Lecturer: Иo1lz Date: Nov. 24th, 2019
OUTLINE
- Are you a dork?
- Search Syntax
- Encore - Github Dork
Are you a dork?
Google Dorks = Google Dorking = Google Hacking
What is Google Hacking?
Simply to describe, the advance searching technique of google.
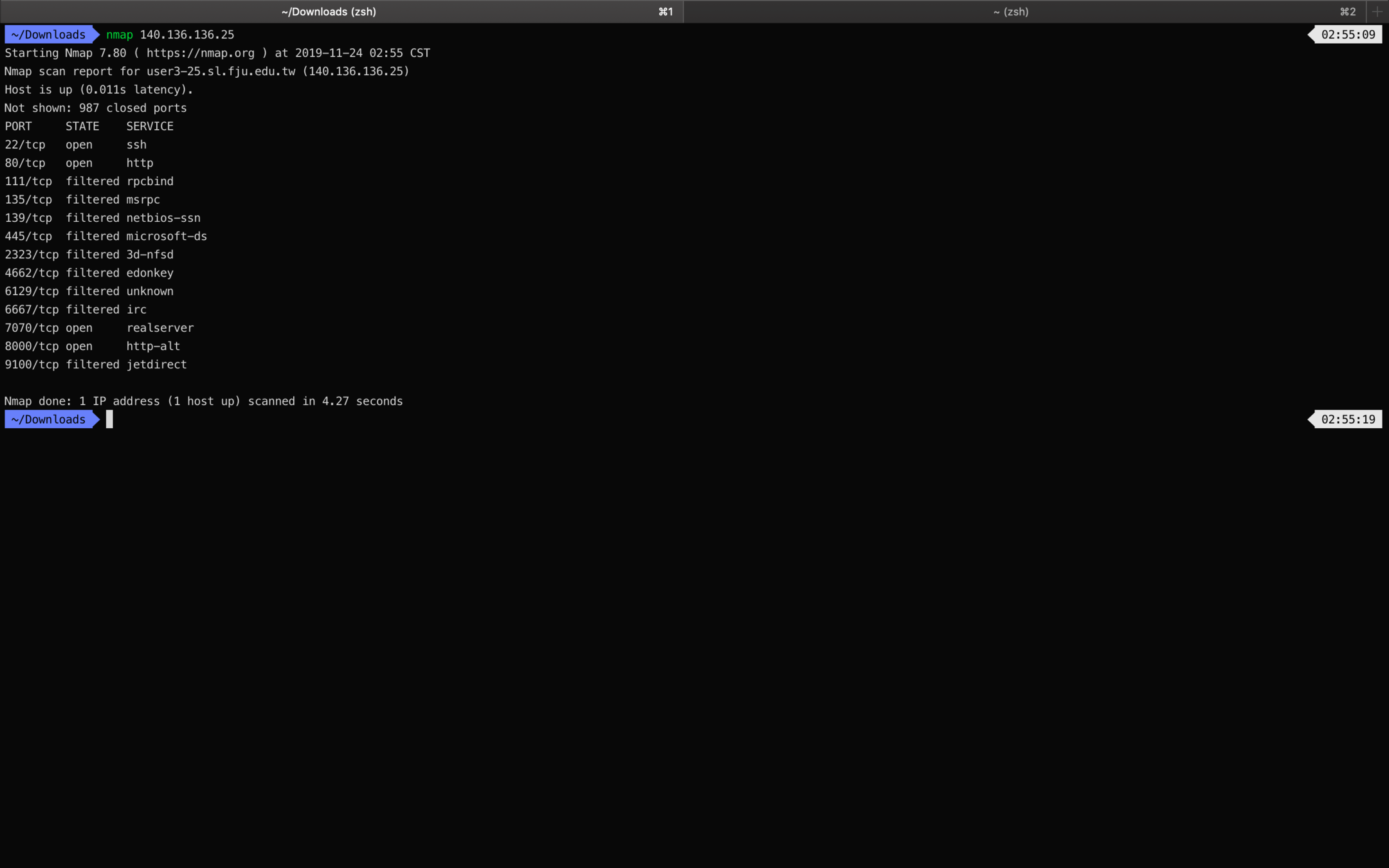
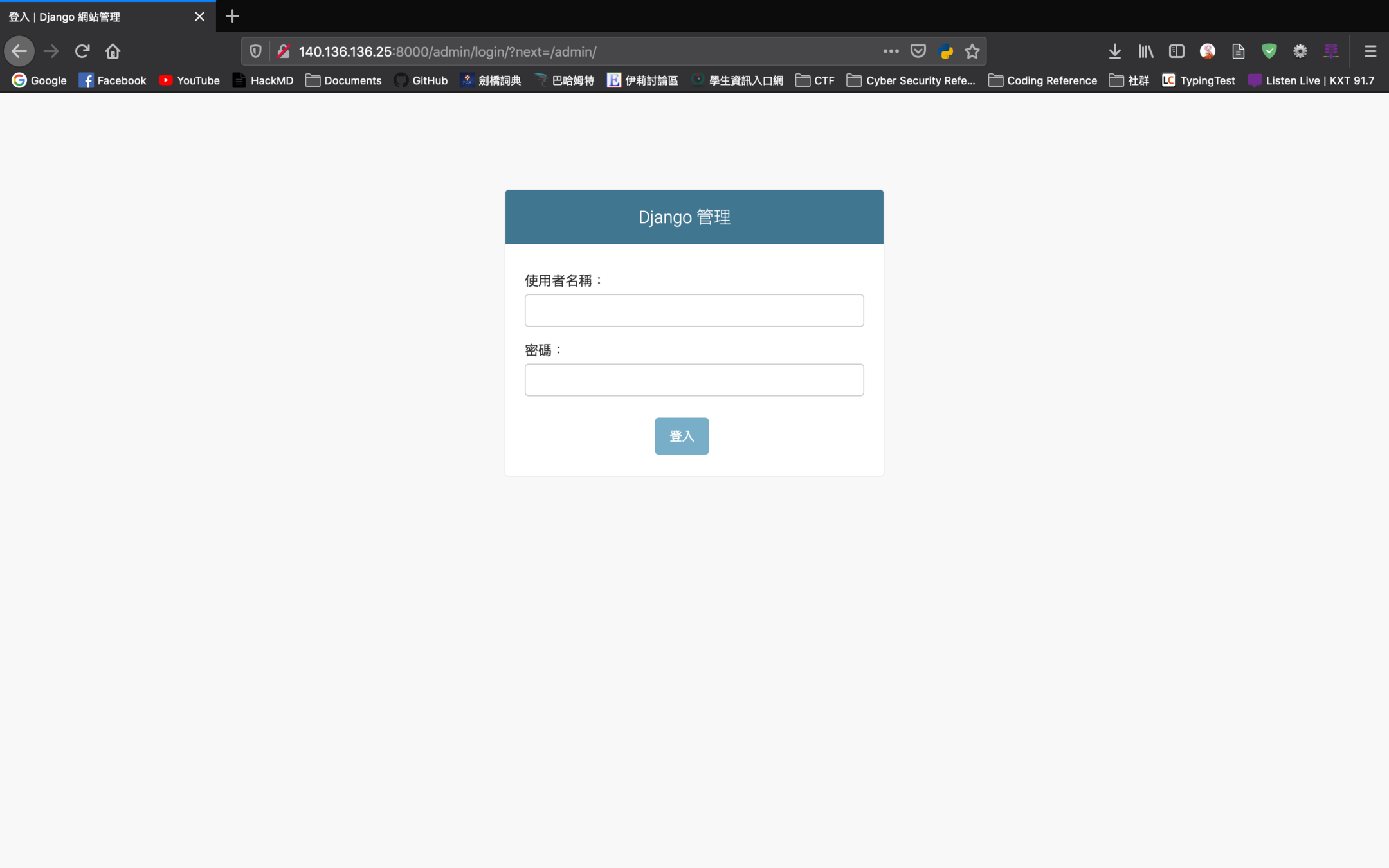
The practice of using Google to find vulnerable web applications and servers by using native Google search engine capabilities.
Unless you block specific website from your website using a robots.txt file, Google indexes all the information that is present on any website.
Before reading any further, be aware that Google will start blocking your connection if you connect from a single static IP. It will ask for captcha challenges to prevent automated queries.

Search Syntax
allintext
Search for specific text contained on any web page.
allintitle
Search for specific text contained on any web page that will show pages that contain titles with X characters
site
Show you the full list of all indexed URLs for the specified domain and subdomain
inurl
The same as allinurl, but it is only useful for one single keyword
filetype
Used to search for any kind of file extensions.
intitle
Used to search for various keywords inside the title.
intext
Useful to locate pages that contain certain characters or strings inside their text
inanchor
This is useful when you need to search for an exact anchor text used on any links
Keywords
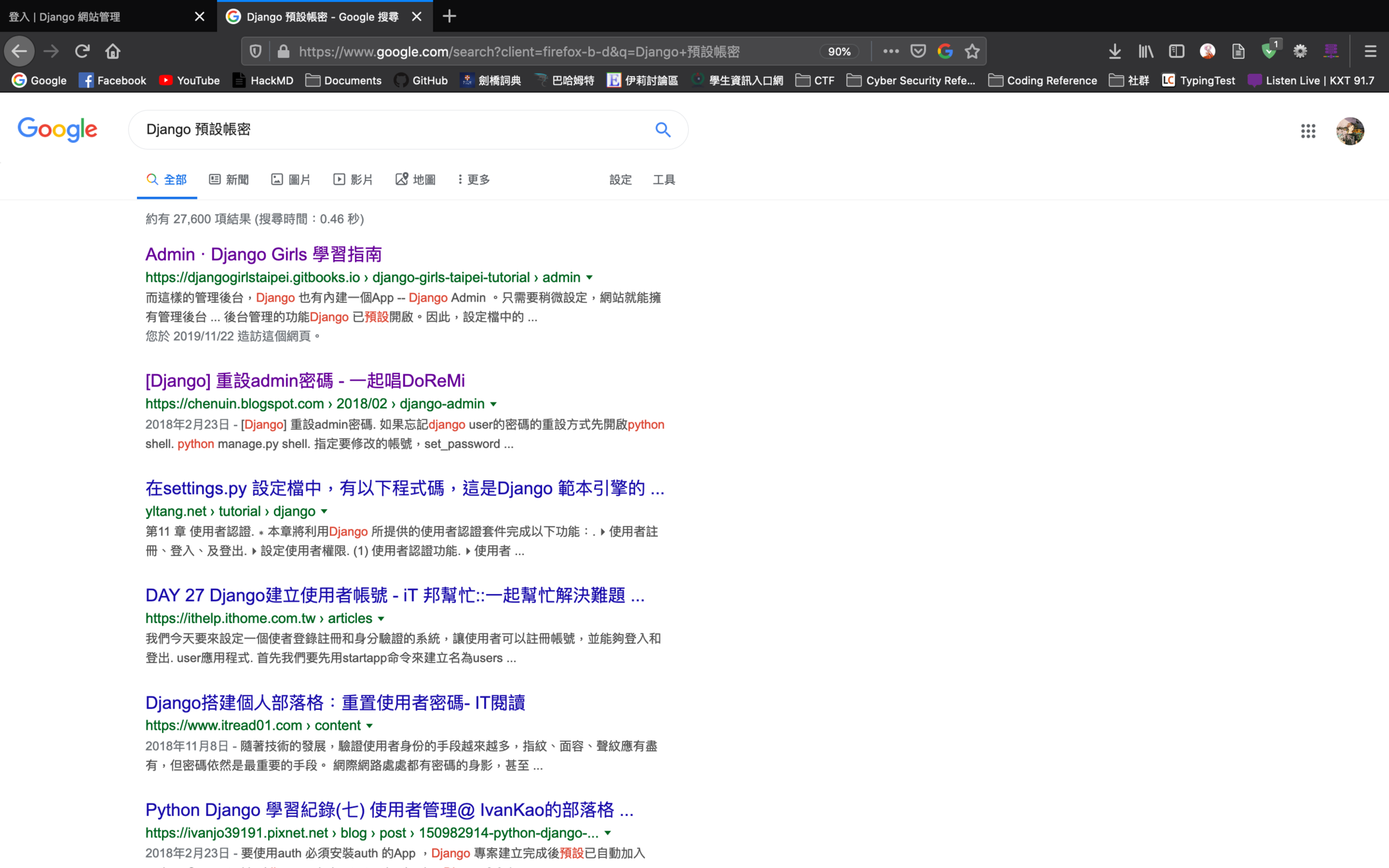
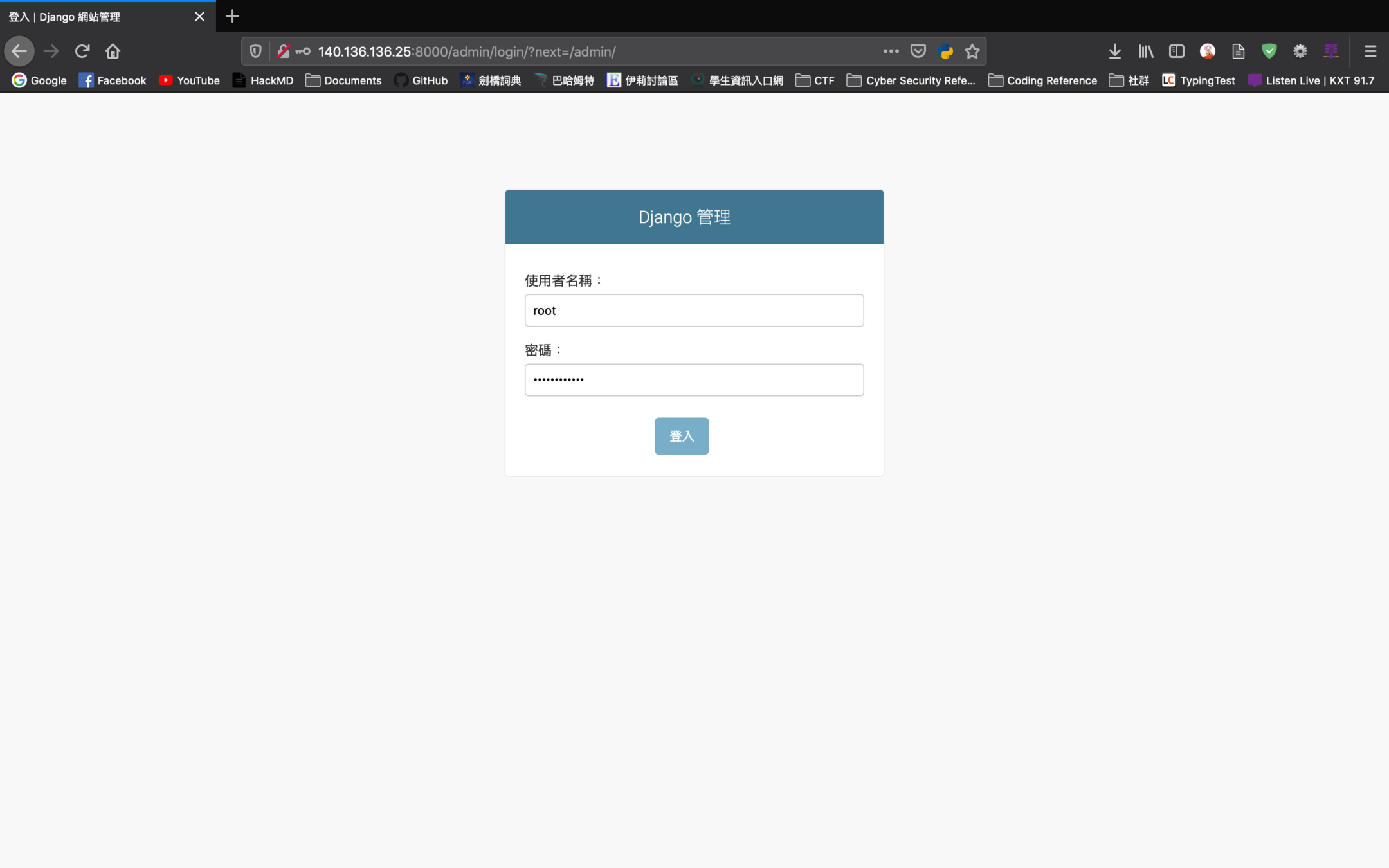
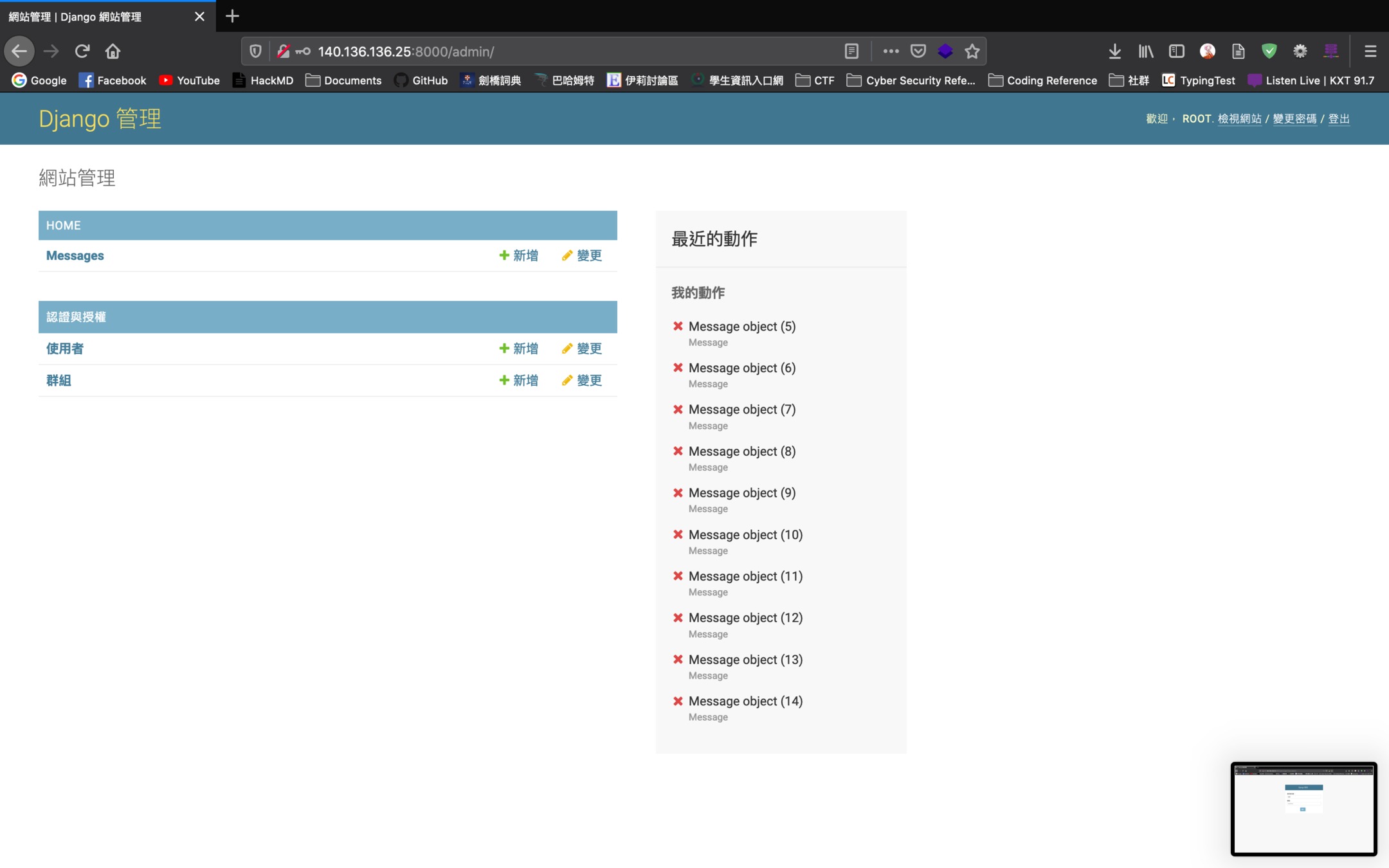
password, login, admin, administrator, passwd, php, pdf, log, edu, root, db, database, account, auth, authenticate, index, access, ssh, xls, xml, jsp, ajax...
Welcome and visit the Google Hacking Database
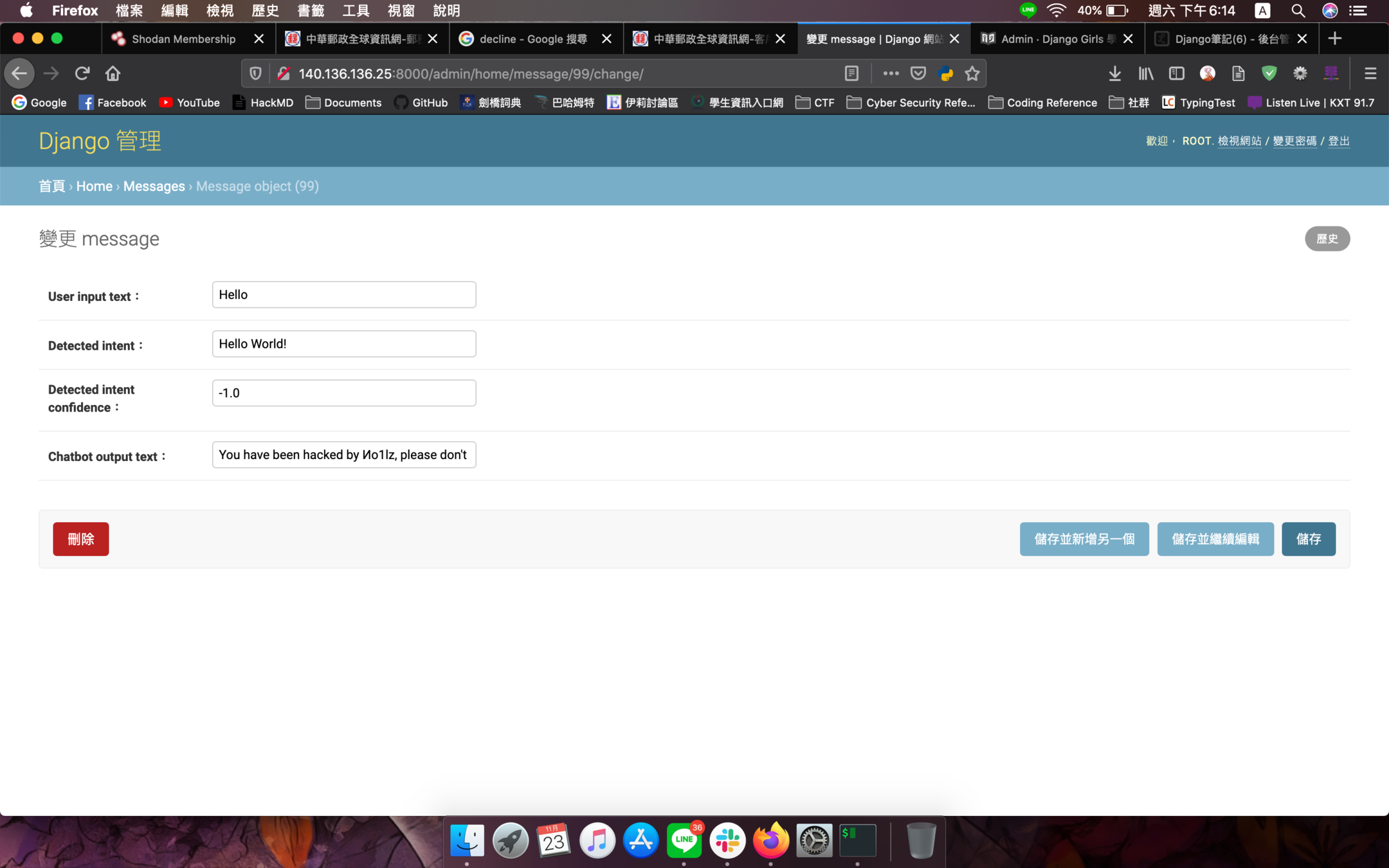
ENCORE
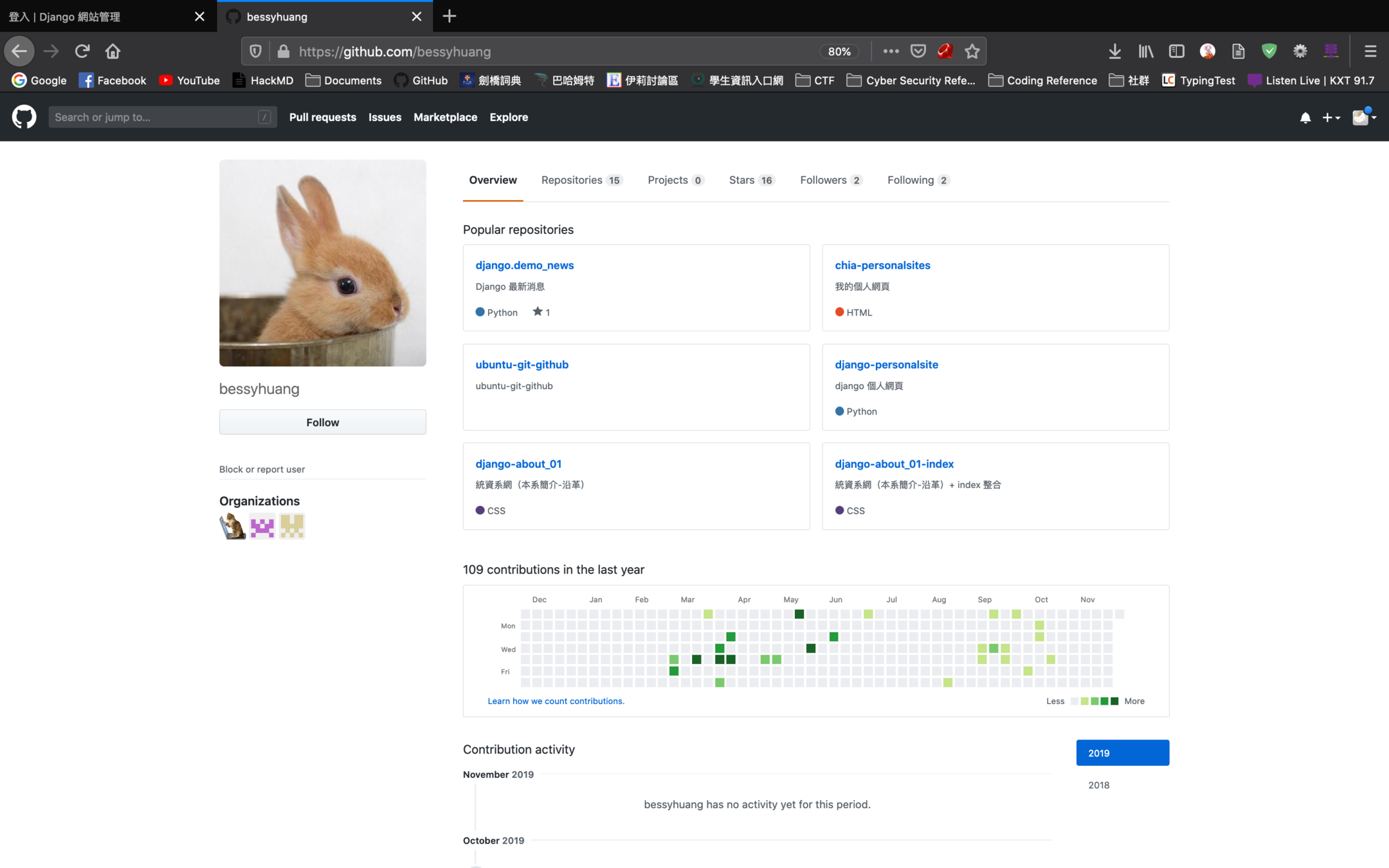
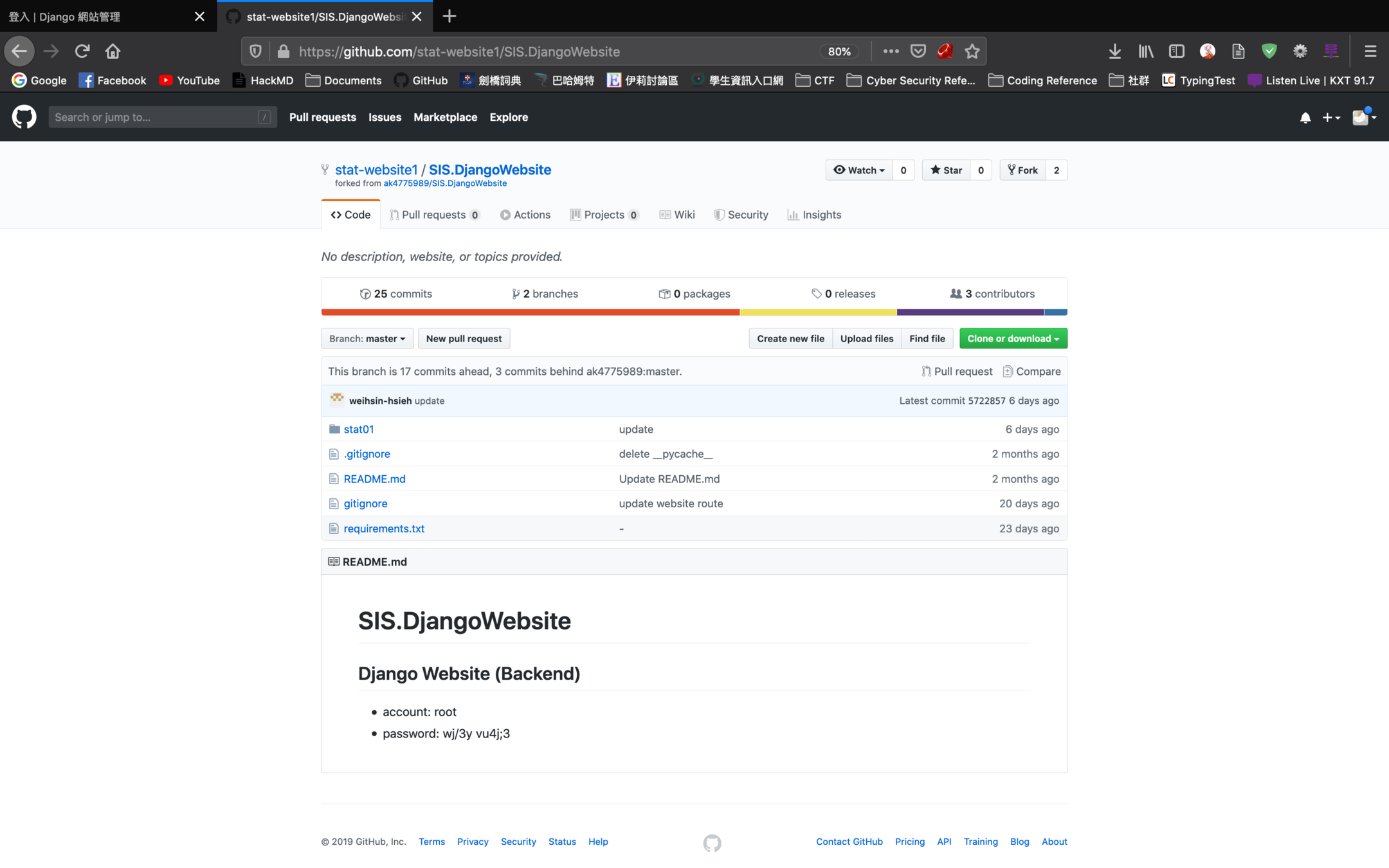
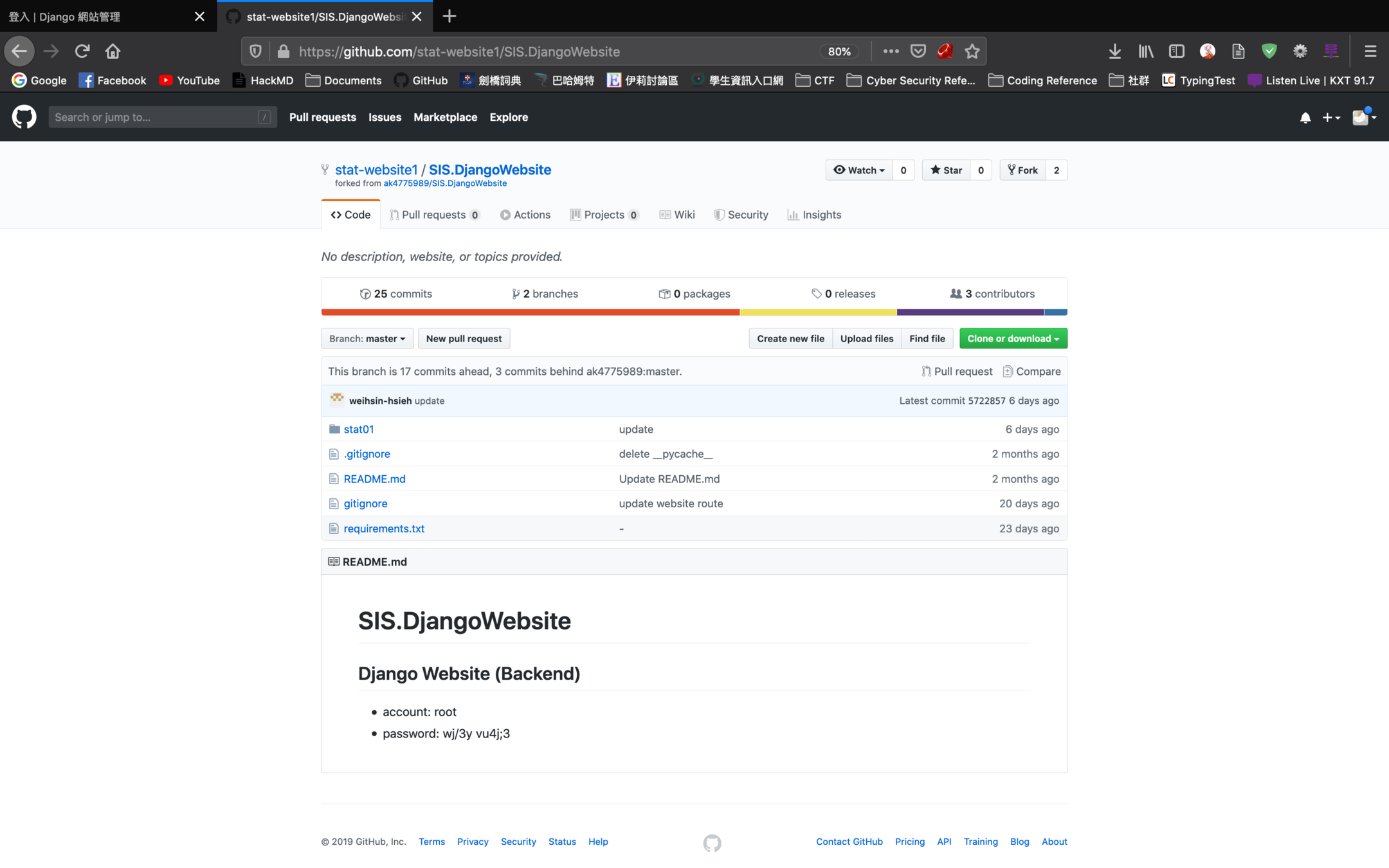
Github Dork


Thanks for listening.
References
- vootpool, (2019), What is Google dorks? | Google Dorks list | Google hacking tool. Retrieved from https://www.vootpool.com/google-dorks-list/
- Exploit Database, (2019), Google Hacking Database. Retrieved from https://www.exploit-db.com/google-hacking-database
- Jack Yu|傑克, (2017, Oct. 17th), Google Hacking. Retrieved from https://yu-jack.github.io/2017/10/17/google-hacking/
- 梅興, (2009, May. 19th), Google Hacking. Retrieved from https://sls.weco.net/node/12922
- Security Trails Team, (2019, Mar. 5th), Exploring Google Hacking Techniques. Retrieved from https://securitytrails.com/blog/google-hacking-techniques
Especially Thanks
Subtitle
Google Dorks
By Иo1lz
Google Dorks
For SIRLA - This 15 Speech
- 380



