Blockchain a Digitálne meny
Workshop
David Stancel
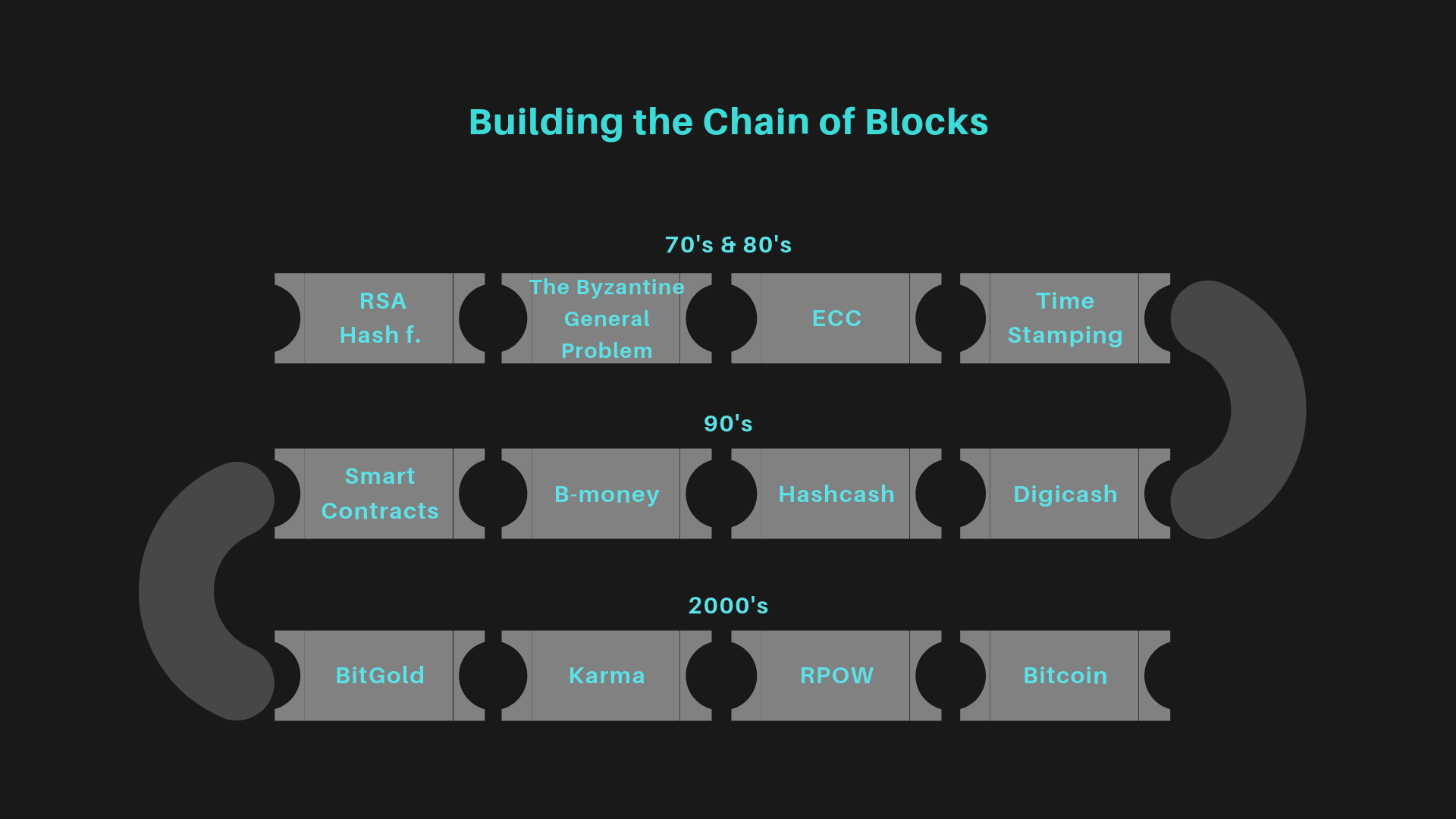
- Vznik elektronických mien Bitcoinu a Blockchainu
- Princípy fungovania blockchain technológií
- Bezpečnostné aspekty a riziká
- Blockchain a jeho využitie
- Trendy, projekty, vízie a výzvy
Obsah
-
Founder @ Blockchain Slovakia
-
exCTO @ Fumbi, exIT Auditor @PwC
-
Advisor @ Vacuumlabs, Aaro Capital
-
Lecturer @ STU FIIT, EUBA FHI
- Author of Coinstory: http://coinstory.tech
About me

DigiCash
... má svoje korene v rôznych myšlienkových smeroch:
teória hier, kryptografia, hackerská kultúra, open source hnutie, a libertarianizmus ..
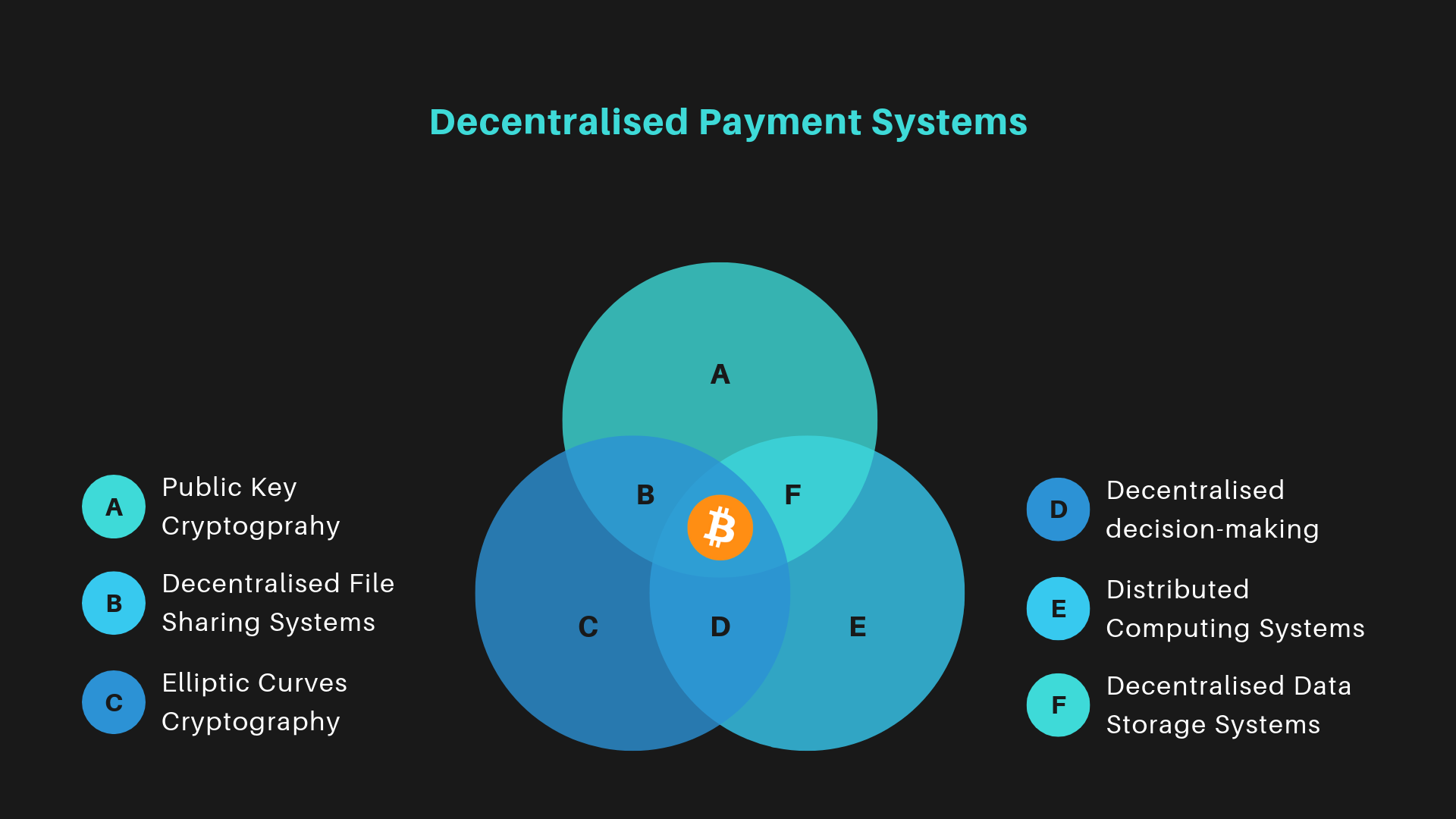
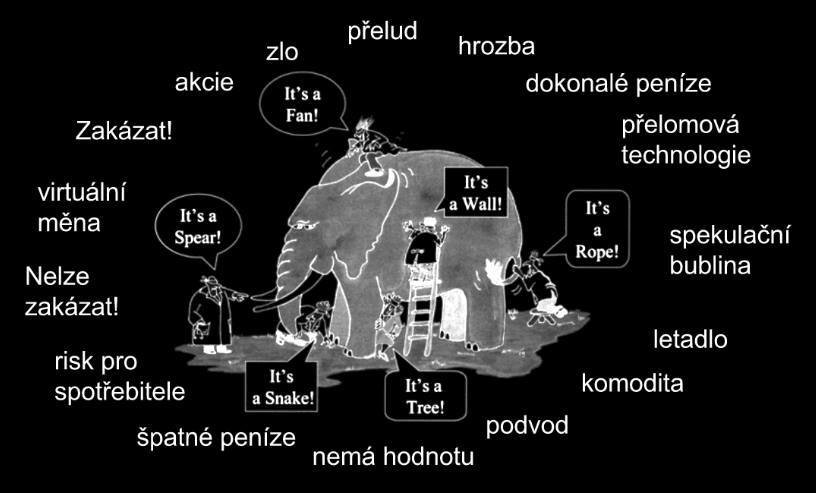
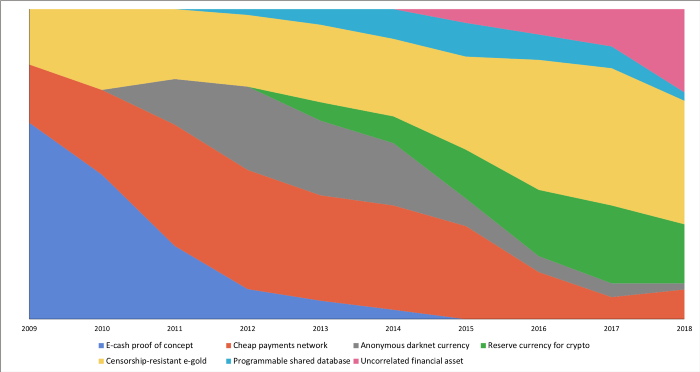
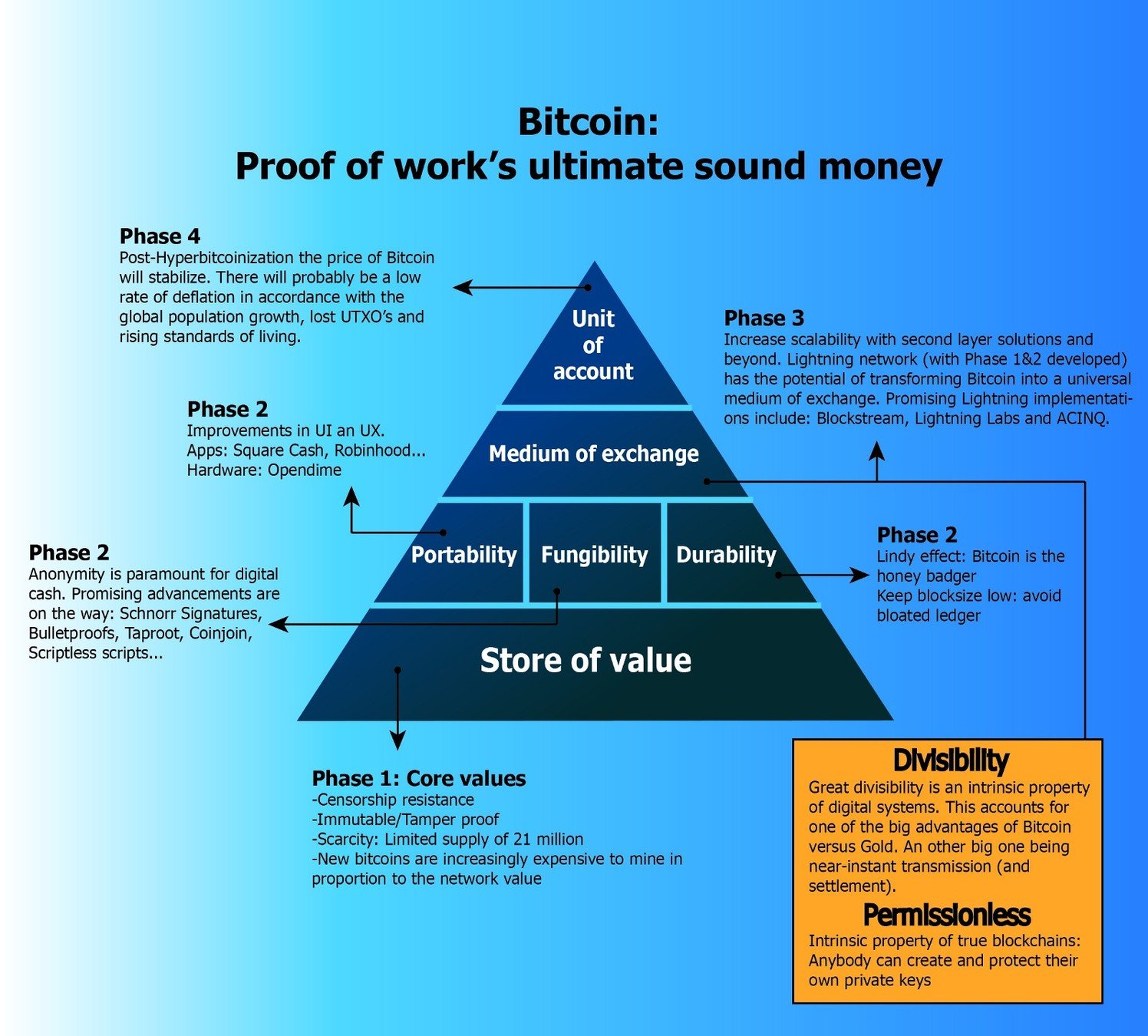
Bitcoin



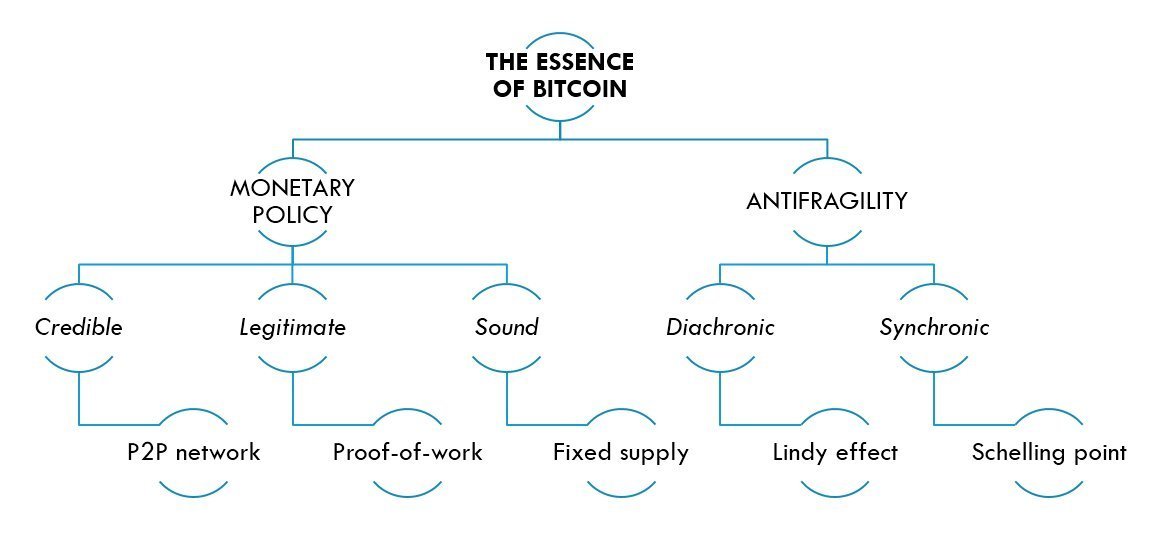
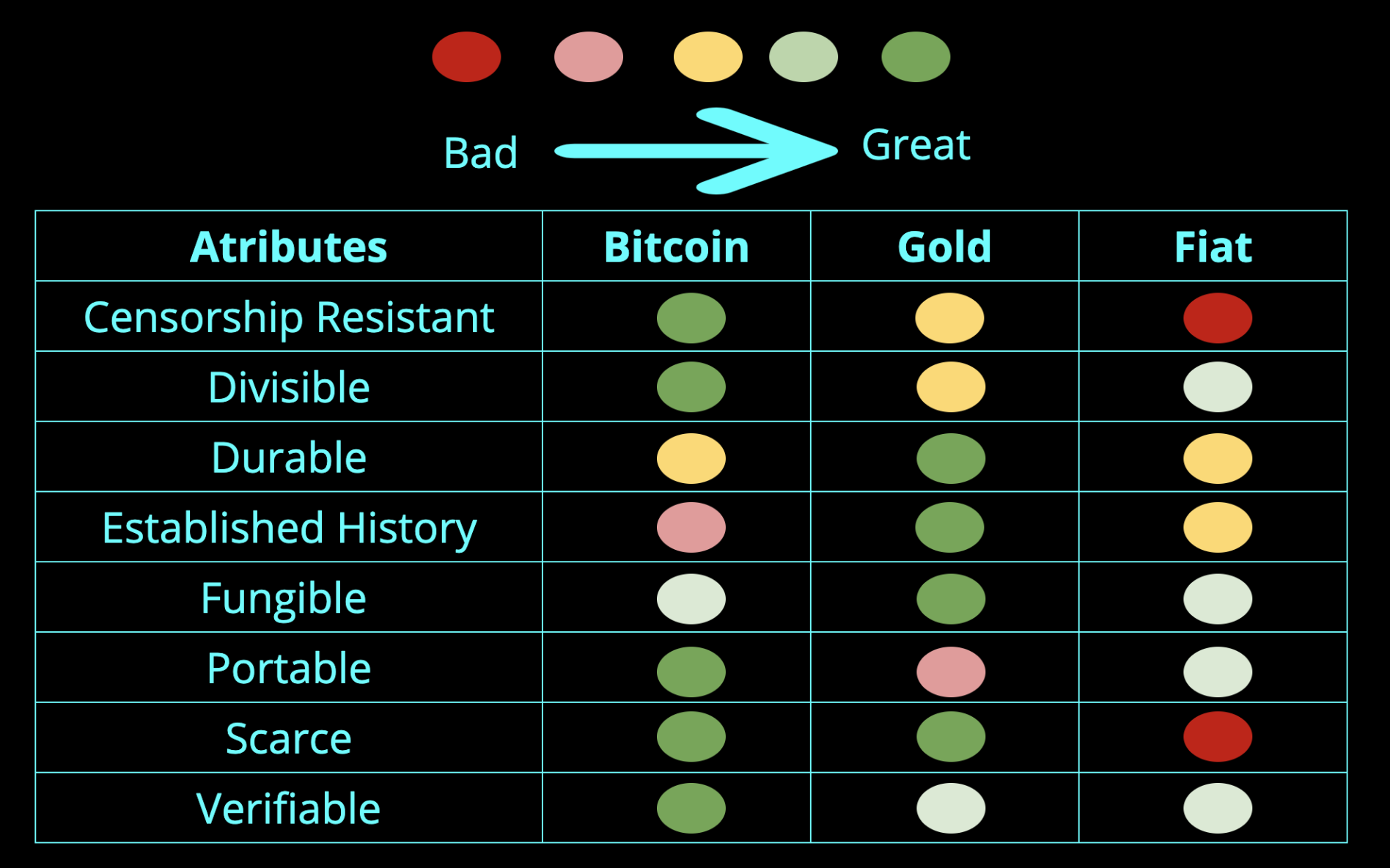
Atribúty:
- Vzácnosť - 21 M mincí
- Delitelnosť - 100 000 000 "halierov" --> satoshi
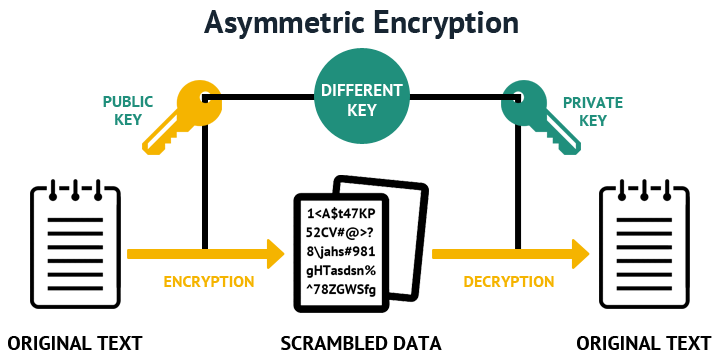
- Overitelnosť - verejná databáza, postavená na kryptografii, open source
- Prenosnosť - stačí privátny kľúč
- Zameniteľnosť (Fungibility)?
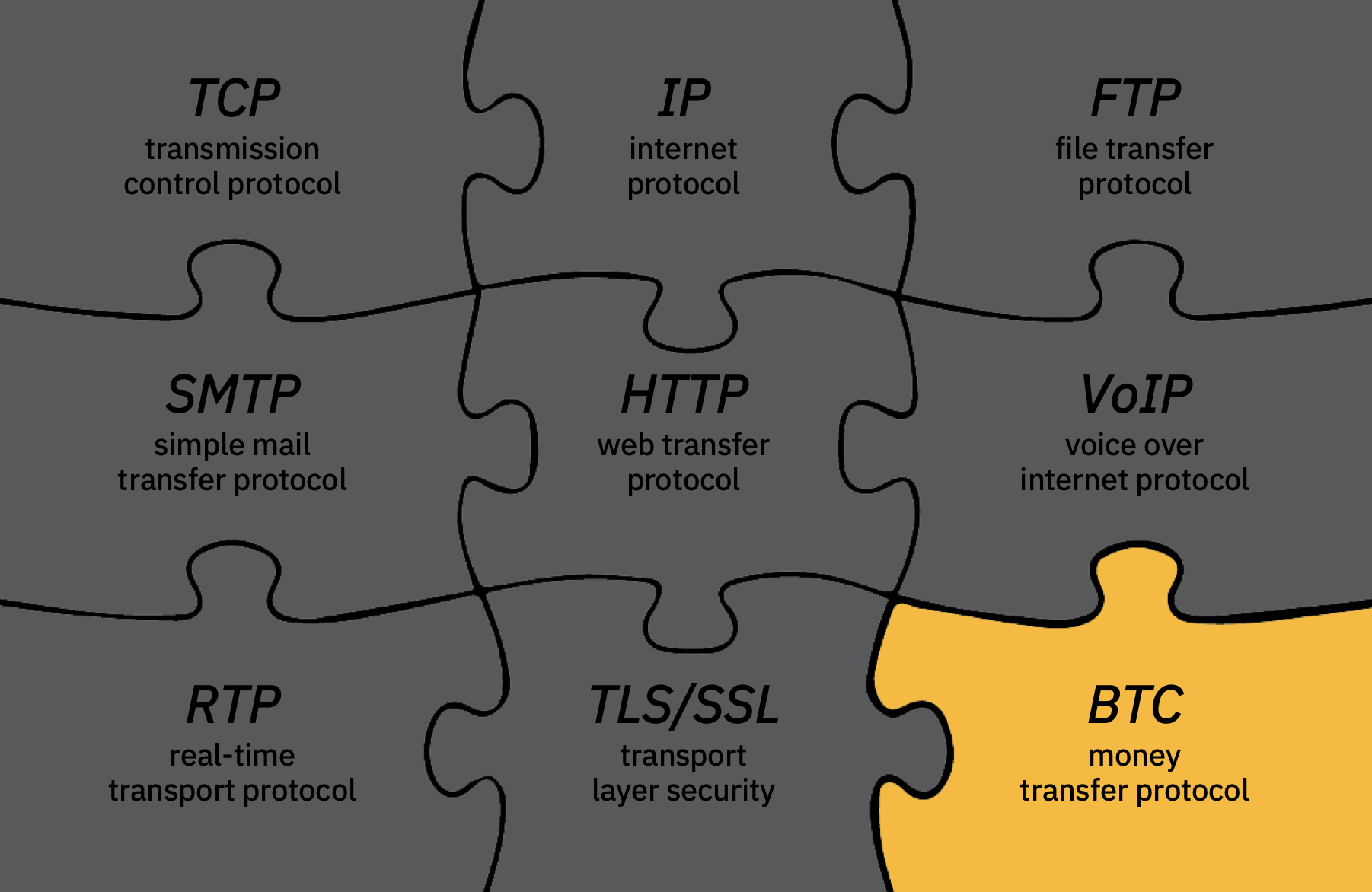
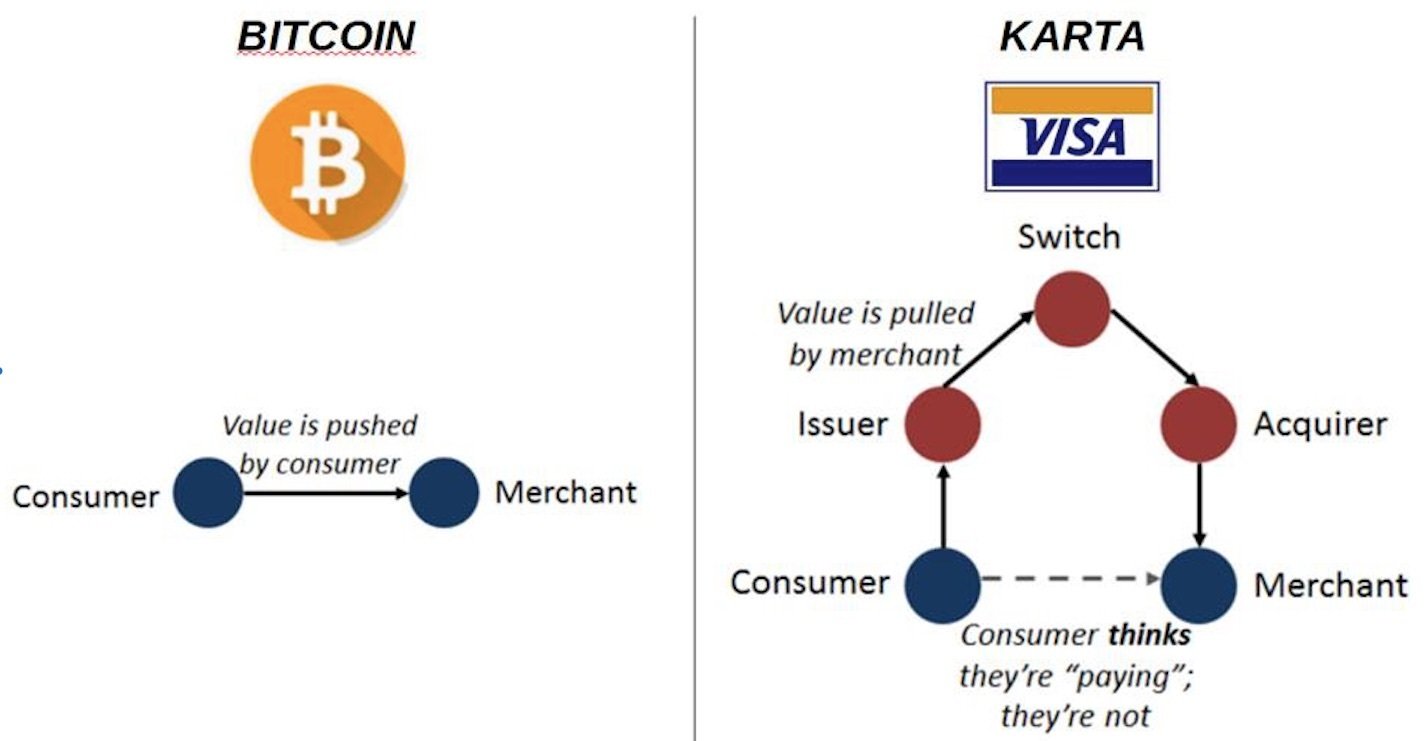
Prostredník

Otázky?
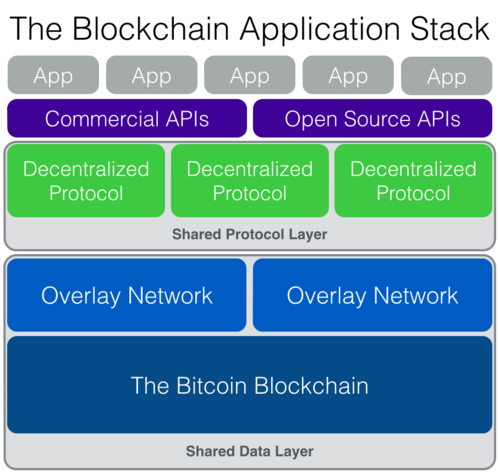
Princípy fungovania Blockchain technológií
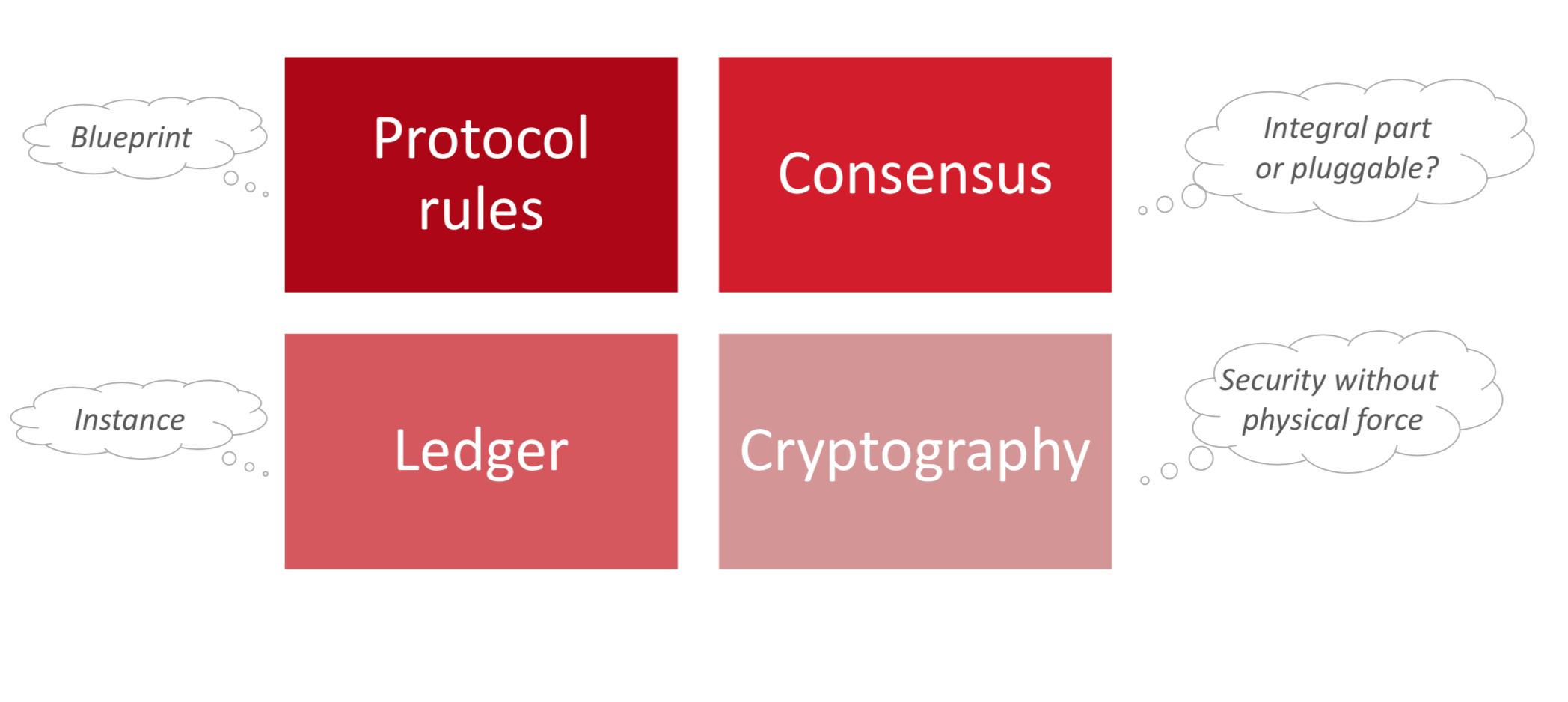
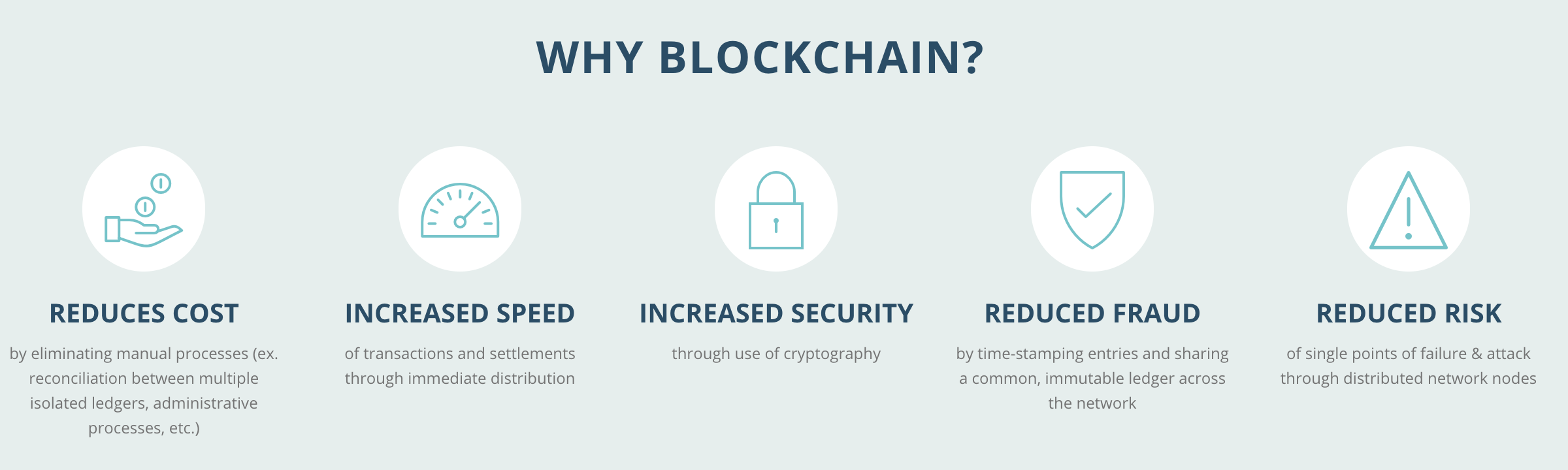
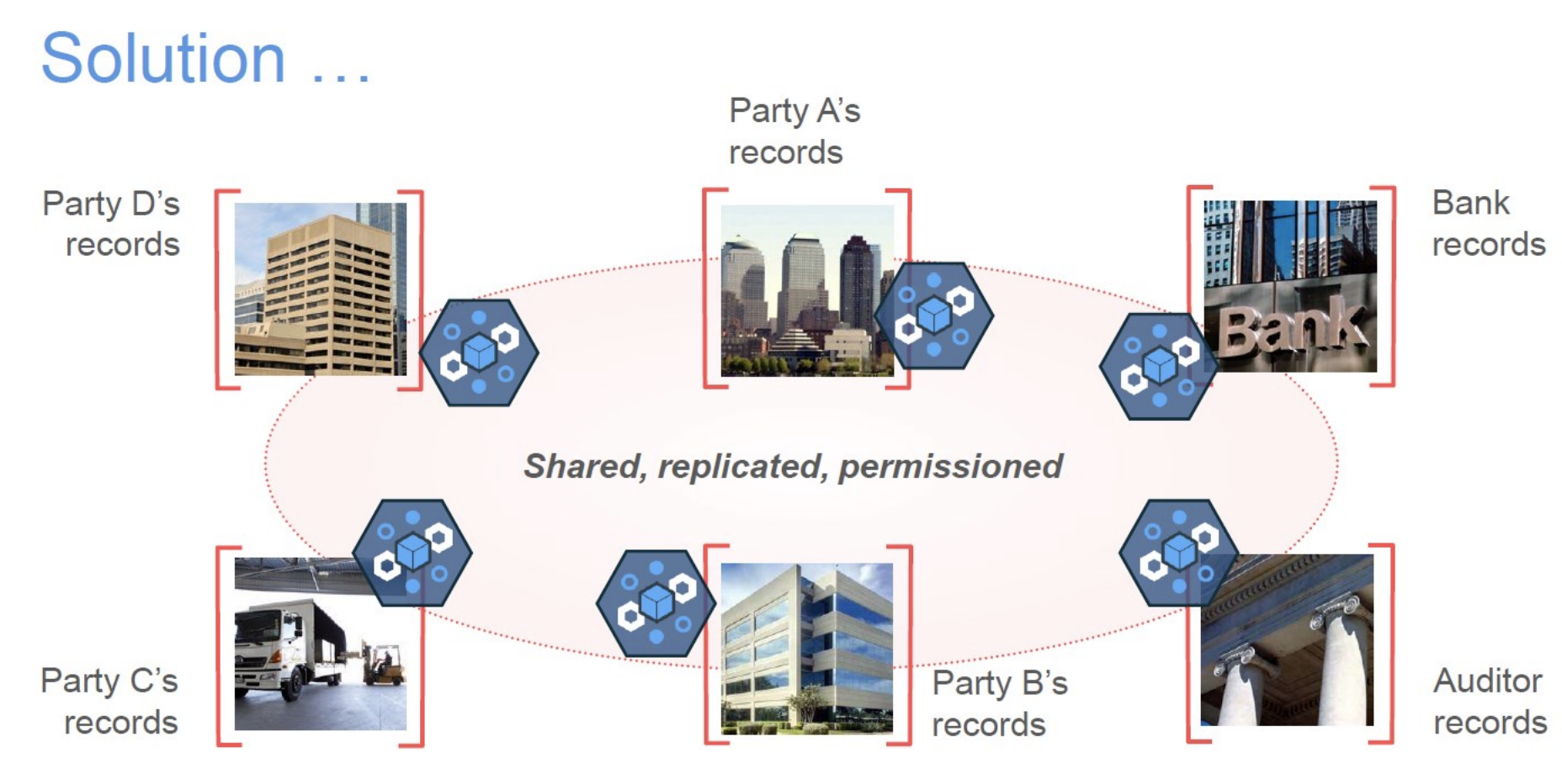
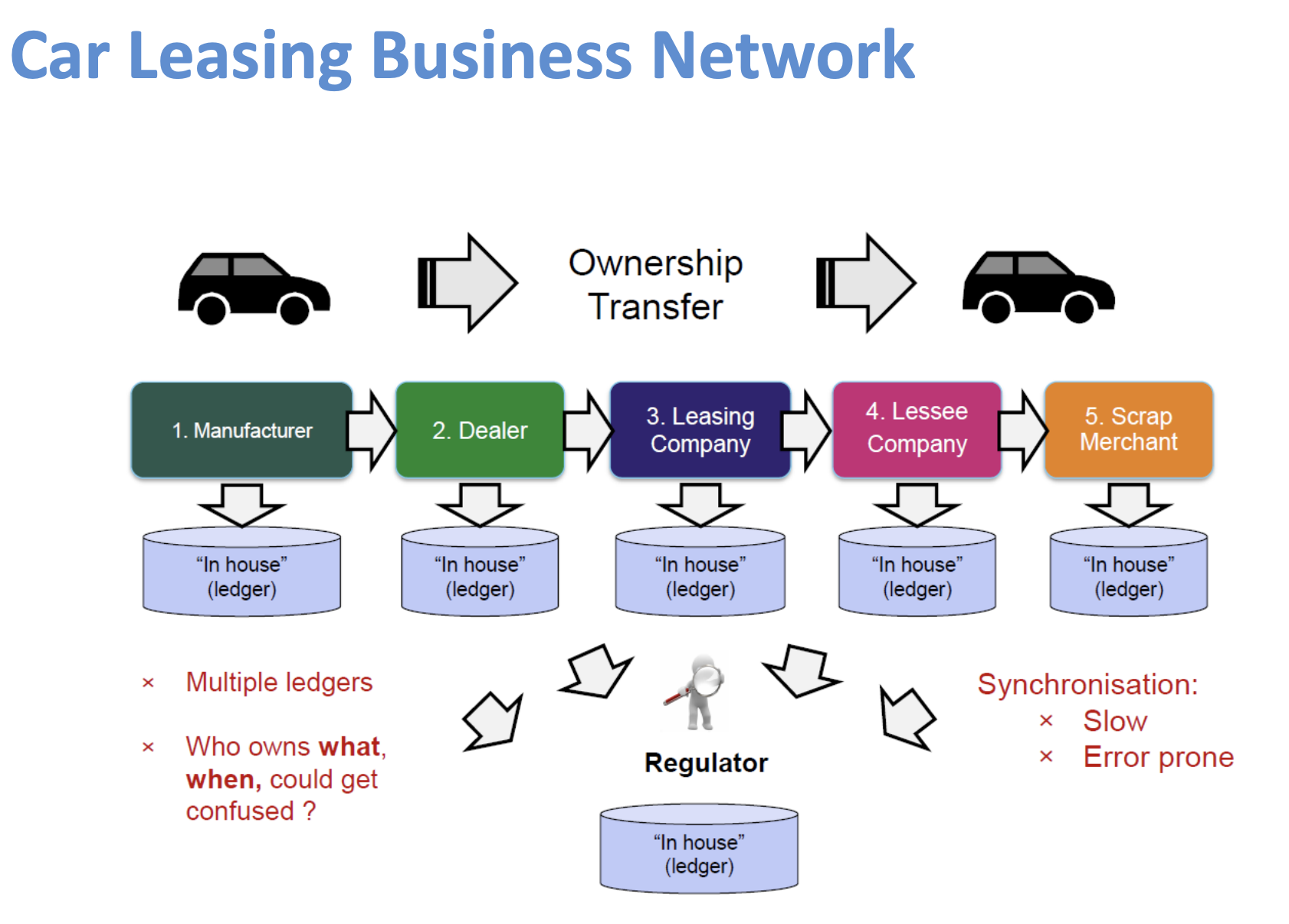
What is Blockchain?
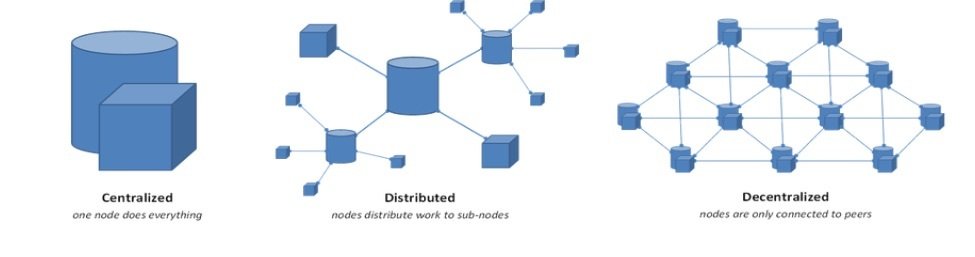
A tamper-proof, shared digital append-only ledger that records transactions grouped into blocks in a decentralized peer-to-peer network. The permanent recording of transactions in the Blockchain stores permanently the history of asset exchanges that take place between the peers.
Updating the ledger (usually) requires solving Byzantine Agreements (hash) with economically incentivized participation, secured by cryptography

Blockchain I.
Blockchain II.
1. Nová tranzakcia je odoslaná do siete
2. Každý uzol v sieti zbiera tranzakcie do bloku
3. Pri každom kole /bloku/ náhodne vybraný uzol získa právo určiť "pravdu"
4. Ďalšie uzle v sieti akceptujú blok iba za definovaných podmienok (ak má validné podpisy a tranzakcie)
5. Akceptáciu bloku vyjadrujú zahrnutím jeho hashu do svojich ďalších blokov
Blockchain III.

Blockchain IV.

Blockchain IV.

Blockchain V.

Blockchain VI.
Otázky?
Bezpečnostné aspekty a riziká

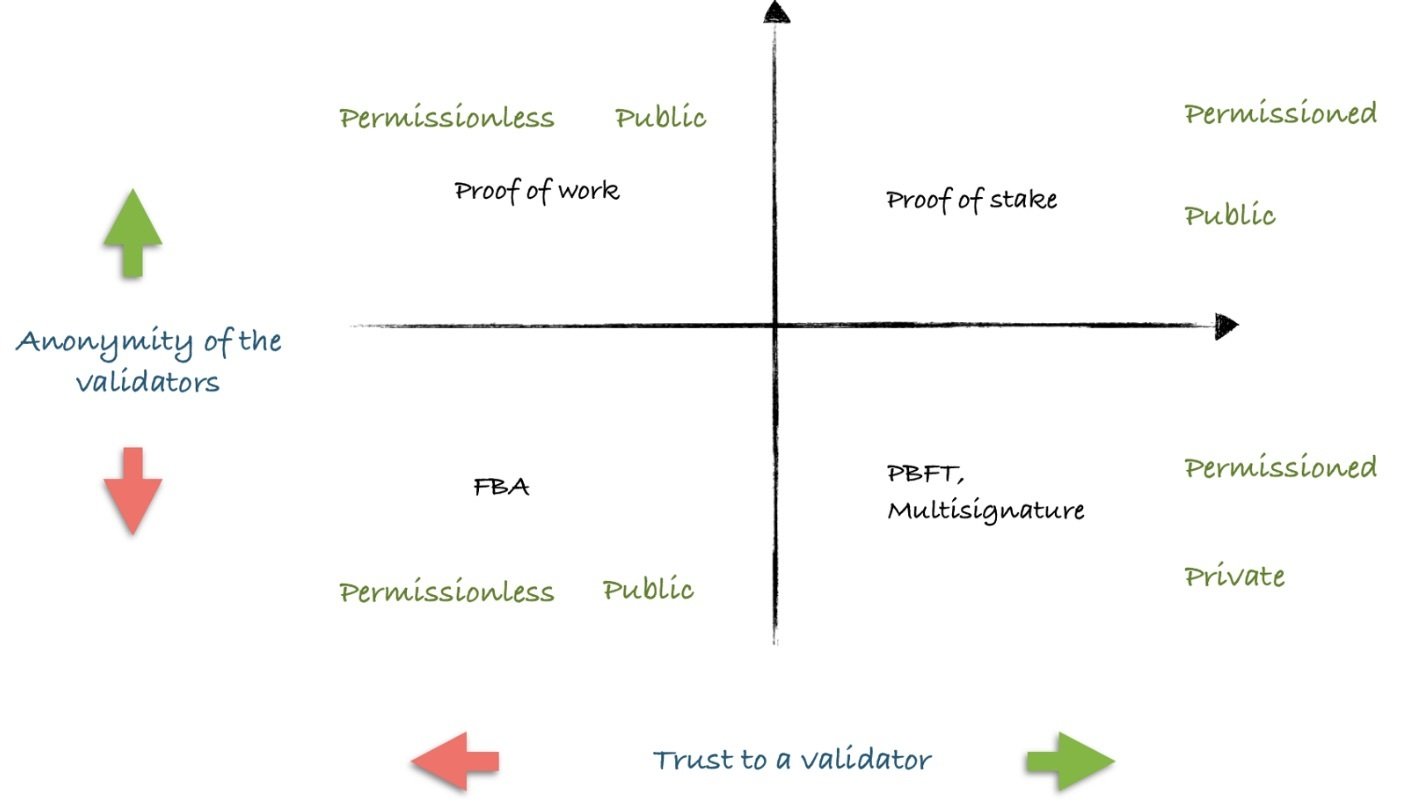
1. Consensus-related attack vectors
2. Anonymity & Privacy
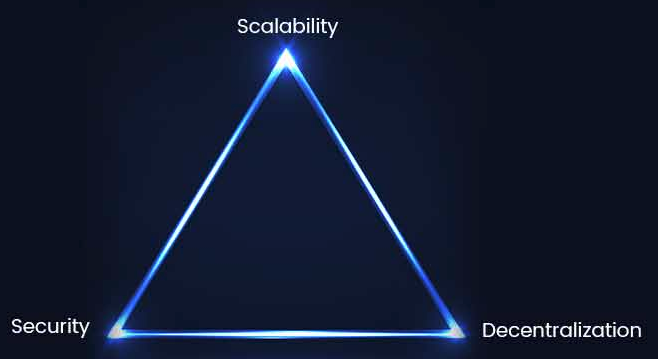
3. Scalability
4. Key management
5. Smart Contracts
Short range attack – attacker waits until merchant accepts payment as confirmed, than double- spends it by bribing validators to reorganize the chain
Long range attack – attacker with enough power can rebuild the chain as he choses, with the ability to build a blockchain however he desires
Coin accumulation – protocols which rely on the age of coins, where attacker could try to accumulate enough old coins to be able to reach a majority in voting
Denial of service – flooding nodes so that they can no longer relay transactions
Sybil attack – flooding the network with bad nodes that isolate good ones
Selfish mining – secretly building on a chain and publish it selectively in order to waste competitors resources
Consensus Mechanisms - Attack Vectors
There are two major ways of controlling the network:
1. Controlling the information flow between peers
2. Controlling the computational power of the network – remember that decisions are based on consensus/majority.
Attack Vectors
An adversary that controls more than half of the network's computing power can effectively control the entire network.
While controlling the network, the attacker can:
- Reverse transactions that s/he sends, thus double- spending own funds.
- Prevent other miners from mining valid blocks.
- Prevent valid transactions from gaining confirmations.
However, the attacker cannot:
- Reverse other people's transactions or spend outputs belonging to others. Create new coins.
- Prevent transactions from being sent across the network.
51% Attack
A denial of service (DoS) attack is an attempt to make an online service unavailable by overwhelming it with traffic.
---> overloading a network/computer with requests above the capacity that the network/computer can handle.
In Blockchain, this can be achieved by sending lots of junk data to a node. The nodes under attack will not be able to process normal transactions.
Denial of Service
- The maximum block size (currently 1Mb)
- The maximum number of signature checks that a transaction or block may request
- The maximum script size (currently 10Kb)
- The maximum size of values pushed while executing a script (currently 520 bytes)
- The maximum number of "expensive" operations in a script (up to 201 operations – anything but push operations).
- The maximum number of keys in multi-sig transactions (currently 20 keys) The maximum number of stack elements stored (currently 1,000 elements)
Protocol-based anti-DoS measures
a (bitcoin) node/peer:
- does not store more than 10,000 orphan transactions;
- does not forward orphan transactions/blocks;
- does not forward double-spend transactions;
- does not forward the same block or transaction to the same peer;
- does not forward or process non-standard transactions;
- bans IP addresses that misbehave;
- keeps a DoS score for each peer;
- penalizes peers that send duplicate/expired/invalid signature messages;
- disconnects from peers that send messages that fail to comply with the rules;
- stores only UTXO (unspent transaction output set) in memory
- checks all inputs are unspent before fetching a transaction from disk to memory – thus preventing a type of DoS, known as continuous hard disk activity DoS
Node-based anti-DoS measures
--> a malicious user gains control over a node's access to information in the peer-to-peer network.
Three prerequisites:
- The adversary should possess a large number of IP addresses and machines (or botnets)
- The victim should have a public IP address (for example not using TOR).
- The adversary is able to make the victim restart its Bitcoin client, for example through a DDoS attack (or if the victim restarts the client due to power/network failure or software update).
Eclipcse Attack
If the above criteria are met then:
- The adversary can monopolize all of the victim's outgoing and incoming connections, effectively isolating the victim from the rest of the network.
- Thus, the adversary can control the victim's view of the blockchain. Further to defrauding the victim, the adversary can use an eclipse attack to:
- Split the mining power in the network.
- Perform an 51% attack with less than 50% mining power.
- Perform selfish mining more easily, by splitting the mining power of honest nodes.
- Double-spend transactions.
Eclipcse Attack II.
The Bitcoin network spans the globe --> nodes are in different time zones.
Time is extremely important --> determines the validity of new blocks.
When establishing new connections, the protocol forces nodes to exchange their system time.
Each node maintains a counter, which represents the median network time of its peers. The counter reverts to system time, if the median differs from it by more than 70 minutes.
By announcing inaccurate timestamps when connecting to a node, an attacker can alter a node's network time counter and deceive it into accepting an alternate blockchain.
--> increase the chances of a successful double-spend.
Time Jacking
- process of sending thousands of nano-value transactions, in order to fill the blocks to the maximum size.
This will create delays to other legitimate transactions, thus delaying the whole network and increasing confirmation time for all transactions.
A flood attack is performed very easily, with the attacker just sending thousands of transactions to himself.
However, it is expensive to sustain for a long time, due to transaction fees.
Flood Attack
- can be used by large miners to increase their returns by not playing fair.
-
The selfish miner starts building a chain of blocks, but does not publish and distribute it to the rest of the network.
-
When the rest of the network is about to catch up with the selfish miner, the miner a releases a portion of the chain to the public.
- Because the chain of the selfish miner will be longer and more difficult, the rest of the network will discard the blocks of other miners and will adopt the chain of the selfish miner.
Selfish Mining
The computing power of honest miners is wasted.
--> selfish miners increase the impact of their own mining power on the network and enjoy additional power and profits.
Selfish mining increases transaction confirmation times, because transactions confirmed by the selfish miner in private, are not broadcast to the public immediately.
Selfish mining also increases the threat of double spending, as both honest and selfish miners can add mutually exclusive transactions to the private and public chains.
May be possible with 1/3 of network (33% attack).
Selfish Mining II.
Anonymity
-
All transactions are public, traceable and permanently stored in the blockchain.
-
To protect your privacy, you must use a new address for every new transaction.
-
Protecting your IP is also a good idea.
- Beware of mixing services: further to potential legality issues, they rely on trusting a third party and are, generally, not effective for large transactions.
Anonymity II.
Zerocoin operates, roughly, as follows:
-
A user withdraws bitcoin from his wallet and turns them into Zerocoins.
-
Zerocoins from multiple users are then "mixed up”.
- The user can then redeem zerocoins and deposit bitcoins to a new wallet address. Nobody can then link the new bitcoins to the old ones.
Anonymity III.
-
Zcash is a new blockchain that also aims at true cryptographic anonymity.
-
The principle is similar to Zerocoin, but the cryptography used is the current state-of- the-art, an evolution of zero-knowledge proof constructions, called zk-SNARKs.
-
It offers both so-called transparent transactions (t-addresses) like Bitcoin, and true anonymous transactions (z-addresses).
-
Transactions using z-addresses are hiding the source, destination and amount involved in the transaction, but they are still verifiable.
Anonymity IV.
- Cryptonote is based on ring signatures, which allow users to sign messages on behalf of a group
- A ring signature only proves the message was created by someone in the group, but all the possible signers are indistinguishable from each other.
- So, the verifier may only identify that a message of the group was the signer, thus providing plausible deniability.
- Cryptonote receivers have multiple one-time addresses, which are derived from a single public key. Funds sent to these one-time addresses cannot be linked to the receiver, who is using the public key.
- Non-repeating one-time addresses and mixed keys in ring signatures make the whole blockchain resistant to analysis.
Scalability
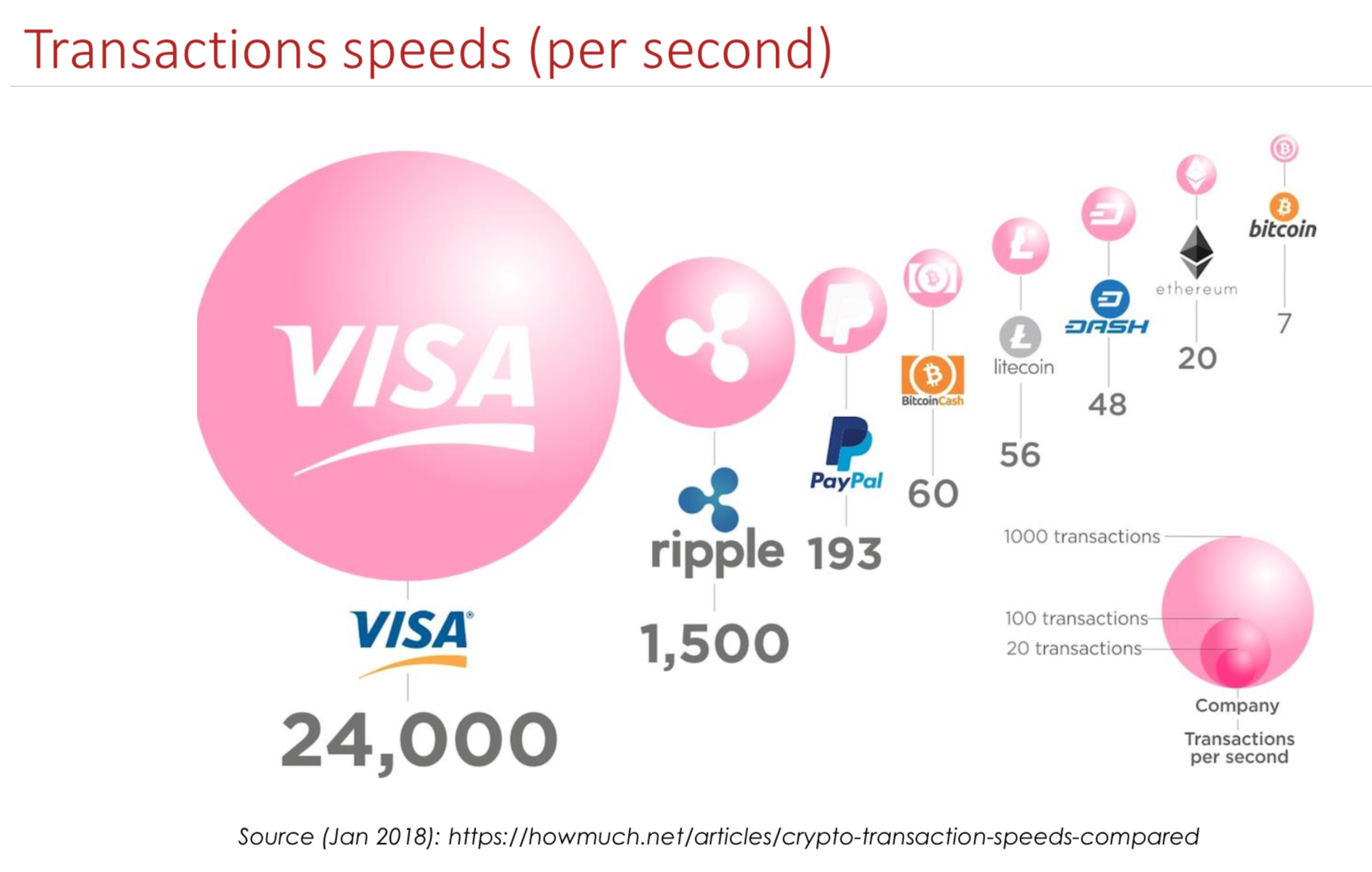
Scalability II.
Processing Power - the more processing power your computer has, the more transactions it can process.
- mostly for verifying transactions using:
- hashing (sha256 and ripemd160) and
-
signature verifications (ECDSA)
In theory, Bitcoin is able to verify approximately 4,000 transactions per second on an average CPU.In reality we cannot hope to scale beyond 200 transactions per second
Scalability III.
Storage - Maintaining a full bitcoin node means storing every single transaction ever recorded on the blockchain.
As of December 2019, around 280Gb space and an additional 5Gb per month.
If the network grows to the size of competing networks, storage requirements will skyrocket:
For 200 transactions per second (tps) – a reasonable target, given PayPal's current rate of 100 tps –nodes would require an additional storage space of 3Tb per year.
Scalability IV.
Bandwidth - Assuming that a bandwidth of 10Mbits/s is available, the rate with which nodes can receive transactions is limited to approximately 2,000 transactions per second.
+ each node is informed about every transaction multiple times and that other non-transaction messages are broadcasted over the network
If bandwidth is not enough, peers won’t be able to receive and validate transactions in time, making them unable to synchronize with the rest of the network.
Interoperability
Key management





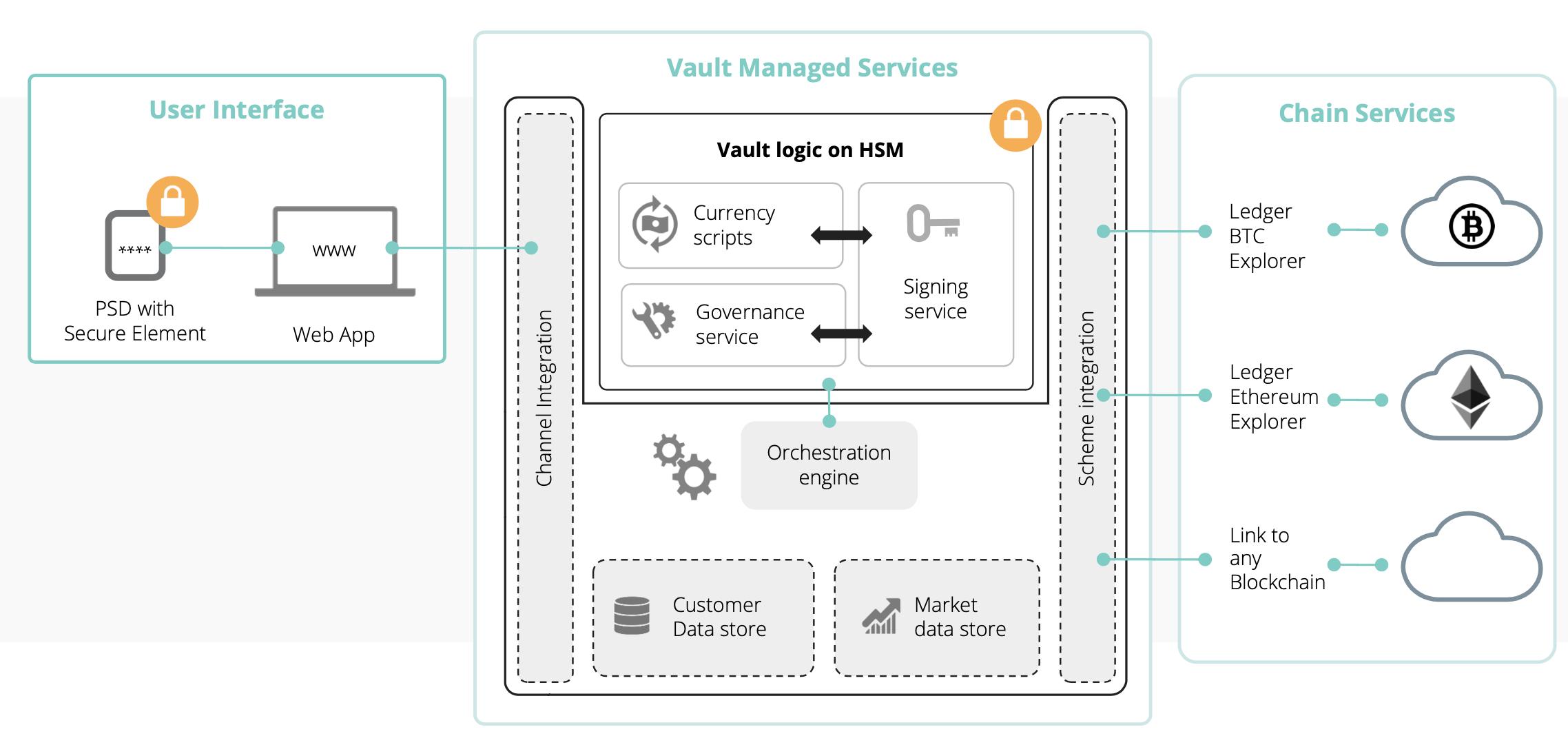
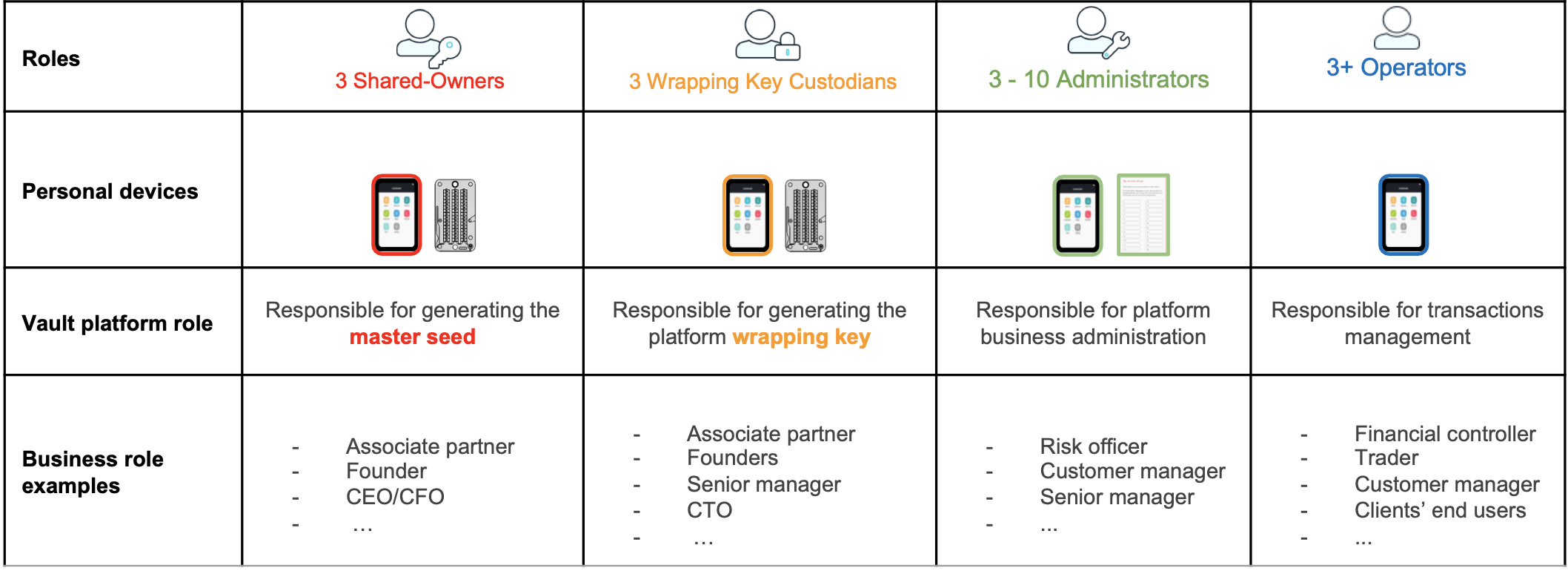
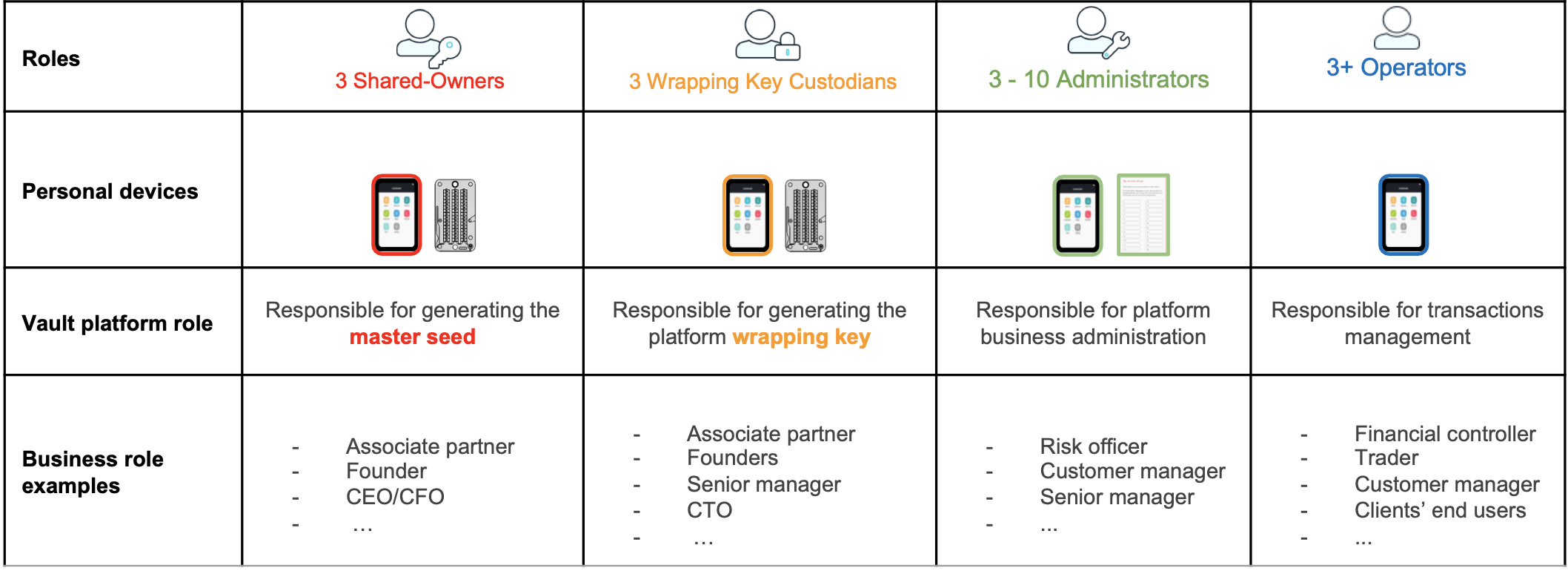
Institutional - Ledger Vault
Institutional - Ledger Vault II
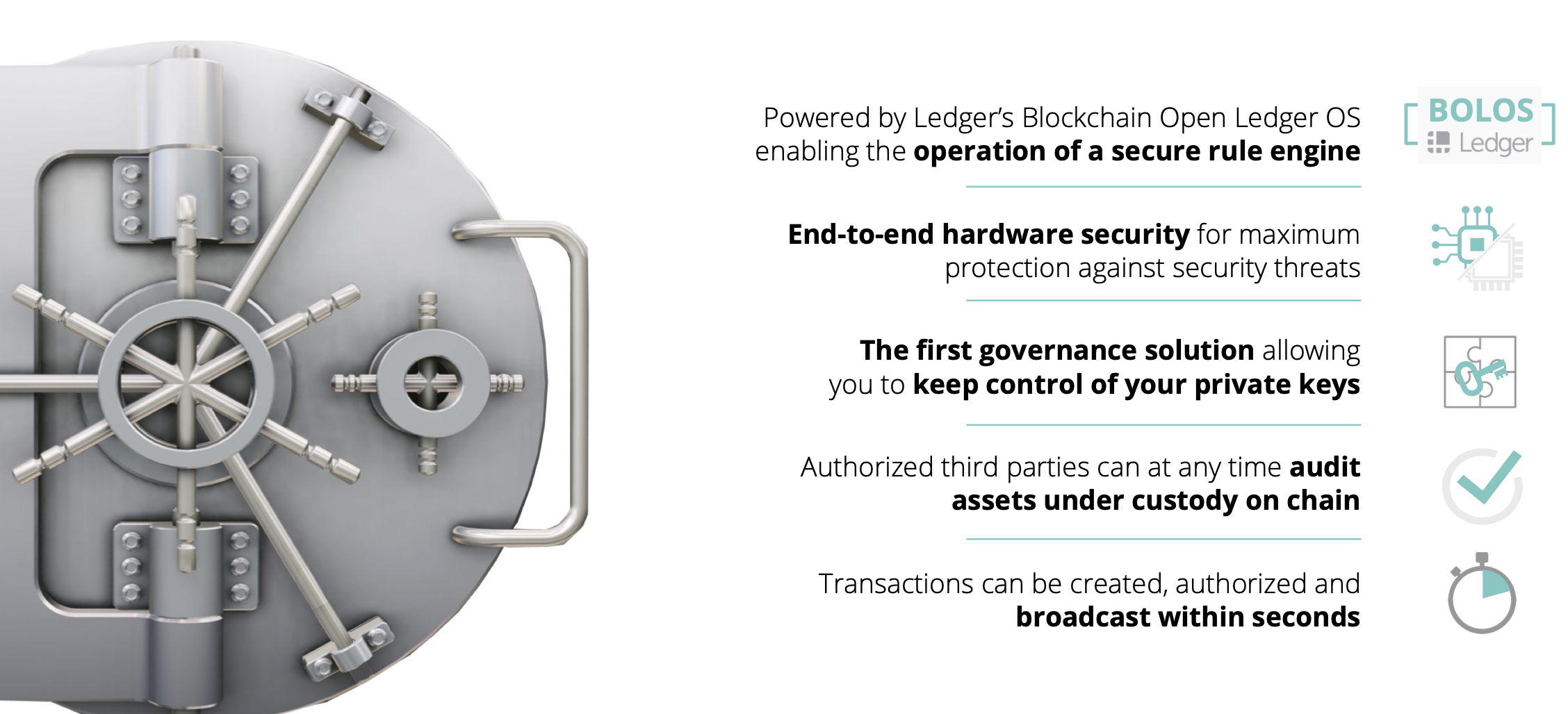
Institutional - Ledger Vault III
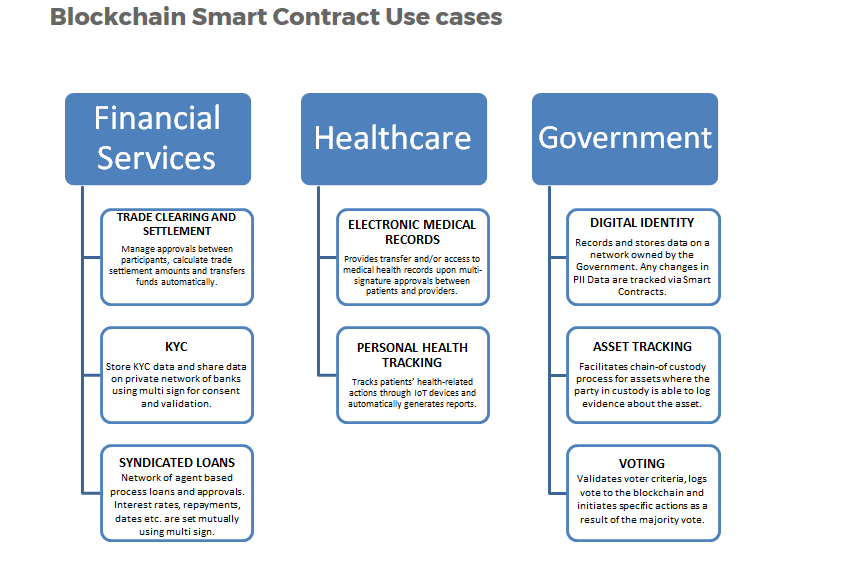
Smart Contracts
- Cutting edge, untested
- 10 x more buggy code
- Different logic than SW on centralized machines
- Potentially unchangeable
- Different platforms, limited interoperability
- Ethereum seems to be so far the winner
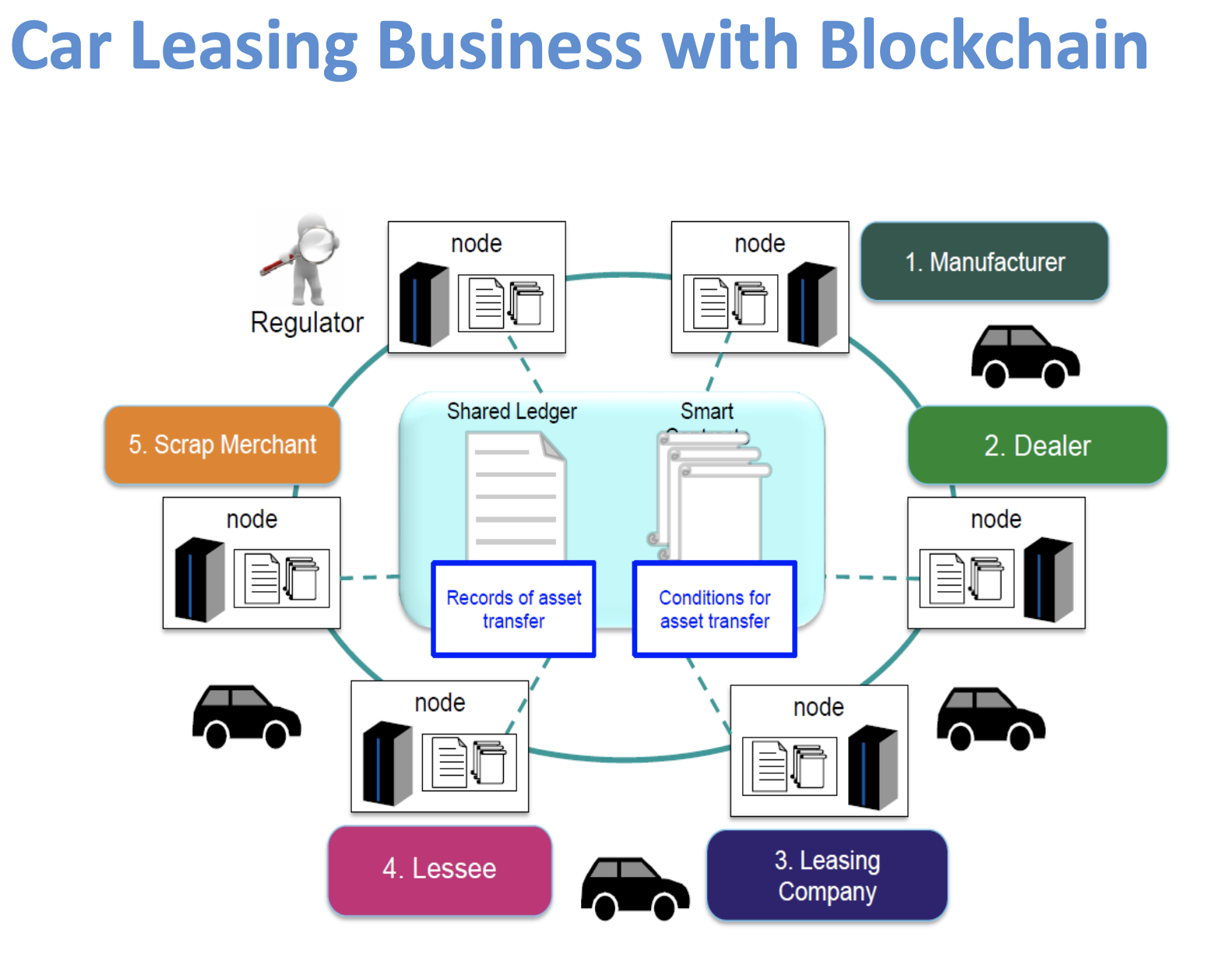
Blockchain a jeho využitie

Blockchain Heuristics

In fact, of the 231 PoCs Gartner reported on, only 14 have moved into a limited scale live-in production environment, reflecting the immaturity of the market we’re seeing today.
The same report estimates only 10% of these projects will make it to a fully-scaled business model by 2020. Given this predicament, it’s no surprise seeing enterprises employing stricter vetting processes and restricting spending on DLT projects overall.
https://www.gartner.com/doc/3869368/blockchain-trials-industries-market-transition


Insurance
https://etherisc.com/
Insurance II.
EY's report on blockchain in Insurance:
https://www.ey.com/Publication/vwLUAssets/EY-blockhain-in-insurance/$FILE/EY-blockhain-in-insurance.pdf
IBM Insurance Blockchain:
https://www.youtube.com/watch?time_continue=58&v=Mhpe0d-nE7k

https://www2.deloitte.com/content/dam/Deloitte/global/Documents/grid/trade-finance-placemat.pdf
Trade Finance
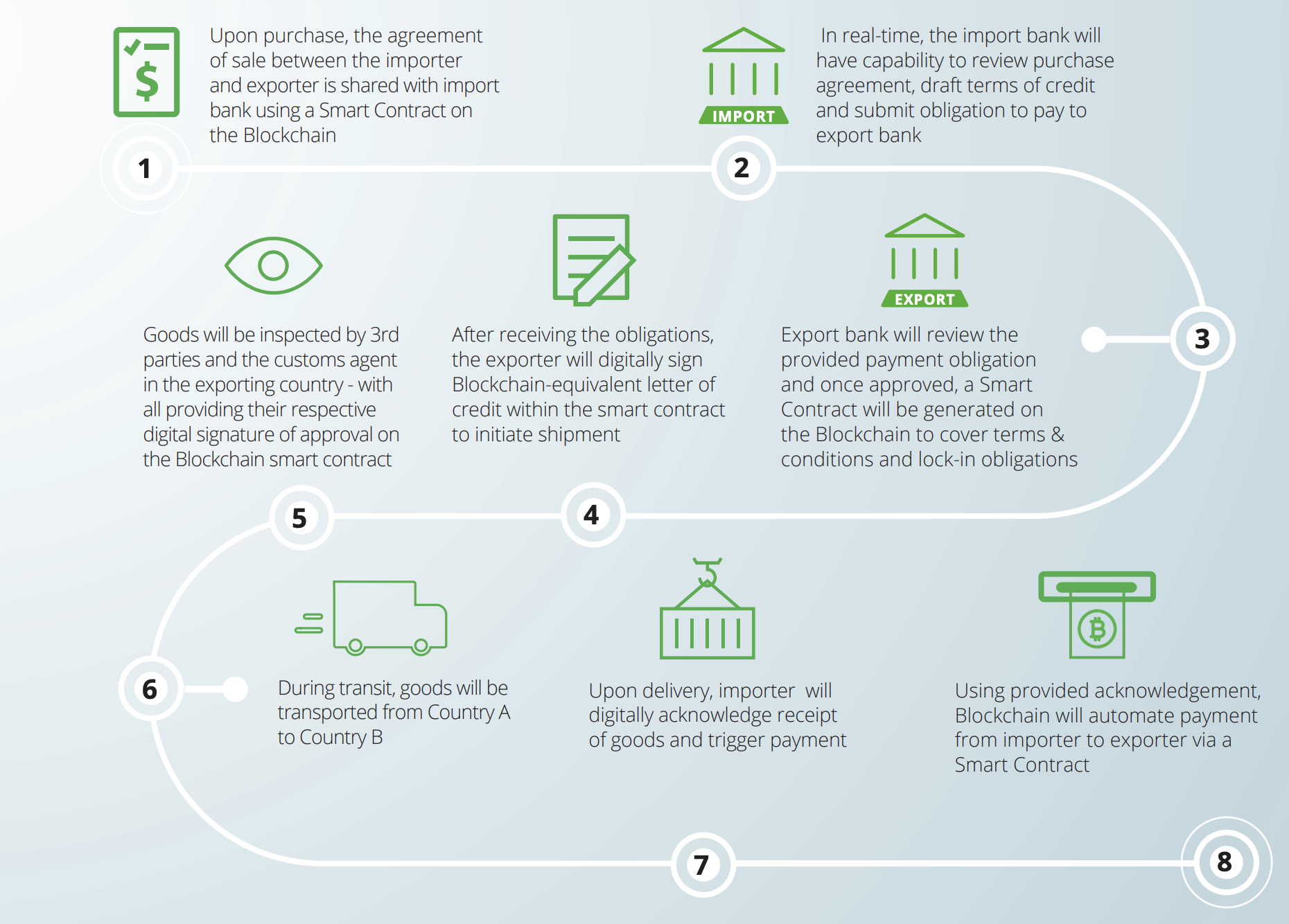
Trade Finance - Komgo
September 2018, fifteen of the world’s largest banking and commodity companies announced the formation of komgo - a global blockchain-based trade financing platform.
Collaboration between: ABN AMRO, BNP Paribas, Citi, Crédit Agricole Group, Gunvor, ING, Koch Supply & Trading, Macquarie, Mercuria, MUFG Bank, Natixis, Rabobank, Shell, SGS and Société Génerale
While using ETHEREUM, it will launch with two initial products: a KYC process and a Letters of Credit product.
https://media.consensys.net/enterprise-blockchain-for-trade-financing-c005ec8fa079
https://block.co/
-
Ease of Publication & Distribution Independent validation
-
Immutable Records - Digital fingerprints (hashes) of the individual certificates issued, are placed permanently in a blockchain transaction
-
Reduced time to issue Certificates
-
Costs of re-issuing certificates in the case the hard copy is lost are minimal
-
Ease and instant authentication by interested parties (e.g. employers) even if the application used or the institution’s website no longer exists. Operational costs minimized
Academic Certificates
https://www.velox.re/
- Authenticity: Property holders could digitally prove and transfer ownership immediately without the need to pay and wait for third-party verification
- Eliminate fraud and costs: Funds of sender and recipient can be logged using the multisig technology and be triggered upon smart contract execution i.e. transfer a land title when funds are received. A “digital ownership certificate” cannot be replicated, and can be linked to one property in the system, making selling or advertising properties you don’t own almost impossible. No further middlemen, paper work and delays
- Transparency: Creation of unique digital IDs for real estate assets, buyers and sellers. Enable faster mortgage process and transfer of ownership. For the buyer, credit history and income could be instantly verifiable, avoiding time-consuming tasks involving banks, lawyers and estate agents. Homeowners can prove ownership and time of residence within a property. For assets, digital identities could be assigned, which would include the chain of ownership, list of repairs etc.
Real Estates
https://www.youtube.com/watch?v=tdhpYQCWnCw
- Digitize Supply Chain Process
- Track the paper trails of shipping containers
- Reduce time spent in transit and shipping process
- Enhance transparency and security of product information exchanged between parties
- Reduce costs and complexity Improve stock management
- Reduce fraud and errors on the quality of products
Supply Chain
- Reduce voter fraud, inefficiencies with verifiable audit trails
- Minimize government fraud, digitize most processes
- Increase accountability and compliance for government officials
- Identity validation; integrity of citizen registry data
Government & Voting
State owned crypto
Deloitte, 2015:
https://www2.deloitte.com/content/dam/Deloitte/us/Documents/strategy/us-cons-state-sponsored-cryptocurrency.pdf
Dutch Central Bank, 2016:
https://www.coindesk.com/dutch-central-bank-to-create-dnbcoin-prototype
FED, 2017:
https://www.cnbc.com/2017/11/29/federal-reserve-starting-to-think-about-its-own-digital-currency-dudley-says.html
Venezuela's Petro:
https://www.reuters.com/article/venezuela-economy-cryptocurrency/venezuela-oil-backed-cryptocurrency-to-launch-in-days-government-idUSL1N1OS1GY
Reserve Bank of New Zeland, 2018:
https://www.rbnz.govt.nz/-/media/ReserveBank/Files/Publications/Bulletins/2018/2018jun81-07.pdf


Ethereum Enterprise Alliance
In March 2017 a group of 30 enterprises announced formation of Ethereum Enterprise Alliance, which has recently grown to more than 200 members, making it probably the largest blockchain consortium today.
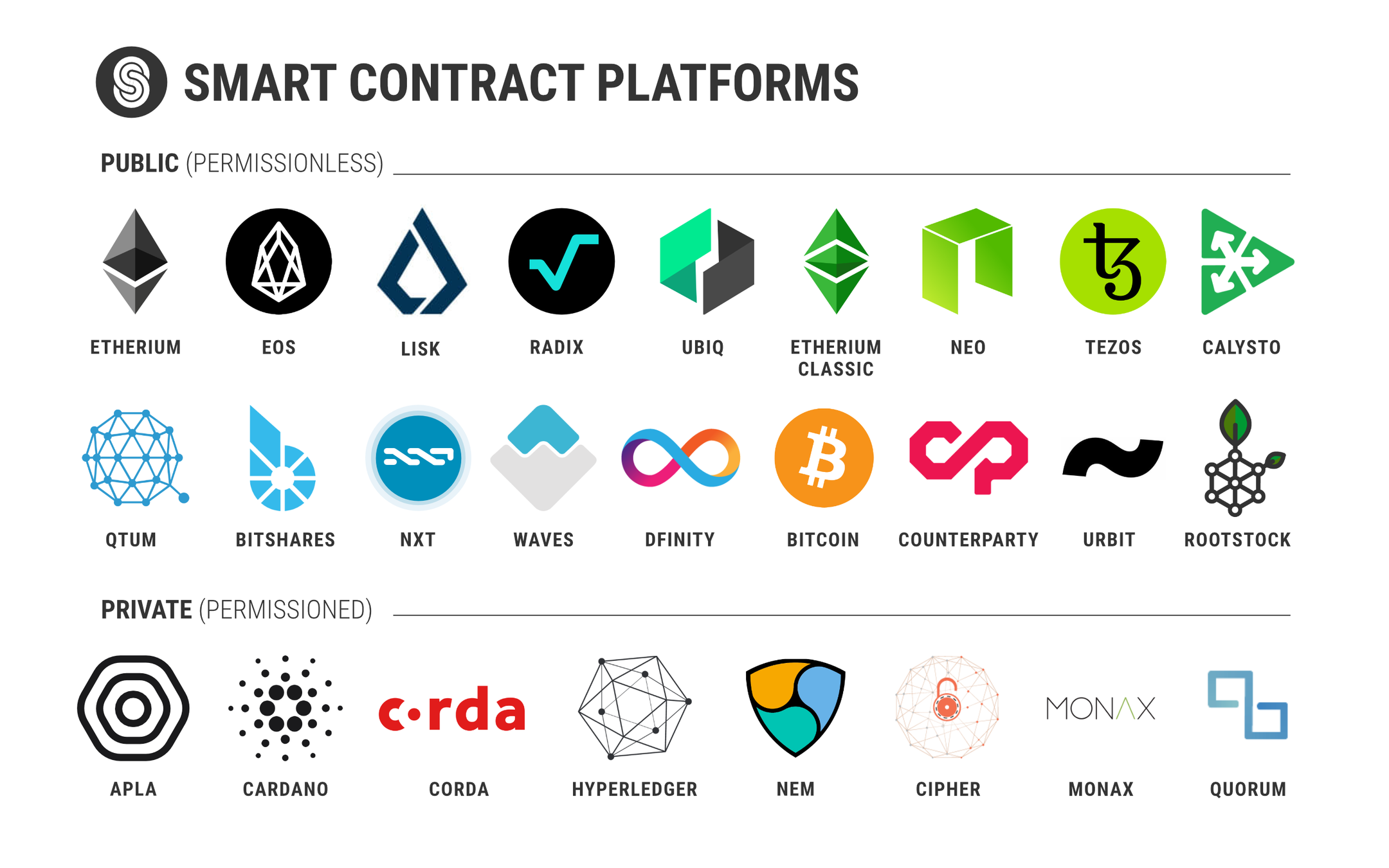
EEA’s focus in bringing Ethereum to the enterprise environment, meaning moving from a public, permissionless to a private, permissioned setting, which means it will be easier to provide better support for privacy and performance. There are some plans to support anchoring on the public Ethereum network as a way to securely timestamp the chain state.

Otázky?

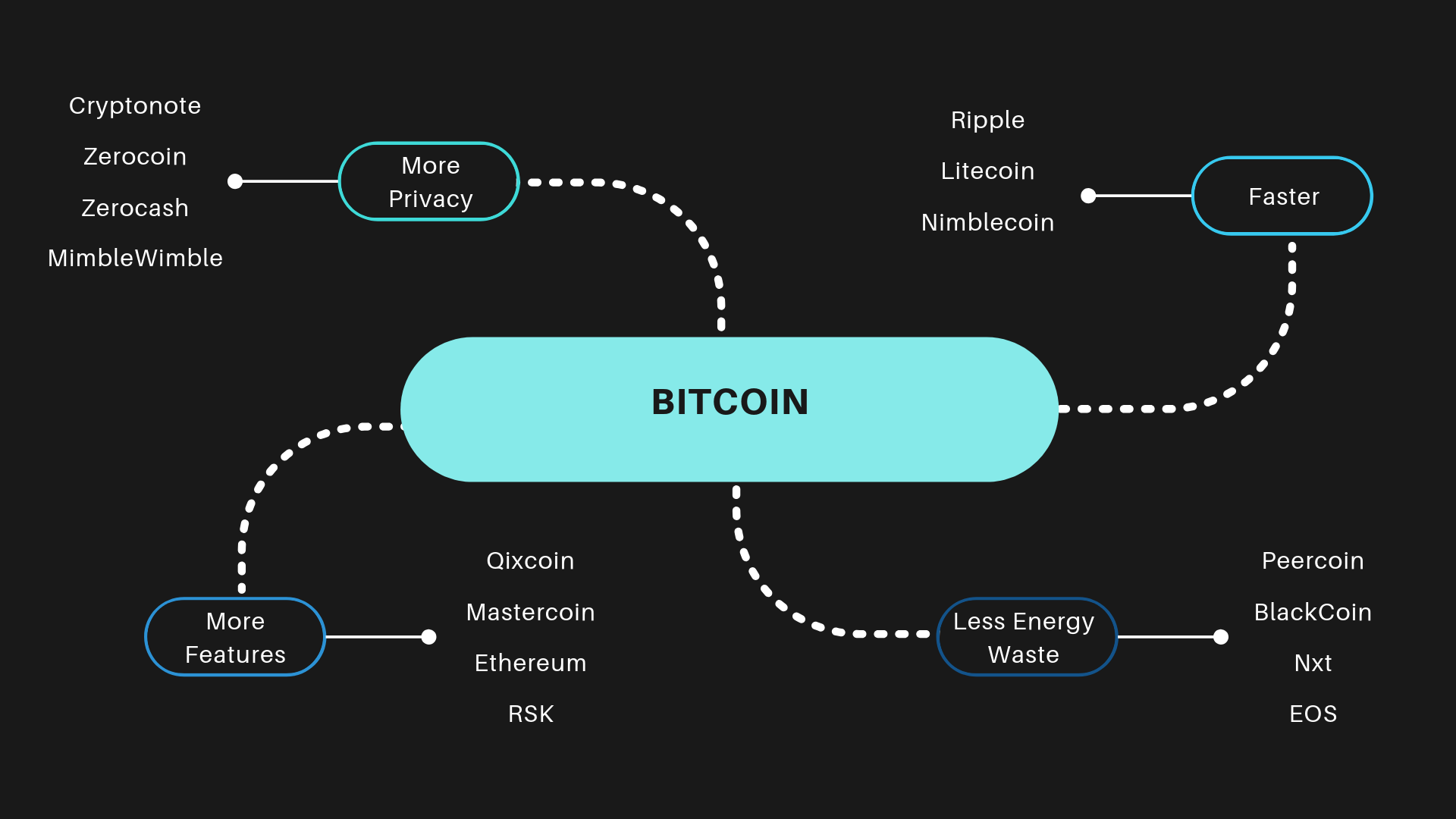
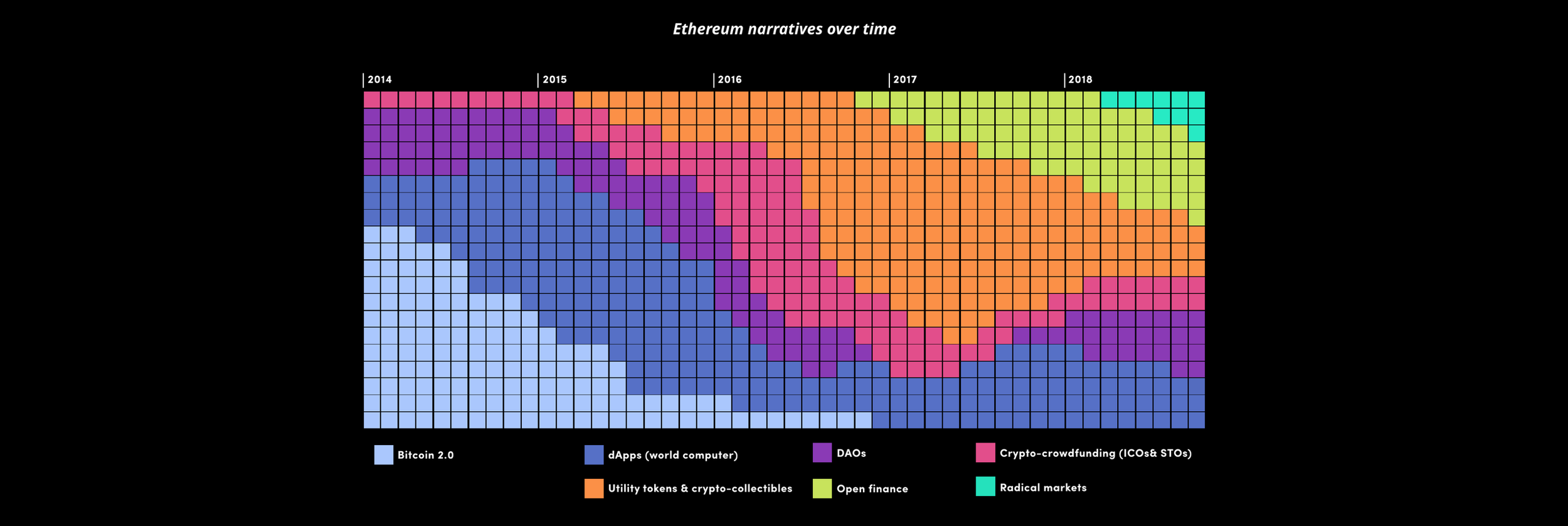
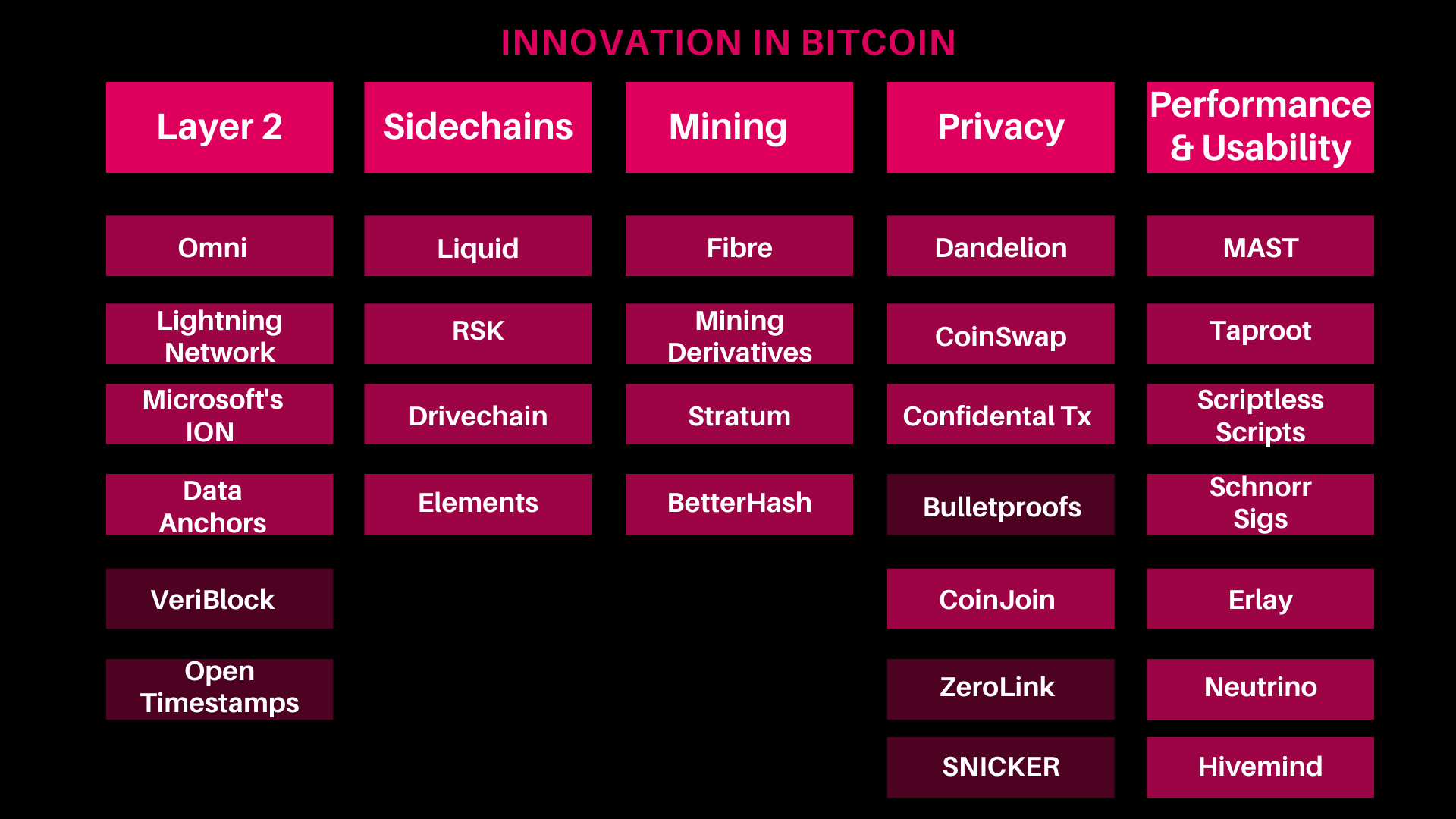
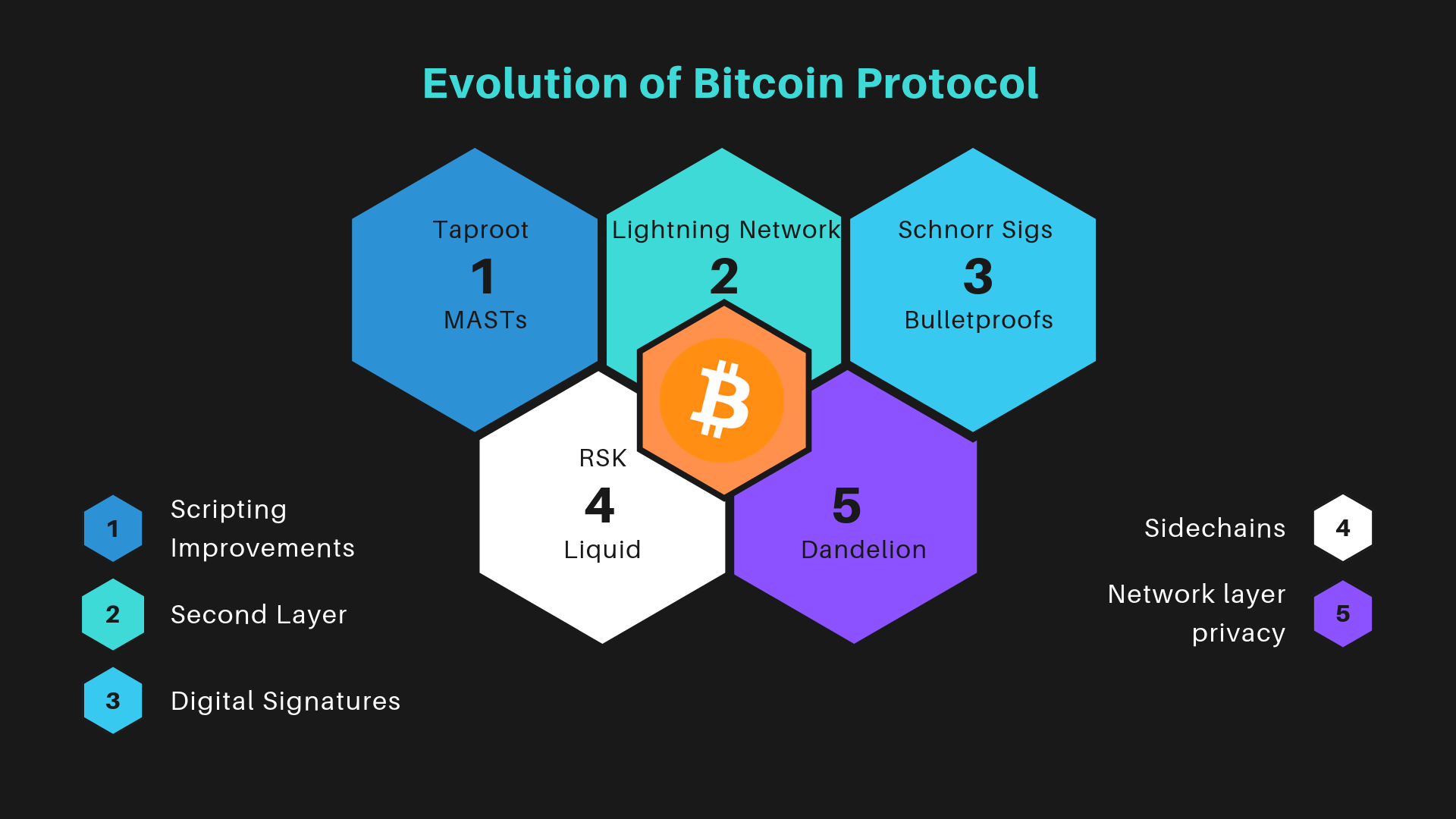
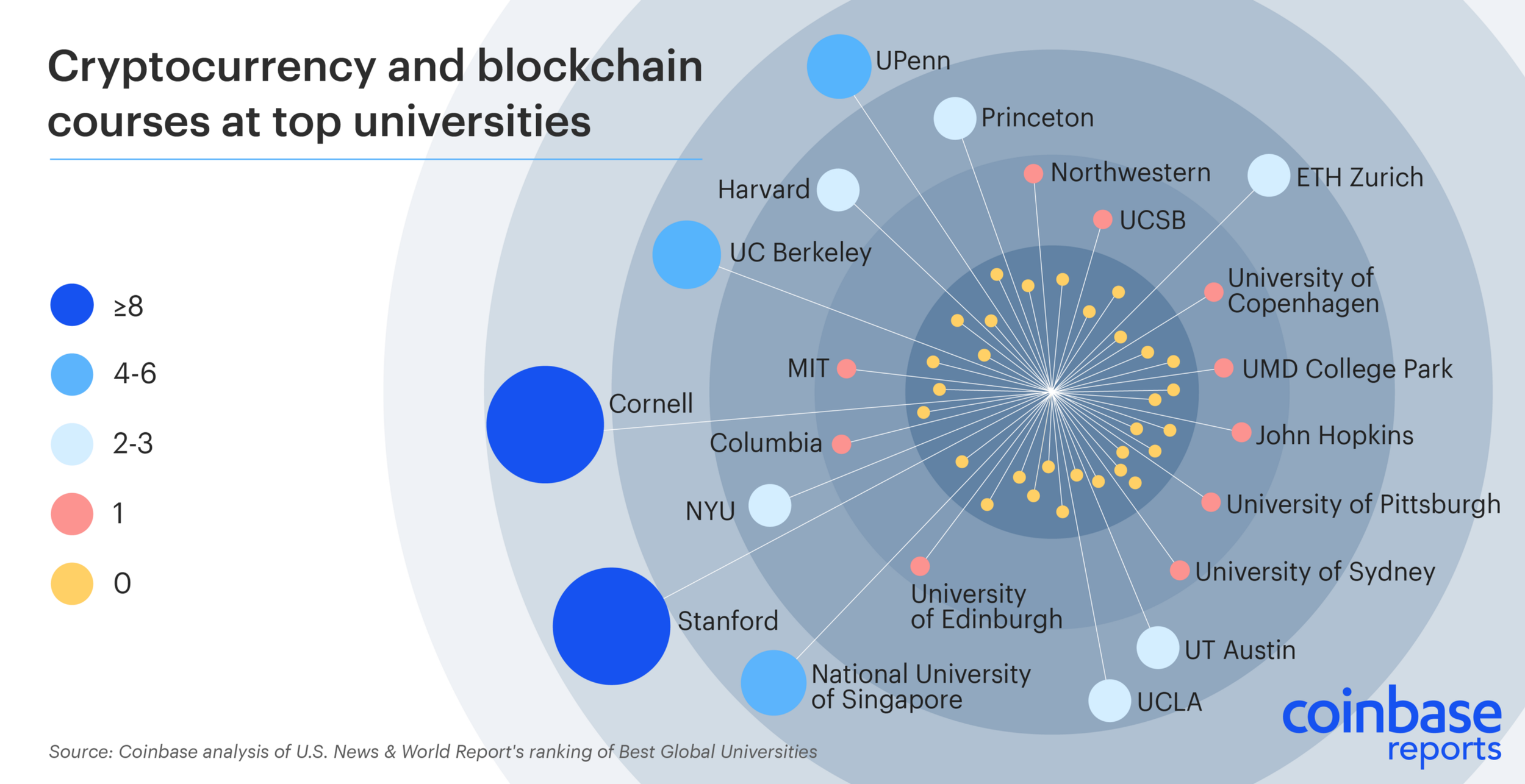
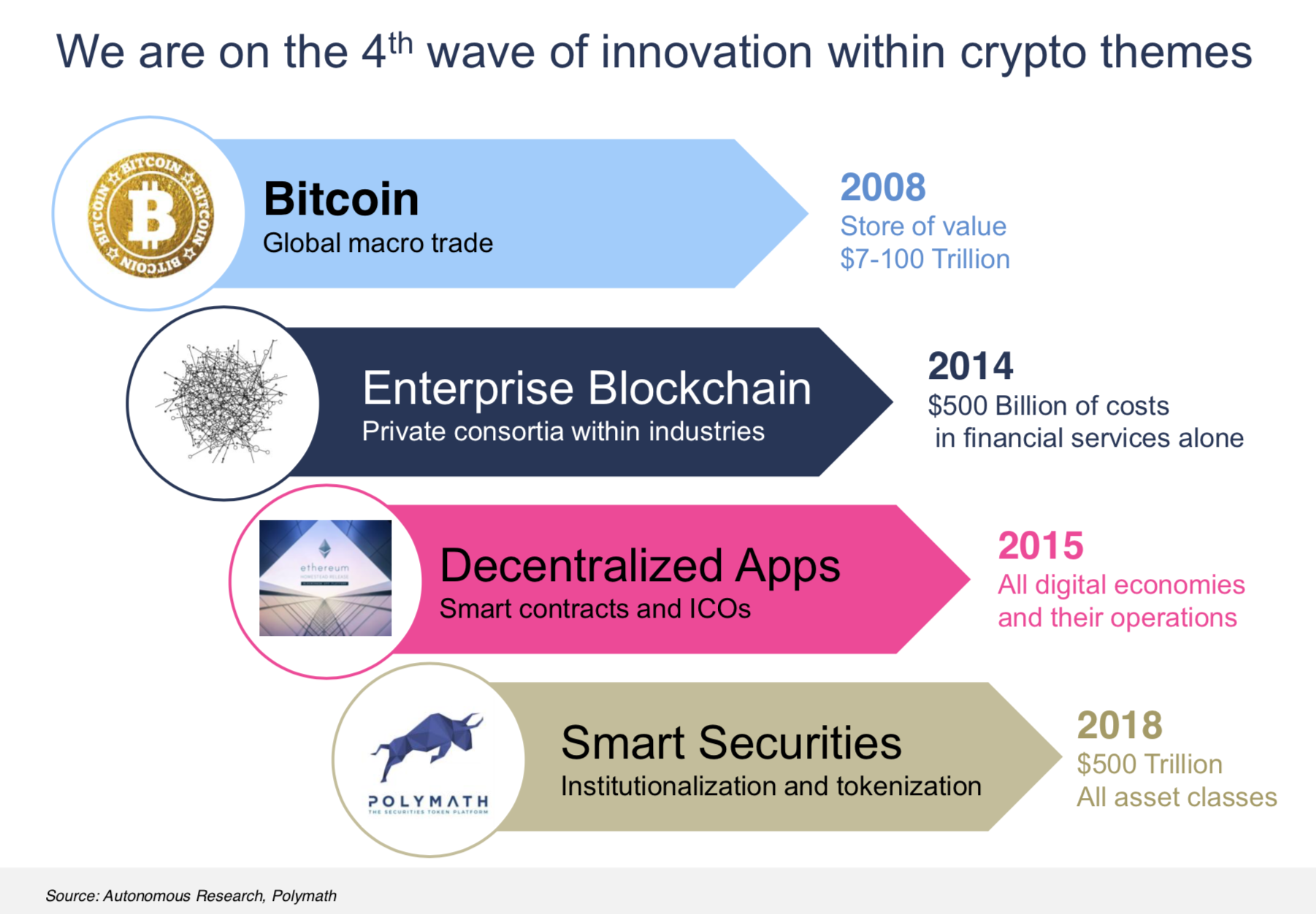
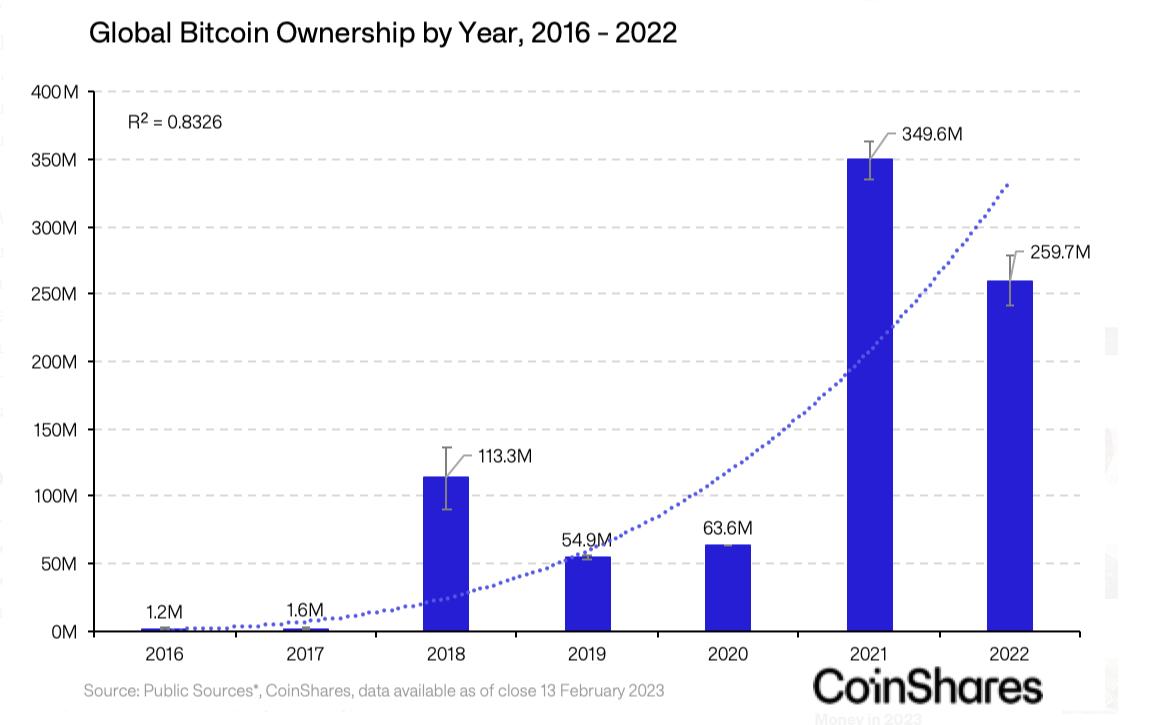
Trendy, projekty, vízie

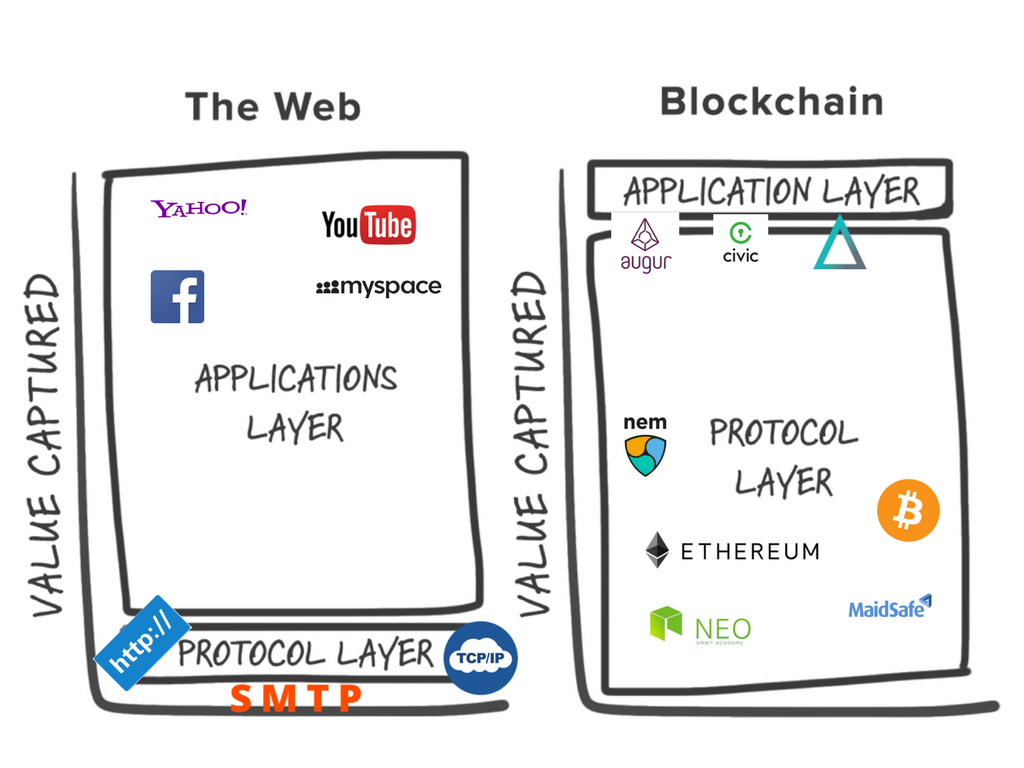
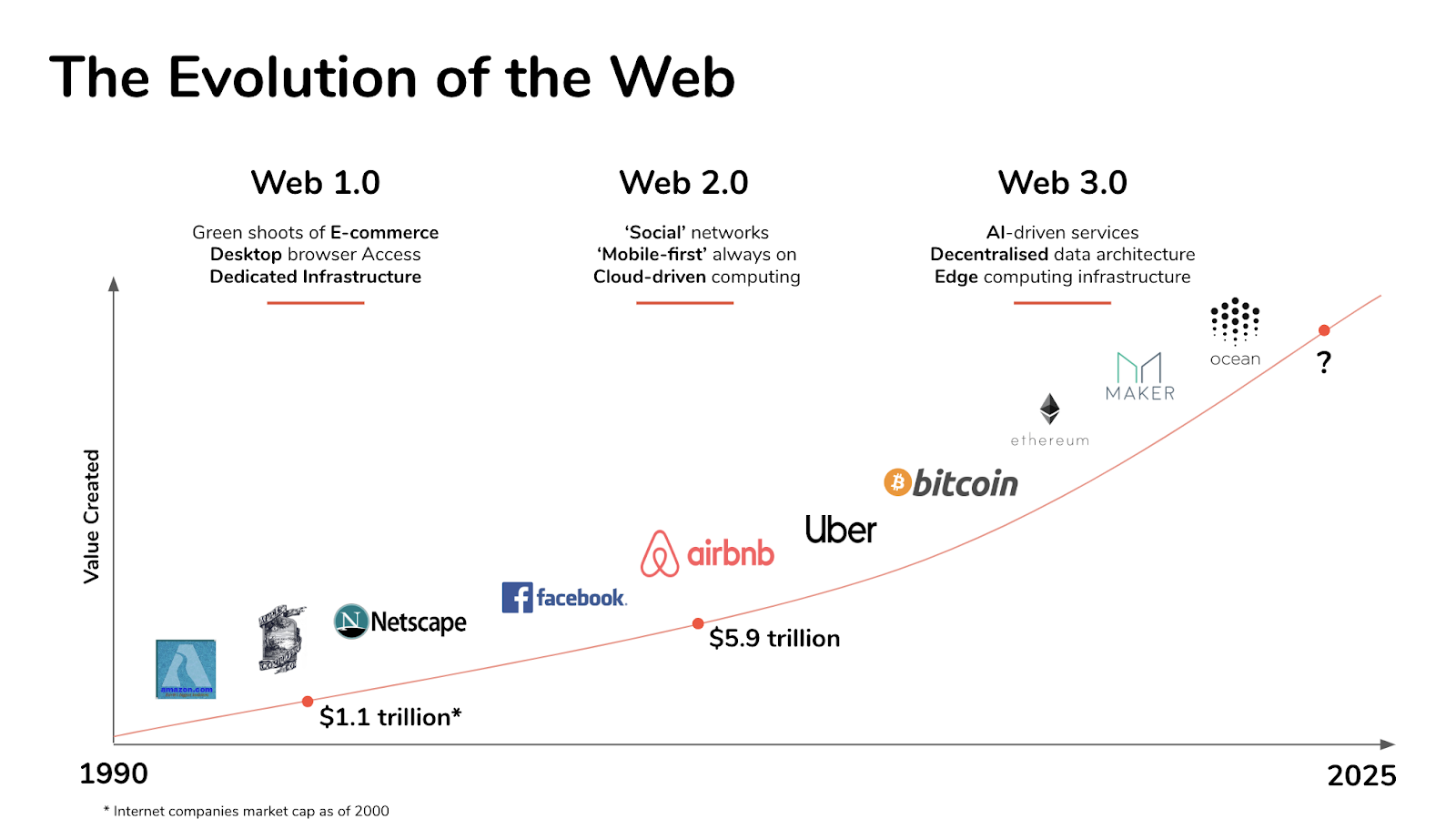
Zmena paradigmy?
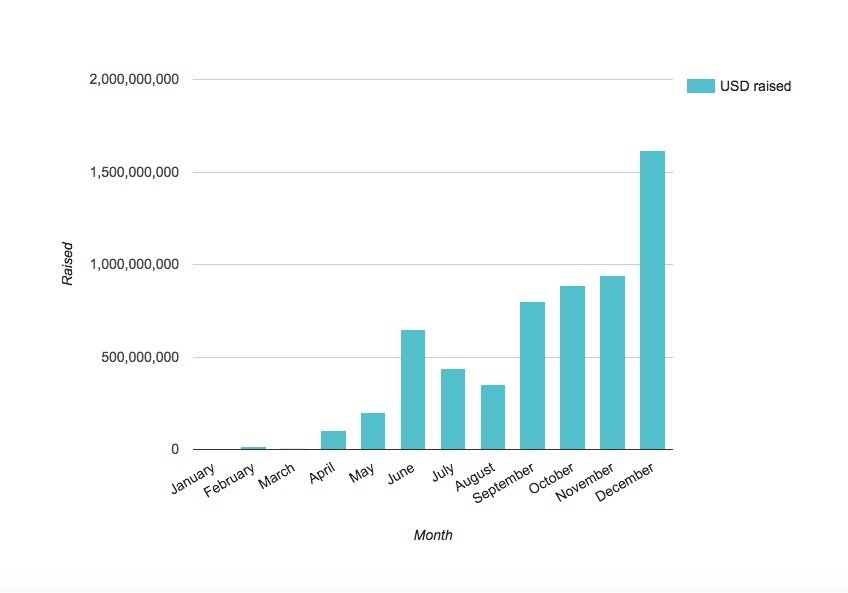
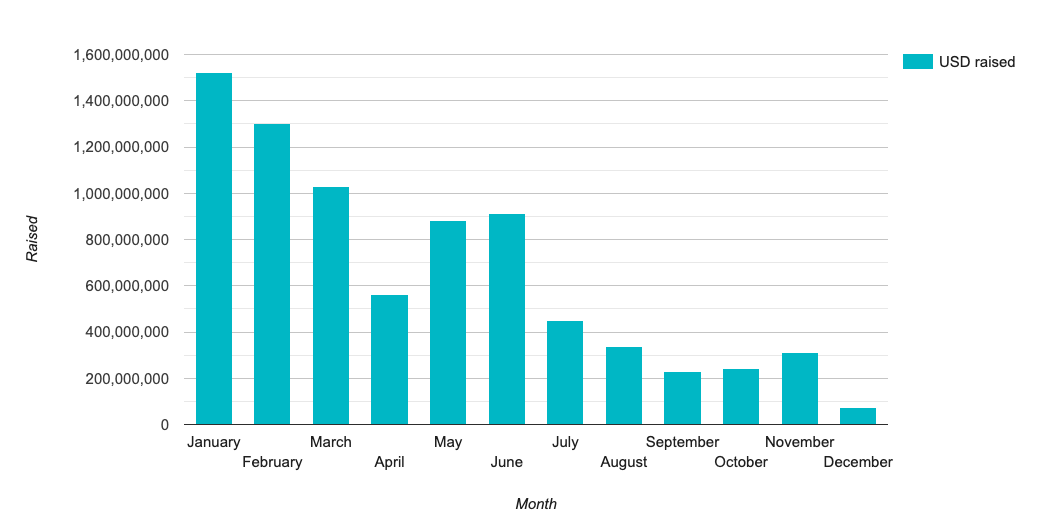
ICOs in 2017
ICOs in 2018


Text
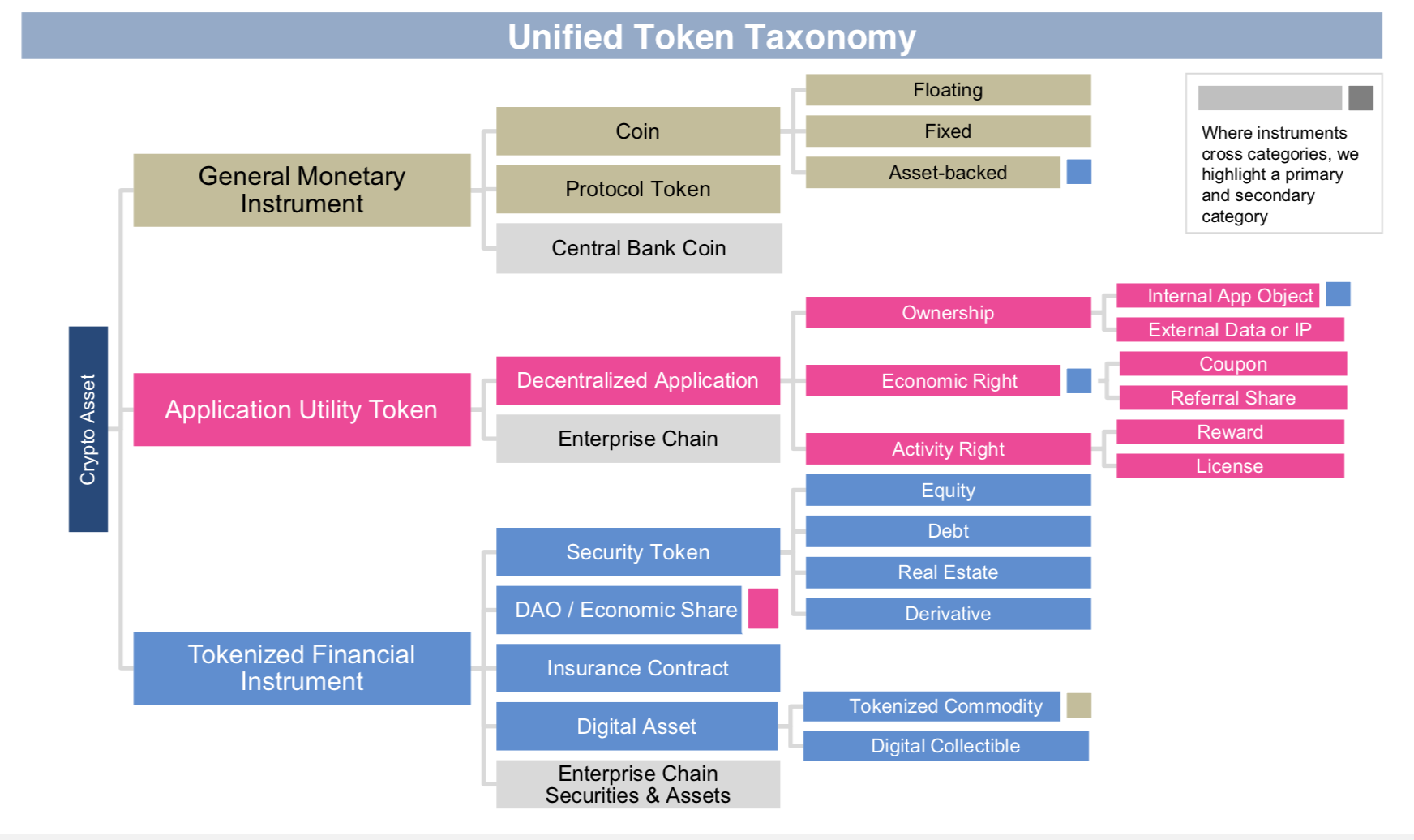
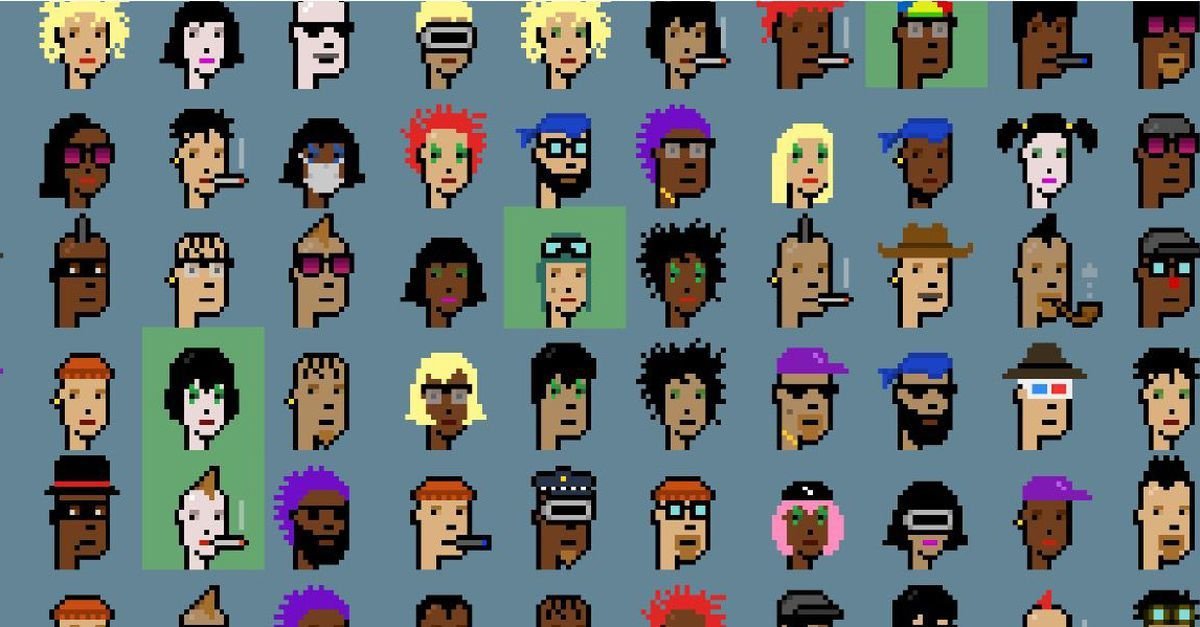
Non-fungible tokens



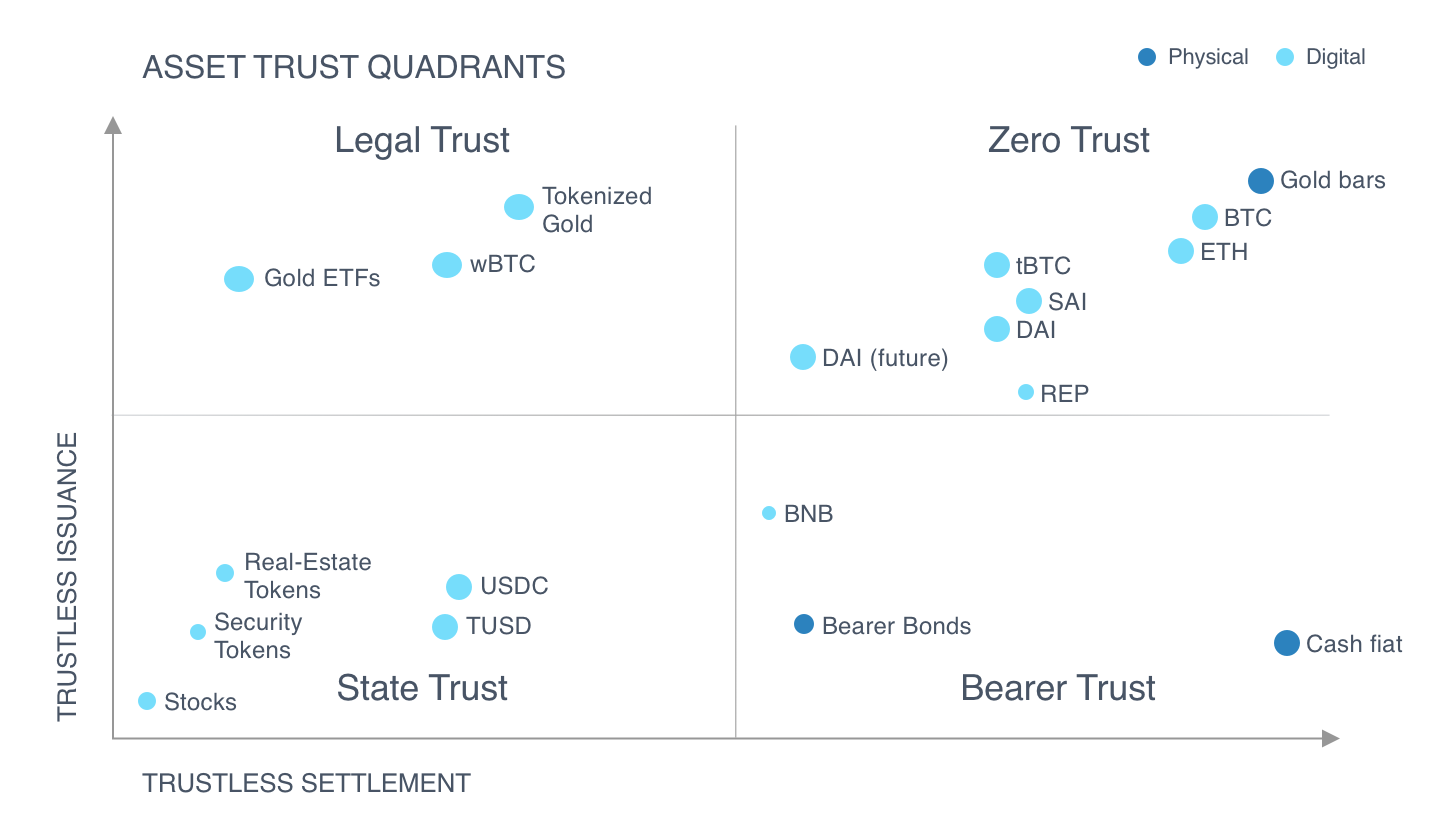
Security Token Offerings
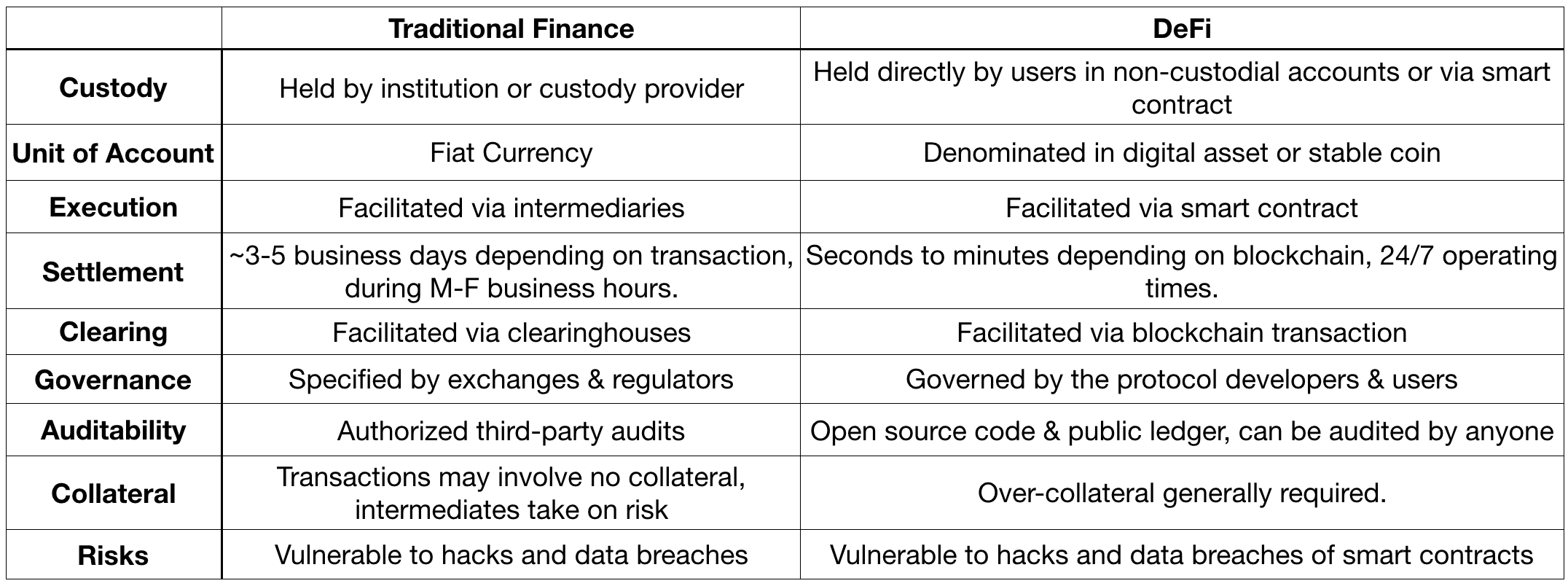
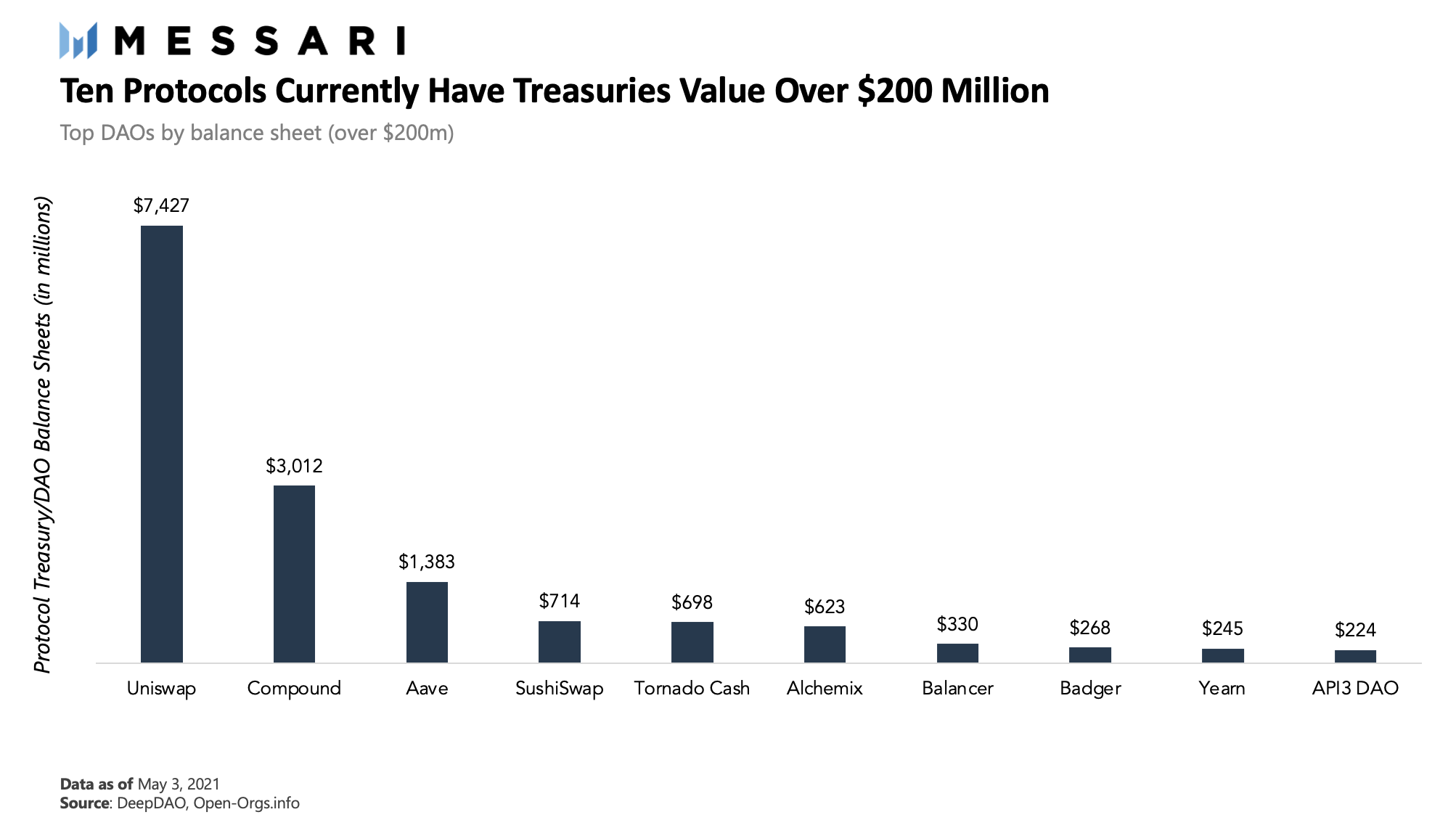
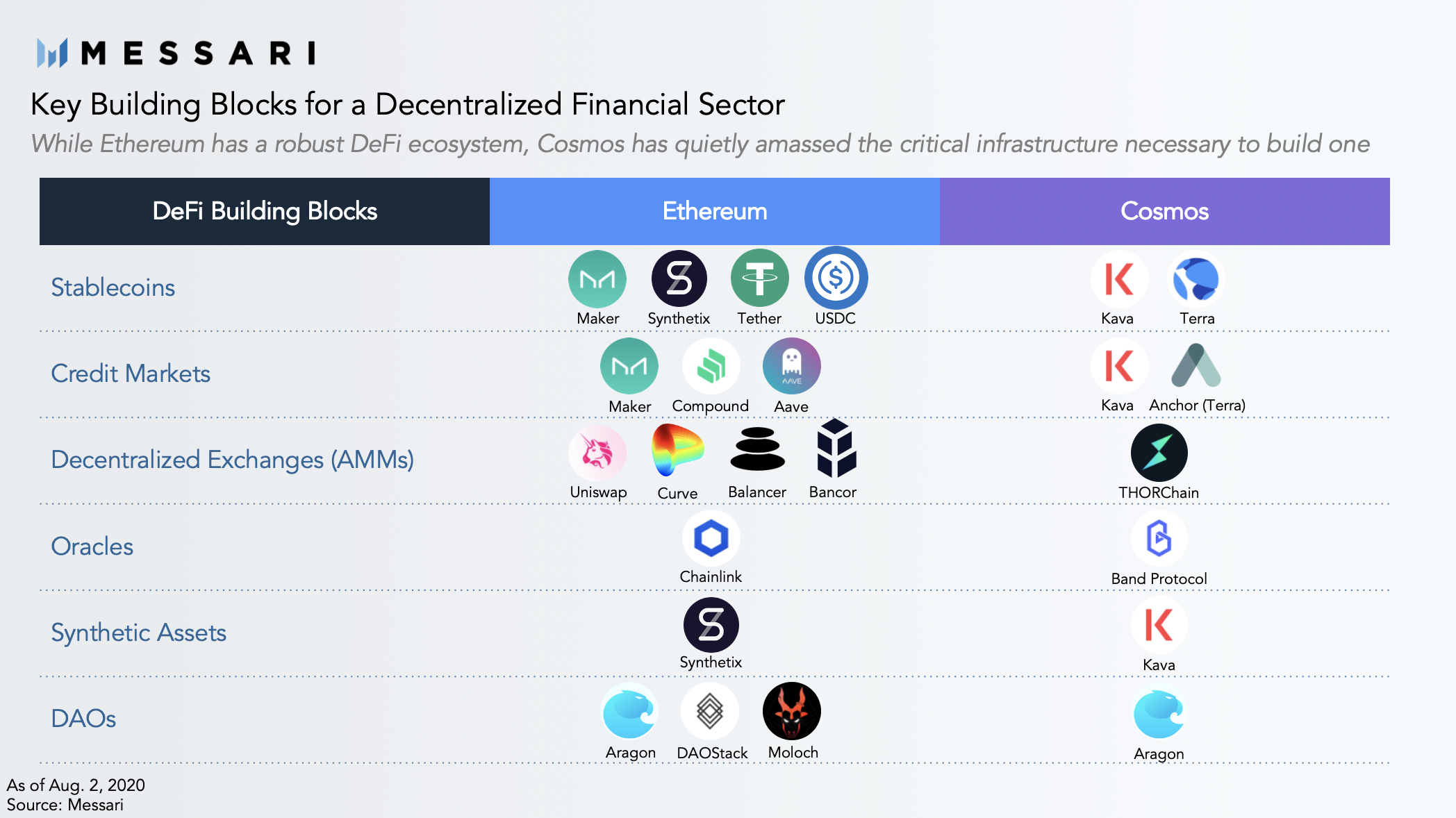
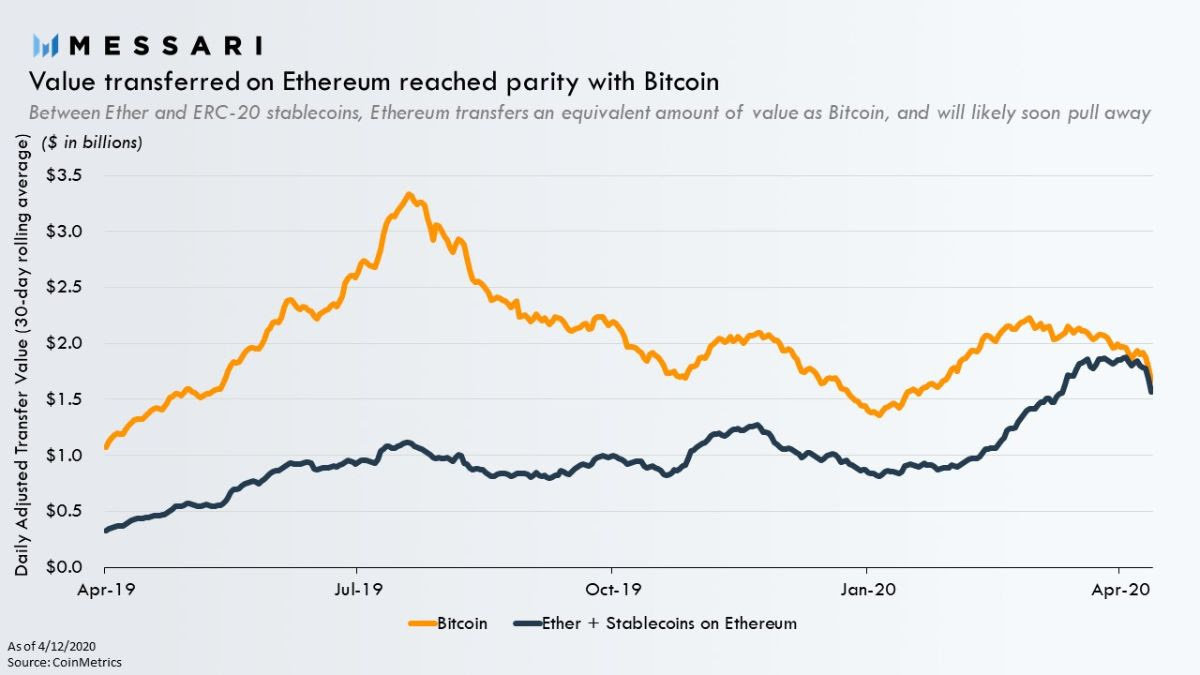
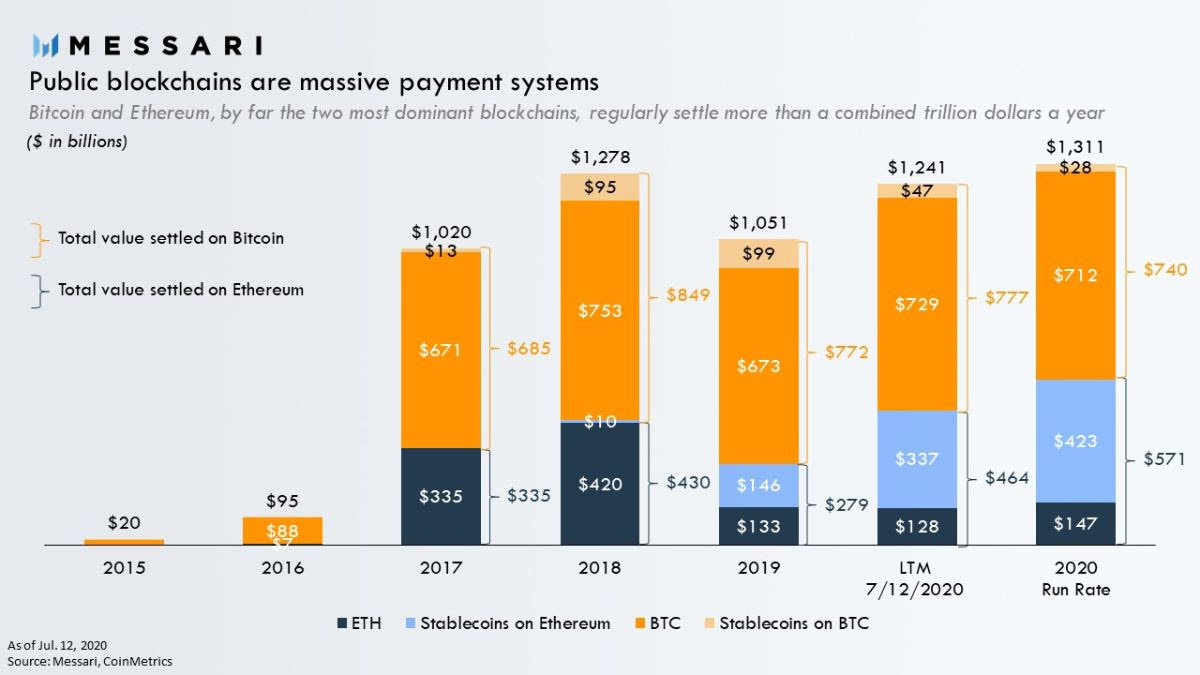
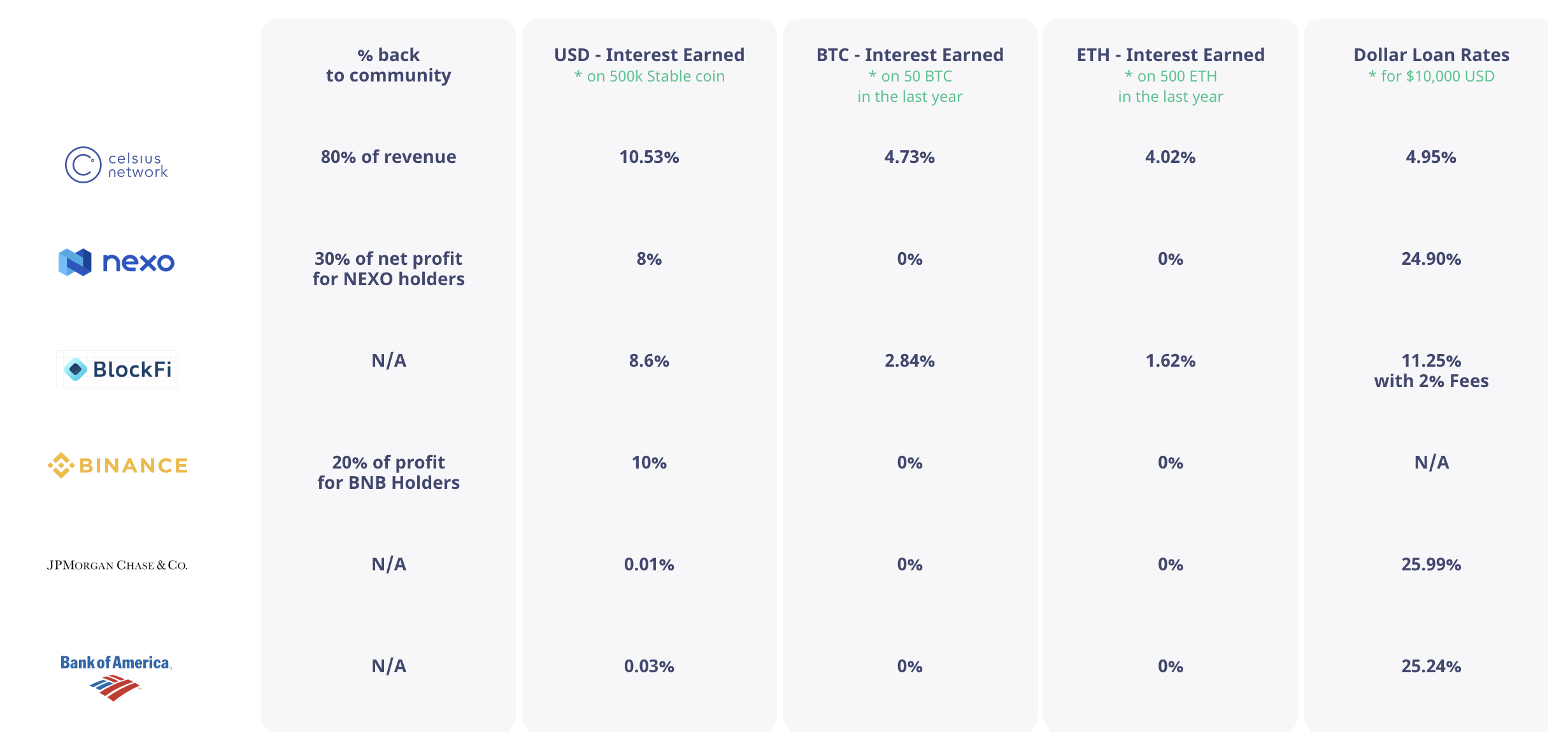
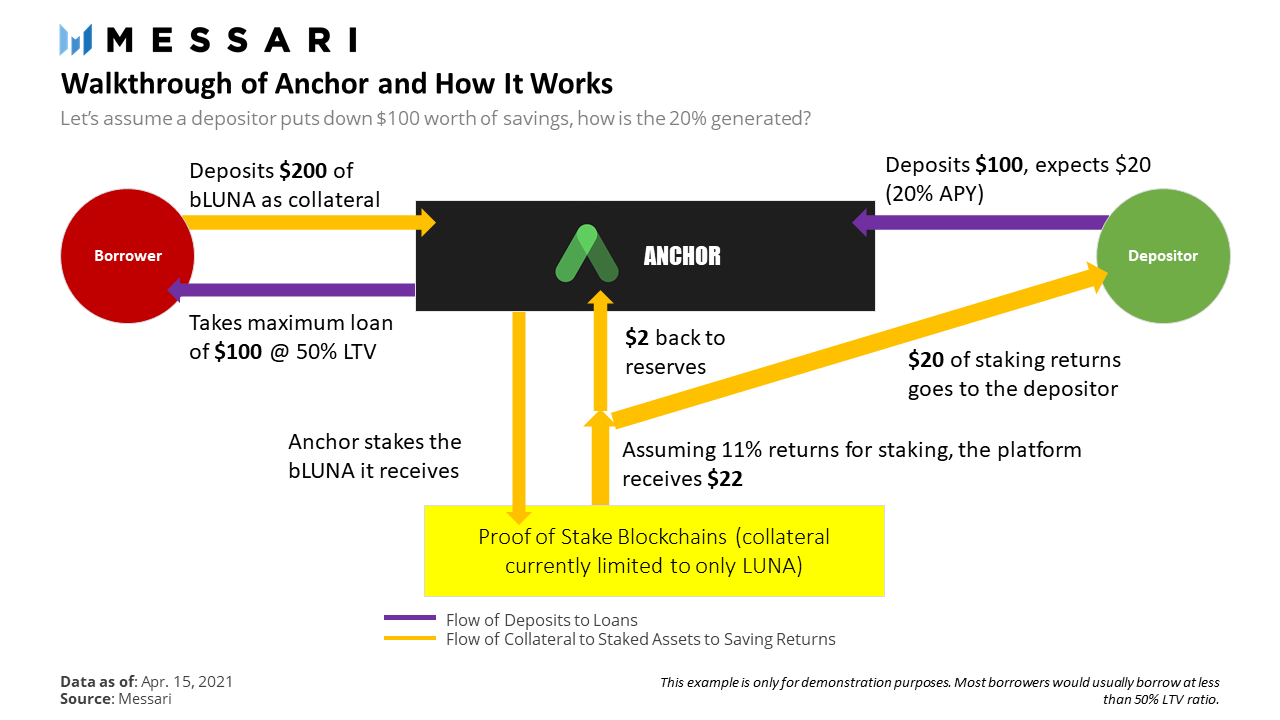
DeFi

DeFi
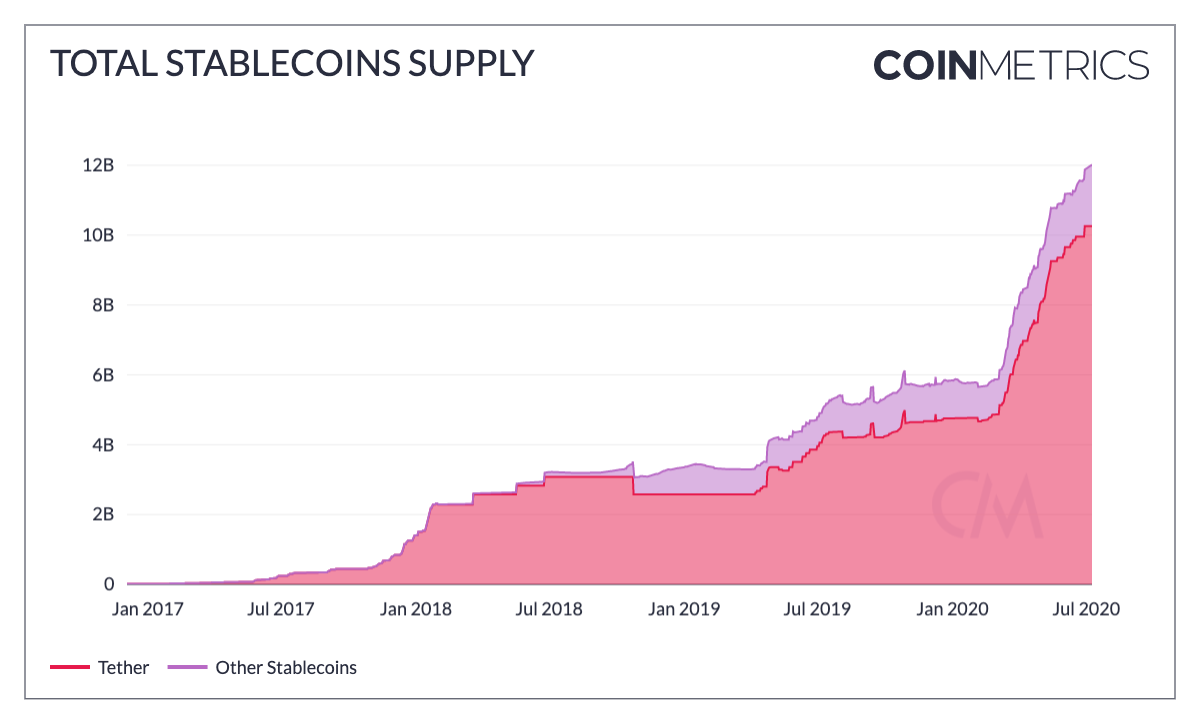
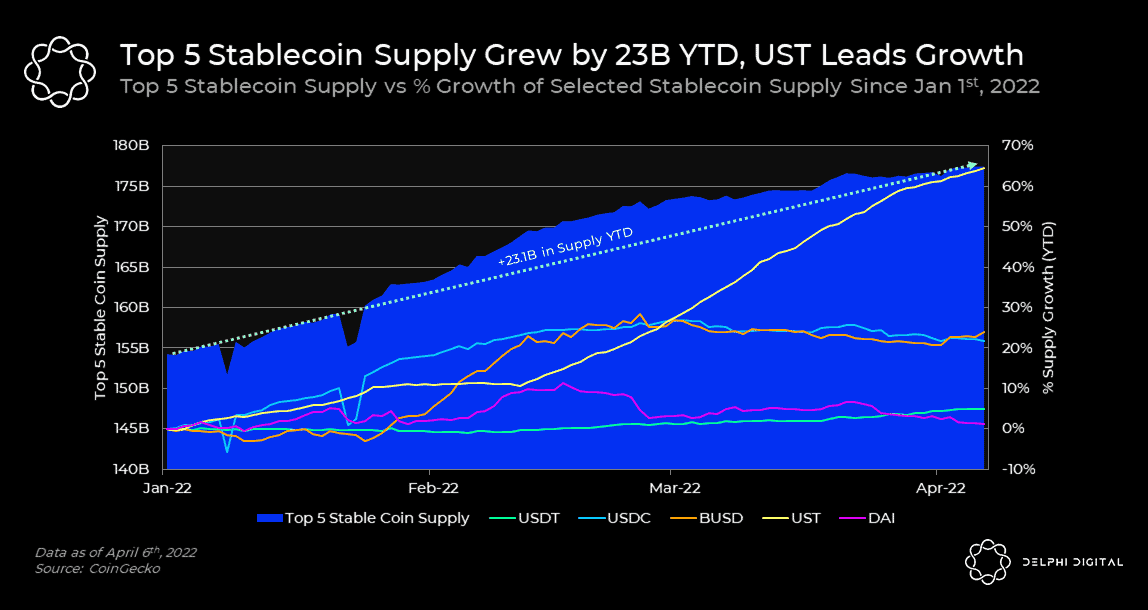
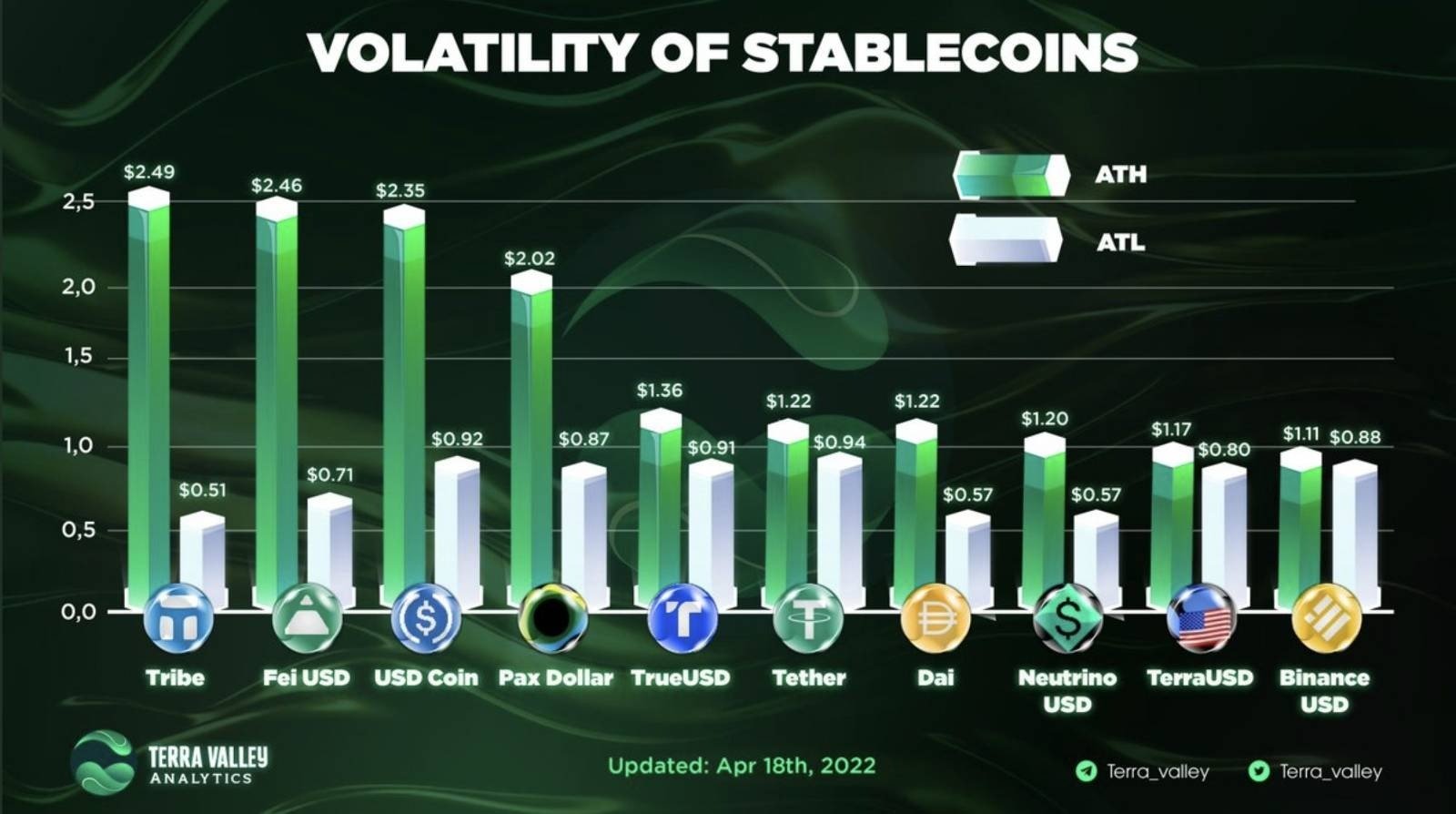
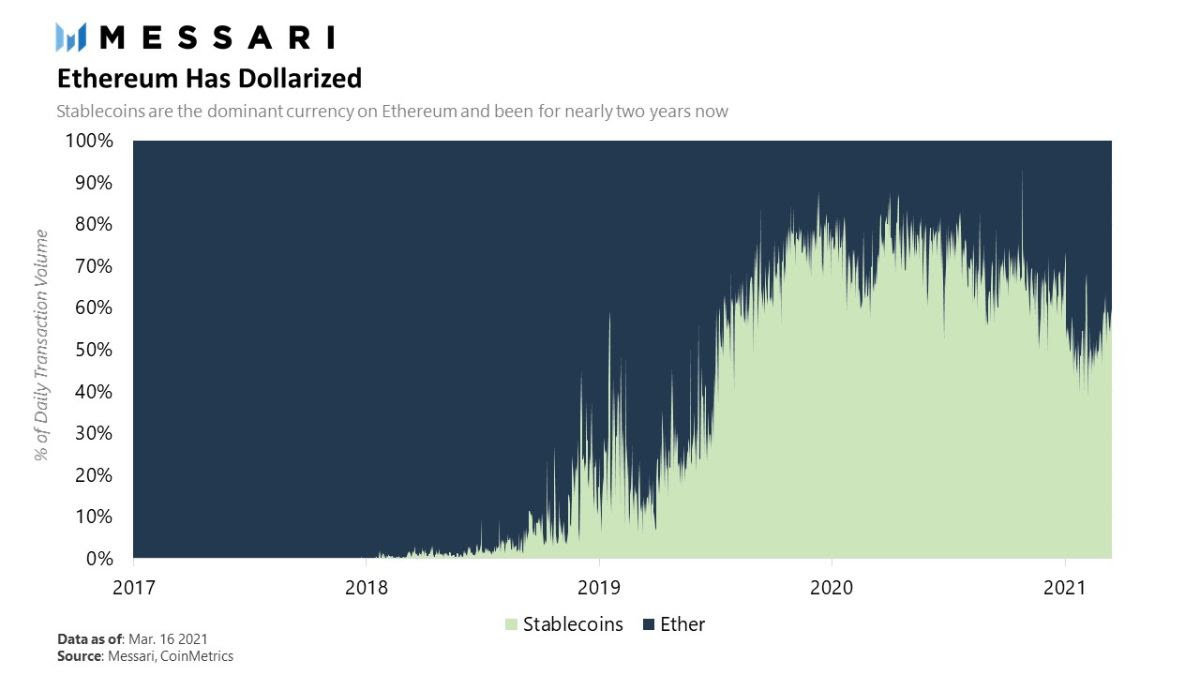
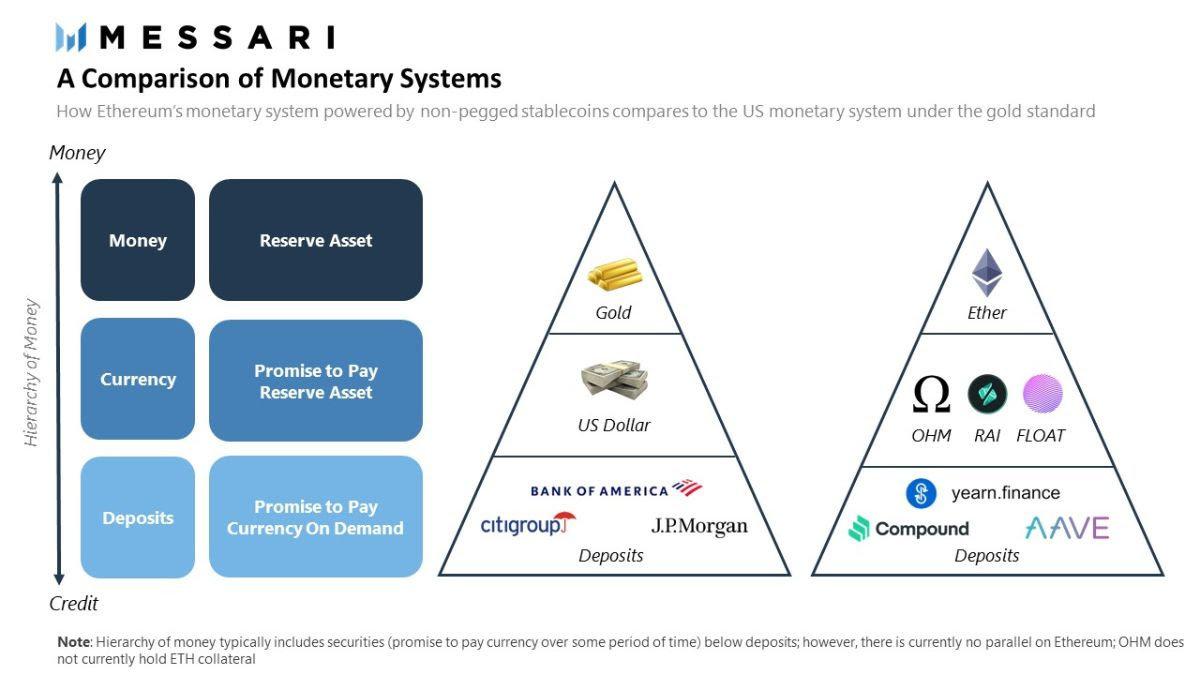
Stable Coins
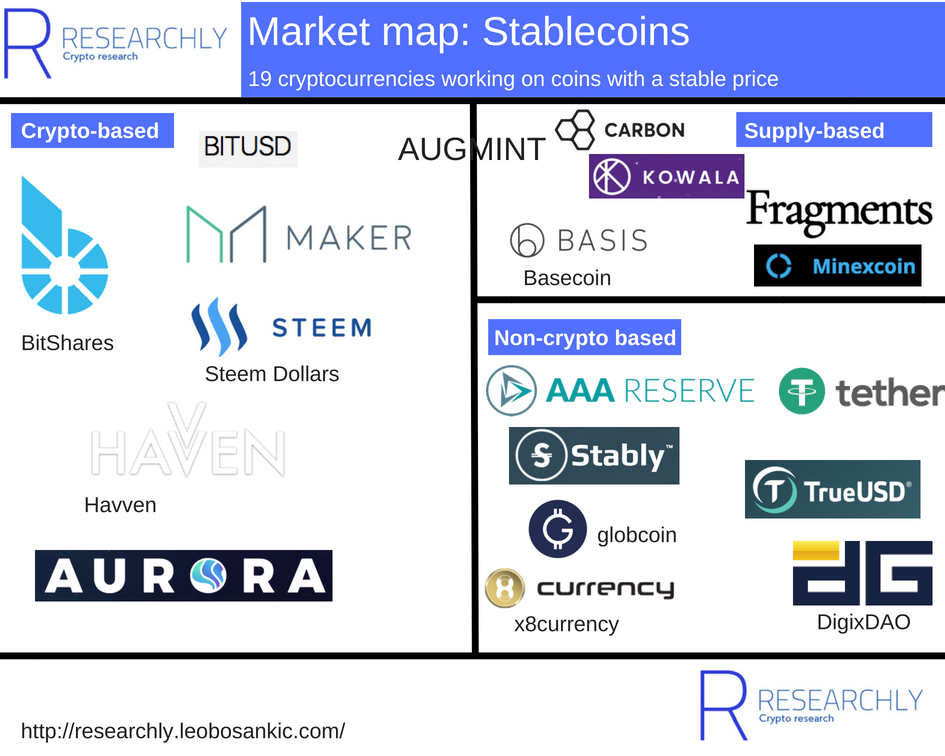
Stable Coins III.
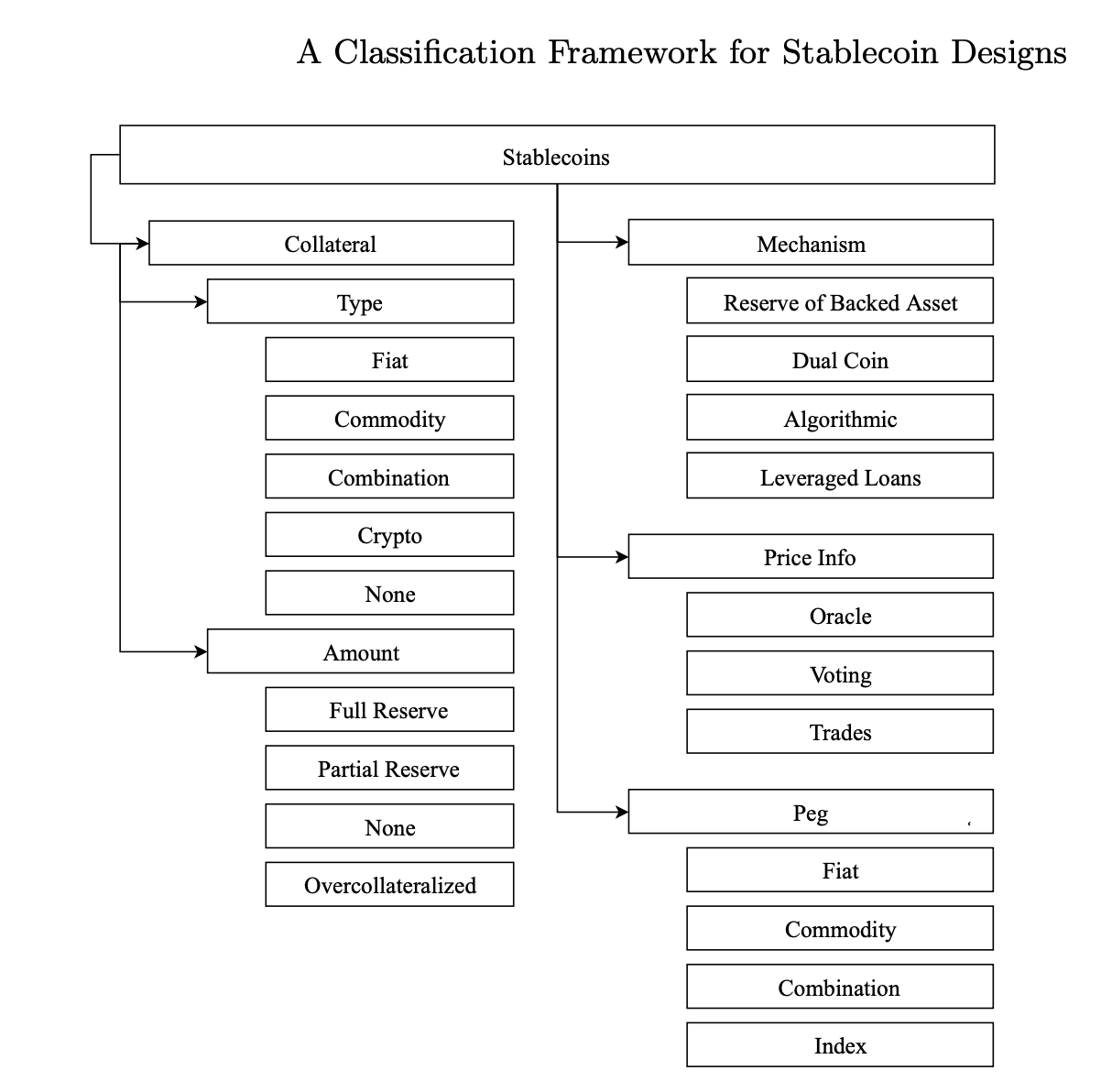
Stable Coins
Key components
Key components
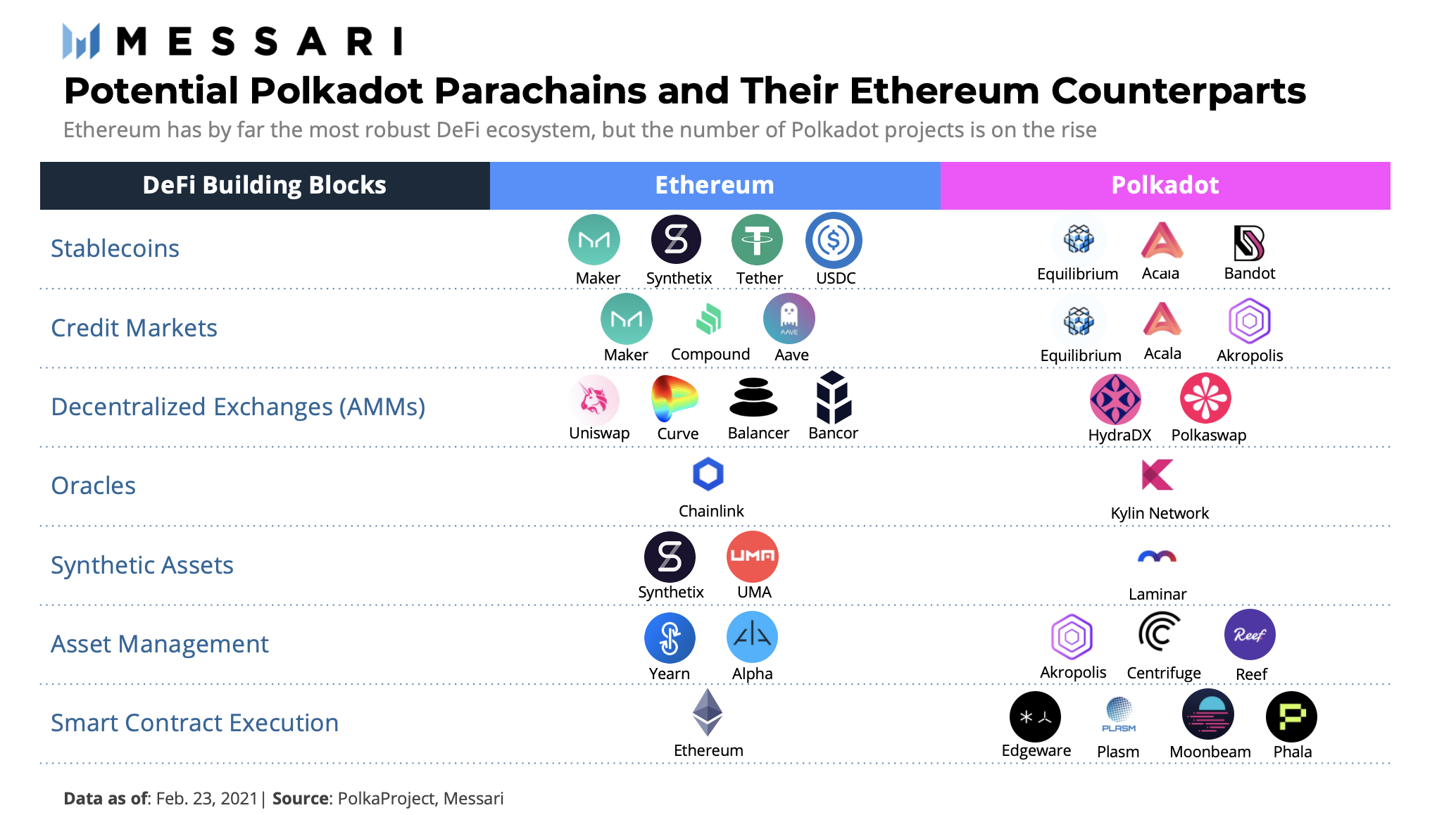
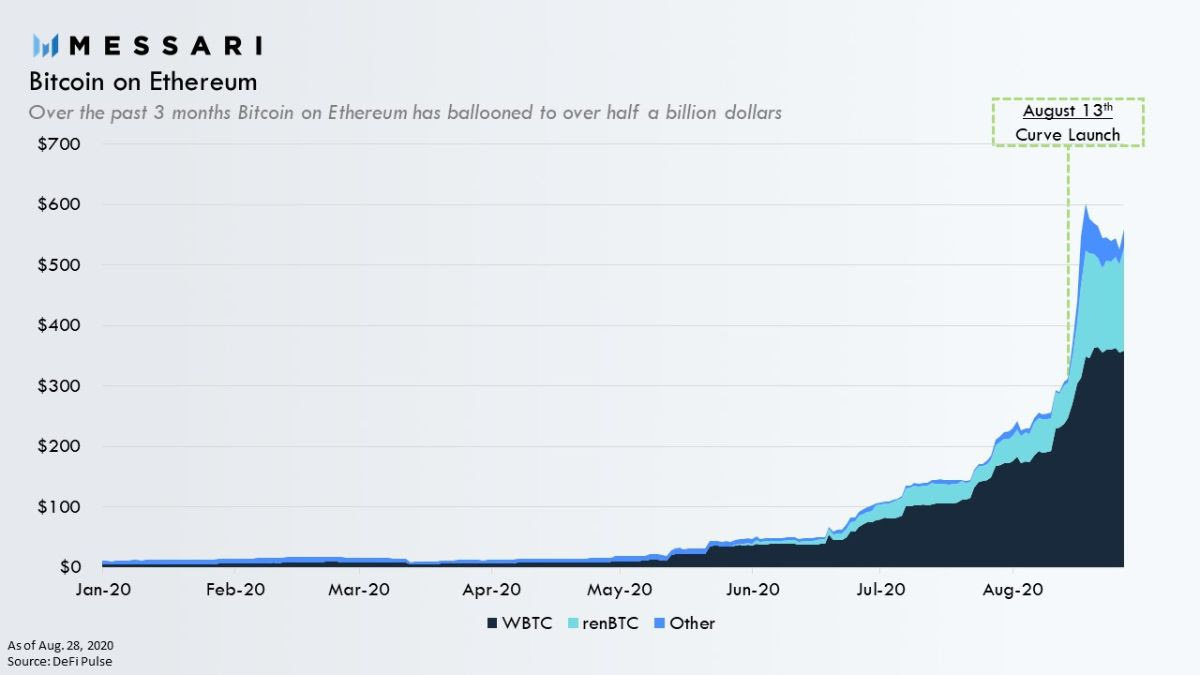
Tokenized BTC
First, ETH is turned into “wrapped ETH” (WETH), which is simply an ERC20 wrapping around ETH. This “tokenizes” ETH so it can be used like any other ERC20 token.
Next, WETH is turned into “pooled ETH” (PETH), which means it joins a large pool of Ethereum that is the collateral for all Dai created.
-
Once you have PETH, you can create a “collateralized debt position” (CDP), which locks up your PETH and allows you to draw Dai against your collateral, which is PETH.
As you draw out Dai, the ratio of debt in the CDP increases. There is a debt limit that sets a maximum amount of Dai you can draw against your CDP.
Once you have Dai, you can spend or trade it freely like any other ERC20 token.
DAI - How
-
You need a loan, and have an asset (ETH) to use as collateral for your loan
-
You believe ETH is going up in value. You can use your CDP to buy ETH on margin — you lock up your ETH in a CDP, draw Dai against it, use the Dai to buy more ETH on an exchange, and then use that ETH to further increase the size of your CDP.
--> without any third-party or centralized authority
- The demand for Dai drives the price above $1 USD. When this occurs, you can create Dai then immediately sell it on an exchange for greater than $1 USD. This is essentially free money, and is one of the mechanisms the Maker system uses to keep Dai pegged to $1 USD. Dai being worth over $1 USD encourages more Dai to be created.
DAI - Why?
-
If Dai < $1 USD, CDP owners can pay down their debt at a cheaper price!
-
fe. CDP with $1000 in ETH --> draw out 500 Dai
to close the position --> pay back 500 Dai (paying debt destroys Dai).
-
If Dai < $1 USD, then buy cheaper DAI (fe 0.99 USD) --> pay off debt with a 1% discount == free money — $500 loan (500 Dai) --> 500 Dai for $495 (0.99 * 500 = 495, a 1% discount)
-
--> demand for Dai increases its price, until it approaches $1 USD.
If Dai stays below $1, CDP owners continue to pay down debt and remove Dai from the system. -
--> When Dai goes above $1 USD, Dai is created to feed the demand. It is this push and pull, creation and destruction, supply and demand which ensures that Dai always matches the $1 USD peg.
DAI - Peg Mechanism

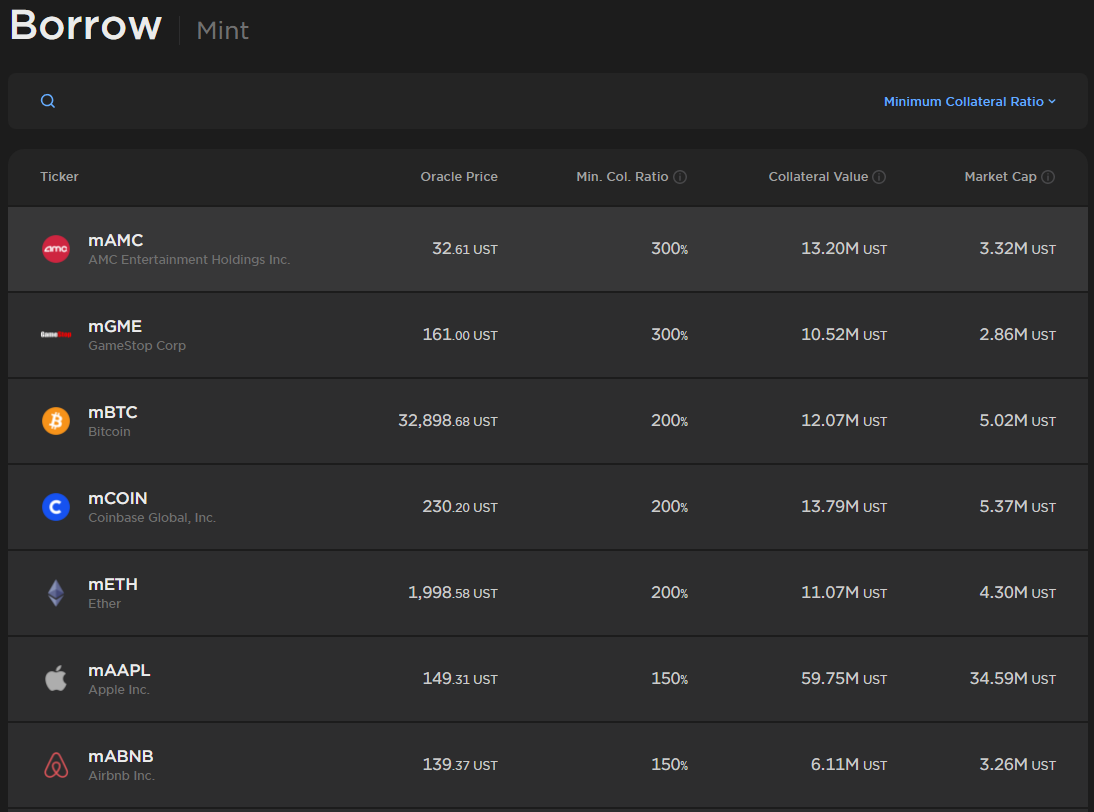
Synthetic Stocks
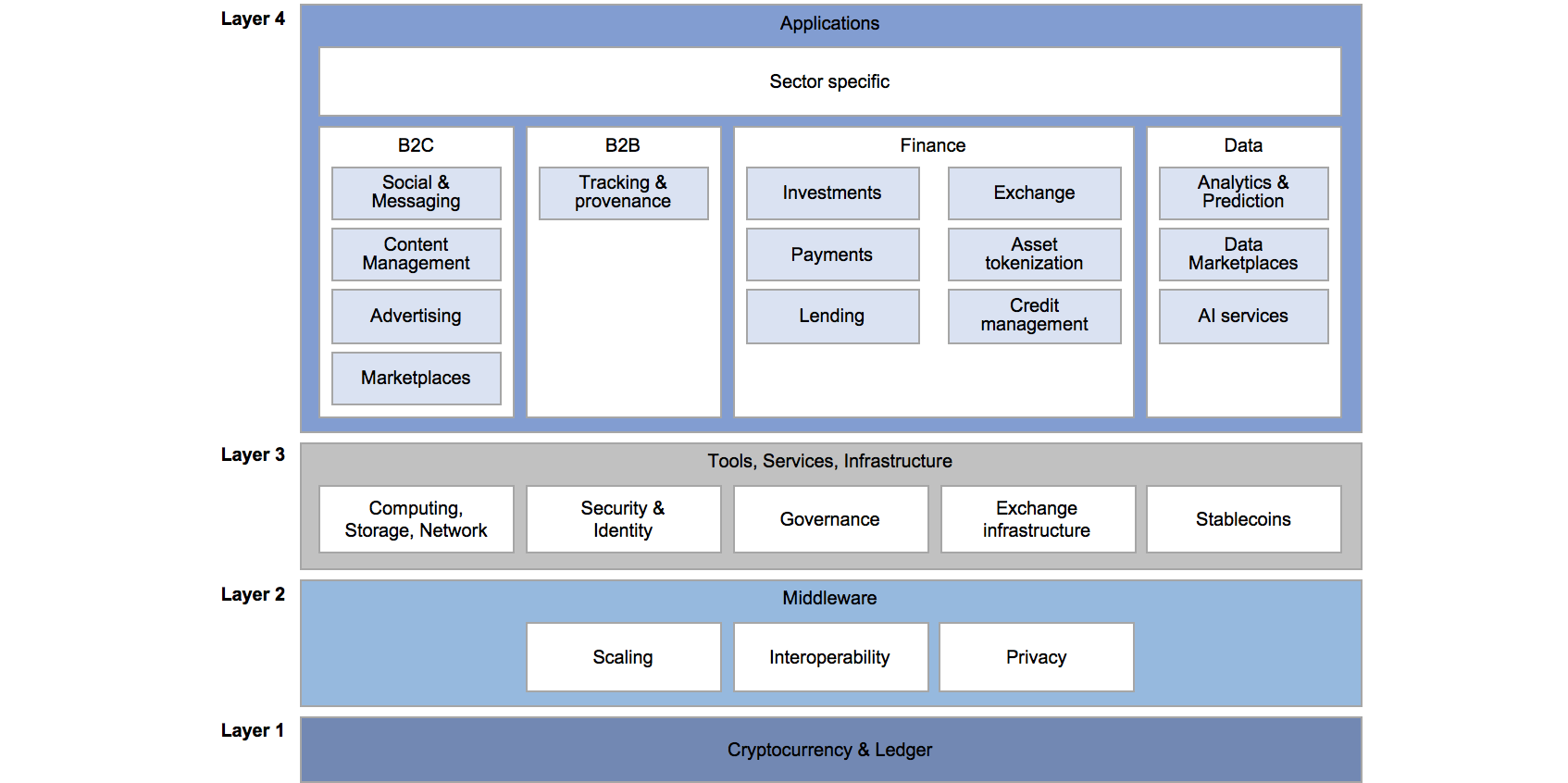
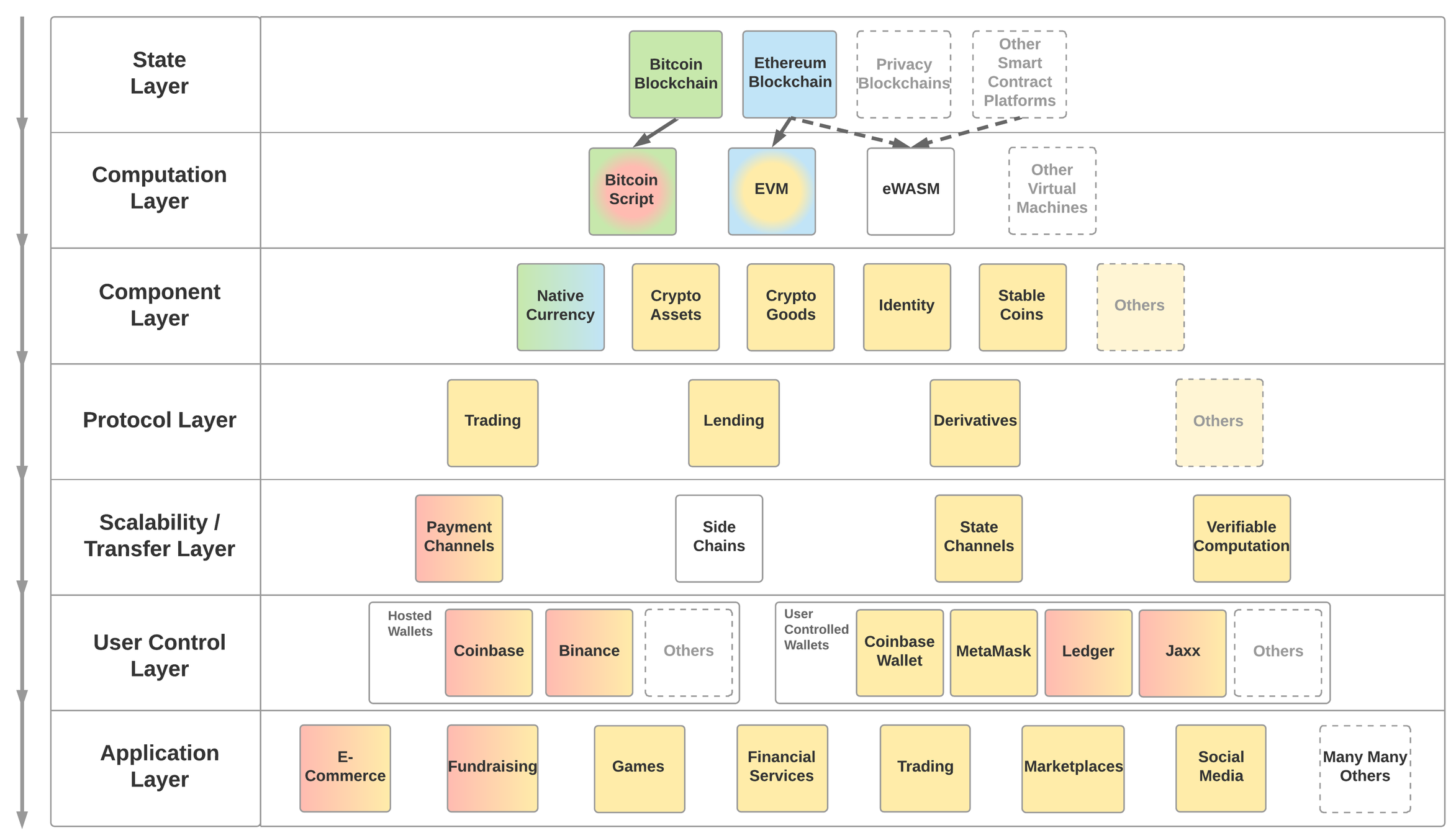
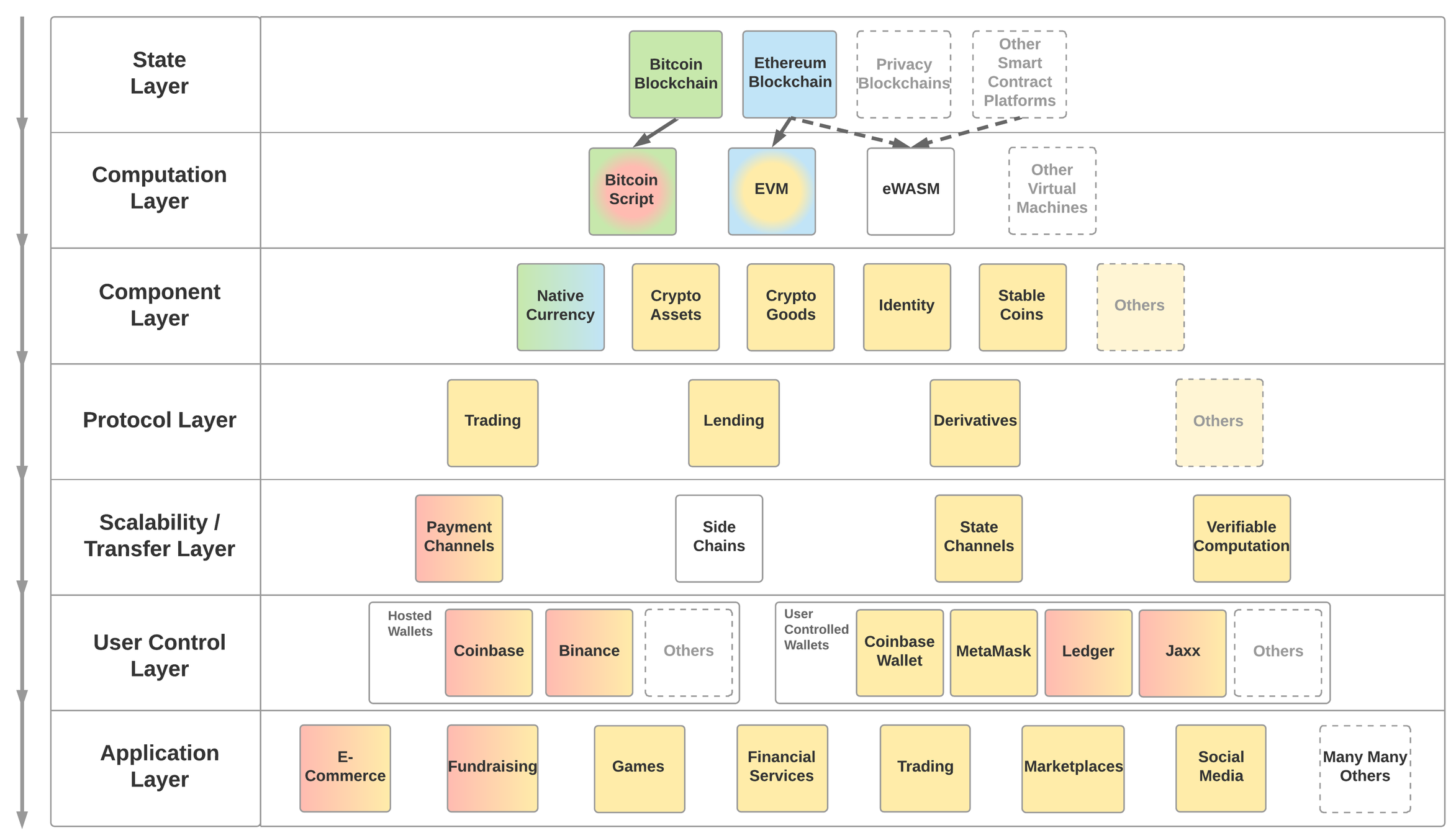
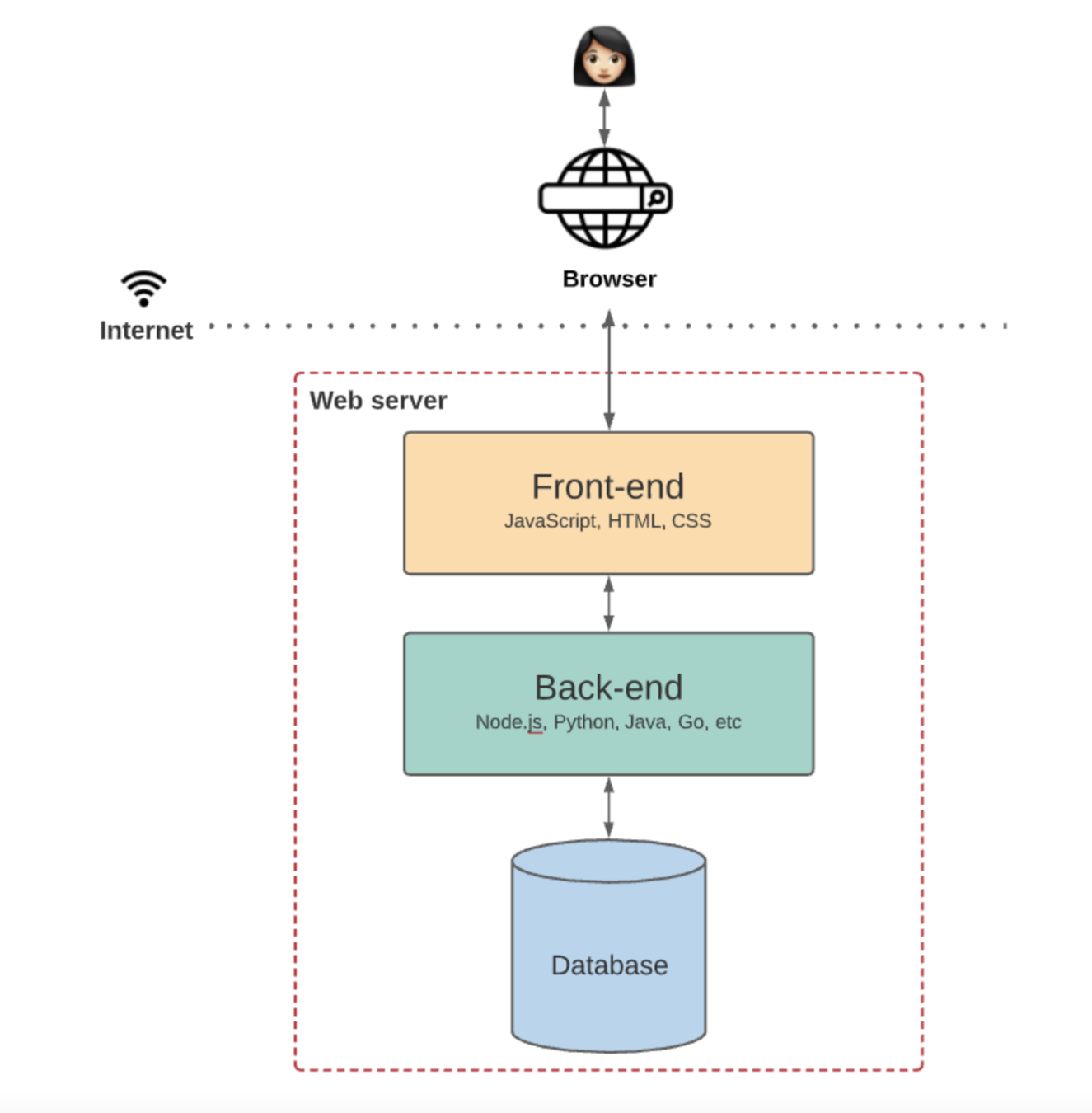
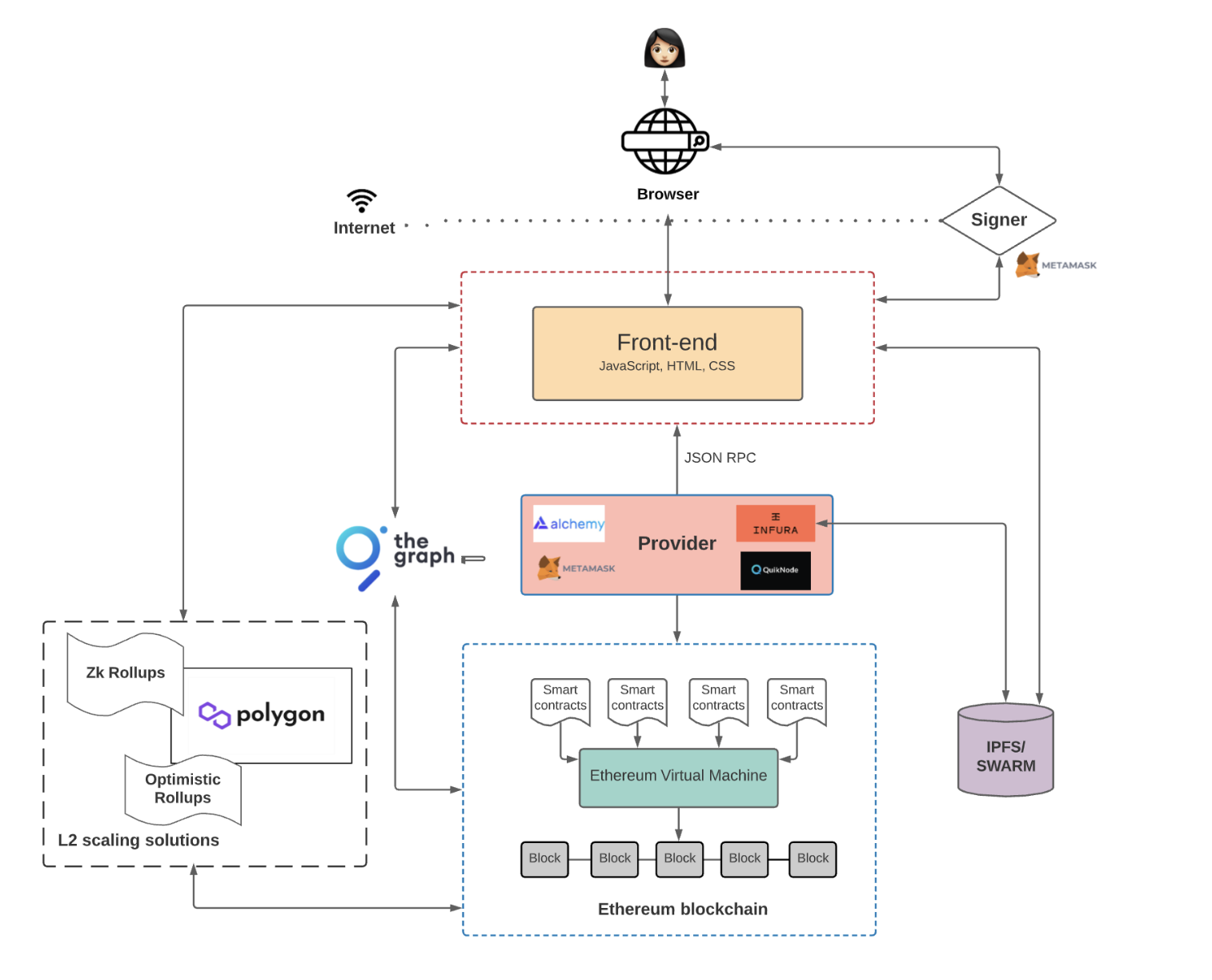
Web 3.0 Stack

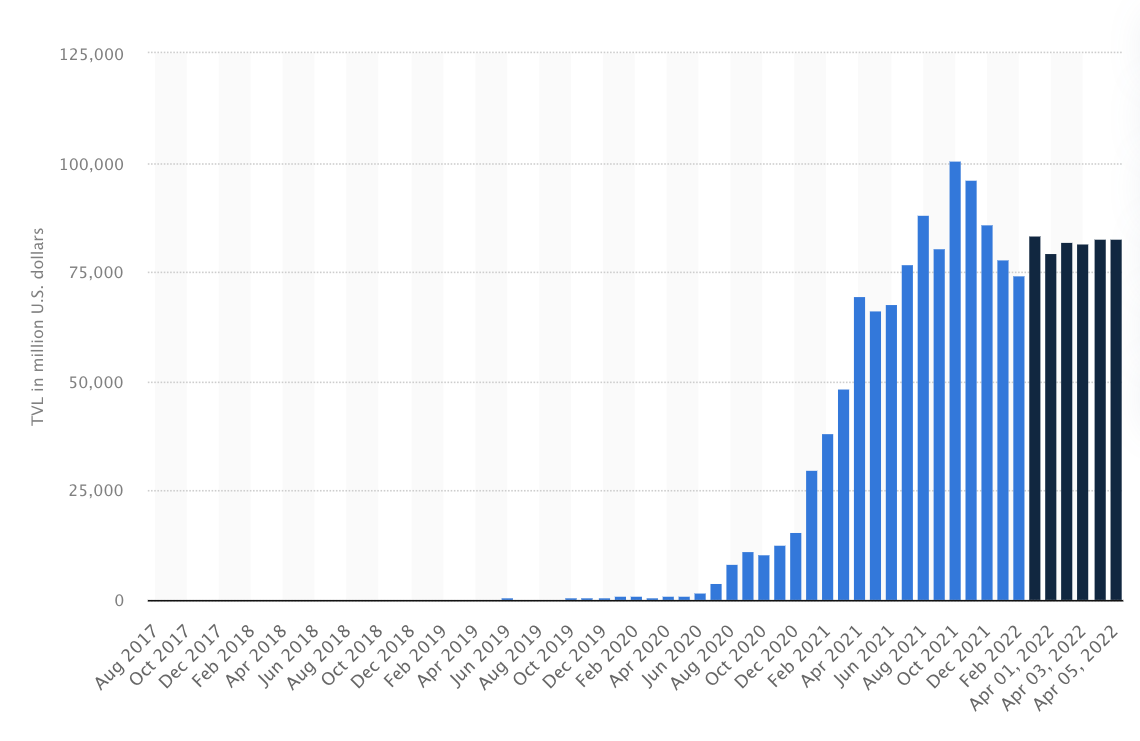
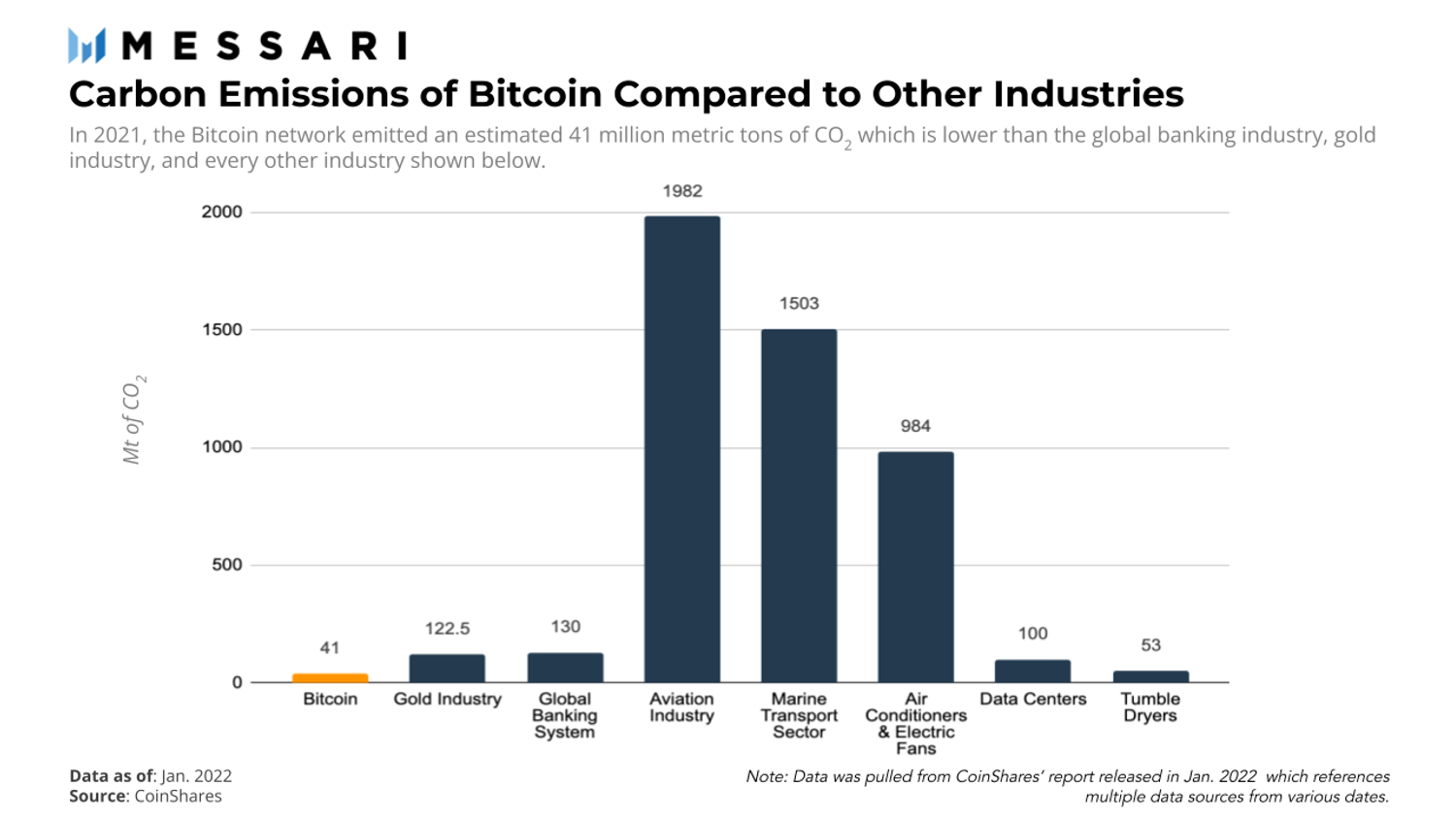
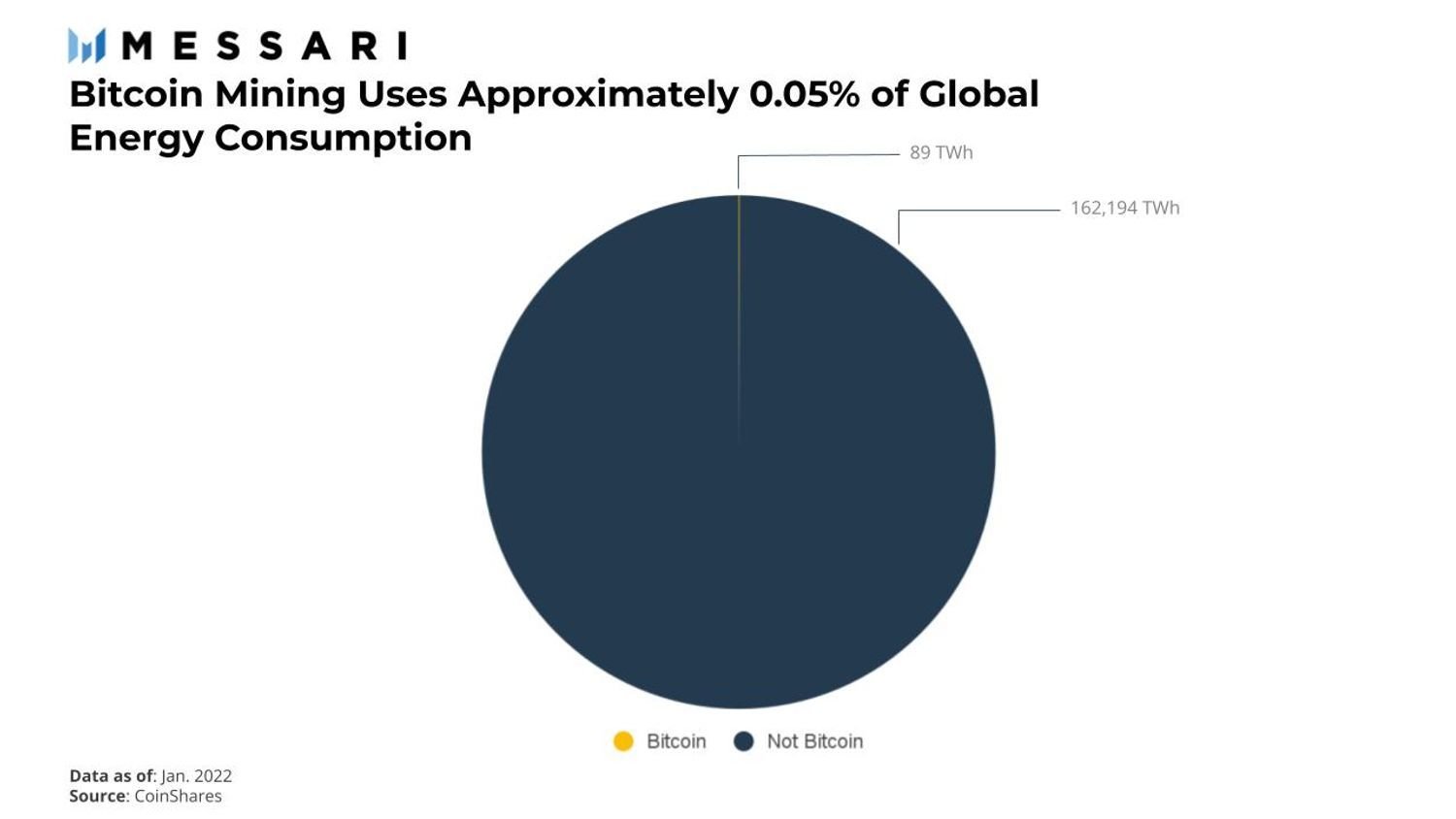
Total Value Locked in DeFi on the Ethereum Blockchain from August 2017 to April 2022
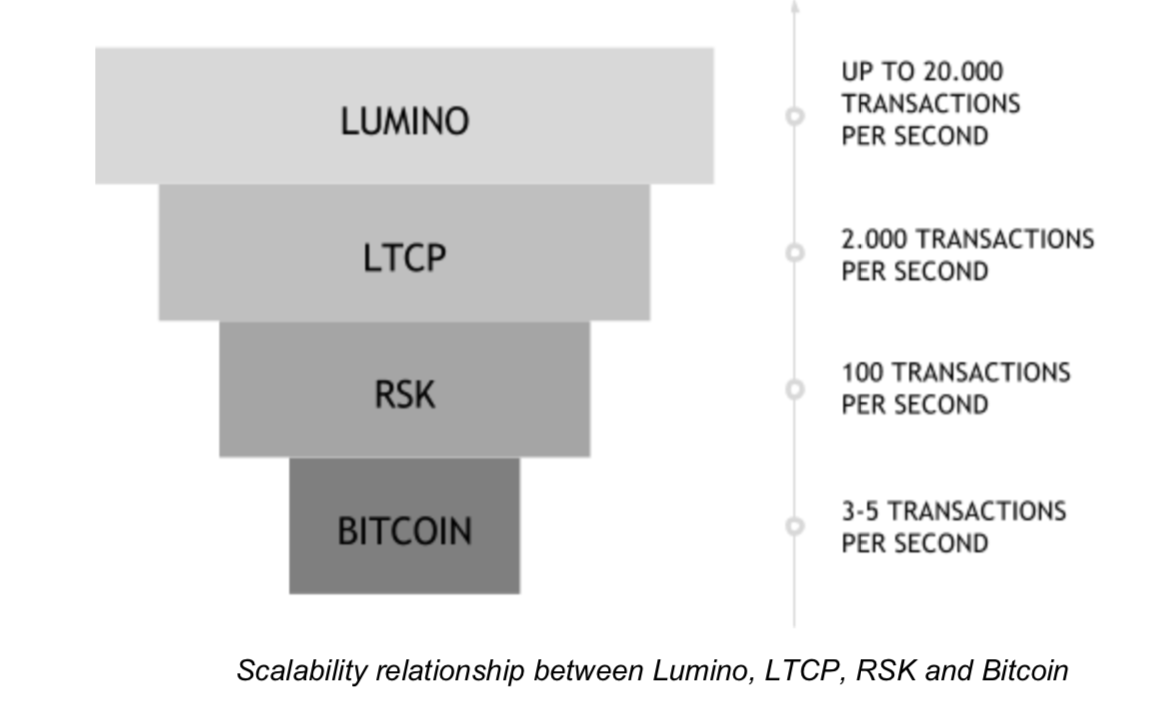
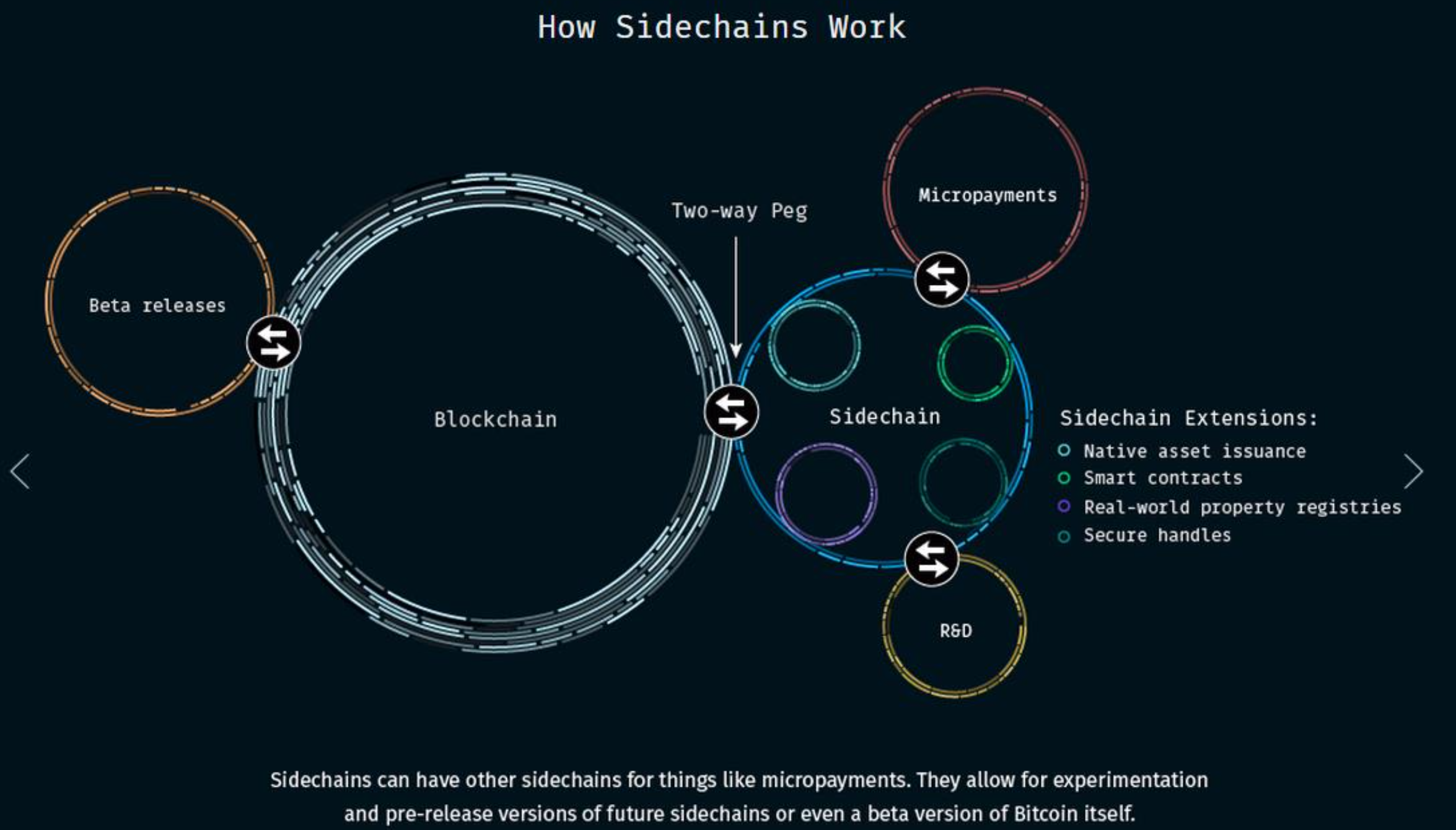
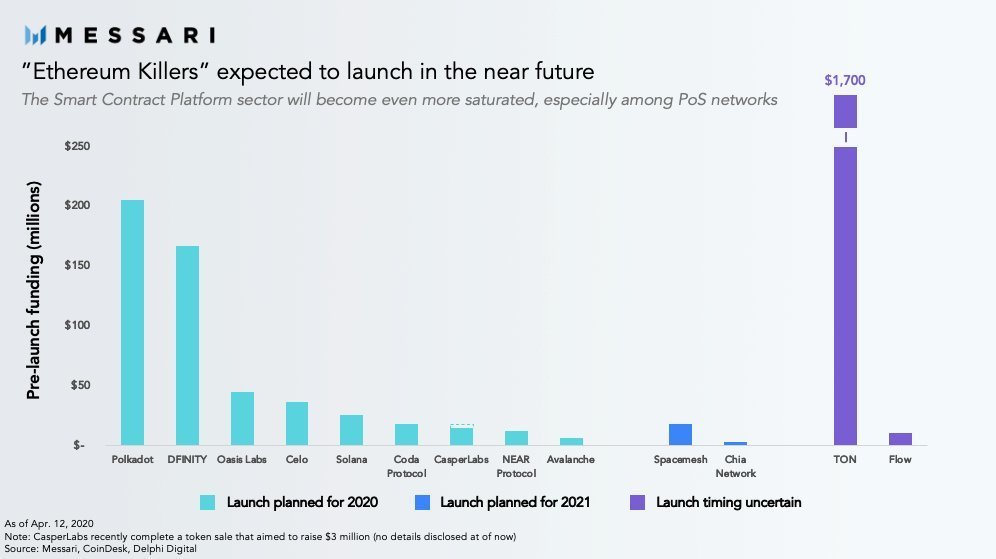
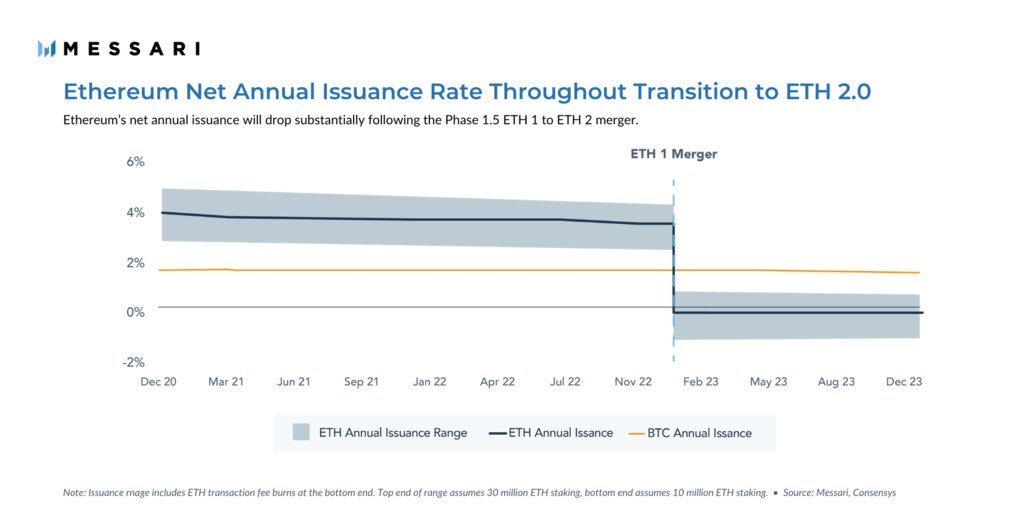
Future
-
Ethereum Transition to PoS
-
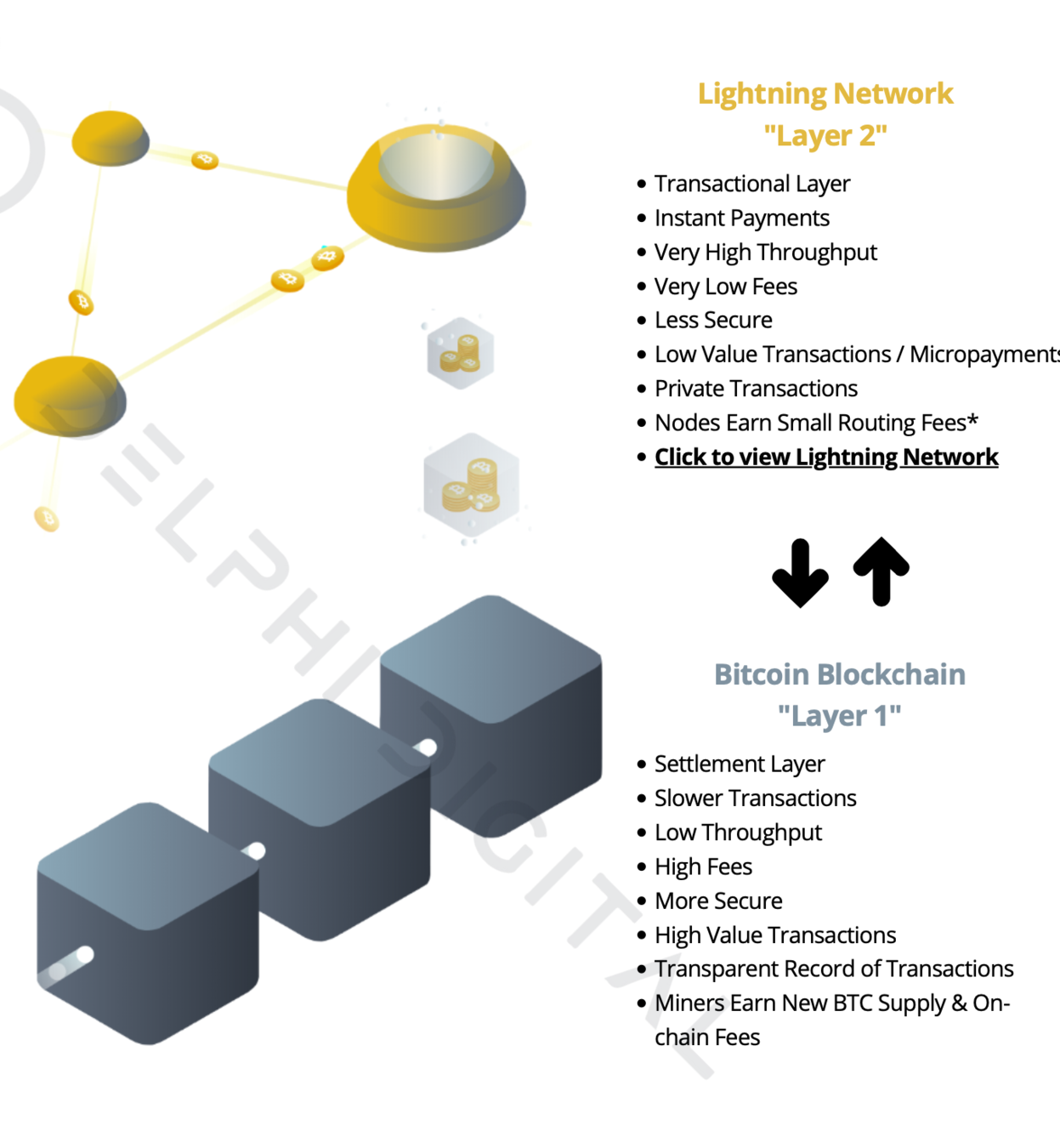
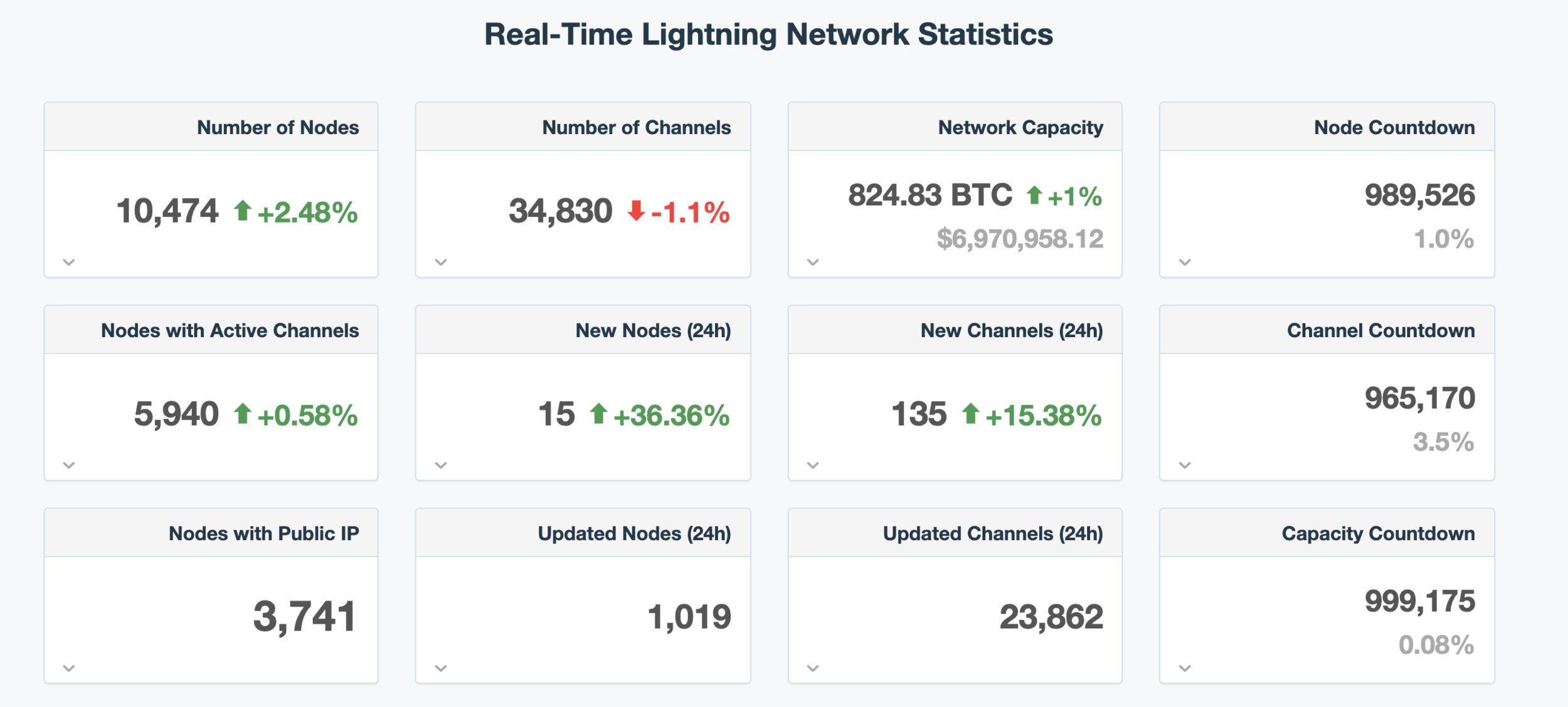
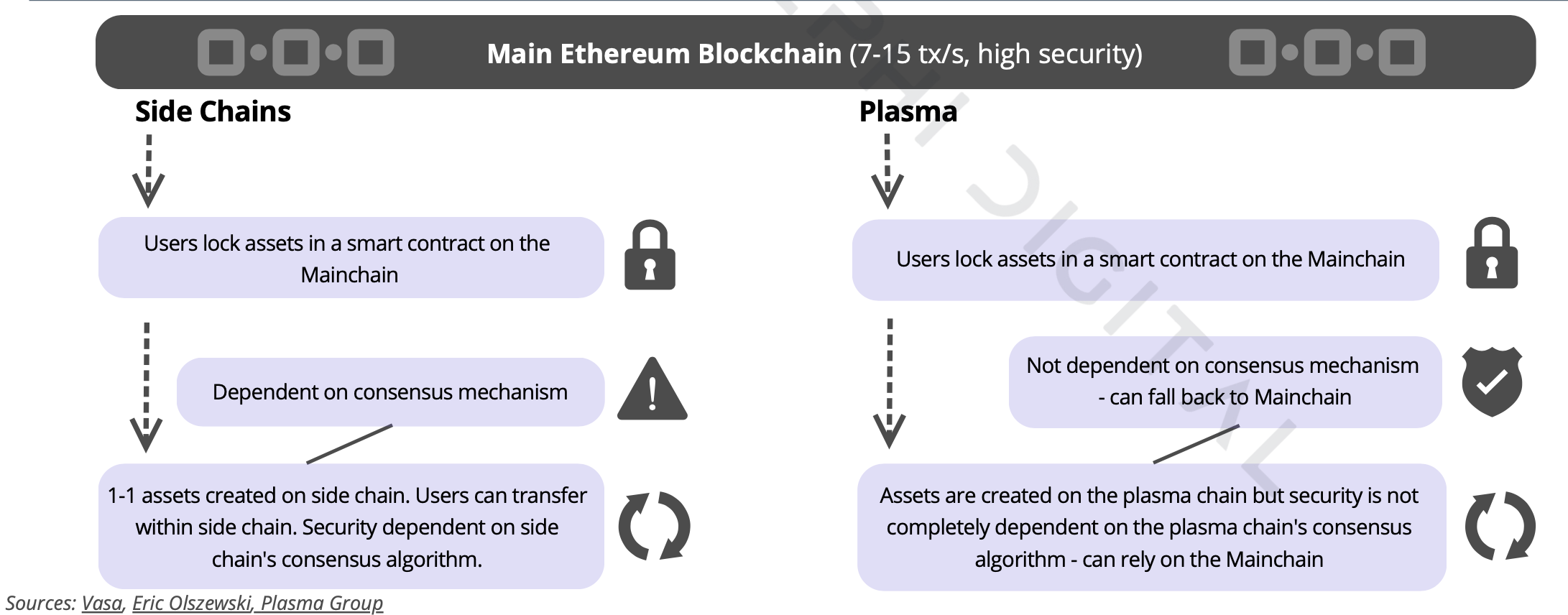
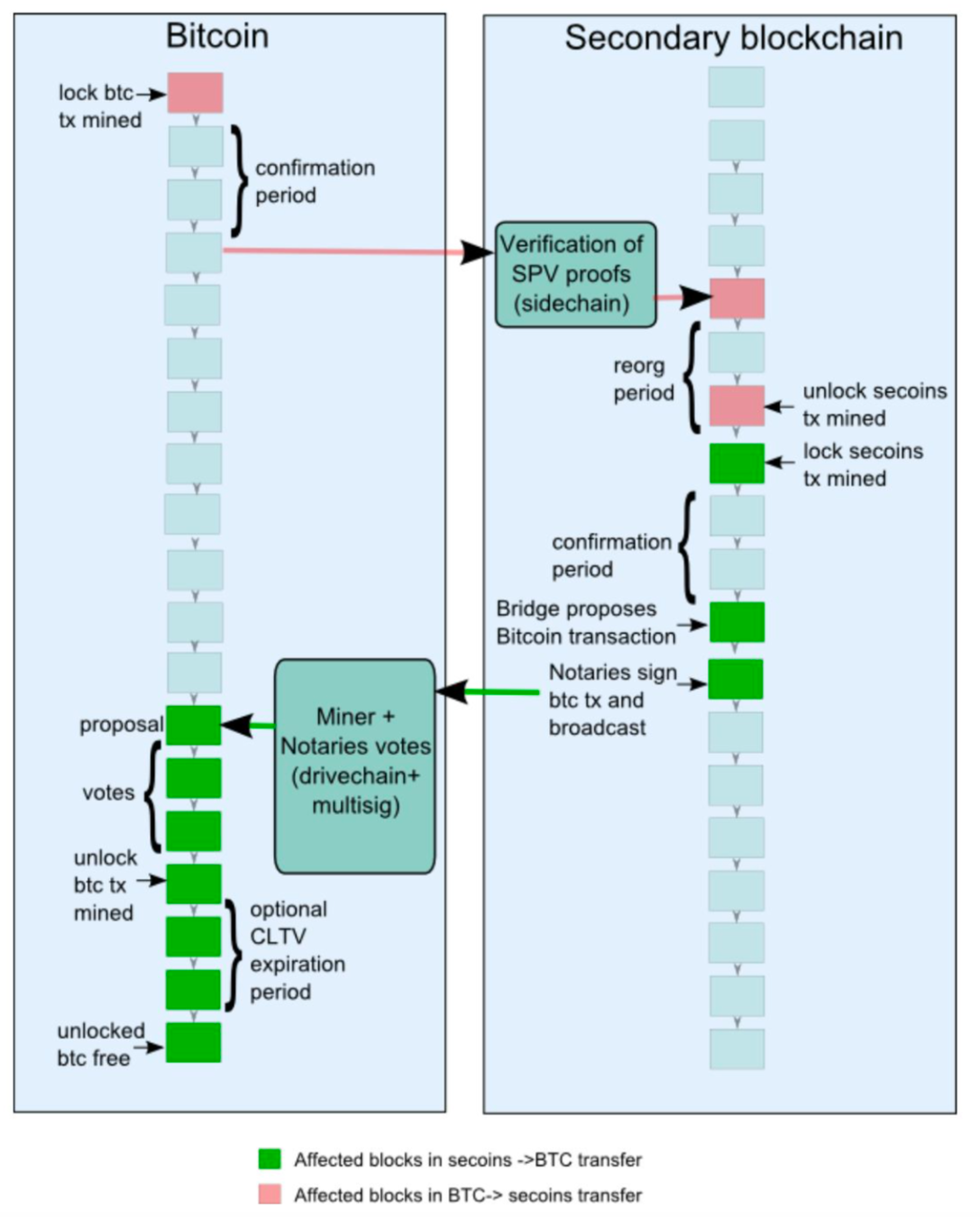
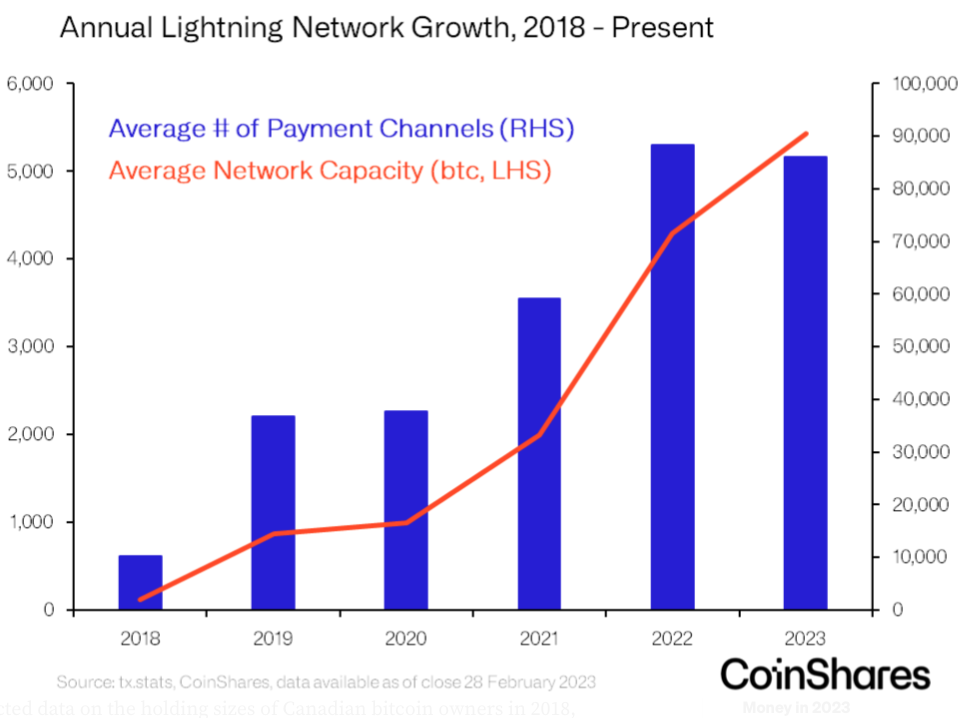
Bitcoin - Lightning Network a RSK
-
Full Fledge Decentralized Finance Ecosystem
-
Prediction Markets (Augur, Gnosis)
-
Tokenization of Assets
-
Interoperability (Polkadot, Avalanche, Cosmos)
-
Oracles (Chainlink, Band Protocol)
- Blockchain & VR/IoT (Virtual Economies) --> Metaverse
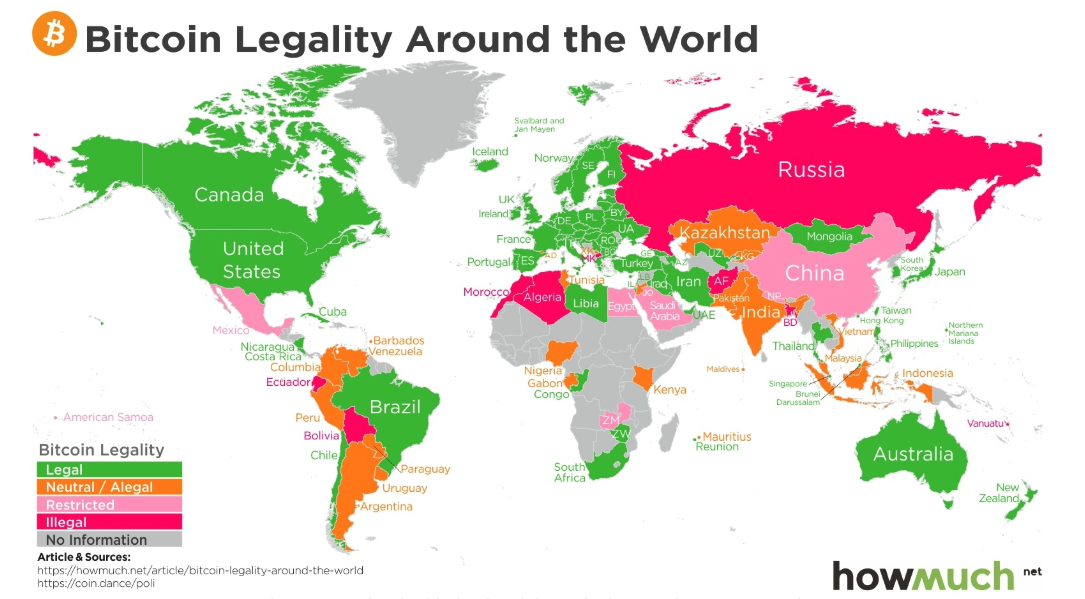
Výzvy:
- Legislatívne:
- Status kryptomien
- Daňové regulácie
- Status tokenov a spôsob ICO
- MiCA
- Technické:
- Škálovateľnosť
- Bezpečnosť
- Užívateľské prostredie
- Tax/ Legal Treatment of Stocks vs Crypto stocks?
- Who is responsible for the undesired app behaviour?
- Is it really immutable?
- Using DeFi via UI vs. Raw transactions ––> no signed disclaimer ––> different legal implications?
- KYC / AML ?
-
Real-World Assets as Crypto Loan Collateral
- MiCA - NFT and DeFi Out of Scope
Challenges in DeFi

Otázky?
Resources:
- Bank of England - Cryptoassets Taskforce:https://assets.publishing.service.gov.uk/government/uploads/system/uploads/attachment_data/file/752070/cryptoassets_taskforce_final_report_final_web.pdf
- Uni of Cambridge - Global Cryptocurrency Benchmarking Study:https://www.jbs.cam.ac.uk/fileadmin/user_upload/research/centres/alternative-finance/downloads/2017-global-cryptocurrency-benchmarking-study.pdf
- R3 - Blockchain in Trade Finance:
https://www.r3.com/wp-content/uploads/2018/07/Can-Blockchain-Make-Trade-Finance-More-Inclusive-1.pdf - Blockchain Progress Report:
https://blogs.cfainstitute.org/investor/2018/08/02/blockchain-a-progress-report/ -
My freely available book on the history and evolution of crypto:
https://coinstory.tech/
Ďakujem!
stanceldavid.sk
My Book & Newsletter: