Dull, Dirty, Dangerous!

It's a bird, It's a plane...
Toys
Cost: 1.5K - 5K INR
Flight time: ~5min
Payload: None
Usage: Recreational

Tools
Cost: In Lakhs
Flight time: ~20-30min
Payload: A lot of tools (~5Kg)
Usage:
Photography
Surveying
Mapping
Search and Rescue
Logistics
Data gathering

Serious Business
Cost: In Crores
Flight time: 8+ hrs
Payload: Tonnes
Usage:
Surveillance
Weapon Delivery




Security Challenges
Regulations
- India: Ministry of Civil Aviation
- A long route for foreigners.
- Registration: UIN (Unique Identification Number)
- Not Beyond Visual Range
- No Fly Zones
- No Permission, No TakeOff
- All these for >250gm, >50feet
- ...
- Are these enforced though? How?
Weather
- Vulnerable to Turbulence, Rain, Snow, Fog etc.
- Uncertainty at local levels in weather.
- Flight aviation reports are tuned to planes.
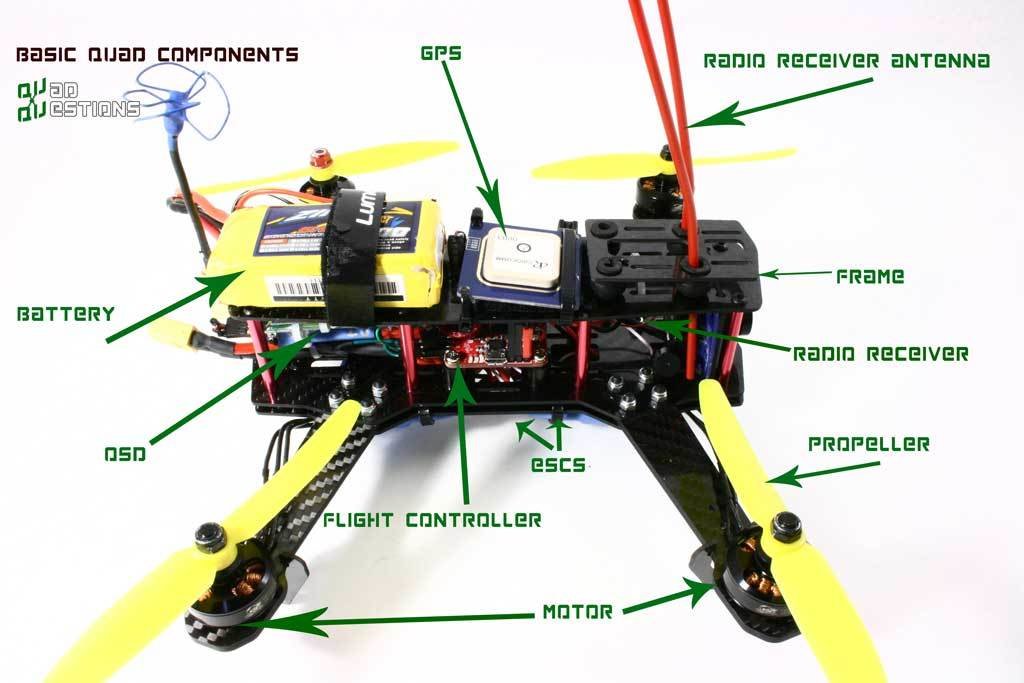
Energy Limitation
- Lightweight LiPo batteries
- Can add more power, but that will add more weight
- Which will need more power and so on...
- + the cost
Communication
- Mostly Unsecure
- Drone-to-Drone: No standardization
- Drone-to-Ground: Bluetooth, Wi-Fi 802.11, Most communication is Public
-
Drone-to-Satellite: GPS
- Prone to Jamming and Spoofing
- e.g Against ISIL in Mosul
Flight Planning
- Basic algorithms for routing
- Mostly controlled in Visual range
- Collision avoidance algo in 3D
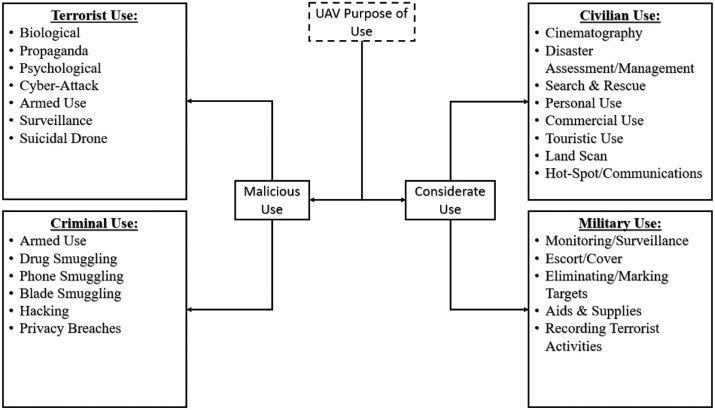
Challenges from Malicious Users
-
Physical Threats
- Assassination attempts (Venezuela, 2018)
- Targetted attacks on Infrastructure
- Smuggling
- Civil Aviation issues
- Swarms
- ...
Challenges from Malicious Users
-
Logical Threats
- WiFI Luring Malware
- Hacking Other Drones
- Logging into insecure device applications (DEFCON'18)
- ...

Title Text
- Bullet One
- Bullet Two
- Bullet Three
How though?
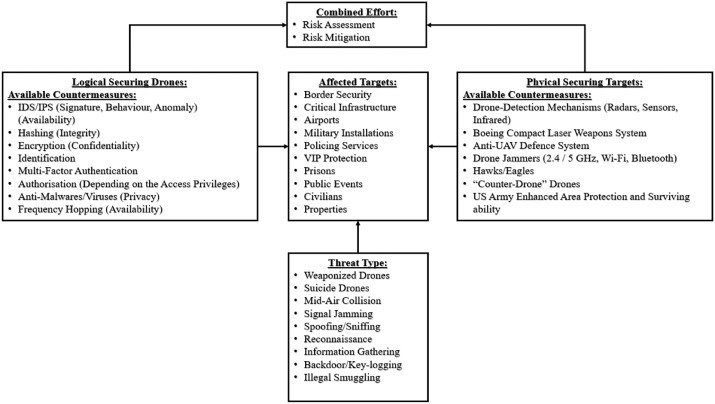
Gaps
- Unauth access
- Social Engineering
Safeguards
- End-to-end Encryption
- Device auth
- Physical Security
- Better Regulations
Authorisation
Gaps
- Malware
- Port Scans
Safeguards
- Stronger Password Policy
- Malware Detection Techniques
Drone
Gaps
- Eavesdropping
- Man-In-the-Middle
- Jamming
- ARP Poisoning
- MAC Spoofing
Safeguards
- Encryption
- Hashing
- Firewalls
- Access Control Updates
Communication
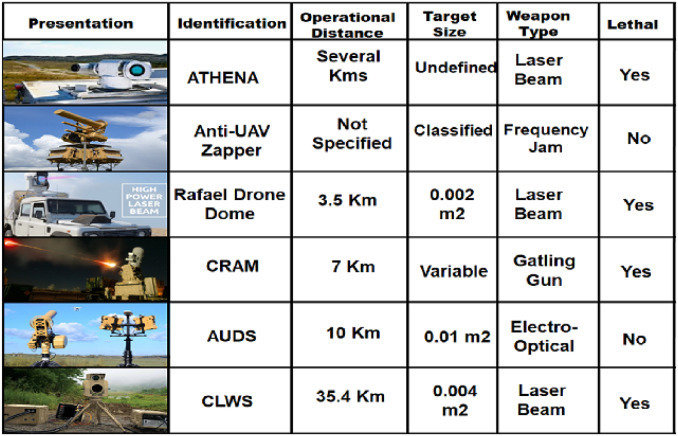
Detection Techniques
- Audio-based
- Visuals
- Motion Detection
- Thermal
- RF-based detection
Post Detection?
The way Ahead
- Improving Regulations
- Secure and Trusted Drone Hardware
- Trusted Communication Channels
- Improvements in Detection
- Improvements in Evasion
- Drone-to-Drone Communications
- Swarm Organization Algorithms
Thank You
deck
By Nikhilesh Singh
deck
- 45



