5G Security
In this presentation
- Why 5G causes COVID
- Why 5G was created by the Government to spy on us
- Why Birds are Government drones
In this Presentation
- Overview of 5G
- Security Vulnerabilities in 5G
What is 5G?
magic!
5G Components
- Radio Access Network (RAN)/New Radio (NR)
- Core Network (called "the core")
- User Equipment (UE, just phones)
5th Generation
- Previous was 4G LTE
- Increased Speeds and decreased latency
- New Core network with security features
- Many new uses
- Edge computing
- IoT
- Industrial
- SA vs NSA

5G Radio Access Network
- Also known as RAN
- Massively Multiple Input Multiple Output
- Multiple frequencies (with multipath resolution)
- OFDM with higher multiplexing

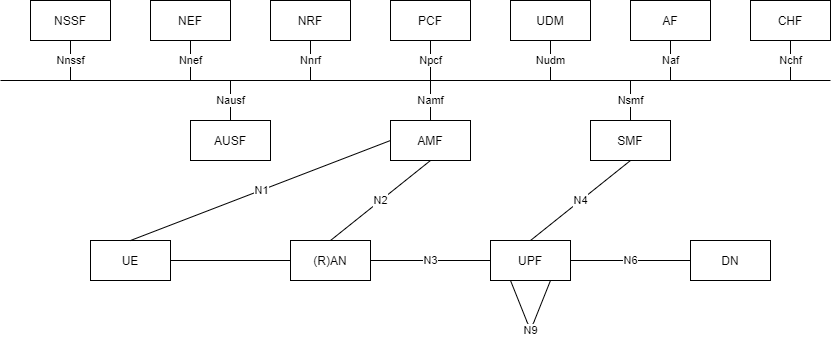
5G Core
- 10 Network Functions
- NRF, NSSF, NEF, PCF, UDM, UDR, AUSF, SMF, UPF, AMF
- Many Network Interfaces
- Can be broken down into control and user planes
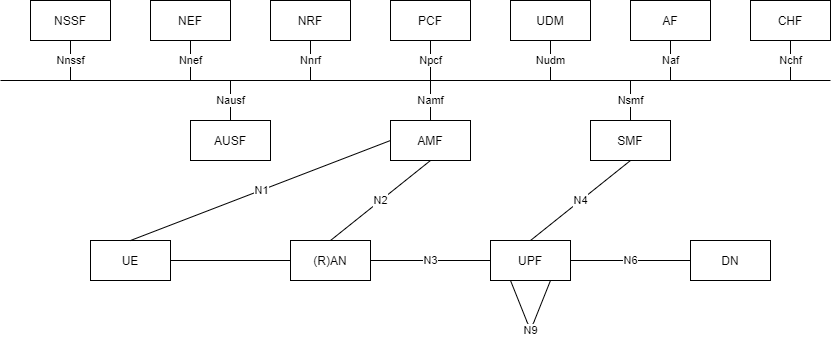
NRF
- Network Repository Function
- Stores all NFs an operator has
- Provides and API for NFs to communicate
- Like the phone book of the NFs
PCF
- Policy Control Function
- Implements policies
- Allows for control of speed to priority, etc
NSSF
- Network Slicing Selection Function
- Slice network up
- Implemented with SDNs
UDM/UDR
- Unified Data Management/User Data Repository
- UDR is the database of the 5G
- UDM accesses the UDR to get information
AUSF
- Authentication Server Function
- Carries out the new key agreement
- AMF contacts the AUSF
SMF
- Session Management Function
- Creates sessions to data network
Questions
5G Security

Three Major Vulnerabilties
- Authentication and Key Management (AKA), SUPI/SUCI
- Fake Base Stations/IMSI Catchers
- Compromised Network Functions
SUPI/SUCI
- Subscription Permanent Identifier
- Subscription Concealed Identifier
- During attach, SUPI is exposed
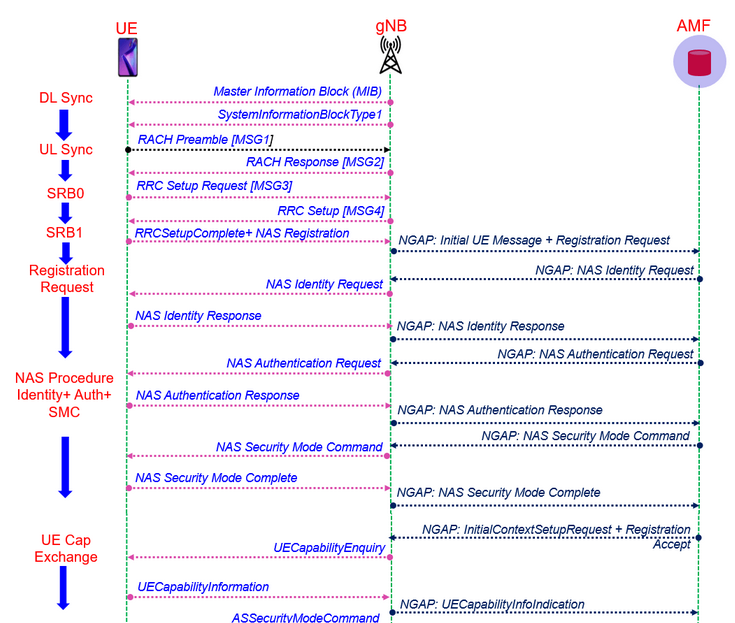
Fake Base Stations
- IMSI Catchers
- MiTM
- DOS/DDOS
Compromised NFs
- Fake AMF
- PFCP exploitation
- Rouge Core
Questions?
5G Security
By Neil Koul
5G Security
- 101



