by Stepan Suvorov
Stepan Suvorov

-
CTO @
-
Google Developer Expert
-
🇺🇦 originally from Ukraine
-
GenAI Evangelist


Christiaan Brand
Security & Identity, Google

Thanks to

Maud Nalpas
Web security & privacy, Google
Agenda
- The Evolution of Authentication
- What's wrong with Passwords?
- Passkeys
- how it works
- for personal use
- for your business
- implementation details & Demo
Auth Evolution
Something you know

Something you have
Something you are
Somewhere you are
Passwords
Why passwords are bad?
- High risk of Identity theft and phishing
- Easily revealed to 3rd Party (accidentally or not)
- Easily hacked using hash matching tables
- Sharing as plain text
- The strength of the password is not always verified automatically
*HYPR, 2022 State of Passwordless Security Report – Download the Report here.

Password managers?

LastPass Story briefly
- Common Database backup storage
- The database contained MFA data
- Database was encrypted
- Keys to decrypt were also stolen


hardware keys?
Passkeys
History
-
2012: The FIDO (Fast IDentity Online) Alliance was founded.
-
2016: The FIDO Alliance releases the FIDO U2F (Universal 2nd Factor) standard. This standard allows users to utilize their smartphones or other devices as a second factor for authentication on websites.
-
2017: Building on the previous standard, the FIDO Alliance introduces FIDO2. This standard includes the WebAuthn (Web Authentication) specification and is designed to support a broader array of authentication methods, including what would eventually be known as passkeys.
-
2022: Apple announces support for passkeys in iOS 16 and macOS Ventura. Similarly, Google revealed that it will support passkeys in Android 13 and Chrome.
-
2023: Microsoft joins the movement, announcing passkey support in Windows 11. Google extends its commitment by incorporating passkeys into its login services.
-
2024: passkeys will become the dominant method of authentication on the web
How Passkeys Work?
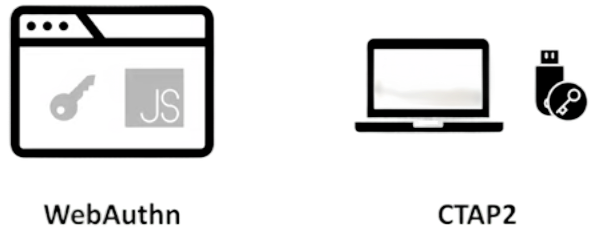
FIDO2 Components
How Passkeys Work?
Sign-up



Public 🔑
Private 🔑
CTAP
WebAuthn
How Passkeys Work?
Sign in



Public 🔑
Private 🔑
Public 🔑
challenge
signed package with challenge
Also good to know

Syncing
Passkeys are not stored on a single device
Cross-device
Passkeys on one device can be used on a different device
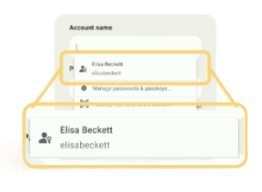
Discoverable
Passkeys contain metadata that allows your system to present passkey to you
Passkeys
for personal use
Can I Use it?



















keep secrets at Google/Apple?
Privacy considerations
- biometric material never leaves the user's device
- Passkey protocols are carefully designed so that no information shared with sites can be used as a tracking vector.
- Passkey managers protect passkeys from unauthorized access and use.
User Journey








Passkeys for your business
Benefits
- increases login success rates
- conversion rates
- reduced 2FA implementation costs
- security: strong protection against:
- phishing
- data breach

https://www.shopify.com/blog/ecommerce-payment-authentication
How difficult to implement?
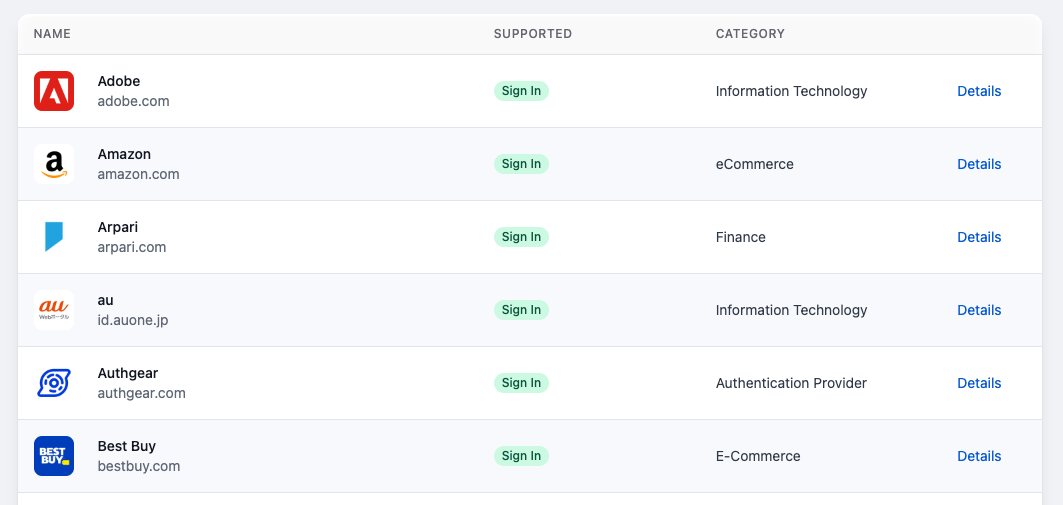
Ready to use services
- Dashlane
- 1Password Passage
- Auth0
- StrongKey (OpenSource)
- LastPass (in progress)
- YubiOn
How difficult for your clients to migrate?
More about implementation
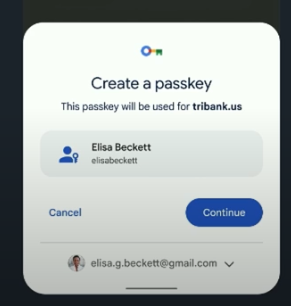
Passkey Creation
const publicKeyCredentialCreationOptions = {
challenge: new ArrayBuffer([219]),
rp: {
name: "Slides",
id: "slides.com",
},
user: {
id: new ArrayBuffer([137]),
name: "elisabeckett",
displayName: "Elisa Beckett",
},
pubKeyCredParams: [{alg: -7, type: "public-key"}],
authenticatorSelection: {
authenticatorAttachment: "platform",
requireResidentKey: true,
},
timeout: 30000
};
const credential = await navigator.credentials.create({
publicKey: publicKeyCredentialCreationOptions
});
Use a Passkey
// Availability of 'window.PublicKeyCredential' means WebAuthn is usable.
if (window.PublicKeyCredential &&
PublicKeyCredential.isConditionalMediationAvailable) {
// Check if conditional mediation is available.
const isCMA = await PublicKeyCredential.isConditionalMediationAvailable();
if (isCMA) {
// Call WebAuthn authentication
}
}
const publicKeyCredentialRequestOptions = {
// Server generated challenge
challenge: new ArrayBuffer([219]),
// The same RP ID as used during registration
rpId: 'slides.com',
};
const credential = await navigator.credentials.get({
publicKey: publicKeyCredentialRequestOptions,
// Specify 'conditional' to activate conditional UI
mediation: 'conditional'
});
Demo Time
passkeys-demo.appspot.com

Conclusion
-
Passkeys are here
- They are a significant UX improvement over passwords
- They provide much better security guarantees (strong phishing resistance)
-
It might take time for regulation to catch up
-
Passkeys are new: It’ll take users some time to become accustomed
- Understanding when passkeys are synced, and when they’re not, is hard
-
Your plan
-
Next week you should:
- Identify core applications in your organization that could benefit from passkey deployment
-
In the first three months following this presentation, you should:
- Decide on a passkey/FIDO server: build or buy
-
Within six months you should:
- Aim to have the passkey/FIDO server deployed
- Drive a passkey implementation project with your initial set of applications
Thank you for your attention.
Questions?
Passkeys: Prepare for the Future
By Stepan Suvorov
Passkeys: Prepare for the Future
- 169



