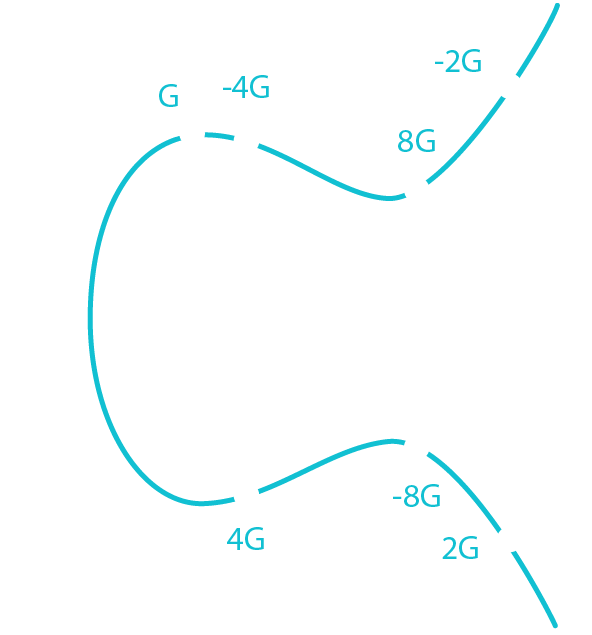
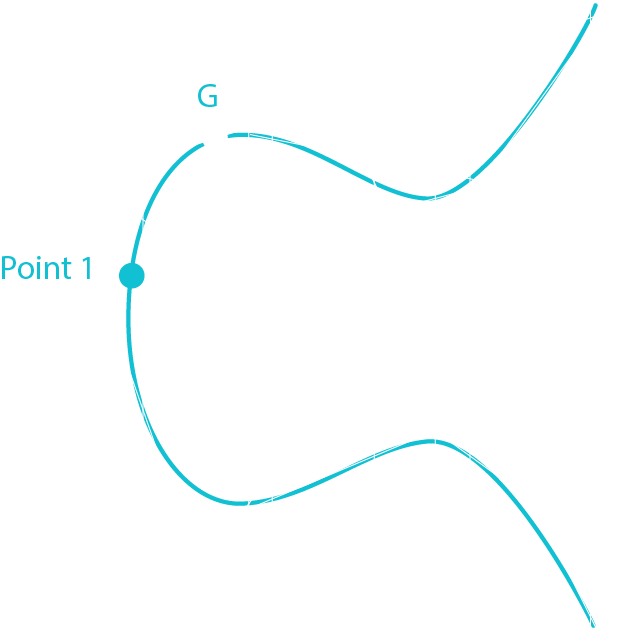
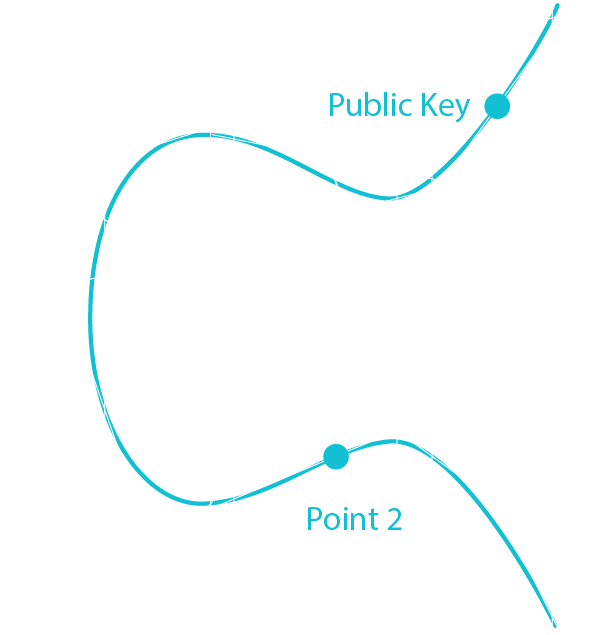
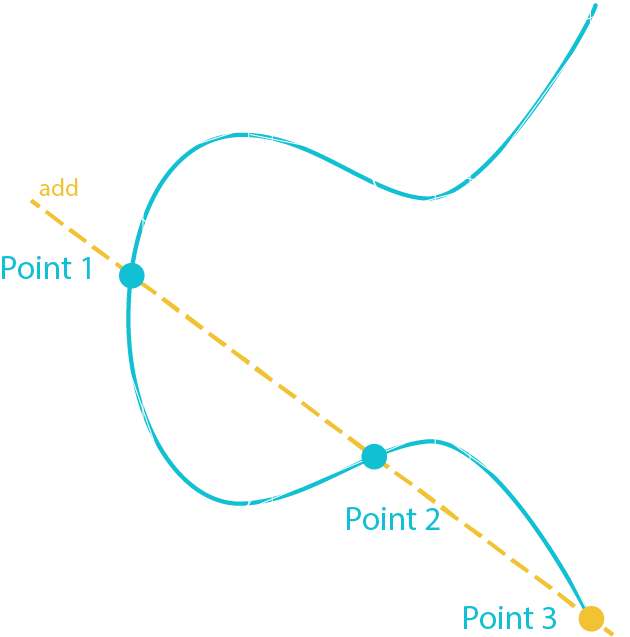
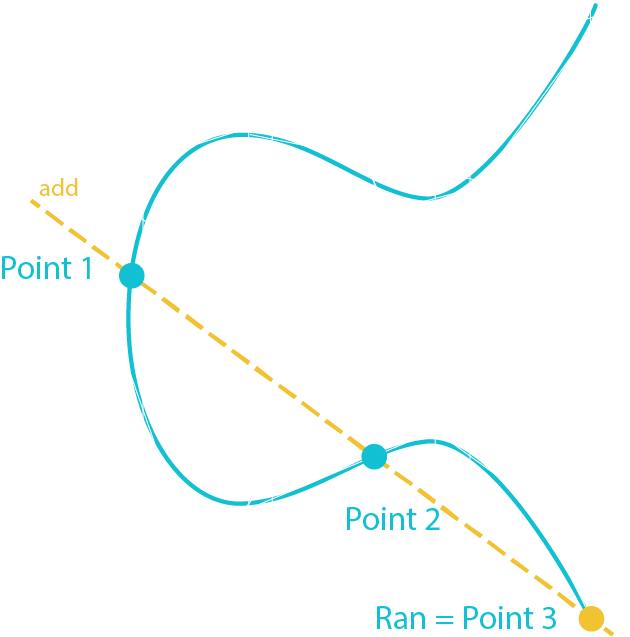
Public Key = G * Private Key
Public Key = G * df5b62be7cede995255057cf9559869850abd67549557098e486e3e8bc9d701f
Through ECDSA we get 2 new coordinates:
x = 81591541406288143274758265124625798440200740391102527151086648448953253267255
y = 64573953342291915951744135406509773051817879333910826118626860448948679381492
In hexadecimal
Public Key (x) = b4632d08485ff1df2db55b9dafd23347d1c47a457072a1e87be26896549a8737
Public Key (y) = 8ec38ff91d43e8c2092ebda601780485263da089465619e0358a5c1be7ac91f4
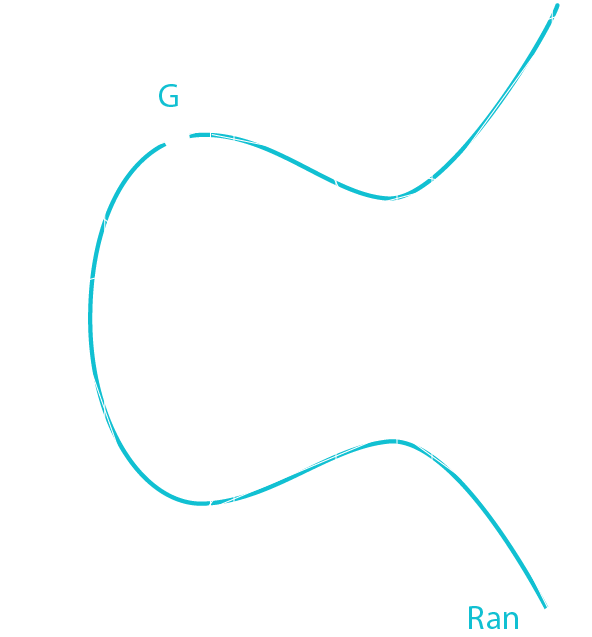
Keep only the (x) coordinate and discriminate the sign of the (y) coordinate
Public Key = 02b4632d08485ff1df2db55b9dafd23347d1c47a457072a1e87be26896549a8737