June 13-16, 2023
iRODS User Group Meeting 2023
Chapel Hill, NC
Advanced Training:
Auditing


Alan King, Senior Software Developer
Justin James, Senior Applications Engineer
iRODS Consortium
Getting Started

sudo apt-get -y install \
irods-externals-cmake3.21.4-0 \
irods-externals-clang13.0.0-0 \
irods-externals-qpid-proton0.36.0-1 \
irods-externals-fmt8.1.1-0 \
irods-dev
export PATH=/opt/irods-externals/cmake3.21.4-0/bin:$PATHInstall and configure build tools
curl -fsSL https://download.docker.com/linux/ubuntu/gpg | sudo apt-key add -
sudo add-apt-repository "deb [arch=amd64] https://download.docker.com/linux/ubuntu $(lsb_release -cs) stable"
sudo apt-get update
sudo apt-get install -y docker-ce
sudo usermod -aG docker ${USER}Install Docker
Setup Auditing Rule Engine Plugin

Clone the auditing REP repository and build packages:
cd git clone https://github.com/irods/irods_rule_engine_plugin_audit_amqp -b 4-3-0-stable mkdir build_audit cd build_audit cmake ../irods_rule_engine_plugin_audit_amqp make package sudo dpkg -i irods-rule-engine-plugin-audit-amqp_4.3.0.1-1~focal_amd64.deb
Setup Auditing Rule Engine Plugin

Edit /etc/irods/server_config.json
-
add a new stanza to the rule_engines array after irods_rule_engine_plugin-irods_rule_language-instance
-
add the audit namespace
"rule_engines": [
{
"instance_name": "irods_rule_engine_plugin-irods_rule_language-instance",
...
...
"shared_memory_instance": "irods_rule_language_rule_engine"
},
{
"instance_name": "irods_rule_engine_plugin-audit_amqp-instance",
"plugin_name": "irods_rule_engine_plugin-audit_amqp",
"plugin_specific_configuration" : {
"amqp_location" : "ANONYMOUS@localhost:5672",
"amqp_topic" : "audit_messages",
"pep_regex_to_match" : "audit_.*"
}
},
{
"instance_name": "irods_rule_engine_plugin-cpp_default_policy-instance",
...
...
"rule_engine_namespaces": [
"",
"audit_"
],
Setup Monitoring

Clone the irods/contrib repository and build the Docker image:
cd git clone https://github.com/irods/contrib cd ~/contrib/irods_audit_elk_stack DOCKER_BUILDKIT=1 docker build -t irods/irods_audit_elk_stack . docker run -dit -p 8080:15672 -p 5672:5672 -p 80:5601 -p 9200:9200 irods/irods_audit_elk_stack
Tracking What We've Done
- We installed the audit plugin which generates events for every dynamic policy enforcement point executed
- We started a docker container with the following software:
- RabbitMQ - message broker to catch events
- Not-Logstash - to read the events and write to DB
- Elasticsearch - database to store the events
- Kibana - visualization tool

Tracking What We've Done
- Visit http://<ip> where ip is the public IP for your VM
- Click on Analytics -> Dashboard

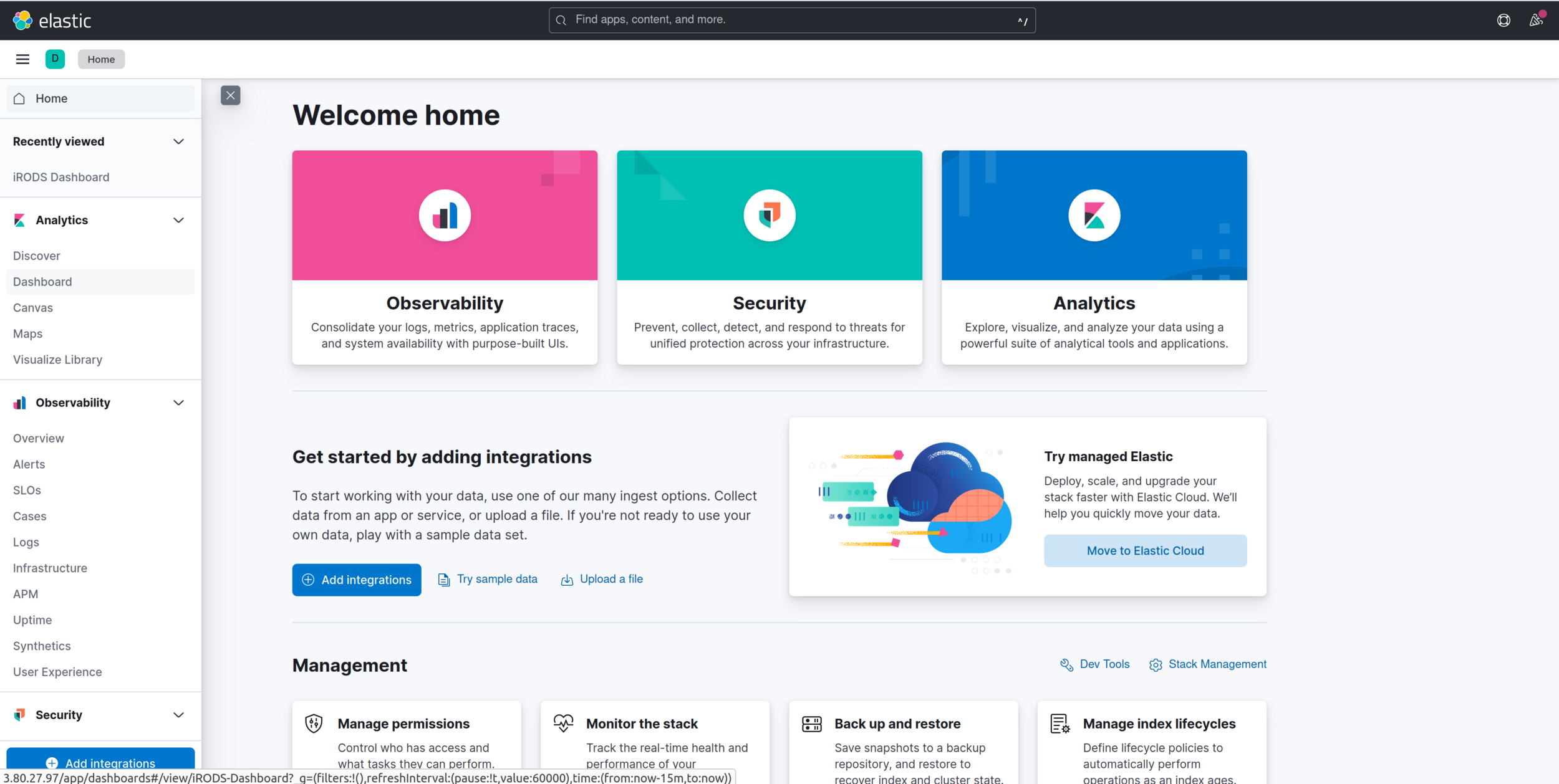
Tracking What We've Done
You have a visualization of what is happening in your iRODS zone.
You can see the bytes written and received, connections, top users, etc.
These are just a sample of what can be visualized.
All of the data is in the Elastic database and can be queried for additional interesting patterns or characteristics.

Tracking Origin of a File
Now let's say we want to track the origin (provenance) of some files in our system.
We have PEPs stored in our Elastic database that provide an audit trail for us.
Before we get started, let's install jq so that we can parse the JSON output of an elasticsearch query.
sudo apt-get -y install jq

Tracking Who Wrote to the File
curl -XGET 'localhost:9200/irods_audit/_search?pretty' -H 'Content-Type: application/json' -d'
{
"_source": [ "@timestamp", "user_user_name", "obj_path" ],
"sort" : [
{"@timestamp":{"order": "asc"}}
],
"size" :10000,
"query": {
"bool": {
"must": [
{ "match": { "rule_name": "audit_pep_api_data_obj_put_pre" } },
{ "match_phrase": { "obj_path": "tempZone/home/rods/stickers.jpg" } }
]
}
}
}' | jq ".hits.hits[] | ._source"Search for put activity on /tempZone/home/rods/stickers.jpg

Tracking Who Wrote to the File
This query returns the following five records showing the user rods put stickers.jpg five times:
{
"@timestamp": "2018-05-30T20:13:01.331Z",
"obj_path": "/tempZone/home/rods/stickers.jpg",
"user_user_name": "rods"
}
{
"@timestamp": "2018-05-30T21:02:59.350Z",
"obj_path": "/tempZone/home/rods/stickers.jpg",
"user_user_name": "rods"
}
{
"@timestamp": "2018-05-30T21:03:16.370Z",
"obj_path": "/tempZone/home/rods/stickers.jpg",
"user_user_name": "rods"
}
{
"@timestamp": "2018-05-30T21:03:31.671Z",
"obj_path": "/tempZone/home/rods/stickers.jpg",
"user_user_name": "rods"
}
{
"@timestamp": "2018-05-30T21:12:01.143Z",
"obj_path": "/tempZone/home/rods/stickers.jpg",
"user_user_name": "rods"
}

Tracking Read Access to the File
curl -XGET 'localhost:9200/irods_audit/_search?pretty' -H 'Content-Type: application/json' -d'
{
"_source": [ "@timestamp", "user_user_name", "obj_path" ],
"sort" : [
{"@timestamp":{"order": "asc"}}
],
"size" :10000,
"query": {
"bool": {
"must": [
{ "match": { "rule_name": "audit_pep_api_data_obj_get_pre" } },
{ "match_phrase": { "obj_path": "tempZone/home/rods/stickers.jpg" } }
]
}
}
}' | jq ".hits.hits[] | ._source"Search for read activity on /tempZone/home/rods/stickers.jpg

Look for all the "pre" PEPs
Search for all the "pre" PEPs that have been executed today, but exclude any authentication PEPs
curl -XGET 'localhost:9200/irods_audit/_search?pretty' -H 'Content-Type: application/json' -d' { "_source": [ "@timestamp", "rule_name" ], "sort" : [ {"@timestamp":{"order": "asc"}} ], "size" :10000, "query": { "bool": { "must" : { "regexp": {"rule_name": "audit_pep_api_.*_pre"} }, "must_not" : { "regexp": {"rule_name": "audit_pep_api_auth.*_pre"} } } } }' | jq ".hits.hits[] | ._source"

UGM 2023 - Auditing
By iRODS Consortium
UGM 2023 - Auditing
iRODS User Group Meeting 2023 - Advanced Training Module
- 631

