Trust is Risk
A decentralized financial trust platform
Orfeas Stefanos Thyfronitis Litos
Dionysis Zindros
Financial Cryptography 2017
Motivation
- Decentralized marketplaces, e.g. OpenBazaar:
- Anonymous purchases (can't call the cops!)
-
Can't just have simple stars + ratings!
-
Adversary can create 1,000,000 accounts (Sybil)
-
...and 1,000,000 fake "good transactions"
-
Adversary can create 1,000,000 accounts (Sybil)
-
Can we build it without fees?
-
We need decentralized reputation
An example purchase


Buyer - Dave
Vendor - Carol


Bob wants to buy sneakers from Alice
But who sends first?
Can't just use escrow: How to trust escrow?
A new type of wallet
You trust your money to your friends
You risk 60m฿ in exchange for being part of the network.

Bob: 24m฿
Charlie: 36m฿
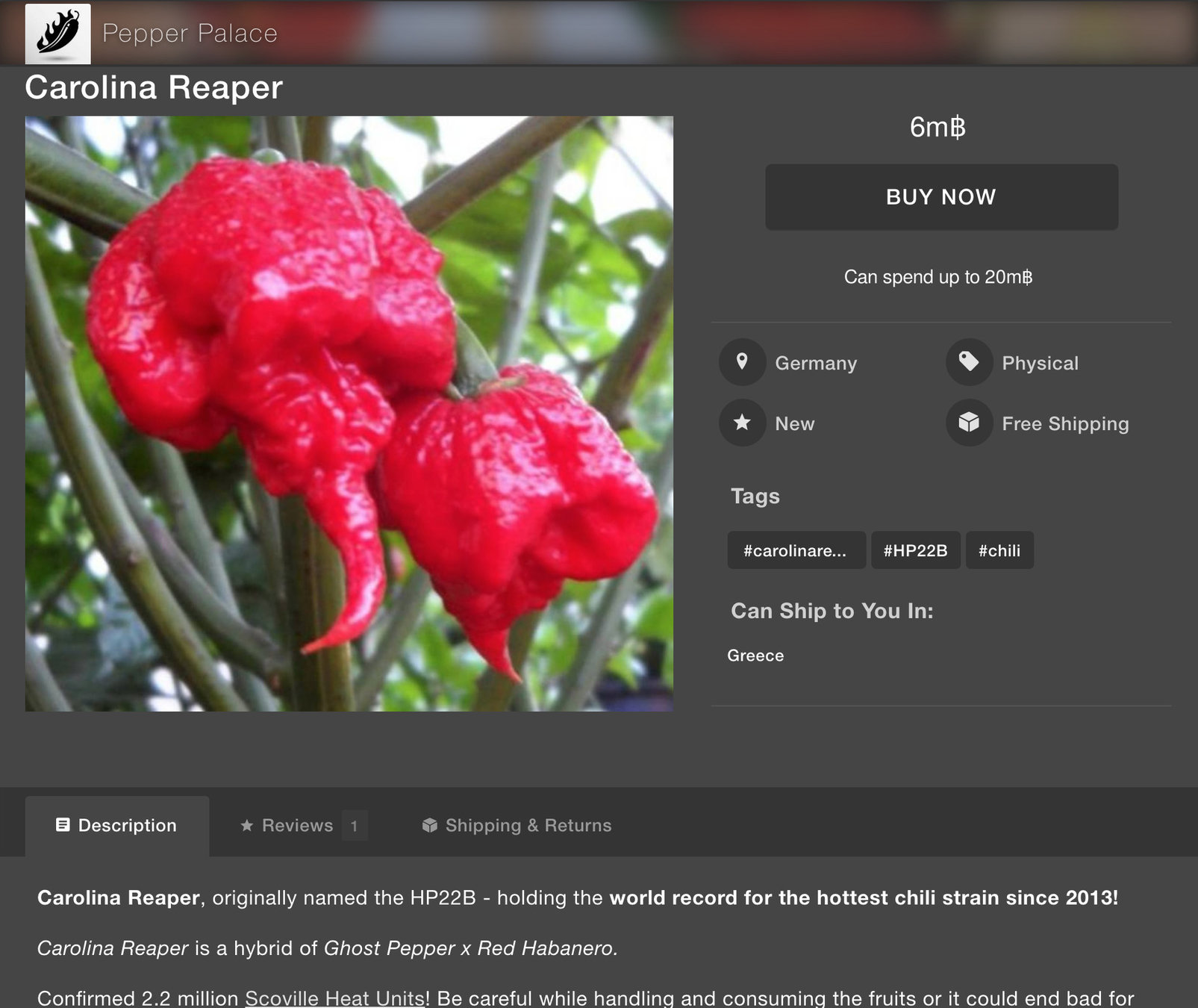
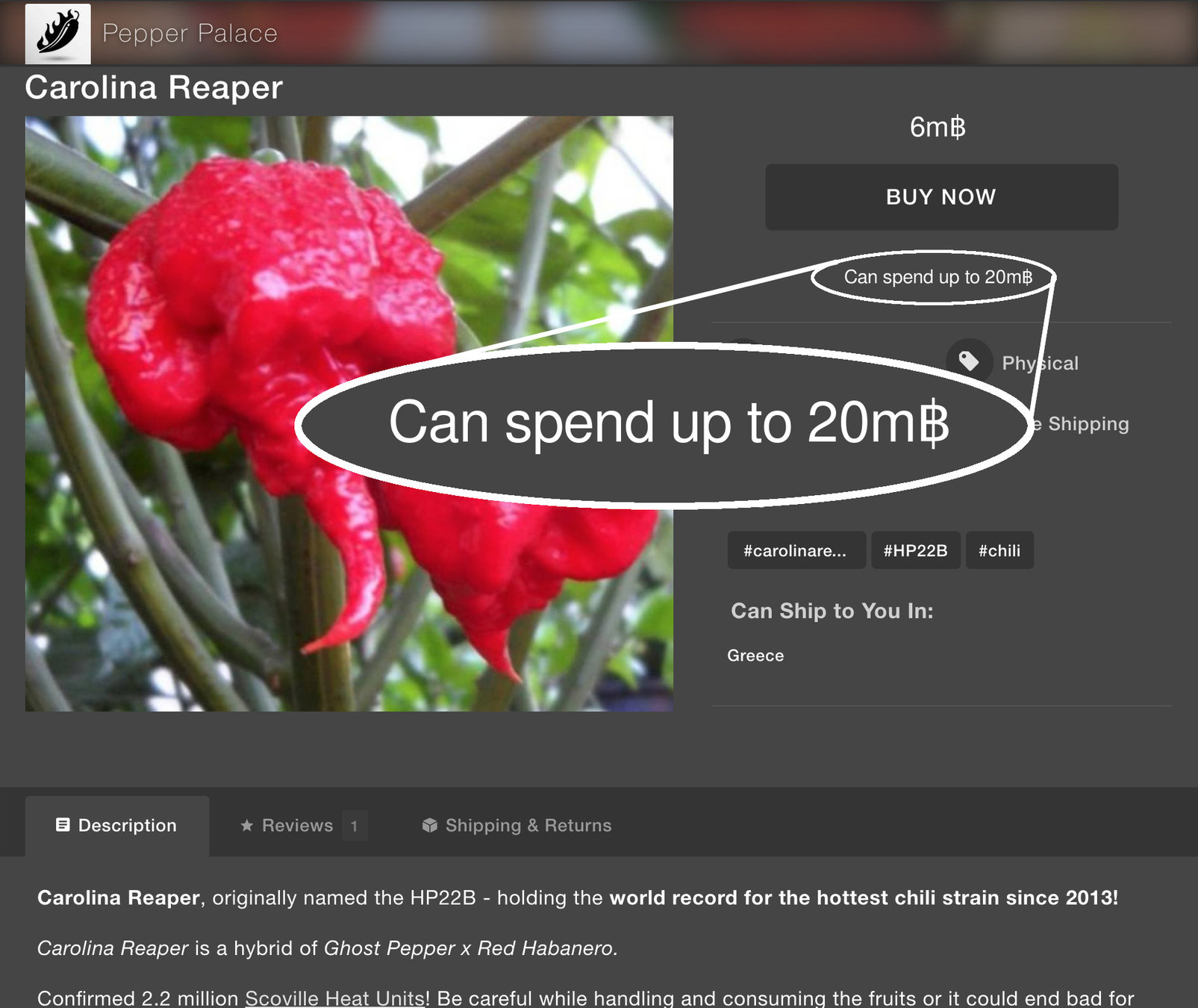

Bob: 22m฿
Vendor: 6m฿
Charlie: 32m฿
Funds are redistributed
Your wallet decides how
1-of-2 Multisig
-
How does Alice trust Bob & Charlie?
-
Puts her money in 1-of-2 multisigs
-
1 / {Alice, Bob}
-
1 / {Alice, Charlie}
-
Example:
Alice trusts Bob with 5m฿. Both Alice & Bob can spend.
Bitcoin graph
Trust Is Risk graph
Alice trusts Bob will not steal 5m฿ from her.
1-of-2 multisig


Trust graph
- Player = node
- Direct trust (1-of-2 multisig) = directed edge
- Weighted & directed graph

Desired properties
-
Risk Invariance
- Risk exposure to vendor does not increase beyond exposure to friends
-
Sybil Resilience
Our model
- Players play one after the other (e.g. round-robin)
- An honest player can:
- Directly entrust coins to friends
- Reclaim previously entrusted coins
- A malicious player additionally can
- Take coins entrusted by others
Turn Example








Indirect Trust intuition
- Alice and Bob are strangers.
- What's the worst that can happen to Alice if Bob is Evil?
- He steals all his incoming direct trust.
- Other players try to minimize losses.
Indirect Trust definition
is the maximum loss Alice can suffer if:
- Bob steals all incoming direct trust and exits the game. (Evil)
- Other players try to make up for their loss. (Conservative)
We call this a Transitive Game.
Trust flow theorem
Treat Direct Trusts as graph capacities.
Proof intuition:
- Every maximum flow corresponds to a Transitive Game with actions replaced by flows
- Every Transitive Game is made up solely of actions that also constitute a valid flow
The Transaction Problem
Client
Vendor
1฿
฿

How to pay the vendor?
...
2฿
...

Trust graph before payment:
฿
Risk exposure before payment: 2฿
How to pay the vendor?
...
2฿
...
Naive idea: just pay the vendor

฿
Risk exposure increased!
How to pay the vendor?
...
1฿
...

Safe idea: redistribute direct trust
฿
Risk exposure decreased!
How to pay the vendor?
...
1฿
...
Now we can safely pay
฿
Risk remained invariant

Risk Invariance theorem
- Alice was trusting her friends willingly
- Alice reduces trust to friends
- She uses that money to pay Vendor
Risk exposure of Alice to Vendor before
=
Risk exposure of Alice to Vendor after
Sybil Attack
Collusion = Corrupted Set ∪ Sybil Set
Corrupted Set: Originally trustworthy players, now compromised by Eve. Honest players may directly trust them.
Sybil Set: Players fabricated by Eve. No honest players directly trust them.
Collusion

Sybil Resilience
Proof intuition:
MaxFlow cannot be increased by adding nodes without incoming direct trusts.
Collusion

It's pointless for an attacker to create multiple accounts!
Thank you!
Questions?
https://github.com/decrypto-org/TrustIsRisk
https://github.com/decrypto-org/TrustIsRisk.js
45DC 00AE FDDF 5D5C B988 EC86 2DA4 50F3 AFB0 46C7
<dionyziz@gmail.com>
FB61 4CCD 94E1 9201 D144 8D5A 9481 00FD BA28 707E
<orfeas.litos@hotmail.com>
fc17
By orfeas
fc17
- 3,513



