Diva Android Security
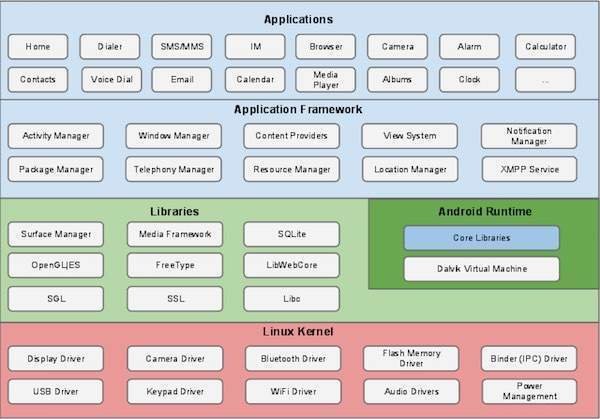
Brief Overview Android Architecture
What is diva?
DIVA (Damn insecure and vulnerable App) is an App intentionally designed to be insecure. We are releasing the Android version of Diva.The aim of the App is to teach developers/QA/security professionals, flaws that are generally present in the Apps due poor or insecure coding practices. If you are reading this, you want to either learn App pentesting or secure coding and I sincerely hope that DIVA solves your purpose. So, sit back and enjoy the ride.
List of vulnerabilities in diva
- Insecure Logging
- Hardcoding Issues - Part 1
- Insecure Data Storage - Part 1
- Insecure Data Storage - Part 2
- Insecure Data Storage - Part 3
- Insecure Data Storage - Part 4
- Input Validation Issues - Part 1
- Input Validation Issues - Part 2
- Access Control Issues - Part 1
- Access Control Issues - Part 2
- Access Control Issues - Part 3
- Hardcoding Issues - Part 2
- Input Validation Issues - Part 3
Lets Hack it
( Before uploading Slides will be added here with screen shots of attacking diva )
Insecure Logging
How To Secure
You should configure your application to remove Log class at final build time. To get this job done, Add the following code into the ProGuard config file.
-assumenosideeffects class android.util.Log{*;}
Hard Coding Issues
How To Secure
To avoid this vulnerability, keep reviewing the source code to be sure that there is no any credentials are stored in it. 😅
Insecure Data Storage How To Secure
Android Specific Best Practices:
1. For local storage the enterprise android device administration API can be used to force encryption to local file-stores using “setStorageEncryption”
2. For SD Card Storage some security can be achieved via the ‘javax.crypto’ library. You have a few options, but an easy one is simply to encrypt any plain text data with a master password and AES 128.
3. Ensure any shared preferences properties are NOT MODEWORLDREADABLE unless explicitly required for information sharing between apps.
4. Avoid exclusively relying upon hardcoded encryption or decryption keys when storing sensitive information assets.
5. Consider providing an additional layer of encryption beyond any default encryption mechanisms provided by the operating system.
Insecure Data Storage How To Secure
Android Specific Best Practices:
1. For local storage the enterprise android device administration API can be used to force encryption to local file-stores using “setStorageEncryption”
2. For SD Card Storage some security can be achieved via the ‘javax.crypto’ library. You have a few options, but an easy one is simply to encrypt any plain text data with a master password and AES 128.
3. Ensure any shared preferences properties are NOT MODEWORLDREADABLE unless explicitly required for information sharing between apps.
4. Avoid exclusively relying upon hardcoded encryption or decryption keys when storing sensitive information assets.
5. Consider providing an additional layer of encryption beyond any default encryption mechanisms provided by the operating system.
Input Validation Check
Lets look at this page
https://owasp.org/www-project-cheat-sheets/cheatsheets/Input_Validation_Cheat_Sheet.html
Access Control Issues
Lets look at this page
https://developer.android.com/training/articles/security-tip
References
- https://medium.com/mobile-penetration-testing/01-insecure-logging-a41c41a8e648
- https://owasp.org/www-project-cheat-sheets/cheatsheets/Input_Validation_Cheat_Sheet.html
- https://www.beyondtrust.com/blog/entry/hardcoded-and-embedded-credentials-are-an-it-security-hazard-heres-what-you-need-to-know
- https://developer.android.com/training/articles/security-tips