A journey into DevSecOps - Scanning your source code as part of your CI pipeline
Brian Sodano
@codemouse
Cybersecurity is the body of technologies, processes and practices designed to protect networks, computers, programs and data from attack, damage or unauthorized access.

The real threats

One of the most problematic elements of cybersecurity is the quickly and constantly evolving nature of security risks. The traditional approach has been to focus most resources on the most crucial system components and protect against the biggest known threats, which necessitated leaving some less important system components undefended and some less dangerous risks not protected against. Such an approach is insufficient in the current environment.



https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2017-5638
CVE-2017-5638
The Jakarta Multipart parser in Apache Struts 2 2.3.x before 2.3.32 and 2.5.x before 2.5.10.1 mishandles file upload, which allows remote attackers to execute arbitrary commands via a #cmd= string in a crafted Content-Type HTTP header, as exploited in the wild in March 2017.
PyPI Package Squatting
Fake packages (correct names in parenthesis):
acqusition (acquisition)
apidev-coop (apidev-coop_cms)
bzip (bz2file)
crypt (crypto)
django-server (django-server-guardian-api)
pwd (pwdhash)
setup-tools (setuptools)
telnet (telnetsrvlib)
urllib/urlib (urllib3)
request lib

Another way to look at this for anyone who got hit by this: your environment is fully exposed to the worse kind of DoS attack vector — operational incompetence.
I am being harsh here for a reason because you got lucky today and some of you still consider this to be someone else’s fault. This change caused your application to fail instead of leak data, lose money, or cause irreversible harm. What I hope you have learned today is that ANYONE with publish rights to ANY module you depends on, directly or indirectly, can shut down your entire environment. That is at best fucking ridiculous and at worst criminally negligent.
Think about what you are admitting to have created — an environment where hundreds (if not thousands) or people have the power, maliciously or innocently, to put you out of business (if only for a short period of time), without any accountability or recourse. Maybe open source isn’t for you.
- Eran Hammer
Blame Game
1. Open Source Library Maintainers
2. Security Team
3. Management
4. Developers

DevSecOps
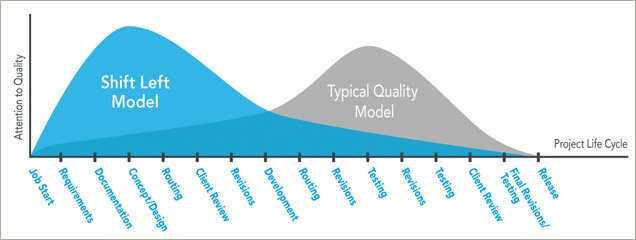
"Shifting Left'
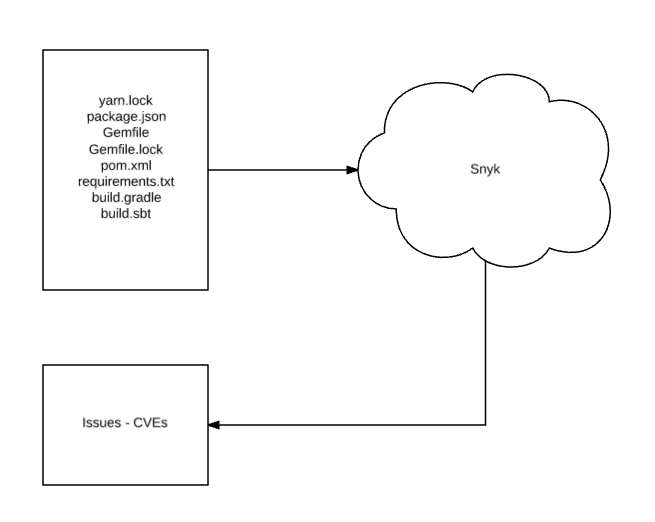
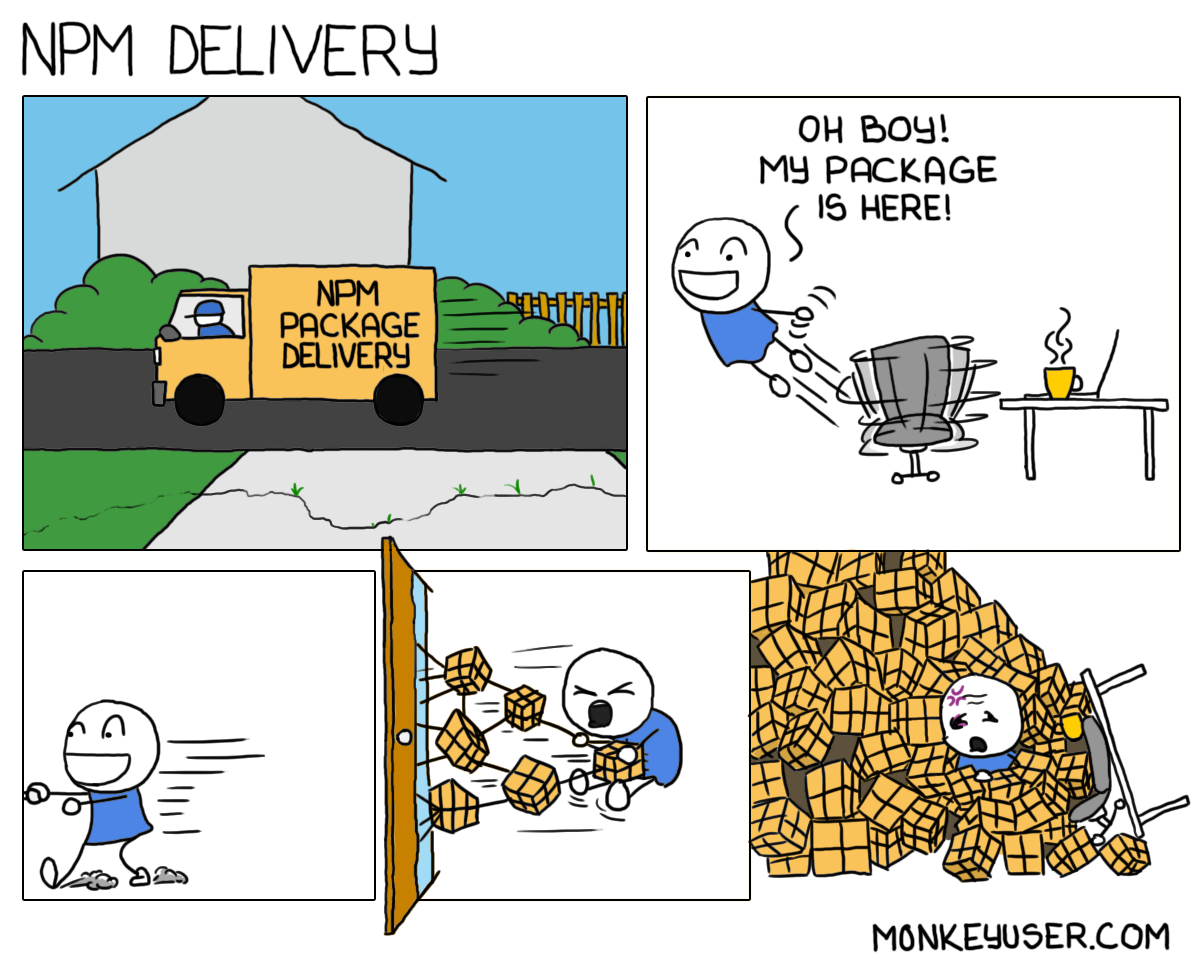
Manifest Scans

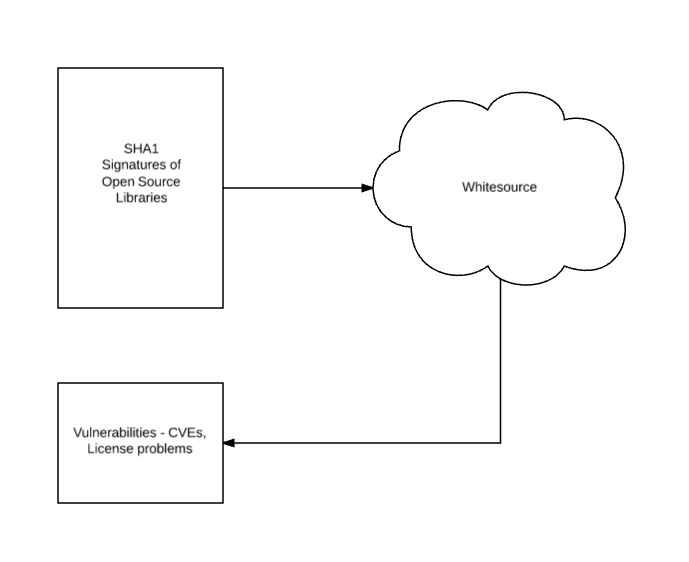
Signature Scans

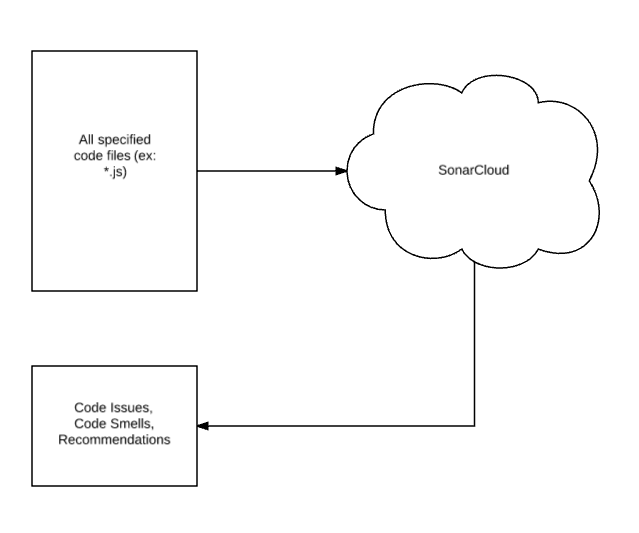
Code Quality Analysis

Caveats
Takeaways:
1. It's your code
2. Check it every commit
3. Educate
https://github.com/codemouse/devsecops-demo
@codemouse
codemouse.com
https://cybric.io
Thanks!

DevSecOps
By Brian Sodano
DevSecOps
- 1,088



