Kubernetes
and
Istio
Webinar


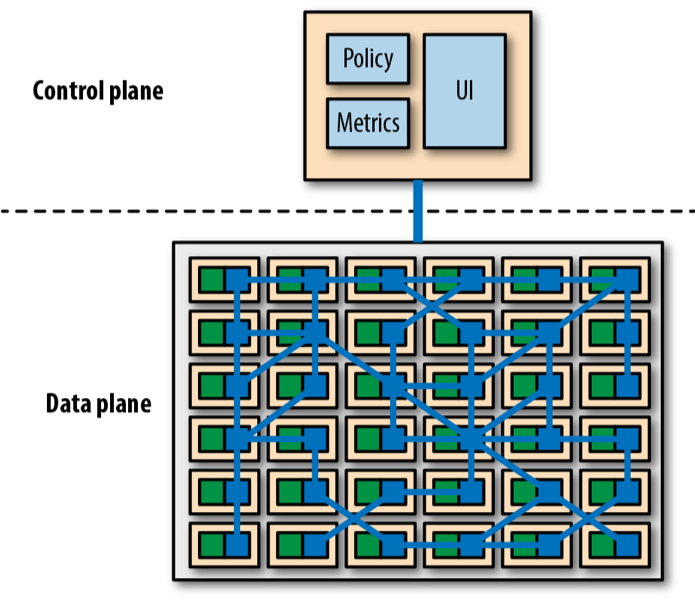
Service Mesh - service-to-service communication


Service Mesh's Control Plane
































Istio

- Greek word for "sail"
- Istio is an open platform-independent service mesh that provides traffic management, policy enforcement, and telemetry collection
- Layer 7 firewall + loadbalancer, ingress, blocking outgoing traffic, tracing, monitoring, logging
- Policies and Telemetry: Prometheus, StatsD, FluentD and many others...


Istio overview



Istio architecture
- Envoy - is a high-performance proxy to mediate all inbound and outbound traffic for all services in the service mesh.
- Pilot - provides service discovery for the Envoy sidecars, traffic management capabilities for intelligent routing.
- Mixer - enforces access control and usage policies across the service mesh, and collects telemetry data from the Envoy proxy and other services.
- Citadel - provides strong service-to-service and end-user authentication with built-in identity and credential/certificate management.
- Galley - is Istio's configuration validation, ingestion, processing and distribution component


Istio components
- DestinationRule - defines policies that apply to traffic intended for a service after routing has occurred.
- VirtualService - defines a set of traffic routing rules to apply when a host is addressed.
- ServiceEntry is commonly used to enable requests to services outside of an Istio service mesh.
- Gateway configures a load balancer for HTTP traffic, most commonly operating at the edge of the mesh to enable ingress traffic for an application.


Traffic Management with Istio



Istio security overview



Istio Security Architecture



Istio Multicluster
Multiple k8s clusters managed by single Istio instance








Istio multicluster service mesh - Gateway
Istio mesh spanning multiple Kubernetes clusters using Istio Gateway to reach remote pods


Istio multicluster service mesh - VPN
Istio mesh spanning multiple Kubernetes clusters with direct network access to remote pods over VPN


Demo

-
Amazon EKS Cluster
-
awscli, eksctl, helm, kubectl, siege or docker
-
2 Worker instances



-
Install Helm -
Install Istio -
Generate + Use SSL certificates -
Install Bookinfo demo application consist of multiple microservices -
Configure Istio Request Routing based on user identity -
Configure Istio Injecting an HTTP delay fault -
Configure Istio Injecting an HTTP abort fault -
Configure Istio - Weight-based routing (Canary Deployments)