Content Addressable Network
Abhishek Kedia & Shonit Chamadia
1
What is CAN ?
CAN is an implementation of distributed hash table (DHT).
2
Distributed Hash Table
Hash Table
- Mapping from keys to values.
- Use a "hash function" to map keys into a reduced space.
- For eg.
- Use this hashed value ( (x) ) to index values into an array.
In DHT the hash table is distributed over a set of inter-connected nodes/peer and is available concurrently to each peer.
3
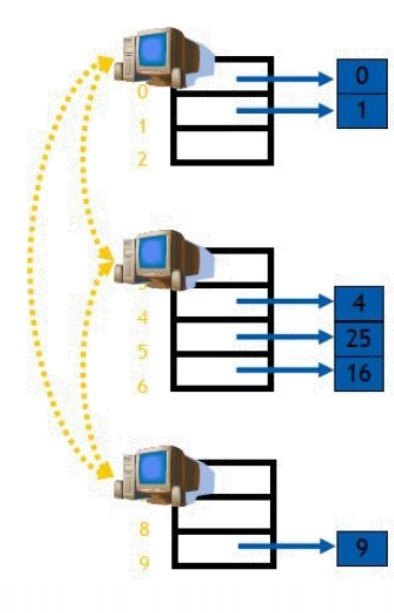
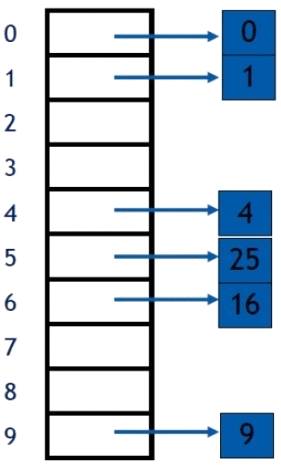
Split and distribute
Approach
Centralized
Distributed
Keys
Values
keys on the same node can be easily accessed
But we need some Routing Mechanism to access keys on other nodes
4
Applications of DHT
Essential for network-wise indexing of resources (files, etc.)
-
BTDigg: BitTorrent search engine
-
cjdns: routing engine for mesh-based networks
-
Freenet: a censorship-resistant anonymous network
-
Hazelcast: Open-source in-memory data grid
-
I2P: An open-source anonymous peer-to-peer network.
-
I2P-Bote: serverless secure anonymous e-mail.
-
YaCy: a distributed search engine
-
Tox: an instant messaging system
-
Twister: a microblogging peer-to-peer platform
5
Implementations
-
CHORD (discussed in class)
-
CAN
-
Pastry/Tapestry
-
SkipNet
-
Symphony
...
6
CHORD
-
Structured P2P Network
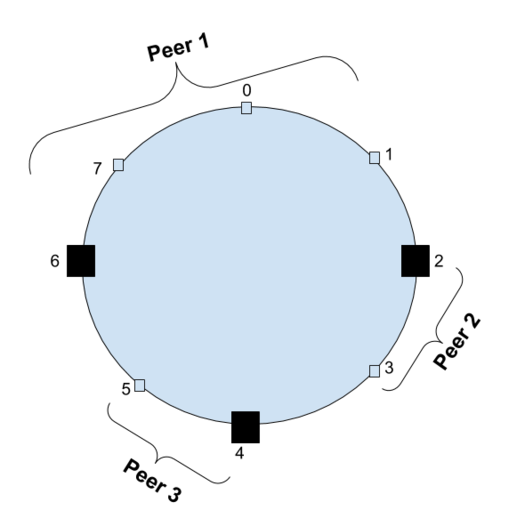
-
Hash Key Space -> Ring
7
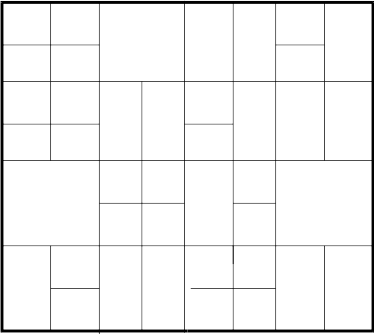
Key Space 1-Dimensional Ring
Obvious Extension
d-dimensional torus !
8
d-torus
d times
d-torus can be obtained from d-dimensional hypercube by gluing opposite faces together.
9
2-torus
10
CAN
- Hash function maps keys onto points on the surface of a d-torus.
- The surface is divided into zones which are maintained by individual nodes/peers.
Each peer maintains:
- (Key,Value) pairs corresponding to points residing in its zone.
-
Address of immediate neighboring peers.
11
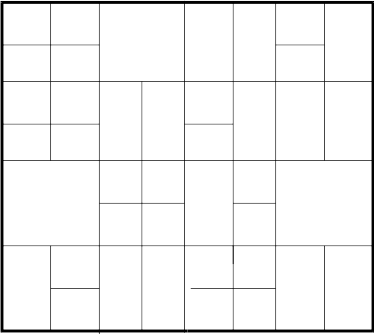
Structure
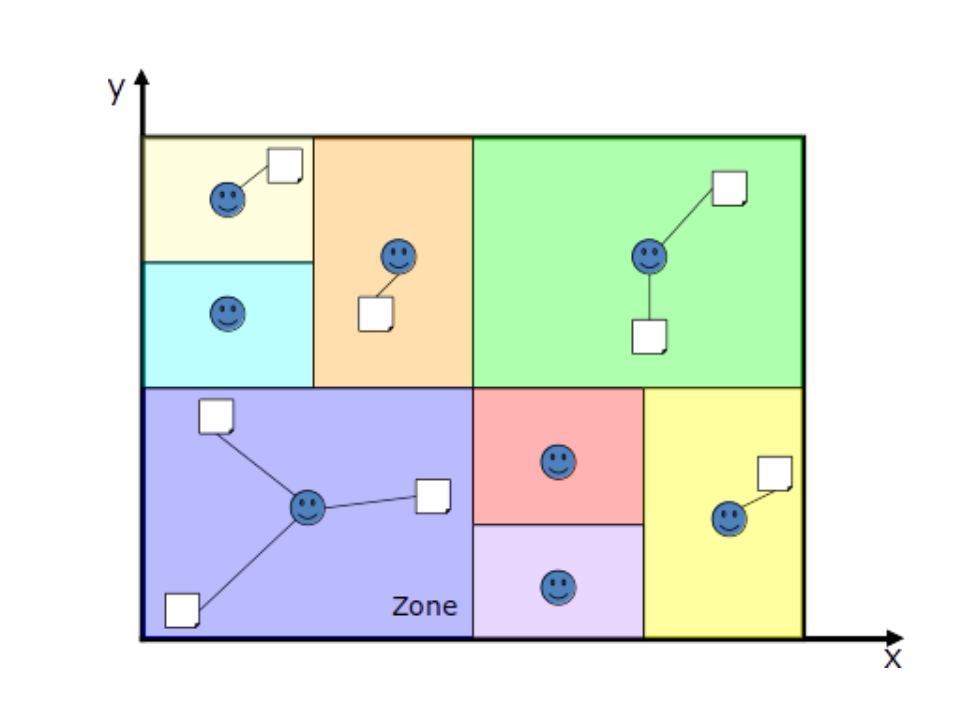


Peer
Resource
Note - Actually the space wraps onto itself, but that has not been shown for simplicity
12
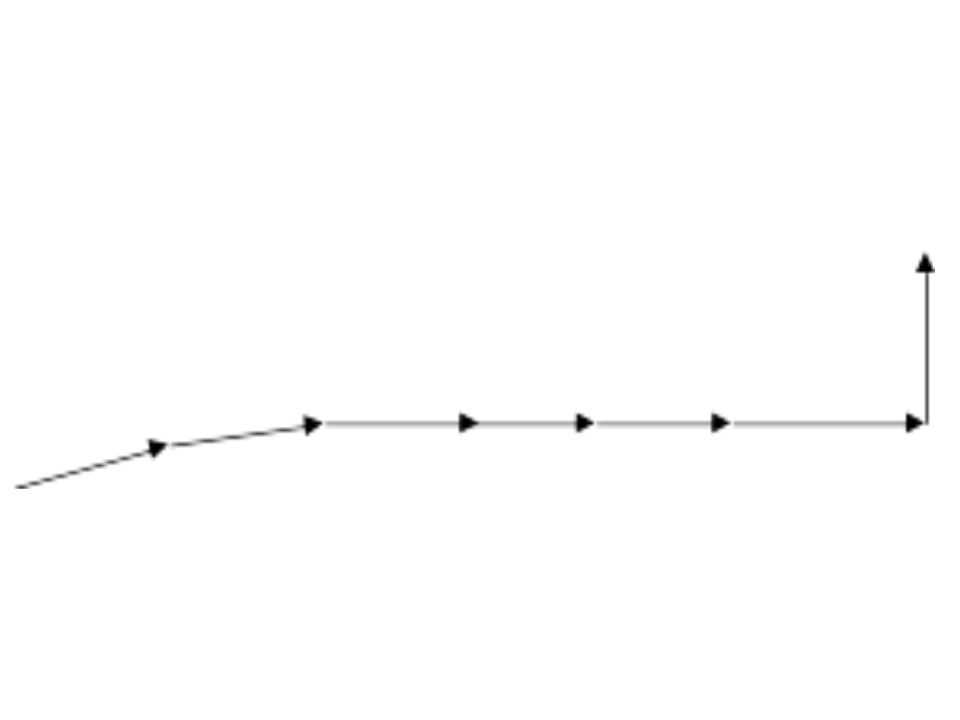
Routing Mechanism
x
Queries resource with key K
H(k) = (a,b)
(a,b)


Request greedy forwarded neighbor closest to destination
13
Average Path Length
If d-dimensional space is partitioned into n equal zones, then
Average Path Length =
By choosing ,we can achieve similar scaling as in CHORD
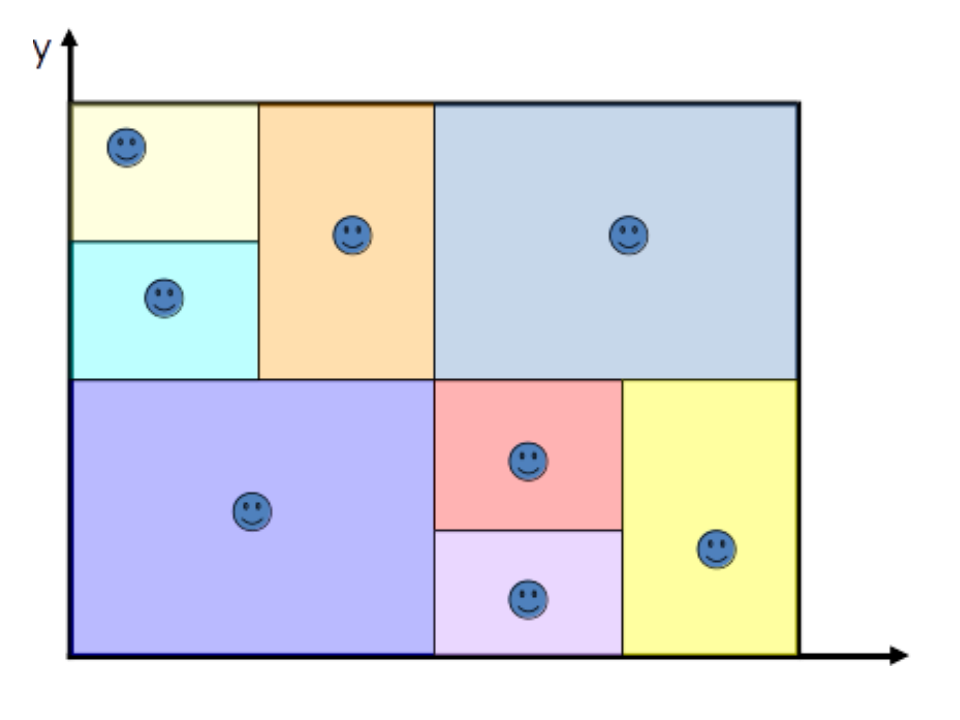
CAN Construction
Network State at some point in time
New Node willing to enter the network
Bootstrap Node
Requests Address
of already existing
node
Responds with address of I
Bootstrap Response I picks a random point P in space
(x,y)
I routes JOIN request to P
On receiving JOIN request zone containing P splits into half
14
CAN Construction
On receiving JOIN request zone containing P splits into half
New Node
One half of the new split is assigned to the new node
Splitting node updates its own neighbor list, and also provides information to the new node
Finally both old & new nodes' neighbors must be informed about this relocation
15
-
These nodes send an update message to their neighbors.
-
Also, every node in the system sends a periodic "heartbeat" to its neighbors
These two ensure that all of the neighbors will quickly learn about the change
- Addition of a node affects only a small number of nodes in a very small locality
- The number of neighbors a node maintains depends only on the dimensionality and independent of number of nodes
16
Node Departure
Graceful Departure
- One of the neighbors takes over. The takeover is decided as:
- If a neighbor that can be merged to produce a valid zone, then it is the takeover node.
- Else, neighbor with the smallest volume temporarily handles both volumes.
- Departing node hands over its (key,value) pairs to the takeover node.
17
Node failure
Detection
- Each node periodically sends "heartbeat"/update messages to its neighbors.
- Prolonged absence of heartbeat signals node failure.
Takeover
- Each neighbor starts a takeover timer in proportion to its volume.
- When timer expires, sends TAKEOVER message to other neighbors. They turn off their timers.
18
deck
By shonitchamadia
deck
- 251

