API Security
Securing SOAP, REST, and GRAPHQL Apis
jmcshannon
Module Overview
- What is API security
- What is the purpose of API Security
- Use Cases
- Threat Modeling for an API
- Access Control, AuthZ, AuthN
- Access Control, API permissions, Object Permissions
- API security types
- LAB -> Securing the Dawg API
PART 0: What is API security?

API Security in a Nutshell
API security is the practice of protecting application programming interfaces (APIs) from threats to Confidentiality, Integrity and Availability.
What does that actually mean?
| Confidentiality | Integrity | Availability |
|---|---|---|
| Information is protected from inadvertent disclosure | API output is not tampered | API is readily available for work |
| Private API routes stay private | API input is not tampered | API is resistant to conditions that would cause the API to be unavailable |
| Underlying API information is not disclosed | API doesn't tamper other services | API doesn't propagate faulty conditions |
PART 1: What is The Purpose of API Security
Why secure an API
- Protect Resources
- Protect Data
- Protect Users
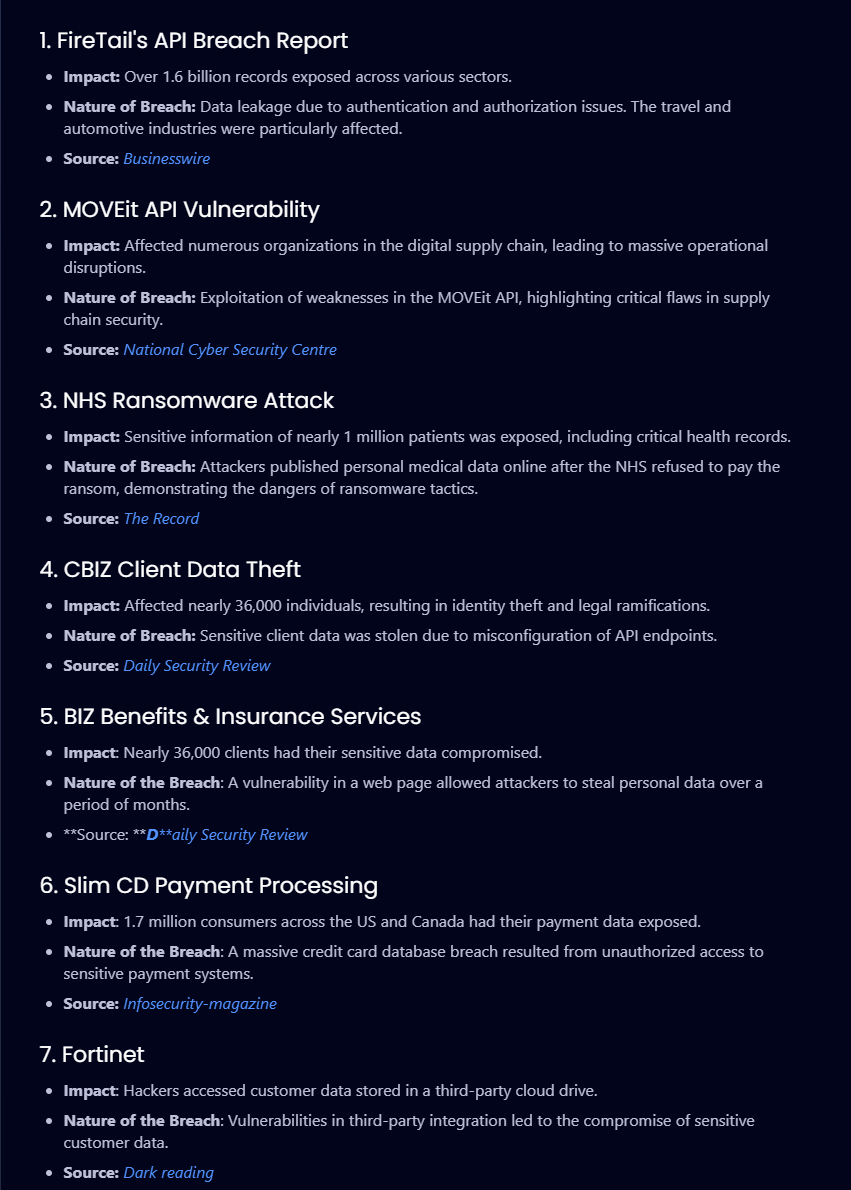
https://treblle.com/blog/top-api-breaches-2024
Part 2: Use Cases
Public API use cases
Private API use cases
- Many APIs are public
- DogAPI
- NVD
- Should these APIs be secured?
- What methods should we use to secure them?
- Likewise what techniques can be used to secure a private API?
- Mixing and Matching private and public APIs
PART 3: Threat Modeling an API
Threat Modeling Methodologies
- Process for Attack Simulation and Threat Analysis (PASTA)
- Damage, Reproducibility, Exploitability, Affected users, and Discoverability (DREAD)
- Spoofing, Tampering, Repudiation, Information disclosure, Elevation of privilege, Denial of service (STRIDE)
S.T.R.I.D.E DOG API
Spoofing - Pretending to be another entity
| Spoofing |
|---|
| unauthenticated user spoofs as authenticated user |
| Authenticated user spoofs as a different authenticated user |
| ??? |
S.T.R.I.D.E DOG API
Spoofing - Pretending to be another entity
| Spoofing | Tampering |
|---|---|
| unauthenticated user spoofs as authenticated user | authenticated user modifies another users data |
| Authenticated user spoofs as a different authenticated user | unauthenticated user is able to modify rate limiting settings |
| ??? | ??? |
Tampering - Unauthorized modification
S.T.R.I.D.E DOG API
Spoofing - Pretending to be another entity
| Spoofing | Tampering | Repudiation |
|---|---|---|
| unauthenticated user spoofs as authenticated user | authenticated user modifies another users data | user submits cat, says they didn't |
| Authenticated user spoofs as a different authenticated user | unauthenticated user is able to modify rate limiting settings | user submits stego image, says they didn't |
| ??? | ??? | ??? |
Tampering - Unauthorized modification
Repudiation - Action taken with no record
S.T.R.I.D.E DOG API
Spoofing - Pretending to be another entity
| Spoofing | Tampering | Repudiation | Information Disclosure |
|---|---|---|---|
| unauthenticated user spoofs as authenticated user | authenticated user modifies another users data | user submits cat, says they didn't | API reveals whether or not a user has an account |
| Authenticated user spoofs as a different authenticated user | unauthenticated user is able to modify rate limiting settings | user submits stego image, says they didn't | API reveals specific version and build information in errors |
| ??? | ??? | ??? | ??? |
Tampering - Unauthorized modification
Repudiation - Action taken with no record
Information Disclosure - exposing information that isn't meant to be exposed
S.T.R.I.D.E DOG API
Spoofing - Pretending to be another entity
| Spoofing | Tampering | Repudiation | Information Disclosure | Denial of Service |
|---|---|---|---|---|
| unauthenticated user spoofs as authenticated user | authenticated user modifies another users data | user submits cat, says they didn't | API reveals whether or not a user has an account | API has no rate limiting and limited scaling capabilities |
| Authenticated user spoofs as a different authenticated user | unauthenticated user is able to modify rate limiting settings | user submits stego image, says they didn't | API reveals specific version and build information in errors | Crafted input causes system to crash |
| ??? | ??? | ??? | ??? | ??? |
Tampering - Unauthorized modification
Repudiation - Action taken with no record
Information Disclosure - exposing information that isn't meant to be exposed
Denial Of Service - Service disruption
S.T.R.I.D.E DOG API
Spoofing - Pretending to be another entity
| Spoofing | Tampering | Repudiation | Information Disclosure | Denial of Service | EOP |
|---|---|---|---|---|---|
| unauthenticated user spoofs as authenticated user | authenticated user modifies another users data | user submits cat, says they didn't | API reveals whether or not a user has an account | API has no rate limiting and limited scaling capabilities | user is able to specify admin account from client side |
| Authenticated user spoofs as a different authenticated user | unauthenticated user is able to modify rate limiting settings | user submits stego image, says they didn't | API reveals specific version and build information in errors | Crafted input causes system to crash | crafted input allows user to specify account type |
| ??? | ??? | ??? | ??? | ??? | ??? |
Tampering - Unauthorized modification
Repudiation - Action taken with no record
Information Disclosure - exposing information that isn't meant to be exposed
Denial Of Service - Service disruption
Elevation of Privilege - unauthorized additional perms
OWASP API TOP 10 2023
| Risk | Description |
|---|---|
| Broken Object Level AuthZ | Any API function that accesses a data source using an attacker controlled ID should implement Object level access control checks |
| Broken AuthN | Incorrect implementation of AuthN mechanisms compromises the overall security of APIs |
| Broken Object Property Level AuthZ | Improper AuthZ at the object property level leading to information disclosure |
| Unrestricted Resource Consumption | Lack of rate limiting and usage restrictions |
| Broken function level AuthZ | Complex authZ schemes create EoP opportunities |
| Unrestricted Access to Sensitive Business Flows | Design/Logic flaw that does not consider how certain flows could cause harm to a business |
| Server Side Request Forgery | Failing to validate user supplied URI results in crafted request to unexpected destination |
| Security Misconfiguration | Failure to follow best practices in a complex environment leads to poor security practices |
| Improper Inventory Management | Can't protect what you don't know about, additionally potentially unwanted exposed endpoints are not documented |
| Unsafe Consumption of APIs | API implicitly trusts data received from another API that is targeted by an attacker |
PART 4: Access Control Authz, AuthN
Access Control Authz AuthN
Access Control - Deciding whether a subject should be granted or denied access to an object/resource
AuthZ - Shorthand for Authorization. Authorization is whether or not a subject has the permissions to perform an action
AuthN - Shorthand for Authentication, Authentication is where you prove an identity
Simple Example
You provide a username, password, and second factor to login to an account. This is authentication. You asserted that you were the identity, and proved that assertion through knowledge of the password and either ownership of the second factor, or by being the second factor in the case of biometrics.
You then take various actions within your account, however when attempting to perform an action outside of your account permissions you are unable due to the aforementioned lack of permissions. This is authorization.
Types of AuthN
- Basic Auth - b64 encode your username and password and include it in the request (No thanks)
- Token Auth - Include a bearer token in your authZ header.
- API Keys - Similar to a password, but usually generated on the API property and has much better entropy. Usually.
- OAUTH - Similar to token auth, but can also include a refresh token in addition to the access token. Provides Scopes. OIDC. JWT
PART 5: APIs and Object Permissions
Object Level Permissions
- Object level permissions unsurprisingly apply to the object returned from an API view
- This permission check checks to see if the request has the proper authZ for performing a function on an object
- In DRF (Django Rest Framework) object level permissions can be applied by using built in permission classes or other methods
- As highlighted by the OWASP top 10 complex authZ schemes and misconfigurations can leave gaps in posture.
PART 6: Lab
Code
By jmcshannon
Code
- 39



