tal

coffescript or coffe-script
coffeescript
@liran_tal

Malicious Modules
time
Jan 2017
crossenv
May 2018
getcookies
@liran_tal

Malicious Modules
time
Jan 2017
crossenv
May 2018
getcookies
Jul 2018
eslint-scope
@liran_tal

Malicious Modules
time
Jan 2017
crossenv
May 2018
getcookies
Jul 2018
eslint-scope
event-stream
Nov 2018
@liran_tal

Malicious Modules
time
electron-native-notify
2019
@liran_tal

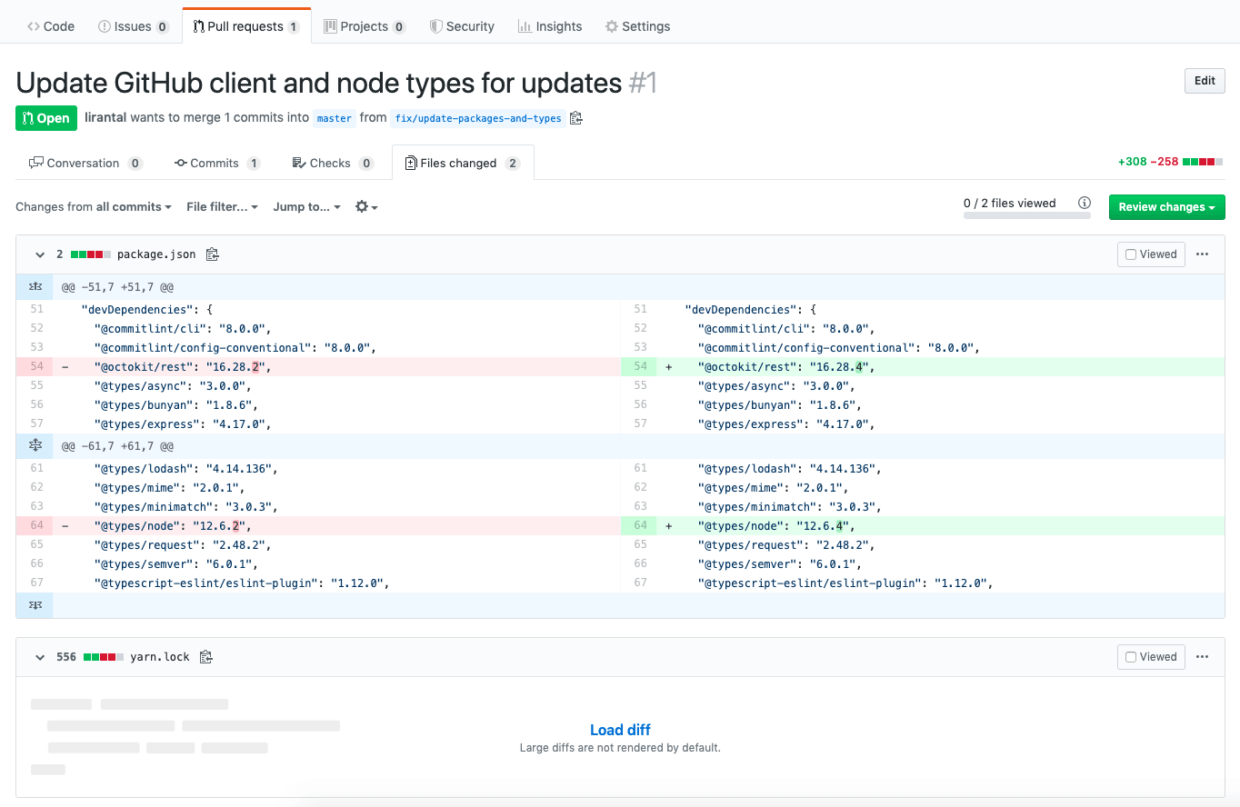
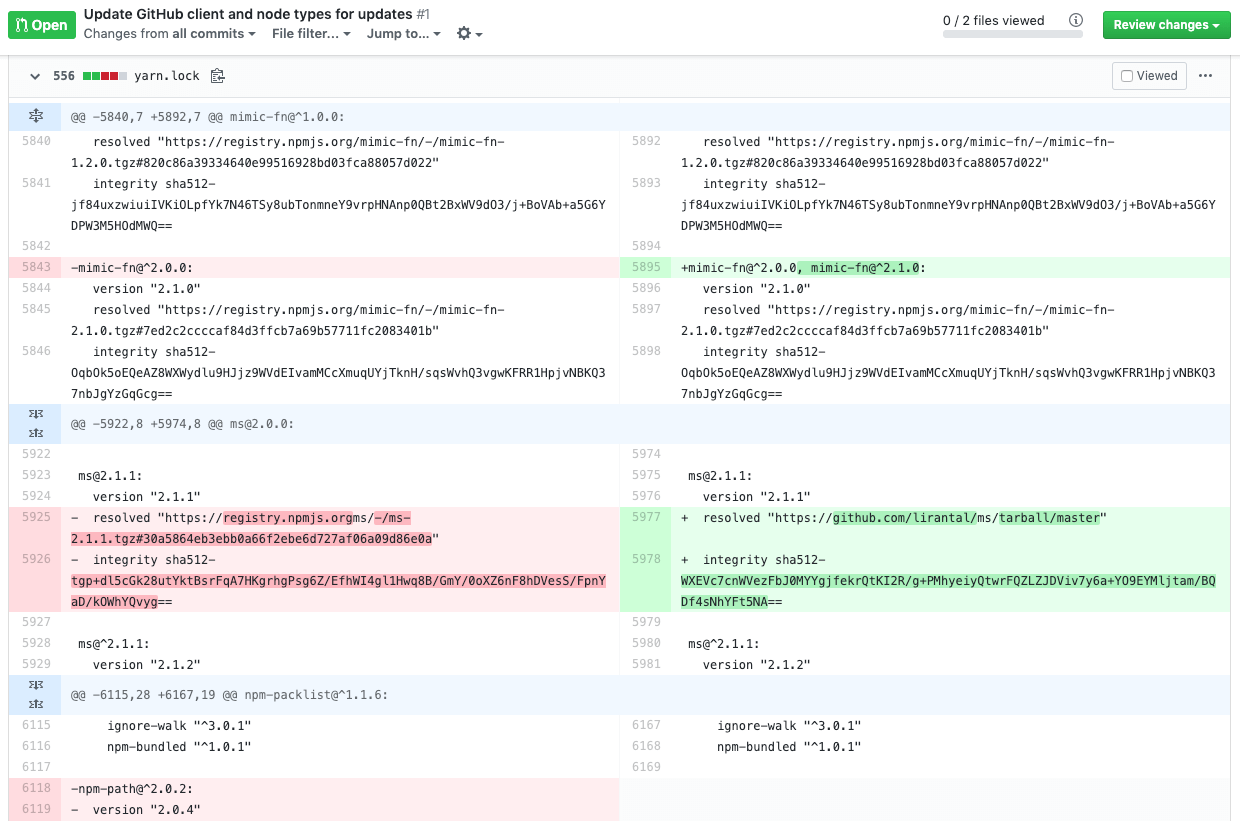
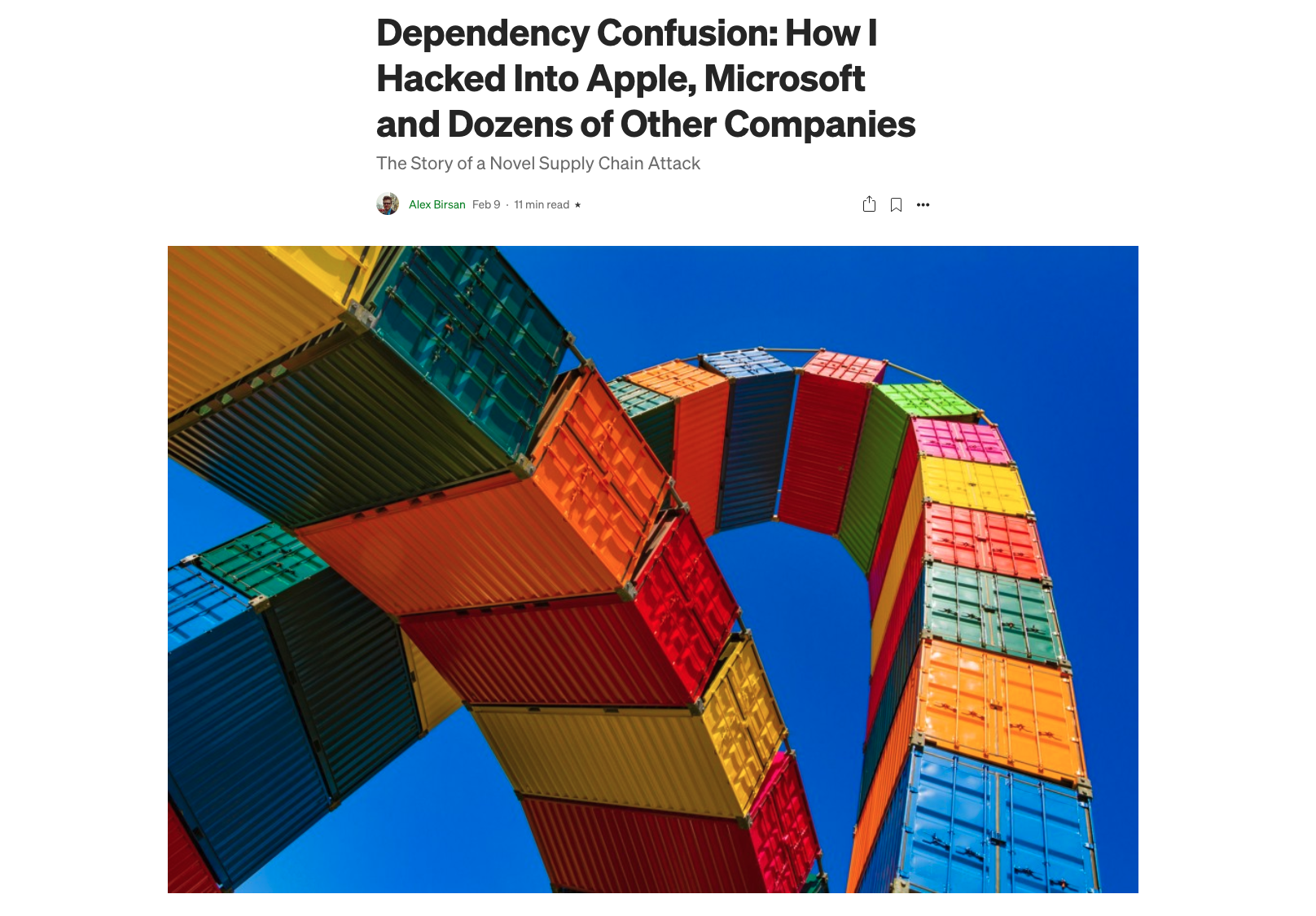
dependency confusion
2021
Semantic Versioning
1.4.6
Semantic Versioning
Major Change

1.4.6
1.4.6
Breaking API

Semantic Versioning
Patch, bug fix

1.4.6
1.4.6
Security fix

Lockfiles
installs based on a dep range is not deterministic

package-lock.json

yarn.lock

The security blindspot of
lockfile attack vectors
@liran_tal

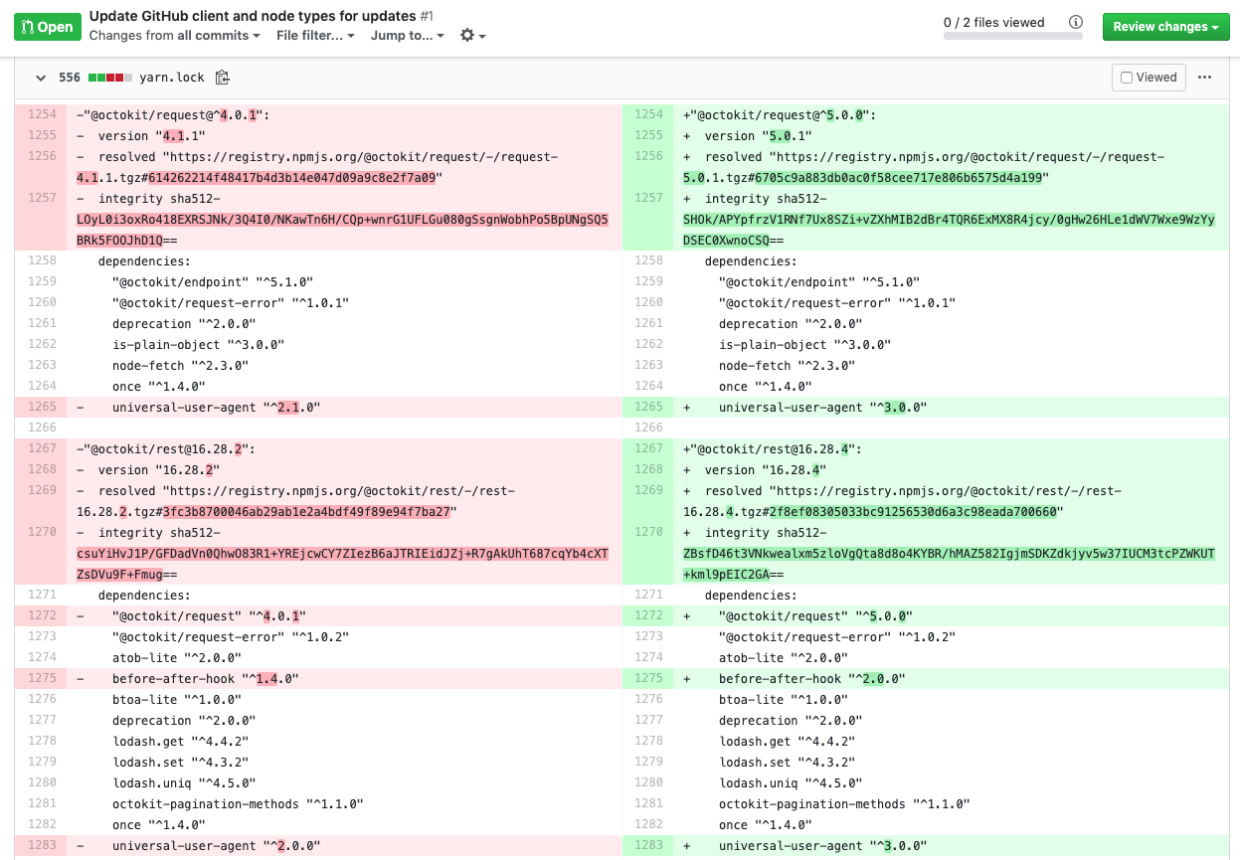
$ npm install lockfile-lint


Lockfiles
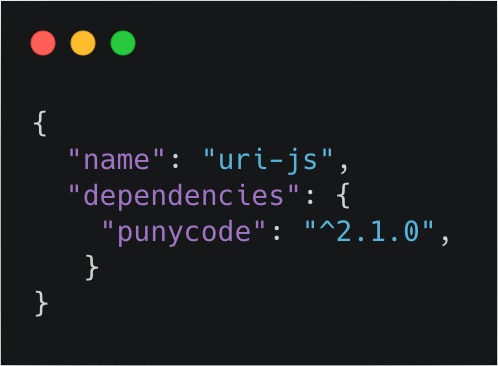
Dependency Confusion
substitution of private packages with
malicious from public repositories
Dependency Confusion
npm install

package-lock.json

source: https://snyk.io/blog/software-supply-chain-security
{
"nodemon": "latest"
}
npm update

npm ci

.npmrc

proxy well-configured

How deep
the rabbit hole goes?

image source: https://www.businessintelligenceinfo.com/tag/magic/page/2
what happens when a dependency breaks?
package.json



breaking changes in the API
why would a package break?

package has been compromised

npmjs is unavailable

networking disruptions

maintainer pulled down the package
???
it's open source.
everyone can do as they please.
what's the worst that can happen?

maintainer pulled down the package
1. Azer Koçulu maintains 273 npm modules
2. 3/2016 - Lawyer threatened Azer to wave-off Kik
3. Azer refused, but npm staff changed ownership
4. As an act of protest Azer removed all of his modules
5. One of those was a little thing called left-pad
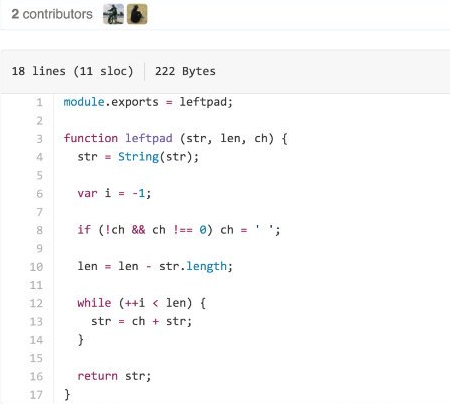
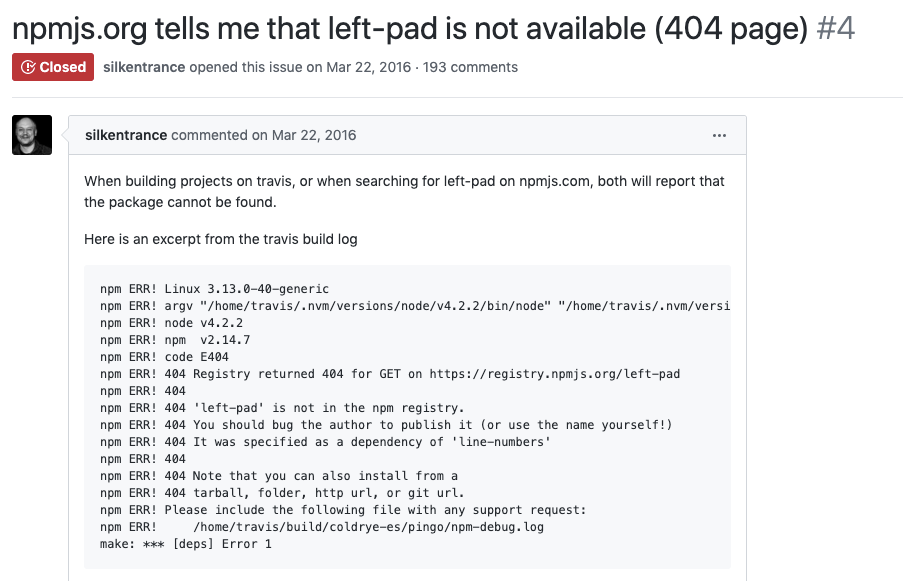
1. Reminder: left-pad is now unpublished
2. Cameron Westland pushed a new left-pad@1.0.0
3. Many builds were still broken as they require ^0.0.3
4. npm re-publishes 0.0.3 from backups
5. total incident time: 2.5 hours
2.1. What if this was a malicious user?
source: https://snyk.io/blog/how-much-do-we-really-know-about-how-packages-behave-on-the-npm-registry

package has been compromised
14%
compromised npm modules
20%
npm total monthly downloads
express
react
debug
moment
request

Compromised Contributors ?
1409
users
had their password set to
their username
Compromised Contributors ?
Compromised Contributors ?
koa
developer
password
had their password set to
Compromised Contributors ?
Compromised Contributors ?
11%
users
had their password set to
previously leaked password
Compromised Contributors ?
2FA Enabled accounts
since npm >= 5.5.1
2018: 6.89%
@liran_tal

2020: 9.87%
Conclusion?
PLEASE ENABLE 2FA

PLEASE ENABLE 2FA

PLEASE ENABLE 2FA

PLEASE ENABLE 2FA

Enterprise Readyness

Why do you need a local npm?
The official registry might fail

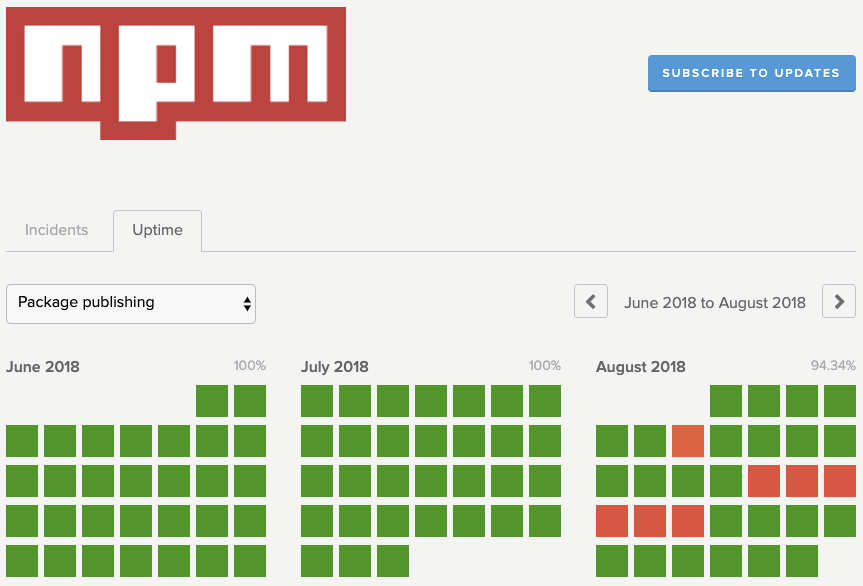
Why do you need a local npm?
Networks disruptions

Bandwidth considerations

Local npm/yarn cache is per dev

Offline and optimal speeds

Why do you need a local npm?
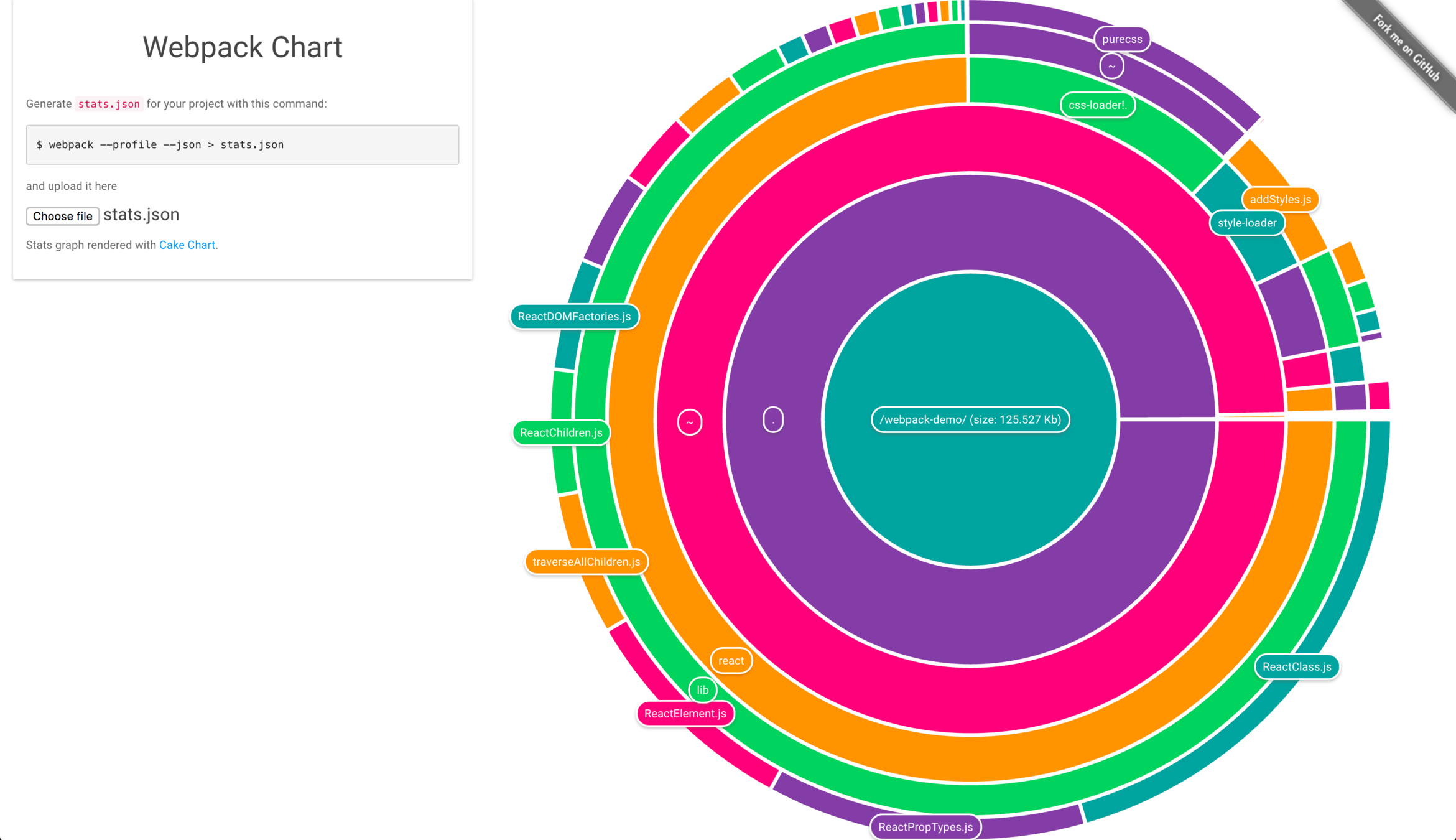
webpack@4.28.3

24 direct dependencies
1,690 total dependencies
1,802 requests to the npm registry
190MB unzipped on disk




Why do you need a local npm?
Packages could suddenly get yanked

Private package hosting cost money

Verdaccio

A Lightweight private npm proxy registry
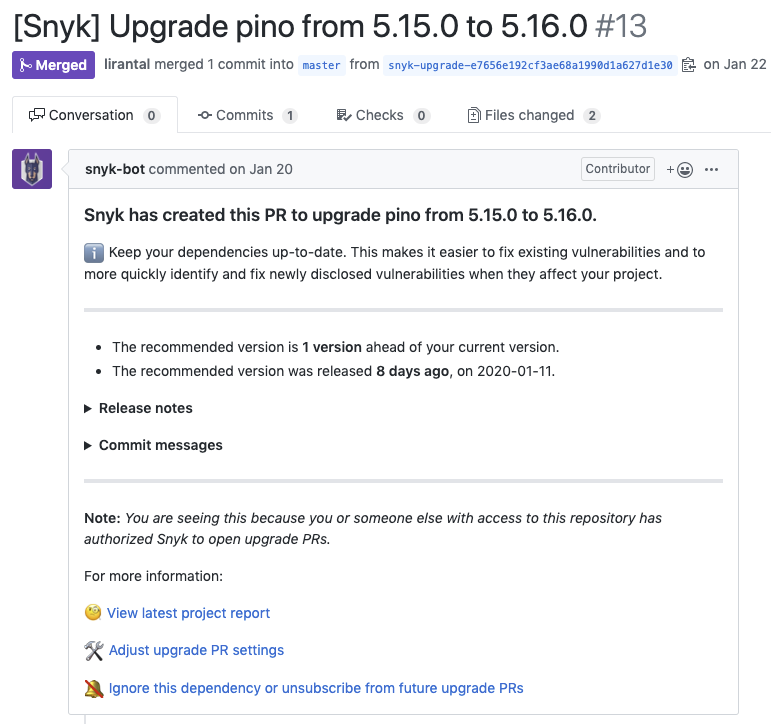
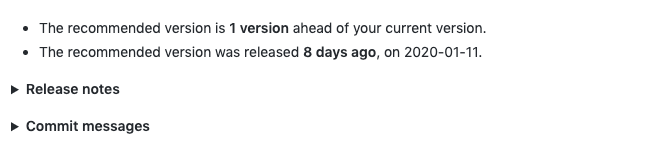
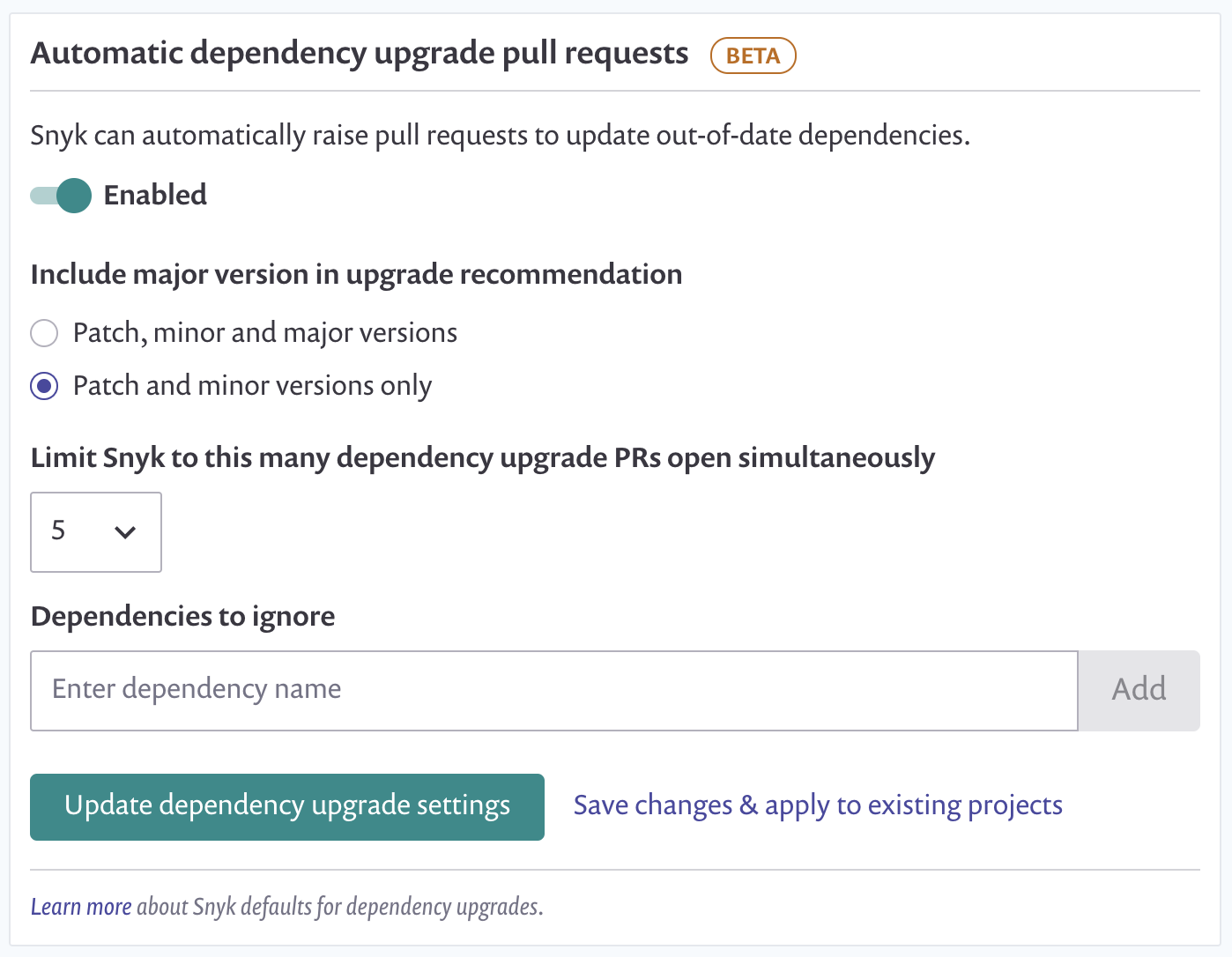
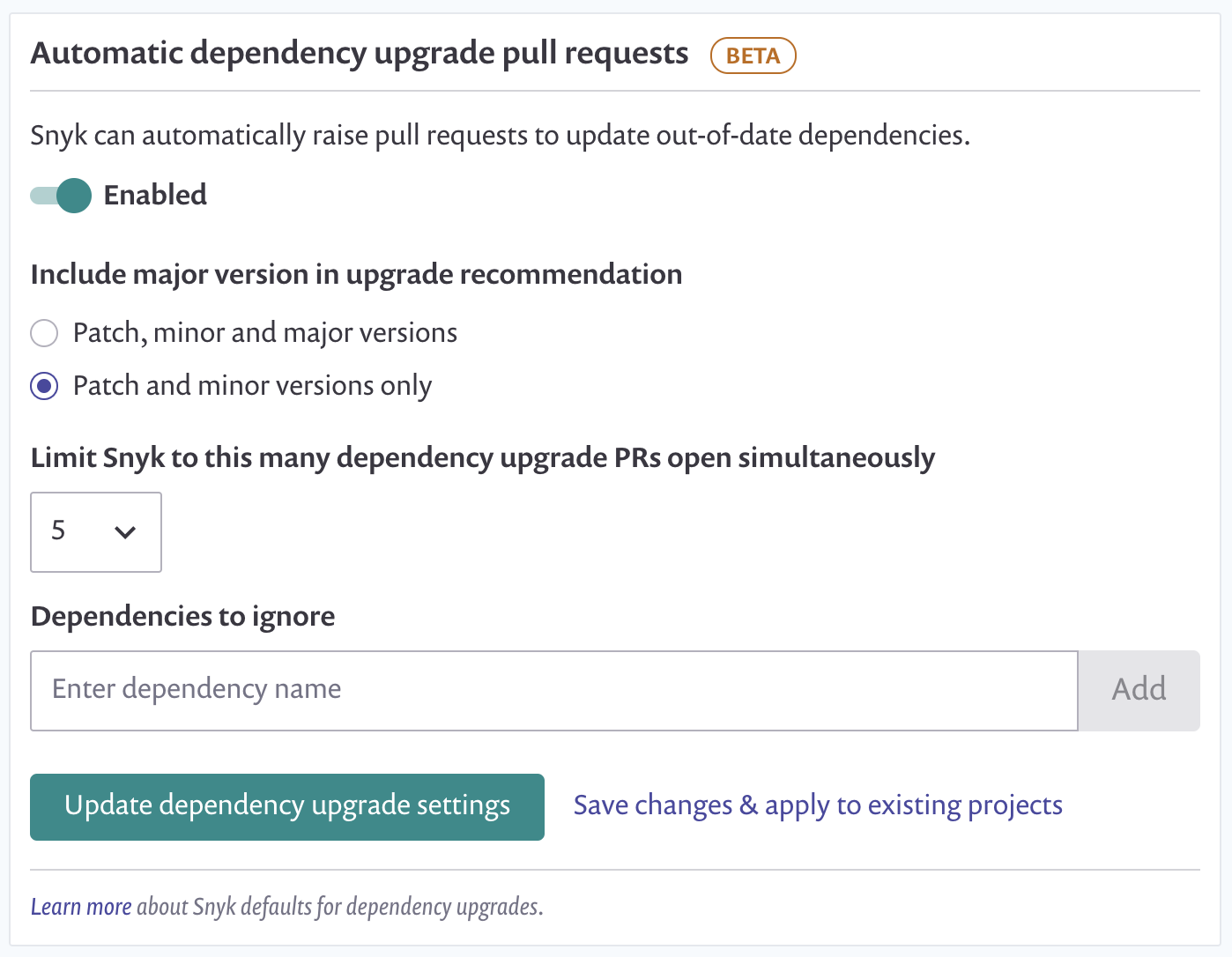
Automated Dependency Management
at scale

How do you choose packages?
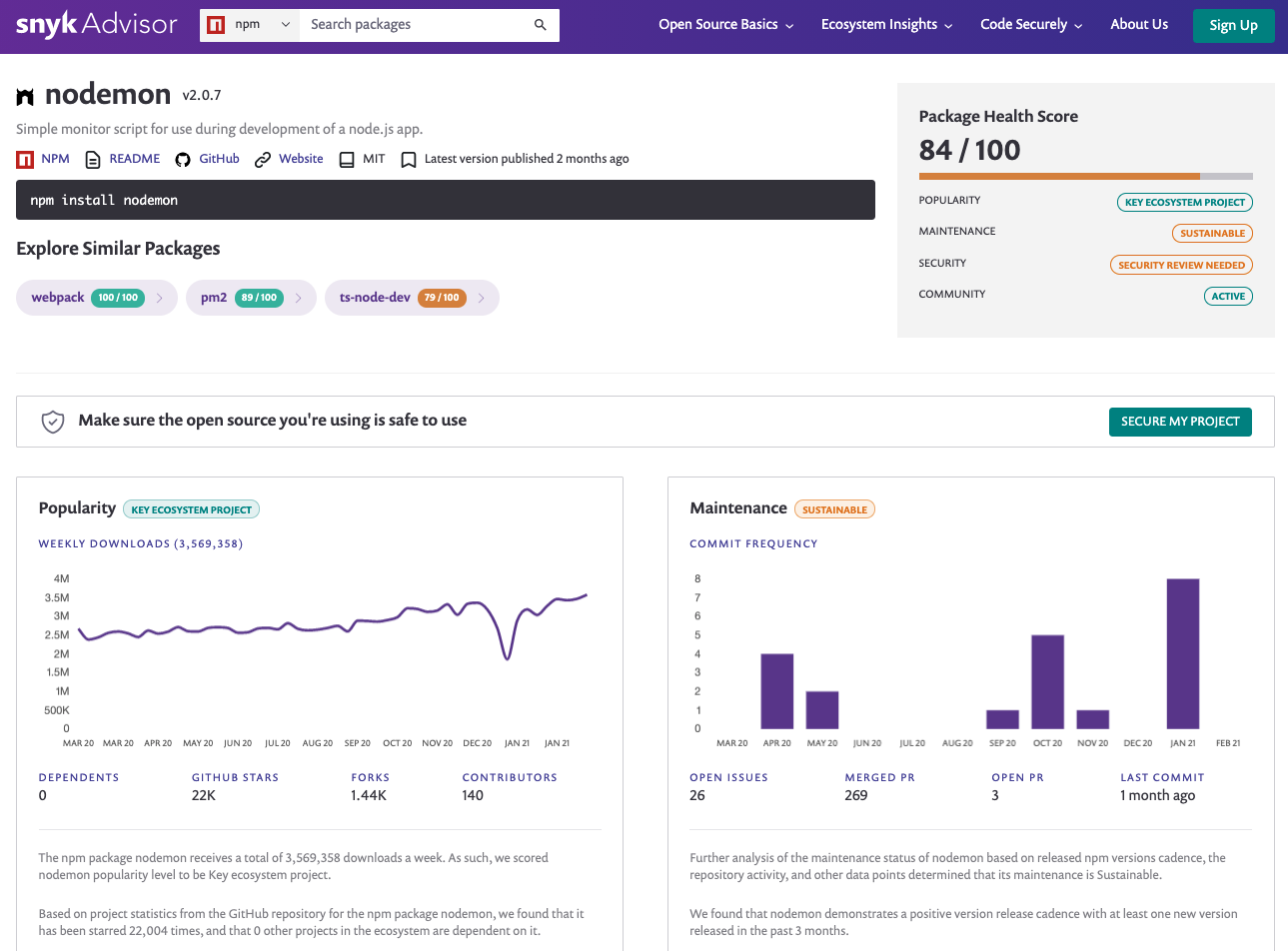
source: https://snyk.io/advisor
Pro Patterns for Teams

npm ci

yarn install --frozen-lockfile

✅ Speed
✅ Surprise-free builds
{
{
solution?
what do I get?
{
my problem is
my CI builds are slow and aren't deterministic with devlopment
use nvm

✅ All team members use the same Node.js version
✅ npm version can also be set
{
{
solution?
what do I get?
{
my problem is
my developers often can't reproduce the bug in production in their envs
$ npm install xyz --ignore-scripts

✅ Script hooks won't be auto-run
❌ May cause grief with other npm run-scripts
{
{
solution?
what do I get?
{
my problem is
I am concerned installing Node.js modules will run malicious code
$ npm config set ignore-scripts true

$ snyk test

✅ Understand which deps you use
{
{
solution?
what do I get?
{
my problem is
what if I'm using packages with known security vulnerabilities?
$ npm audit or owasp dependency check as fallbacks

✅ Get dependency health stats
✅ Test packages for security issues
$ npm profile enable-2fa auth-and-writes

✅ Every npm publish or login will require 2FA to execute
{
{
solution?
what do I get?
{
my problem is
will someone compromise my npm account and publish malicious code?
enable 2fa

use files: [] in package.json

✅ Avoid accidentally leaking sensitive data to the publish registry
{
{
solution?
what do I get?
{
my problem is
I accidentally leaked some secrets in a config file when I published a pkg
use detect-secrets module in your git hooks


Liran Tal

Developer Advocate at
@liran_tal
github.com/lirantal

