Aggregate Cash Systems:
a cryptographic investigation of Mimblewimble
Michele Orrù
joint work with Georg Fuchsbauer, Yannick Seurin

Mimblewimble
A cryptocurrency that improves on privacy, fungibility, and scalability.
Core ideas:
-
CoinJoin [Maxwell]
-
transaction cut-through [Maxwell]
-
confidential transactions [Back, Maxwell]
Further investigations: Andrew Poelstra.
Bitcoin Transactions
Each input spends an output of a previous transaction. For each input there is a signature validating the spending.
Tx
\(\textsf{in}\)
\(\textsf{out}\)
Tx
\(\textsf{in}\)
\(\textsf{out}\)
Tx
\(\textsf{in}\)
\(\textsf{out}\)
\(v_0, \mathsf{vk}_0\)
\(\sigma_0\)
\(v_2, \mathsf{vk}_2\)
\(v_1, \mathsf{vk}_1\)
\(\sigma_1\)
\(\sigma_3\)
\(\sigma_4\)
\(v_5, \mathsf{vk}_5\)
\(v_6, \mathsf{vk}_6\)
Coinbase transaction
balanced, i.e.:
\(\sum \mathsf{in} = \sum \mathsf{out}\)
\(\textsf{UTXO}\)

Blockchain vs UTXO size
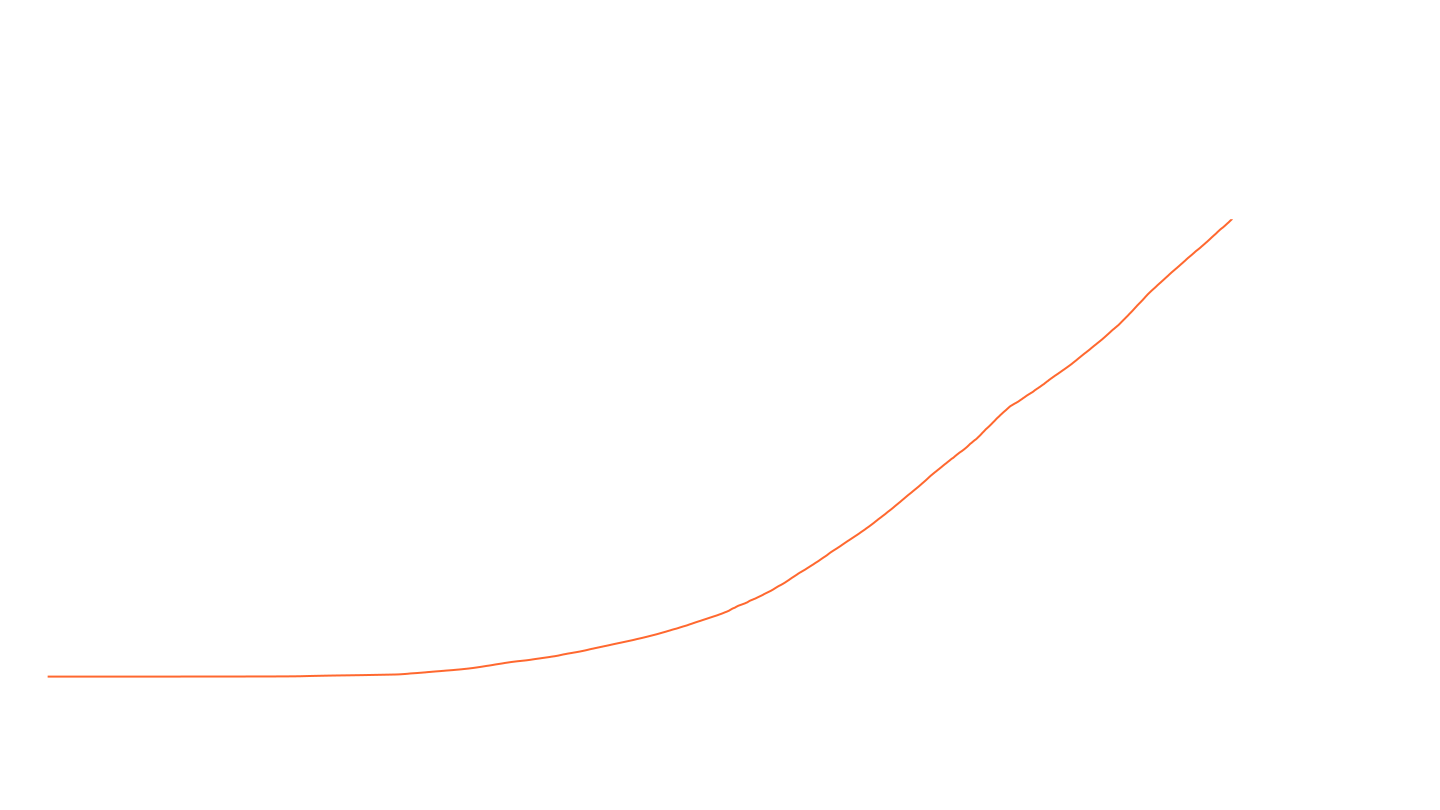
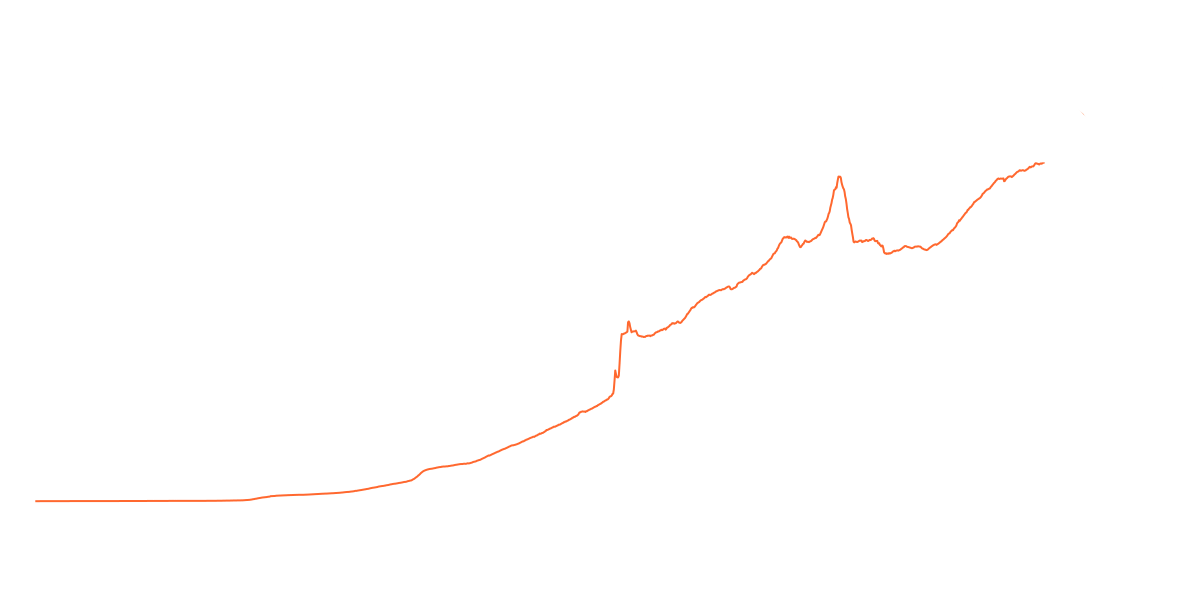
«The amount of bandwidth and processing power needed to catch up with the system should be proportional to the current state of the system.»
— Grindelwald (A. Poelstra), Mimblewimble

(~ 4GB)
Tx
\(\textsf{in}\)
\(\textsf{out}\)
\(v_0, \mathsf{vk}_0\)
\(v_1, \mathsf{vk}_1\)
\(\sigma_0\)
Tx
\(\textsf{in}\)
\(\textsf{out}\)
\(v_2, \mathsf{vk}_2\)
\(\sigma_2\)
Tx
\(\textsf{in}\)
\(\textsf{out}\)
\(v_n, \mathsf{vk}_n\)
\(\sigma_n\)
,
...
,
Tx
\(\textsf{in}\)
\(\textsf{out}\)
\(v_0, \mathsf{vk}_0\)
\(v_1, \mathsf{vk}_1\)
\(\sigma_0\)
\(\sigma_1\)
\(\vdots\)
\(\sigma_n\)
\(\vdots\)
\(v_n, \mathsf{vk}_n\)

shuffle
CoinJoin
Combine multiple payments into a single transaction.

…requires coordination!
,
Cut-Through
Matching inputs and outputs can be eliminated. (Not really possible in Bitcoin.)
Tx
\(\textsf{in}\)
\(\textsf{out}\)
\(A\)
\( B\)
Tx
\(\textsf{in}\)
\(\textsf{out}\)
\(B\)
\(C\)
Confidential Transactions
The amounts involved in a transaction are hidden.
Consider a cyclic group \(\mathbb{G} = \langle G \rangle = \langle H \rangle \) of prime order \(p\).
Replace values with Pedersen commitments:
$$C_i \coloneqq v_i H + r_i G.$$
Balanced if:
$$(v_1 + v_2 - v_0)H + (r_1 + r_2 - r_0)G = \mathbf{0}.$$
That is:
$$v_1 + v_2 -v_0 = 0 \qquad r_1 + r_2 - r_0 = 0$$

\(\textsf{in}\)
\(\textsf{out}\)
\(\sigma_0\)
\(C_1',~\mathsf{vk}_1\)
\(C_2', ~\mathsf{vk}_2\)
\(C_0, \mathsf{vk}_0\)
Tx
Confidential Transactions
The amounts involved in a transaction are hidden.
Consider a cyclic group \(\mathbb{G} = \langle G \rangle = \langle H \rangle \) of prime order \(p\).
Replace values with Pedersen commitments:
$$C_i \coloneqq v_i H + r_i G.$$
Balanced if:
$$(v_1 + v_2 - v_0)H + (r_1 + r_2 - r_0)G = \mathbf{0}.$$
That is:
$$v_1 + v_2 -v_0 = 0 \qquad r_1 + r_2 - r_0 = 0$$
\(\textsf{in}\)
\(\textsf{out}\)
\(\sigma_0\)
need rangeproof \(\pi\)!

\(C_1',~ \pi_1', \mathsf{vk}_1\)
\(C_2', ~\pi_2', \mathsf{vk}_2\)
\(C_0, \pi_0, \mathsf{vk}_0\)
Tx
Mimblewimble
Coins:
Transactions:
\(\textsf{in}\)
\(\textsf{out}\)
\(C_1',~ \pi_1', \mathsf{vk}_1\)
\(C_2', ~\pi_2', \mathsf{vk}_2\)
\(\mathsf{Tx}\)
\(C_0, \pi_0, \mathsf{vk}_0\)
[Pedersen commitments, coming with a rangeproof]
Sample \(r_0 \stackrel{\$}{\leftarrow}\mathbb{Z}_p\).
$$C_0 \coloneqq v_0H + r_0G $$
\(C_0, \sigma_0\)
Coins:
Transactions:
\(\textsf{in}\)
\(\textsf{out}\)
\(C_1',~ \pi_1', \mathsf{vk}_1\)
\(C_2', ~\pi_2', \mathsf{vk}_2\)
\(C_0, \sigma_0\)
\(\mathsf{Tx}\)
\(C_0, \pi_0, \mathsf{vk}_0\)
balanced if:
$$E \coloneqq \sum C_i' - \sum C_i = (r_1 + r_2 - r_0 )G$$
Is a "public key" for which sender and receiver know the "secret key".
We call it excess.
\(\sigma_E\)
Sample \(r_0 \stackrel{\$}{\leftarrow}\mathbb{Z}_p\).
$$C_0 \coloneqq v_0H + r_0G $$
Mimblewimble
Coins:
Sample \(r_0 \stackrel{\$}{\leftarrow}\mathbb{Z}_p\).
$$C_0 \coloneqq v_0H + r_0G $$
Transactions:
\(\textsf{in}\)
\(\textsf{out}\)
\(C_1',~ \pi_1'\)
\(C_2', ~\pi_2'\)
\(C_0\)
\(\mathsf{Tx}\)
\(C_0, \pi_0\)
balanced if:
$$E \coloneqq \sum C_i' - \sum C_i = (r_1 + r_2 - r_0 )G$$
Is a "public key" for which the receiver knows the "secret key".
We call it excess.
\(\sigma_E\)
Knowledge of the opening suffices for security
Mimblewimble
Coinbase Transactions
A transactions with only output coins.
$$C_0 \coloneqq v_0 H + r_0 G \qquad (r_0 \stackrel{\$}{\leftarrow} \mathbb{Z}_p)$$
Signature under the excess:
$$E \coloneqq C_0 - v_0 H = r_0 G$$
the supply
Tx
\(\textsf{in}\)
\(\textsf{out}\)
\(C_0, \pi_0\)
$$\sigma$$
$$v_0$$
$$\textsf{Com}(v_0; 0)$$
Spend Money
two-party computed
"remainder" coin (receiver)
"change" coin (sender)
Alice puts input and change coins, Bob puts coins for the remainder.
Tx
\(\textsf{in}\)
\(\textsf{out}\)
\(C_0\)
$$\sigma$$
\(C_1, \pi_1\)
\(\hat C_2, \pi_2\)
$$0$$
(or, non-interactively)
Aggregate Transactions
[non-interactive CoinJoin]
\(\mathsf{Tx}_0\)
\(\textsf{in}\)
\(\textsf{out}\)
$$E_0 \coloneqq \sum \textsf{out}_0 - \sum \textsf{in}_0 $$
\(\textsf{in}\)
\(\textsf{out}\)
$$E_1$$
$$\sigma_1$$
$$E_1 \coloneqq \sum \textsf{out}_1 - \sum \textsf{in}_1 $$
\(\mathsf{Tx}\)
\(\textsf{in}\)
\(\textsf{out}\)
$$E_0, E_1$$
$$\sigma$$
$$=$$
$$+$$
\(\mathsf{Tx}_1\)
$$E_0$$
$$\sigma_0$$
$$E_0 + E_1 = \sum \textsf{out} - \sum \textsf{in} $$
Aggregate Transactions
[cut-through]
\(\mathsf{Tx}_0\)
\(\textsf{in}\)
\(\textsf{out}\)
$$E_0 \coloneqq \sum \textsf{out}_0 - \sum \textsf{in}_0 $$
\(\textsf{in}\)
\(\textsf{out}\)
$$E_1$$
$$\sigma_1$$
$$E_1 \coloneqq \sum \textsf{out}_1 - \sum \textsf{in}_1 $$
\(\mathsf{Tx}\)
\(\textsf{in}\)
\(\textsf{out}\)
$$E_0, E_1$$
$$\sigma$$
$$E_0 + E_1 = \sum \textsf{out} - \sum \textsf{in} $$
$$=$$
$$+$$
(verification keys for the respective signatures)
\(\mathsf{Tx}_1\)
$$E_0$$
$$\sigma_0$$
Ledger
The ledger is just the aggregation of all previous transactions.
\(\textsf{in}\)
\(\textsf{out}\)
total amount of money in the system
excess of all transactions aggregated
signature attesting validity of all transactions ever done
$$Λ = $$
$$S$$
$$E_0, E_1, \dots, E_{n-1}$$
$$\sigma$$
\(\vdots\)
Our Contributions
Abstracting Mimblewimble.
- simulation-extractable zero-knowledge arguments (rangeproofs)
- homomorphic commitments
- aggregate signatures
}
Compatible!
A verification key is a commitment to zero:
$$\textsf{Sig}.\textsf{KeyGen}() = \textsf{Com}.\textsf{C}(0)$$
\(\implies\) opening information is a signing key
\(\implies\) commitment space is the space of verification keys
Our Contributions
New joint security assumptions on (Com, Sig).
EUF-NZO
It is difficult to produce a signature that verifies and that opens to a non-zero value.
EUF-CRO
Given a challenge commitment \(C^*\),
it is difficult to produce a valid signature and an opening under \(-C^*\)
(even with a related-key oracle)
$$\begin{aligned}&\big(L, m, \sigma, (v, r)\big) \gets\mathcal{A} \\&v \neq 0 \textsf{ and }\textsf{Sig}.\textsf{V}(L, m, \sigma) \textbf{ and } \textsf{Com}.\textsf{C}(v, r) = \textstyle\sum L \end{aligned}$$
$$\begin{aligned}&\big(L, \sigma, (v, r)\big) \gets\mathcal{A}^{\text{Sign}}(C^*) \\&\textsf{Sig}.\textsf{V}(L, \sigma) \textbf{ and } \textstyle\sum L - \textsf{Com}.\textsf{C}(v, r) = - C^*\end{aligned}$$
Our Contribution
Security:
- inflation resistance
- theft resistance
-
confidentiality of amounts
Security model of an Aggregate Cash System.
Instantiations:
- Pedersen, Schnorr
- Pedersen, BLS
Inflation
Cannot spend more money than existing in the ledger.
Tx
\(\hat C, \pi\)
… and knows an opening \(\hat v, \hat r\) such that \(\hat v > S\).
𝒜
\(\textsf{in}\)
\(\textsf{out}\)
\(\Lambda\)
\(\textsf{in}\)
\(\textsf{out}\)
\(S\)
\(\sigma\)
\(\sigma\)
,
Inflation
Cannot spend more money than existing in the ledger.
Tx
\(\hat C, \pi\)
𝒜
\(\Lambda\)
\(\textsf{in}\)
\(\textsf{in}\)
\(\textsf{out}\)
\(\textsf{out}\)
\(S\)
\(\sigma\)
\(\sigma\)
,
,
\((\hat v, \hat r)\)
$$\mathsf{Tx.in}\subset \mathsf{\Lambda.out},\quad \hat v > S $$
- the adversary broke the proof system
- the adversary produced a commitment to a nonzero value with a valid signature
$$\implies$$
Theft Resistance
Cannot spend coins of honest users.
𝒜
\(\Lambda'\)
\(\textsf{in}\)
\(\textsf{out}\)
\(\sigma'\)
\(??\)
If an adversary manages to spend a honest coin,
then it is possible to find a valid opening for it.
\(\text{Mint, Send, Receive, Ledger}\)
Transaction Indistinguishability
Two transactions with the same structure* are indistinguishable.
Tx
\(\equiv\)
\(\textsf{in}\)
\(\textsf{out}\)
* same number of inputs, outputs and excesses.
Ind.
Tx'
\(\textsf{in}\)
\(\textsf{out}\)
Transaction Indistinguishability
Return \(\mathsf{tx}_b\) if:
-
same number of inputs/outputs
-
same excesses
-
balanced
𝒜
$$\mathcal{O}$$
… what about stronger notions of privacy?
$$\mathsf{tx}_b$$
\((\vec v_0, \vec v'_0, \vec v''_0), (\vec v_1, \vec v'_1, \vec v''_1)\)
pairs (input, change, reminder)
It is possible to reconstruct the constituent transactions of an aggregated transaction.
\(\mathsf{Tx}_0\)
\(\textsf{in}\)
\(\textsf{out}\)
\(\textsf{in}\)
\(\textsf{out}\)
$$E_1$$
$$\sigma_1$$
\(\mathsf{Tx}\)
\(\textsf{in}\)
\(\textsf{out}\)
$$E_0, E_1$$
$$\sigma$$
$$=$$
$$+$$
\(\mathsf{Tx}_1\)
$$E_0$$
$$\sigma_0$$
$$E_0 = C_0' - (C_0 + C_1)$$
$$C_0$$
$$C_1$$
$$C_0', \pi_0'$$
$$C_2$$
$$C_1', \pi_1'$$
$$E_1 = C_1' - C_2$$
$$C_0$$
$$C_1$$
$$C_0', \pi_0'$$
$$C_2$$
$$C_1', \pi_1'$$
Kernel Offsets
Kernel Offsets
\(\mathsf{Tx}_0\)
\(\textsf{in}\)
\(\textsf{out}\)
\(\textsf{in}\)
\(\textsf{out}\)
$$E_1$$
$$\sigma_1$$
$$+$$
$$E_0$$
$$\sigma_0$$
$$E_0 = C_0' - (C_0 + C_1)-\textsf{Com}.\textsf{C}(0; x_0)$$
$$C_0$$
$$C_1$$
$$C_0', \pi_0'$$
$$C_2$$
$$C_1', \pi_1'$$
$$E_1 = C_1' - C_2-\mathsf{Com}.\mathsf{C}(0; x_1)$$
$$x_0$$
\(\mathsf{Tx}\)
\(\textsf{in}\)
\(\textsf{out}\)
$$E_0, E_1$$
$$\sigma$$
$$=$$
$$C_0$$
$$C_1$$
$$C_0', \pi_0'$$
$$C_2$$
$$C_1', \pi_1'$$
$$(x_0\!+\!x_1)$$
$$x_1$$
\(\mathsf{Tx}_1\)
[T]o mitigate this, we include a kernel offset with every transaction, [i.e.] a blinding factor that needs to be added back to the kernel excess to verify the commitments sum to zero.
— Antioch Peverell, Mimblewimble wiki
\(0\)
\(0\)
\(0\)
- More privacy?
Food for thought
- More privacy?
- Aggregating two transactions costs \(1|\mathbb{G}|\)
Food for thought
\(\textsf{in}\)
\(\textsf{out}\)
$$E_0, E_1, \dots, E_{n-1}$$
$$\sigma$$
\(\vdots\)
$$Λ = $$