PG6300-14
Webutvikling og API-design
06: CORS & Hello, security
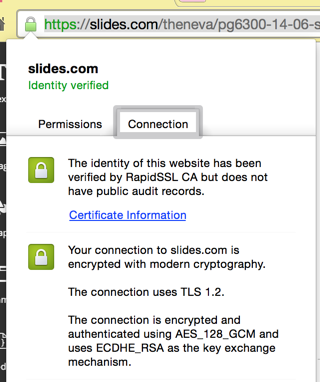
HTTPS
HTTP over Transport Layer Security
a.k.a.
HTTP Secure


2
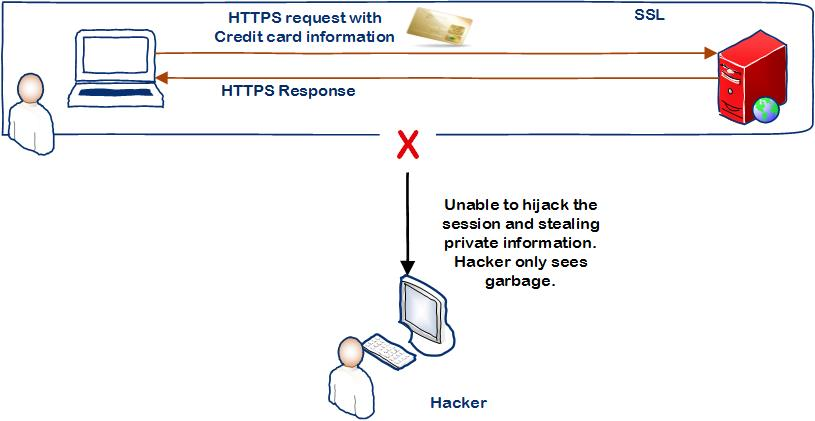
WITH TLS
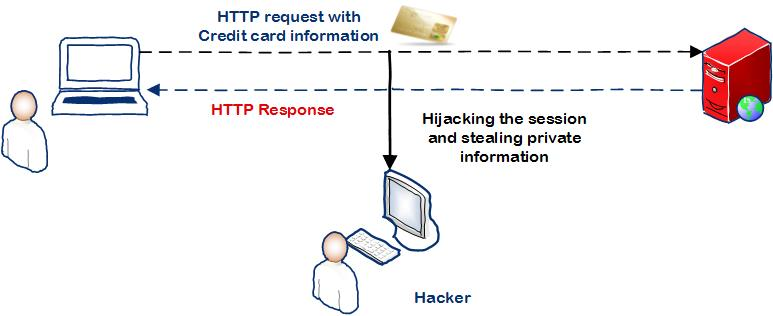
NO TLS
+ verification (signed)
CORS
Cross-Origin Resource Sharing
Browser forutsetter samme domene for JS-data
... eller eksplisitte headers (ugh)
Access-Control-Allow-Origin: http://origin.fooLøses på serversiden
app.use(require('cors')());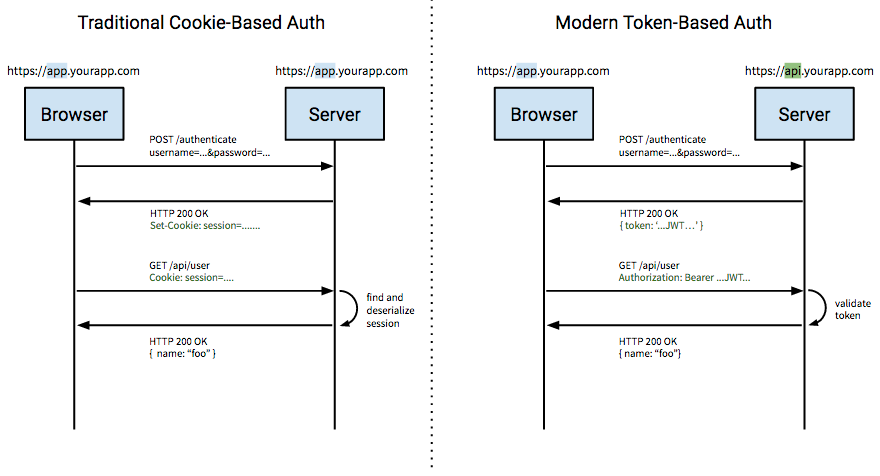
Cookies & tokens
Cookies
Leker ikke fint med CORS
(må settes opp på klientside også)
Ikke bra for non-browser apps
Tokens
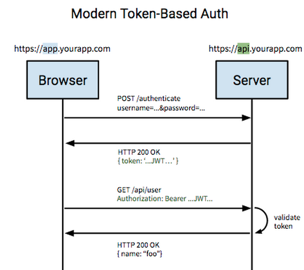
Produserer og sender et token
Identifiserer klient med token
Token kan signeres (TK2100)
Kan lagre informasjon(?)
+ LocalStorage
Clever authentication!
JSON Web Token (JWT)
(uttales "jot")
Signert token med payload
Signert med en 'secret' string
Raskere enn session store (dekodes med algoritme, ikke DB-oppslag)
Ikke kryptert – bare signert
JWT under the hood
eyJ0eXAiOiJKV1QiLCJhbGciOiJIUzI1NiJ9.eyJ1c2VybmFtZSI6InZhbGlkVXNlcm5hbWUifQ.N5ppD4k72pbST4_DESbHzqjrFCZK4QEzhGHI0H49GtM
header: { "typ": "JWT", "alg": "HS256" }
payload: { "username": "validUsername" }
<signature>
signature = HMACSHA256(
base64UrlEncode(header) + "." +
base64UrlEncode(payload) +
<secret>)
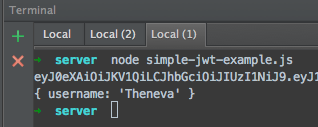
JWT med Node.js
var jwt = require('jwt-simple');
var jwtSecret = 'some secret';
var signedToken = jwt.encode({username: 'Theneva'}, jwtSecret);
console.log(signedToken);
var payload = jwt.decode(signedToken, jwtSecret);
console.log(payload);jwt-simple
JWT i Express: for "real"
var app = require('express')();
var jwt = require('jwt-simple');
app.post('/sessions', function(req, res) {
// get and validate login info
if (invalid) {
// respond with 401 unauthorized
} else {
// encode jwt with payload & sign with secret
// return the jwt
}
});
app.get('/user', function(req, res) {
// verify & decode jwt
// get jwt payload username
// retrieve user by username from DB
// return user info
});
Example
JWT med Angular
var app = angular.module('jwtExample', []);
var api = 'http://localhost:1234';
app.controller('MainController', function ($scope, $http, UserService) {
UserService.login('validUsername', 'matchingPassword')
.then(function (response) {
$scope.user = response.data;
});
});
app.service('UserService', function ($http) {
var service = this;
service.login = function (username, password) {
return $http.post(api + '/sessions', {username: username, password: password})
.then(function (response) {
var jwt = response.data;
$http.defaults.headers.common['Authorization'] = jwt;
return service.getUser();
});
};
service.getUser = function () {
return $http.get(api + '/user');
};
});bcrypt
var bcrypt = require('bcrypt');
var password = 'ananas';
var passwordHash = bcrypt.hashSync(password, 10);
console.log(password + ' -> ' + passwordHash);
var isMatch = bcrypt.compareSync(password, passwordHash);
console.log(isMatch);
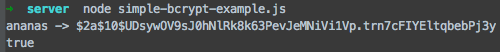
Passord i plaintext?
Kryptert?
NOPE