

Your password has been breached!


Troy Hunt
- Gold Coast, Australia
- Microsoft Regional Director
- Course maintainer at Pluralsight
- Founder of Have I Been Pwned (HIBP)
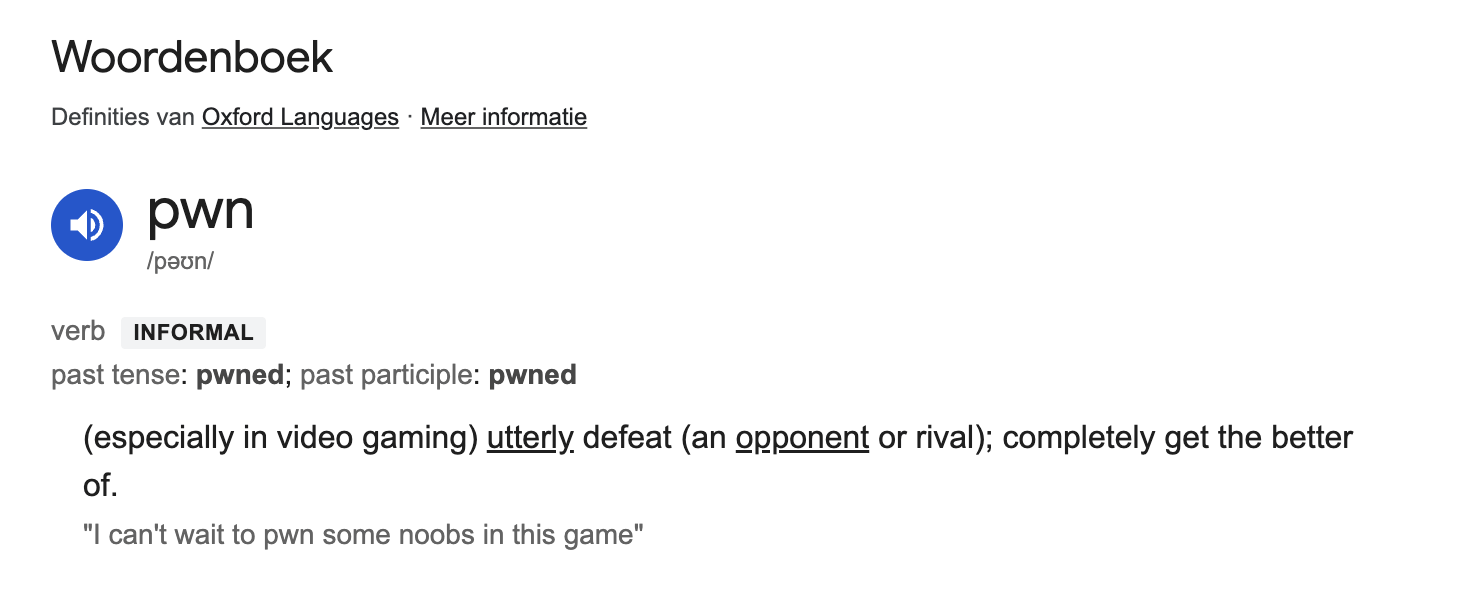

Have I Been Pwned (HIBP)
- Assess if your data was ever compromised
- Founded in 2013, after one of the biggest
data breaches ever → Adobe- 38 million customers’ sensitive information
- Hashed/encrypted passwords
- Credit card details
- E-mail addresses
- ...
- 38 million customers’ sensitive information


Have I Been Pwned
- What's on the website?
- Chronological list of breaches details
- Lookup on e-mail address
- Lookup on password
- Notification service
- API documentation
- ...

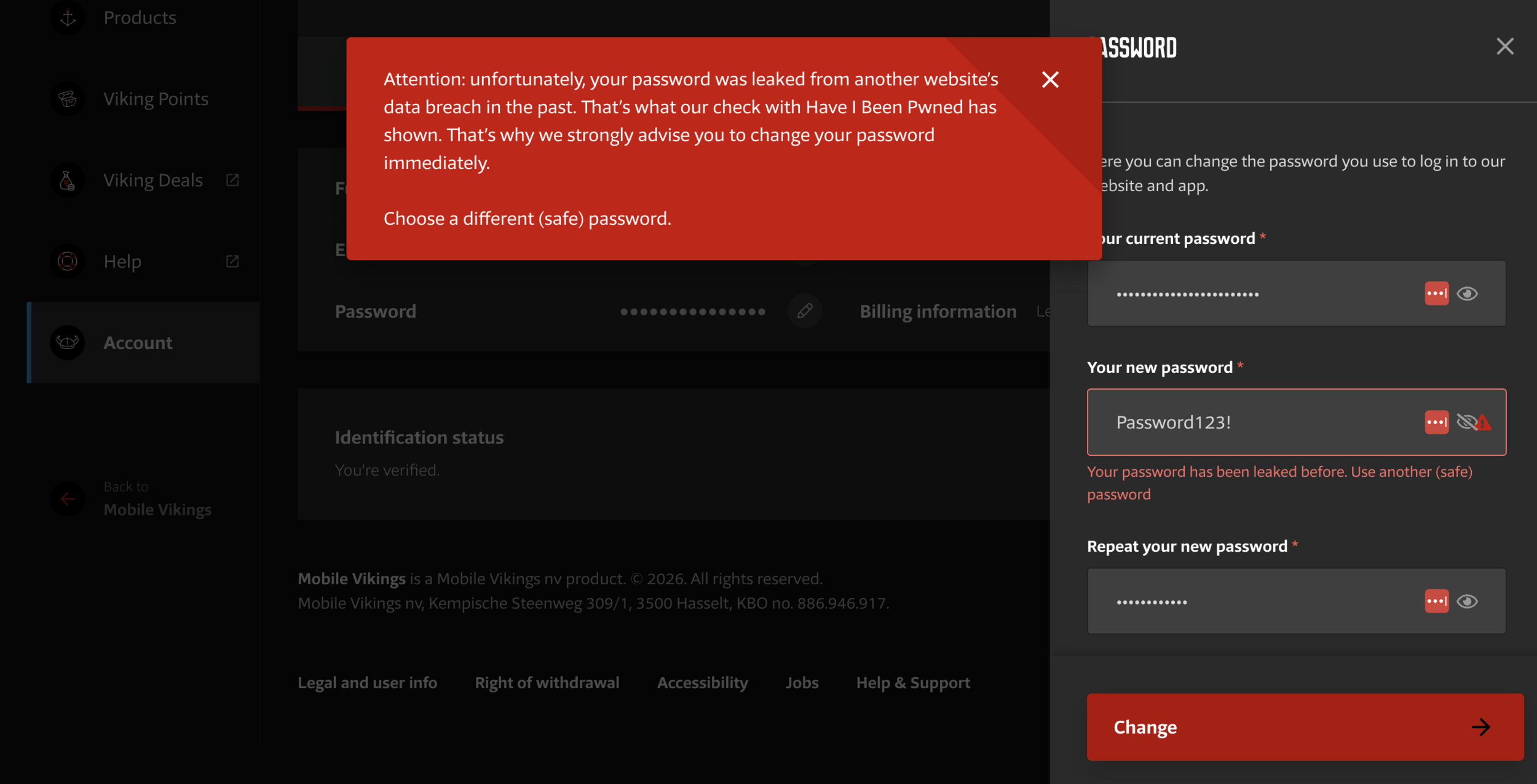
Integrations - Mobile Vikings

Integrations - Mozilla

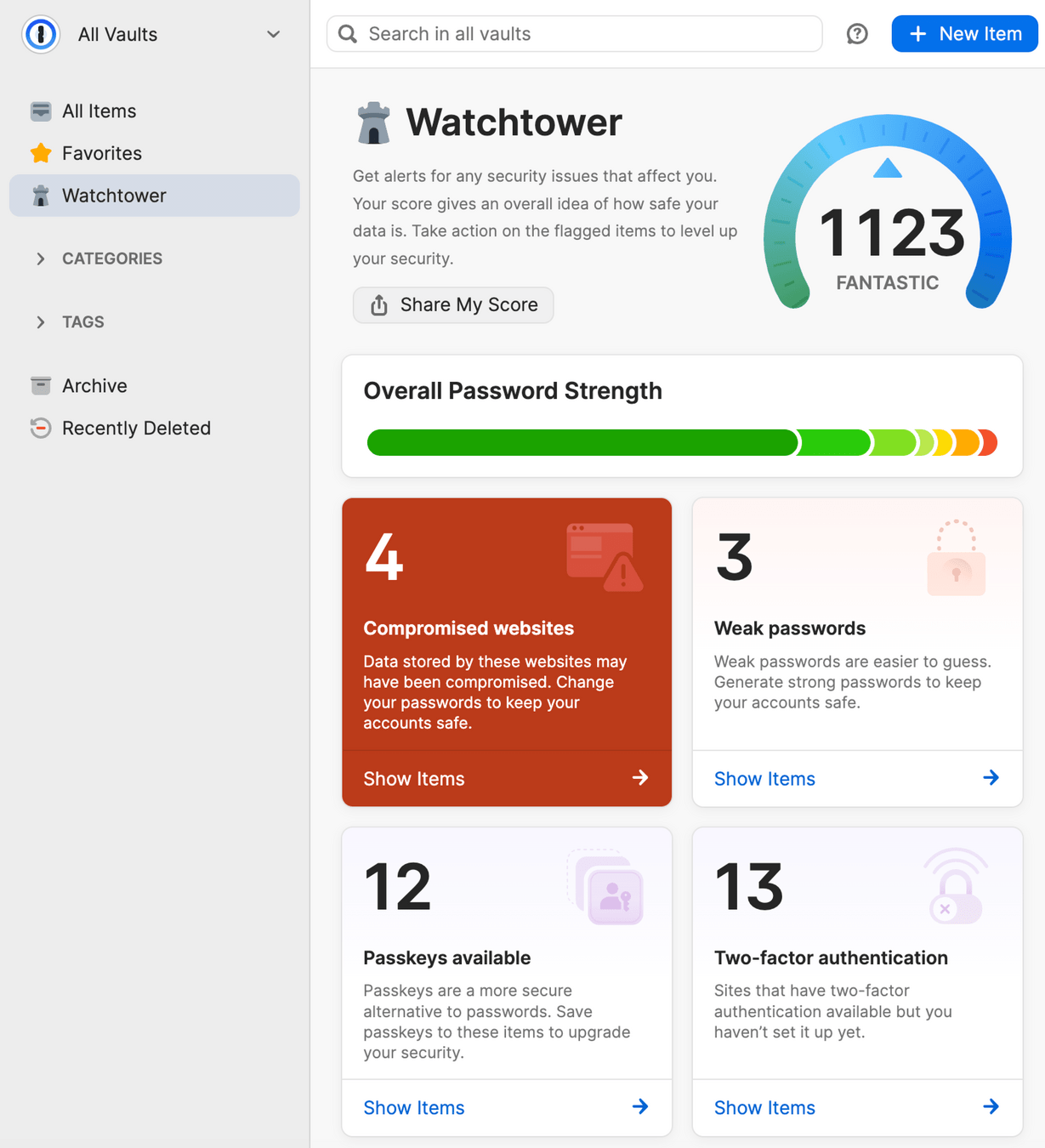
Integrations - 1Password

Lookup on password
Lookup on password, is that secure? 🤔
→ Feel free to download the database
- Billions of hashed passwords (SHA-1)
- Do whatever you want with it

Lookup on password
Nevermind, I'll use the API or website
... but is it really secure? 🤔
- k-anonimity
- No link between usernames and password (hashes)

Recap: hashing
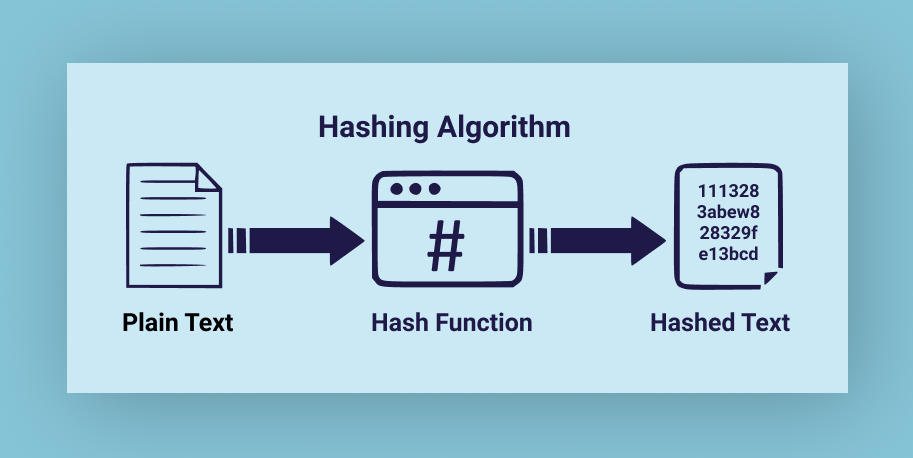

Hashing
Characteristics of cryptographic hashing:
- Input of any length → fixed size output
- Given the output → infeasible to find the input
- Given an input and output →
infeasible to find another input with the same output

Hashing in JavaScript
Node.js: super easy
// Hashing a super bad password in Node.js with SHA-1
const { hash } = require('node:crypto');
const hashedPassword = hash("SHA1", "password");
console.log(hashedPassword);
Hashing in JavaScript
const text = "password";
async function digestMessage(message) {
const msgUint8 = new TextEncoder().encode(message);
const hashBuffer = await window.crypto.subtle.digest("SHA-1", msgUint8);
const hashArray = Array.from(new Uint8Array(hashBuffer));
const hashHex = hashArray
.map((b) => b.toString(16).padStart(2, "0"))
.join("");
return hashHex;
}
digestMessage(text).then((digestHex) => console.log(digestHex));Browser environment: less easy (but doable)

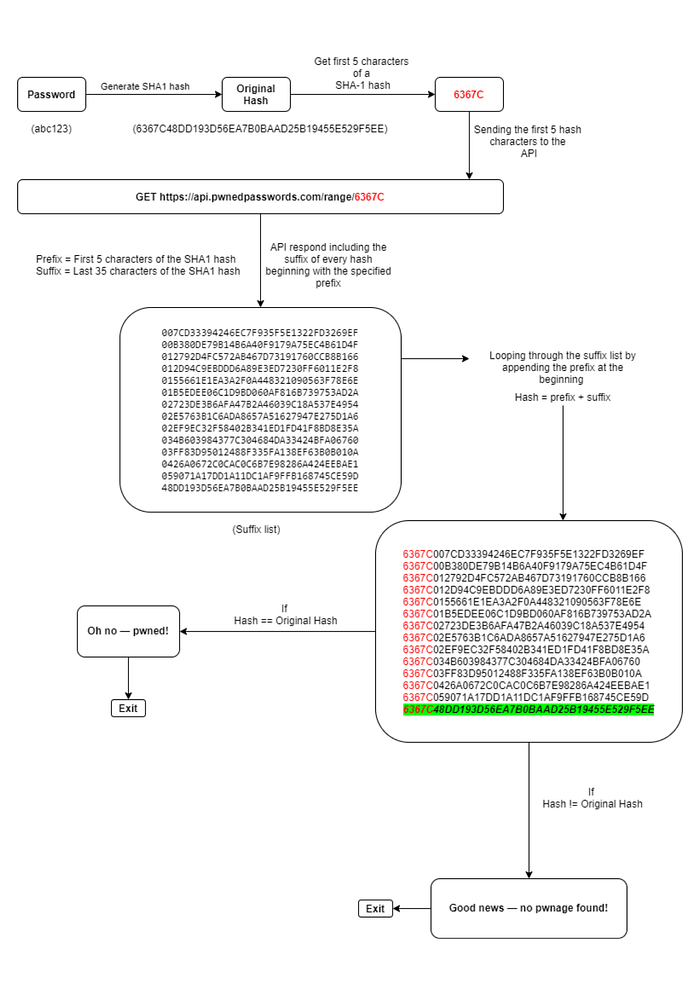
k-anonimity
- Retrieve data about a specific password,
without revealing which password - Solution?
- Servers sends data from all passwords
with the same first 5 characters
- Servers sends data from all passwords
- Why 5 characters? Balance between:
- Response times
- Anonimity

Range search
- All passwords in the DB are hashed (SHA-1)
- API request:
- Send first 5 chars of the hashed password
- API response:
- Return last 35 chars of all hashed passwords
that match the first 5 chars
- Return last 35 chars of all hashed passwords
- Praise the demo Gods! 🙏



Range search (w/ padding)
What if someone intercepts the encrypted API responses, and probes the API based on response size? 🤔
- Padding to the rescue
- Request header: Add-Padding
- Ensures a response of variable size,
making it less likely to guess the prefix

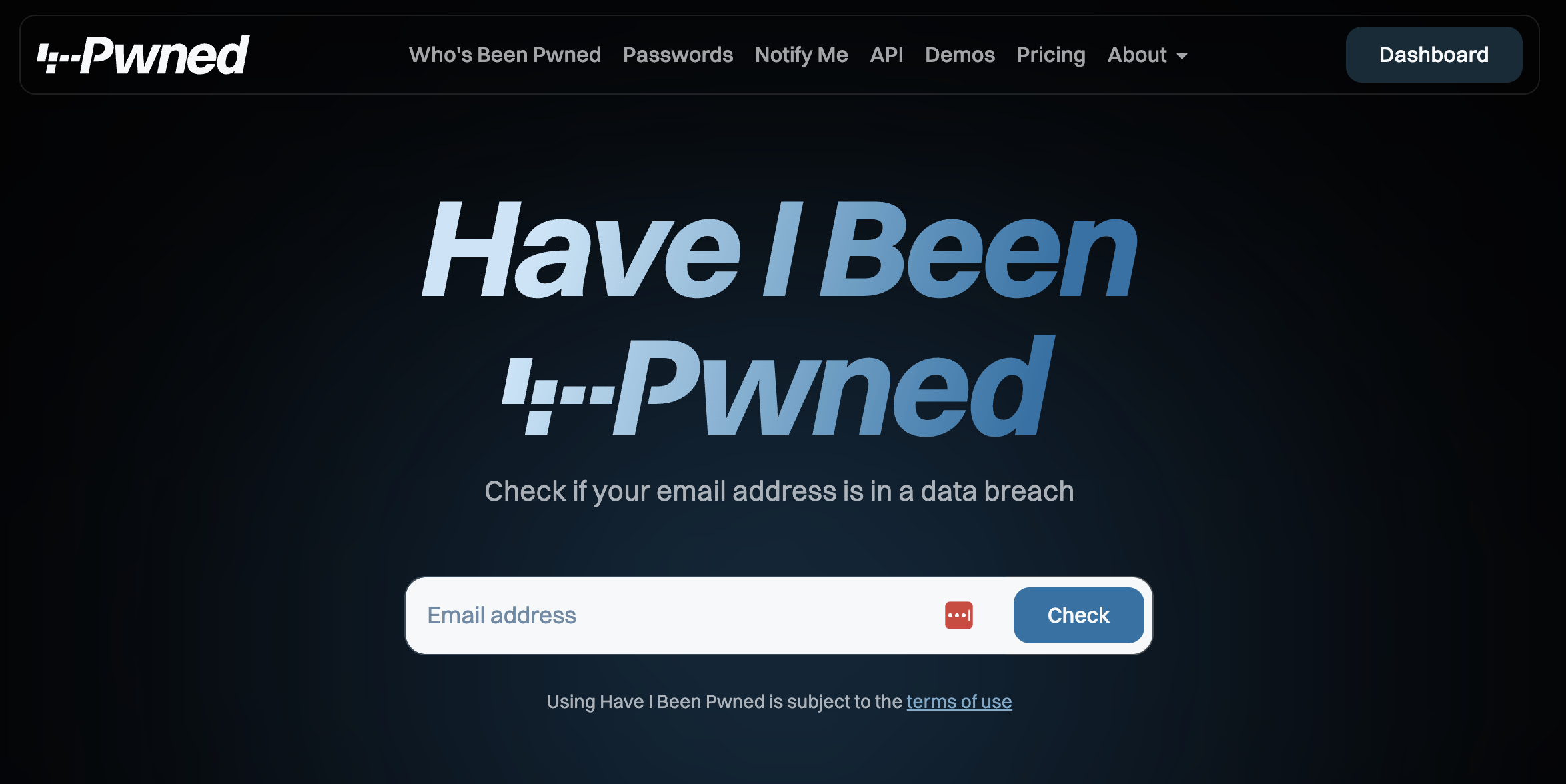
Have I Been Pwned API
- Password search API: completely free
- No rate limit
- Meaning: informing clients when logging in
with a breached password → easy as cake!
- One last time: praise the demo Gods! 🙏

Key takeaways
- Hobby projects can turn into
globally renowned organizations! - You should check out haveibeenpwned.com!
- Integrating HIBP into your sign-up & sign-in flow is super easy, free and beneficial for everyone.
Thanks for listening and keep your passwords safe!
Your password has been breached!
By kareldesmet
Your password has been breached!
- 273



