Iptables - FirewallD
Quick and Dirty
XXXXXXXXXXXXXXXXXX
XXX Network XXX
XXXXXXXXXXXXXXXXXX
+
|
v
+-------------+ +------------------+
|table: filter| <---+ | table: nat |
|chain: INPUT | | | chain: PREROUTING|
+-----+-------+ | +--------+---------+
| | |
v | v
[local process] | **************** +--------------+
| +---------+ Routing decision +------> |table: filter |
v **************** |chain: FORWARD|
**************** +------+-------+
Routing decision |
**************** |
| |
v **************** |
+-------------+ +------> Routing decision <---------------+
|table: nat | | ****************
|chain: OUTPUT| | +
+-----+-------+ | |
| | v
v | +-------------------+
+--------------+ | | table: nat |
|table: filter | +----+ | chain: POSTROUTING|
|chain: OUTPUT | +--------+----------+
+--------------+ |
v
XXXXXXXXXXXXXXXXXX
XXX Network XXX
XXXXXXXXXXXXXXXXXX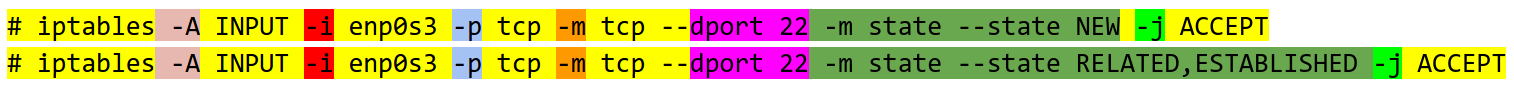
Iptables - Beispiel: SSH
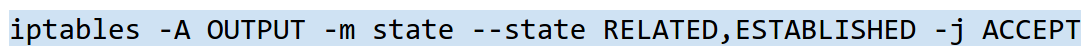
Output
Input
# lock ip-range over time
iptables -A OUTPUT -m iprange --dst-range IP-IP -m time --timestart 12:00 --timestop 13:00 -j ACCEPT
# self defined chain for dns
-N INPUT_DNS
-A INPUT -j INPUT_DNS
-A INPUT_DNS -p udp -m udp --dport 53 -m state --state NEW -j ACCEPT
-A INPUT_DNS -p udp -m udp --dport 53 -m state --state RELATED,ESTABLISHED -j ACCEPT# port knocking
iptables -N TRAFFIC
iptables -N KNOCK1
iptables -N KNOCK2
iptables -A INPUT -j TRAFFIC
iptables -A TRAFFIC -p icmp --icmp-type any -j ACCEPT
ipabtles -A TRAFFIC -m state --state ESTABLISHED,RELATED -j ACCEPT
iptables -A TRAFFIC -m state --state NEW -m tcp -p tcp --dport 8022 -m recent --rcheck --seconds 30 --name SSH2 -j ACCEPT
iptables -A TRAFFIC -m state --state NEW -m tcp -p tcp --dport 8022 resent --remove --name SSH2 -j DROP
iptables -A TRAFFIC -m state --state NEW -m tcp -p tp -m recent --dport 9991--rcheck --name SSH1 -j KNOCK2
iptables -A TRAFFIC -m state --state NEW -m tcp -p tcp -m rcent --remove --name SSH1 -j DROP
iptables -A TRAFFIC -m state --state NEW -m tcp -p tp -m recent --dport 7777--rcheck --name SSH0 -j KNOCK1
iptables -A TRAFFIC -m state --state NEW -m tcp -p tp -m recent --remove--name SSH0 -j DROPFirewallD - Features
- Zones
- Services
- D-BUS interface
- ICMP types
- Direct interfaces (apps & services)
- Permanent configuration
- Default/Fallback configuration
# current config
firewall-cmd --zone=public --add-service=ssh
# permanent config
firewall-cmd --permanent --zone=public --add-service=ssh
# current config
iptables -A INPUT -i enp0s3 -p tcp -m tcp --dport 22 -m state --state NEW -j ACCEPT
iptables -A INPUT -i enp0s3 -p tcp -m tcp --dport 22 -m state --state RELATED,ESTABLISHED -j ACCEPT
# permanent config
iptables-save > /etc/sysconfig/iptables <= recover with iptables-restoreIptables
firewalld
# zones
=> drop <= only outgoing connections allowed
=> block <= incoming connections blocked with icmp message
=> public <= only selected connection allowed public network <== default on CentOS7
=> external <= * external connection (nat active) used by routers
=> dmz <= * server with public access and limited private access
=> work <= * mostly trusted (office)
=> home <= * mostly trusted (home)
=> internal <= * mostly trusted (internal)
=> trusted <= all connection accepted - trusted clients only
# show default zone
firewall-cmd --get-default-zone
public
# show active zones with the related interfaces
firewall-cmd --get-active-zones
public
interfaces: eth0
# available services
[root@pmatti ~]# firewall-cmd --get-services
RH-Satellite-6 amanda-client bacula bacula-client dhcp dhcpv6 dhcpv6-client
dns freeipa-ldap freeipa-ldaps freeipa-replication ftp high-availability http
https imaps ipp ipp-client ipsec iscsi-target kerberos kpasswd ldap ldaps
libvirt libvirt-tls mdns mountd ms-wbt mysql nfs ntp openvpn pmcd pmproxy
pmwebapi pmwebapis pop3s postgresql proxy-dhcp radius rpc-bind rsyncd samba
samba-client smtp ssh telnet tftp tftp-client transmission-client
vdsm vnc-server wbem-https
firewall-cmd --list-all-zones
public (default, active)
interfaces: eth0
sources:
services: dhcpv6-client http https ssh
ports: 4000/tcp 9090/tcp 2008/tcp 9091/tcp 30033/tcp 9987/udp 80/tcp
masquerade: no
forward-ports:
icmp-blocks:
rich rules: <=== high level language
external
interfaces:
sources:
services: ssh
ports:
masquerade: yes
forward-ports:
icmp-blocks:
rich rules:
internal
interfaces:
sources:
services: dhcpv6-client http ipp-client mdns samba-client ssh
ports:
masquerade: no
forward-ports:
icmp-blocks:
rich rules:
/etc/firewalld/firewalld.conf
# firewalld config file
# default zone
# The default zone used if an empty zone string is used.
# Default: public
DefaultZone=public
# Minimal mark
# Marks up to this minimum are free for use for example in the direct
# interface. If more free marks are needed, increase the minimum
# Default: 100
MinimalMark=100
# Clean up on exit
# If set to no or false the firewall configuration will not get cleaned up
# on exit or stop of firewalld
# Default: yes
CleanupOnExit=yes
/etc/firewalld/zones/public.xml
<?xml version="1.0" encoding="utf-8"?>
<zone>
<short>Public</short>
<description>Public Zone</description>
<service name="dhcpv6-client"/>
<service name="http"/>
<service name="ssh"/>
<service name="https"/>
<port protocol="tcp" port="80"/>
</zone>iptables-firewalld
By Phil Matti
iptables-firewalld
short overview about iptables and firewalld
- 468

