Anonymous Tokens
Michele Orrù
joint work with Ben Kreuter, Tancrède Lepoint, Mariana Raykova
Definition
Anonymous tokens are lightweight, single-use anonymous credentials.
… we focus on secret-key tokens with a private metadata bit.
The Problem
\(\mathcal{U}\)
[CloudFlare]
[Tor User]
[CDN]
request
solution?
challenge
\(\mathcal{I}\)
\(\mathcal{W}\)
request
response
response / no
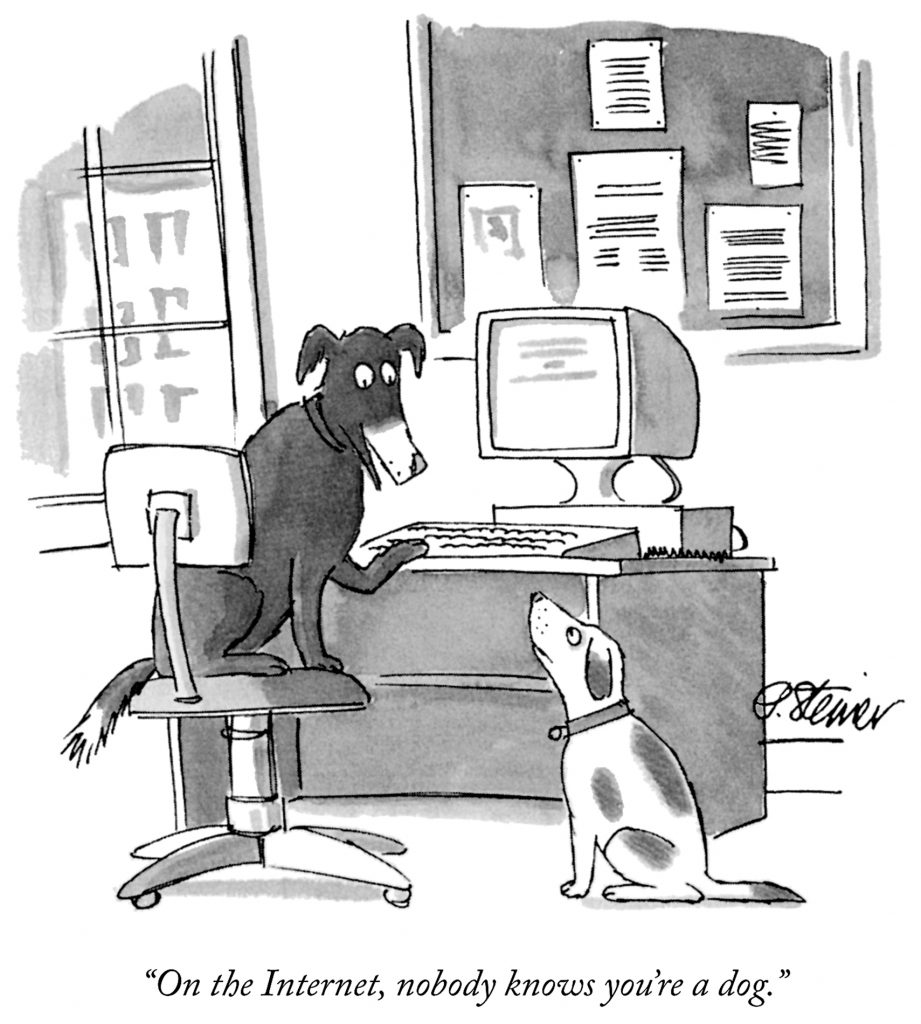
Privacy Pass: Bypassing Internet Challenges Anonymously. [PETS'18]
Website protection.
CloudFlare's story
\(\mathcal{U}\)
[CloudFlare]
[Tor User]
[CDN]
request
solution?
\(\mathcal{I}\)
\(\mathcal{W}\)
request
response
response / no
Privacy Pass: Bypassing Internet Challenges Anonymously. [PETS'18]
CAPTCHA, CAPTCHA, CAPTCHA
CloudFlare's story
Website protection.
Art credits: Marie Gutbub. [source]

\(\mathcal{U}\)
[CloudFlare]
[Tor User]
[CDN]
challenge
solution?
challenge
\(\mathcal{I}\)
\(\mathcal{W}\)
request
response
response + tokens / no
Privacy Pass: Bypassing Internet Challenges Anonymously. [PETS'18]
CloudFlare's story
request
Website protection.
\(\mathcal{U}\)
[CloudFlare]
[Tor User]
[CDN]
request, token
\(\mathcal{I}\)
\(\mathcal{W}\)
request
response
Privacy Pass: Bypassing Internet Challenges Anonymously. [PETS'18]
response / no
CloudFlare's story
Website protection.
Micro payments.
Other stories
Challenge bypass on the Ristretto group. [Github]

Fraud prevention.
Other stories

Fighting fraud using partially blind signatures. [Facebook Engeneering Blog]

Deprecating 3rd party cookies.
Other stories
Building a more private web: A path towards making third party cookies obsolete. [Chromium Blog]
Private medatada
token?
✗
\(\mathcal{I}\)
𝒜
Private metadata
\(\mathcal{I}\)
token?
\(\dots\)
request, \(\sigma^{(b)}\)
\(\sigma^{(b)}\)
\(b\)
𝒜
The (formal) problem
\(\sigma \gets \langle \mathcal{U}(\mathsf{pp}, t), \mathcal{I}(\mathsf{sk}, b)\rangle\)
Issuance protocol:
Redemption algorithm:
\(\{0, 1,\perp\}\gets \mathcal{V}(\mathsf{sk}, t, \sigma)\)
Security notions
- Unlinkability
𝒜
\(\mathcal{U}_1\)
\(\vdots\)
\((t_i, \sigma_i)\)
\(i\)
\(\mathcal{U}_2\)
\(\mathcal{U}_n\)
Security notions
- Unlinkability
- One-more unforgeability
\(\mathcal{I}\)
𝒜
\((t_i, \sigma_i)_{i=1}^{\ell+1}\)
\(\vdots\)
\((\ell)\)
\((1)\)
Security Notions
- Unnlinkability
- One-more unforgeability
- Privacy of the metadata bit
\(\mathcal{I} (\mathsf{sk}, b\!=\!0)\)
\(\mathcal{I} (\mathsf{sk}, b\!=\!1)\)
\({\stackrel{\tiny\textsf{ind.}}{\equiv}}\)
Standardization
W3C: Trust Token API
IETF: Privacy Pass draft
fetch('https://iacr.org/.well-known/trust-token', {
trustToken: {
type: 'token-request',
issuer: 'ens.fr'
}
});
[Example derived from the original proposal.]
fetch('https://eprint.iacr.org/2020/072.pdf', {
trustToken: {
type: 'raw-token-redemption',
issuer: 'ens.fr'
}
});
1. Introduction
In some situations, it may only be necessary to check that a client
has been previously authorized by a service; without learning any
other information. Such lightweight authorization mechanisms can be
useful in quickly assessing the reputation of a client in latency-
sensitive communication.[Draft version 00.]
Our contribution
- Formalization of Anonymous Tokens;
- Private Metadata extension;
- New techniques for removal of zk proofs.
Related works
- Anonymous Credentials
- Algebraic MACs
- Blind Singatures
Privacy Pass
\(W' := x T'\)
\(T'\)
\(W'\)
\(\cdots\) redemption \(\cdots\)
\(t, W\)
- check \(x\mathsf{H}(t) = W\)
- add \(t\) to spent tokens.
User
Issuer
\(\Gamma := (p, \mathbb{G}, G)\)
\(r \gets \mathbb{Z}_p^*\)
\(T' := r^{-1}\mathsf{H}(t)\)
\(W := r W'\)
\(X = xG\)
\(\pi := \mathsf{zkp}\left\{ x\begin{bmatrix}G\\T'\end{bmatrix} = \begin{bmatrix}X\\ W'\end{bmatrix}\right\} \)
, \(\pi\)
check \(\pi\)
Privacy Pass
\(W' := x T'\)
\(T'\)
\(W'\)
\(\cdots\) redemption \(\cdots\)
\(t, W\)
- check \(x\mathsf{H}(t) = W\)
- add \(t\) to spent tokens.
User
Issuer
\(\Gamma := (p, \mathbb{G}, G)\)
\(r \gets \mathbb{Z}_p^*\)
\(T' := r^{-1}\mathsf{H}(t)\)
\(W := r W'\)
\(X = xG\)
\(\pi := \mathsf{zkp}\left\{ x_b\begin{bmatrix}G\\T'\end{bmatrix} = \begin{bmatrix}X_b\\ W'\end{bmatrix}\right\} \)
\(W' := x_b T'\)
\(X = x_bG,~~ b \in \{0, 1\}\)
- check \(b\) s.t. \(x_b\mathsf{H}(t) = W\)
- add \(t\) to spent tokens.
Private metadata?
, \(\pi\)
check \(\pi\)
\(T'\)
\(W'\)
\(\cdots\) redemption \(\cdots\)
\(t, W\)
User
Issuer
\(\Gamma := (p, \mathbb{G}, G)\)
\(r \gets \mathbb{Z}_p^*\)
\(T' := r^{-1}\mathsf{H}(t)\)
\(W := r W'\)
Attack
\(r, s \gets \mathbb{Z}_p^*\)
\(T' := r^{-1}\mathsf{H}(t)\)
\(S' := s^{-1}\mathsf{H}(t)\)
\(W' := x_0 T'\)
Adversary
\(r W' \stackrel{?}{=} s V'\)
Issuer
\(T'\)
\(W'\)
\(X_b = x_bG,~~ b \in \{0, 1\}\)
\(\Gamma := (p, \mathbb{G}, G)\)
\(S'\)
\(V' := x_1 S'\)
\(V'\)
\(W := x T' + yS'\)
\(\pi := \mathsf{zkp}\left\{x\begin{bmatrix}G\\T'\end{bmatrix} + y\begin{bmatrix}H\\S'\end{bmatrix} = \begin{bmatrix}X\\ W'\end{bmatrix}\right\} \)
\(W := r W'\)
\(S := r \mathsf{H}(T', s)\)
check \(\pi\)
\(T'\)
\(s, W'\)
, \(\pi\)
\(s \gets \{0, 1\}^\lambda;~ S' := \mathsf{H}(T', s)\)
\(X = xG +yH\)
\(\cdots\) redemption \(\cdots\)
\(t, S, W\)
- check \(x\mathsf{H}(t) + yS= W\)
- add \(t\) to spent tokens.
Privacy Pass variant
User
Issuer
\(\Gamma := (p, \mathbb{G}, G, H)\)
\(r \gets \mathbb{Z}_p^*\)
\(T' := r^{-1}\mathsf{H}(t)\)
\(\pi := \mathsf{zkp}\left\{x_b\begin{bmatrix}G\\T'\end{bmatrix} + y_b\begin{bmatrix}H\\S'\end{bmatrix} = \begin{bmatrix}X_b\\ W'\end{bmatrix}\right\} \)
\(W := r W'\)
\(S := r \mathsf{H}(T', s)\)
check \(\pi\)
\(T'\)
\(s, W'\)
, \(\pi\)
\(X_b = x_bG +y_bH,~~ b \in \{0, 1\}\)
\(\cdots\) redemption \(\cdots\)
\(t, S, W\)
- check \(b\) s.t. \(x_b\mathsf{H}(t) + y_b S = W\)
- add \(t\) to spent tokens.
Private metadata
User
Issuer
\(\Gamma := (p, \mathbb{G}, G, H)\)
\(r \gets \mathbb{Z}_p^*\)
\(T' := r^{-1}\mathsf{H}(t)\)
\(W := x_b T' + y_bS'\)
\(s \gets \{0, 1\}^\lambda;~ S' := \mathsf{H}(T', s)\)
Removing the zk proof
\(W' := x T'\)
\(T'\)
\(W'\)
\(\cdots\) redemption \(\cdots\)
\(t, W\)
- check \(x\mathsf{H}(t) = W\)
- add \(t\) to spent tokens.
User
Issuer
\(\Gamma := (p, \mathbb{G}, G)\)
\(r, \rho \gets \mathbb{Z}_p^*\)
\(T' := r(\mathsf{H}(t) - \rho G)\)
\(W := r^{-1} W' + \rho X\)
\(X = xG\)
Concrete security
- One-more Diffie-Hellman is not extensively studied;
- Token Hijacking;
- Engeneering issues.
Implementation
#[test]
fn it_works() {
let mut csrng = rand::rngs::OsRng;
// generate a keypair
let keypair = KeyPair::generate(&mut csrng);
// get the public parameters
let pp = PublicParams::from(&keypair);
// client's first message (the blinded token)
let blinded_token = pp.generate_token(&mut csrng);
// server's reponse (the signed token) with hidden metadata bit 0
let signed_token = keypair.sign(&mut csrng, &blinded_token.to_bytes(), 0);
// clien'ts unbliding (the final token)
let token = blinded_token.unblind(signed_token);
assert!(token.is_ok());
// verification of the token
assert!(keypair.verify(&token.unwrap()).is_ok());
}
In Rust, using curve25519-dalek::Ristretto.
Check out [benchmarks report] for fancy stats.